Nissan's plan for safer autonomous driving? Connect the car to a human brain

Instead of removing the human element completely, the driver's brain activity is measured and sent to the car using a headband, the announcement said. The car can then predict human actions such as braking or accelerating and begin the action more quickly, potentially leading to safer, less stressful driving. The Brain-to-Vehicle (B2V) technology shows a different approach to autonomous driving by allowing the human to maintain some control. By staying physically in the driver's seat, some consumers may feel more comfortable with it compared to self-driving vehicle technology. "When most people think about autonomous driving, they have a very impersonal vision of the future, where humans relinquish control to the machines," Nissan executive vice president Daniele Schillaci said in the announcement. "Yet B2V technology does the opposite, by using signals from their own brain to make the drive even more exciting and enjoyable."
Connected Humans, Connected Things: AI and Human Intelligence in 2018
“What is real is the value of data,” Fitze said, “and that data is poised to explode in 2018 with billions of new endpoints lighting up, driven largely by the Internet of Things. Machine learning, deep learning, intelligence is richer when we have more data to derive patterns. Making life simpler and better through data makes sense, with smarter products – and that is the underlying value of layering in AI in IoT applications.” The trend towards automation and data collection and analysis is where Fitze sees “many, many use cases coming up. Where IoT gets even more interesting is when we finally reach the pivotal moment of IPV6, enabling over 600 billion IP addresses by each square millimeter around the world, as well as the speed of the manifestation of 5G/LTE networks which support voice recognition and more. When billions of people can use their voice to command billions of things, we’ll find ourselves in an entirely new world experience.”
Major Linux redesign in the works to deal with Intel security flaw
Intel's blunder was to allow user programs to be able to gather hints about how the kernel address space is laid out. As discovered by Austria's university researchers this summer, "Modern operating system kernels employ address space layout randomization (ASLR) to prevent control-flow hijacking attacks and code-injection attacks. While kernel security relies fundamentally on preventing access to address information, recent attacks have shown that the hardware directly leaks this information." ASLR is vital to today's operating systems' defense against malware. The Intel vulnerability isn't so much a new hole as it is a way of making all those many existing attack methods against ASLR-defended operating systems much stronger. The researchers' solution was KAISER, a system for Linux kernel address isolation. In November, these patches were proposed for the Linux kernel. Realizing just how dangerous these attacks could be, the Linux kernel developers quickly started revising these patches.
8 Biggest Tech Trends to Watch at CES 2018

At CES 2018, you'll see the Vobot Halo, a stylish smart light clock with Alexa, as well as the Blink Video Doorbell, a $99 device that's coming next year. In fact, Amazon has agreed to acquire Blink to accelerate its smart home domination. Security will be a huge theme at CES that extends to all-in-one security systems that hope to build on the success of products like SimpliSafe. The upcoming Angee has a 360-degree camera, voice recognition and motion sensors, and we'll see a separate home security gateway that supports HomeKit, Alexa and Google Assistant. ... So what makes micro LEDs so special? They have LEDs smaller than 100 micrometers — slimmer than the width of a human hair. According to Patently Apple, each of the red, green and blue subpixels in micro LEDs produces its own light, offering high contrast ratios and deep blacks. In addition, ZDNet says the displays will consume less power and won't suffer from burn-in as OLED panels do. In other words, Samsung could give OLED TVs a serious run for their money.
Competition Bureau weighs in on fintech: urgent action required
The Canadian Competition Bureau has released its final market study report into technology-led innovation in Canada's financial-services sector. The study is a valuable addition to a growing body of analysis and evidence that we need to do more to ensure that Canada is not left behind, as fintech has the potential to make an increasingly important impact on the availability and delivery of financial services to Canadians. In its study, the Bureau notes that since the 2007-08 global financial crisis, a new wave of financial-services firms has emerged, leveraging the latest technologies. In a number of jurisdictions, these firms are helping to reshape their domestic financial-services sectors and, in some cases, the leading firms are becoming national champions with global reach. The bureau notes that Canada lags behind its peers in fintech adoption; a number of reasons for slow adoption are suggested, including regulatory and non-regulatory barriers.
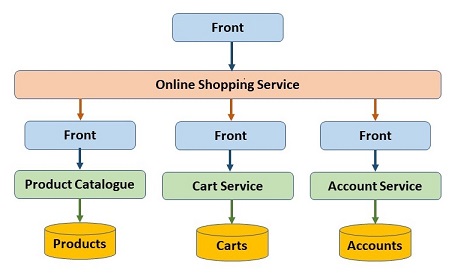
Implementing DevOps: Mind the Details
Many successful organizations roll out DevOps gradually to let different stakeholders see and appreciate the practice's value. This, in the long run, "accelerates the adoption of DevOps practices within the organization," Thethi explained. Looking for a quick start, many enterprises opt to create a DevOps team by simply rebranding their existing ops staff. "Don’t do that, as it keeps the silos running," warned James Wickett, an author of DevOps courses on Lynda.comand head of research at Signal Sciences, a cloud security platform provider. "Instead, rally the team around the aspirational goals of DevOps to deliver software faster through continuous delivery, automation and instrumentation," he suggested. ... "Since DevOps is mostly about processes and a way of working and collaborating, one of the major blockers can be from team members who do not understand or refuse to work with this new methodology," cautioned Sylvain Kalache
What’s now and next in analytics, AI, and automation
The world is more connected than ever, but the nature of its connections has changed in a fundamental way. The amount of cross-border data flows has grown 45 times larger since just 2005. It is projected to increase by an additional nine times over the next five years as flows of information, searches, communication, video, transactions, and intracompany traffic continue to surge. In addition to transmitting valuable streams of information and ideas in their own right, data flows enable the movement of goods, services, finance, and people. Virtually every type of cross-border transaction now has a digital component. Approximately 12% of the global goods trade is conducted via international e-commerce, with much of it driven by platforms such as Alibaba, Amazon, eBay, Flipkart, and Rakuten. Beyond e-commerce, digital platforms for both traditional employment and freelance assignments are beginning to create a more global labor market.
Bad AI Comes From Bad Data

Data completeness is the degree to which we have a total picture of donors, volunteers, activists, and other key constituent groups. This is a combination of self-reported information in addition to appended demographic data. Over time, the goal is to have a broader understanding of constituents interests, engagements, and preferences. Together, data quality and completeness are about 90% of the data health challenge. And yet, many of the claims of data struggle are design related. The plethora of custom fields in a system that can’t be normalized or made meaningful. The skeletons in the data closet from decisions made in the past about how data collection and management have been handled poorly. Fixing data design issues will take more time and toil, but addressing data quality and completeness can be started without delay. The sooner that data health is prioritized, valued, and championed then the greater chances for benefits to the organization.
Bringing AI into the enterprise
Sometimes, you see a decision being made and, from an organizational point of view, everyone agrees that this decision is really strongly data driven. But it's not strongly data driven. It's data driven based upon the historical information that two or three people are using. It looks like they're looking at data and then making a decision, but, in fact, what they're doing is, they're looking at data and they're remembering one of 2,000 past examples in their heads and coming out with a decision. ... There are sets of tasks in almost any organization that nobody likes to have anything to do with. In the legal profession, there are tasks around things like discovery where you actually need to be able to look through a corpus of documents, but you need to have also some idea of the semantic relationships between words. This is totally learnable using existing technologies.
Technology in 2018 will reach new heights
The financial industry has embraced chatbots in a big way. Capital One, MasterCard, Royal Bank of Scotland and Santander are just a handful of institutions using them, so too has the legal sector. Clerksroom is using Billy Bot, a junior robot clerk, to automate many of its administrative processes. As a result, it has saved its clerks around 200 hours per month and been able to focus on higher value activities for enabling growth. What’s clear is that organisations are quickly seeing the value in AI, and we will see investment rocket in 2018 and beyond. .... When Chancellor Philip Hammond delivered his annual Autumn budget in November last year, he said: “A new tech business is funded every hour and I want that to be every half hour. So, today we invest over £500 million in a range of initiatives from artificial intelligence to 5G and full-fibre broadband.”
Quote for the day:
"At the heart of great leadership is a curious mind, heart, and spirit." -- Chip Conley