Return to the office: This company is giving workers beeping wristbands to keep them socially distancing

Getting back into the swing of things will be by no means be easy. With remote
workers having been confined to their homes for so long, sharing a workspace
with others will require employees to be mindful of their surroundings, not to
mention to curb their desire to reform old office huddles. "As the trial
began, it became clear that many people were undercutting the correct physical
distance," Renner admits. "But, as they got used to wearing the sensors, the
trial participants got a better feel for the distance they needed to keep –
and the number of beeps heard around the office quickly fell." Renner makes a
point that some of the challenges of re-entering office life are things that
businesses could very easily overlook. "It may seem straightforward, but one
of our challenges has been to work out how people can safely bring in, prepare
and eat their own lunch in the office," he says. "Initially, employees were
asked not to use the microwaves as a lot of people touch these appliances. But
quite a few people wanted to bring in their own food. So, we changed the rules
and allowed people to use the kitchen again and, to make things safer, we
moved cutlery and plates outside of drawers, so people don't have to touch so
many handles and surfaces."
R&D in the Banking Sector: Making the case for Innovation Data Labs

As the BFSI industry turns its attention to Fintechs to meet their
digitization challenges; the eventual target areas for their R&D
efforts does not waver: Develop and Deploy new technologies to
better serve B2B banking customers, Increase profits, improve compliance and
security preparedness and reduce infrastructure costs. If the end-goals are
similar, then where does the Banking R&D differentiation come from? In
one word: Reliability. To infuse reliability as a core rubric in its R&D
paradigm means Banks have to check a number of boxes. Firstly, Banks and
Technology teams need to bedrock ‘reliability-as-a- yardstick’ in their
partnerships; across vendors, across geographies, across platforms.
Secondly, Reliability is built over time by adopting a divergent approach.
The ‘traditional-hire-and-instruct-engineers-on-a-project-mode’, does not
produce optimum test results because to harness advanced technologies
necessitates an experimental mindset as opposed to the erstwhile engineering
approach. Finally, reliability comes at a cost. To experiment with
production in real time comes with a sizable expense – One, the cost of
errors can be high, and Two, the multifarious skill base
We are at a critical point for mental health in the tech sector

We are now entering a new phase, with lockdown easing and more aspects of life
beginning to move towards something more like normality. But while
instinctively one might expect this to reduce the mental strain on people, for
a significant proportion this easing is in fact ushering in a whole new phase
of worry, concerned about catching the virus or passing it on to members of
their household. This just underlines the fact that the Covid-19 crisis and
its effects are not a one-off shock – but a long-term shift into a new normal.
It becomes essential for tech businesses to ensure they are responsive to this
and provide their staff with the support they need, for example by creating
online resources, supporting the creation of mental health networks and
discussion forums and, potentially, offering staff access to counselling
services too. Encouragingly, we found that 56% of companies have increased the
level of personal and emotional support to staff since the crisis began.
However, half of businesses still don’t offer any formal support for mental
health issues. The difference this makes is visible: three quarters of those
working for unsupportive companies are either concerned about their mental
health now or in the past.
Ethics in AI – Responsibilities a business has to the consumer

The software may be fool proof, but the same cannot be said about the data.
Biases in the initial data the program is learning from will quickly spread to
its outputs. Amazon had to scrap its recruitment AI tool because it started
penalising CVs for containing the word “women’s”. In the male-dominated IT
industry, men had been recruited at a higher rate than women. Words unique to
women’s CVs appeared much less in successful hires compared to general words
like “leadership”. The AI concluded that these words must be of low value and
started penalising them. The lesson to be learned from this example is to
identify gaps in the data and apply weightings so that demographics are
equally represented. The fidelity with which an AI can classify massive
amounts of data can even discourage looking for errors. Who’s going to argue
with a program that can classify thousands of people’s faces with 98% accuracy
via impenetrable mathematics? This is compounded by the so-called Black Box
AIs that never show their workings. Typically, it involves the software
projecting the data across high-dimensional mathematical spaces to extract
unique features, but it is very abstract. Resist the temptation to outsource
your thinking to the program or assume it knows what it’s doing.
How UK arts CIOs are keeping the show going on during the pandemic

“Any kind of technology is a tool that theatre can use, both creatively and to
make itself visible. Just as limelight, gas lighting or the Victorian illusion
of Pepper’s ghost were once new technologies, digital is another technology
that can benefit theatre,” says theatre critic Lyn Gardner. How can the arts
survive an uncertain future? Returning to the old ways of visiting museums or
mingling in crowds at shows hardly seems viable, now that social distancing
seems to be on the table at least in the medium term. Although there might be
a day when we're able to enjoy again the unique experiences only the live arts
can offer, in the meantime, CIOs and CTOs have an essential role to play in
supporting the existing alternatives, and imagining new ones. Augmented
reality, mixed reality or virtual reality could be one way forward for this
sector, so urgently in need of sustainable recovery. Solomon Rogers, founder
and CEO of immersive content studio REWIND and chairman of both the BAFTA
Immersive Entertainment Advisory Group and Immerse UK, is of the opinion that
these technologies present the arts with limitless opportunities.
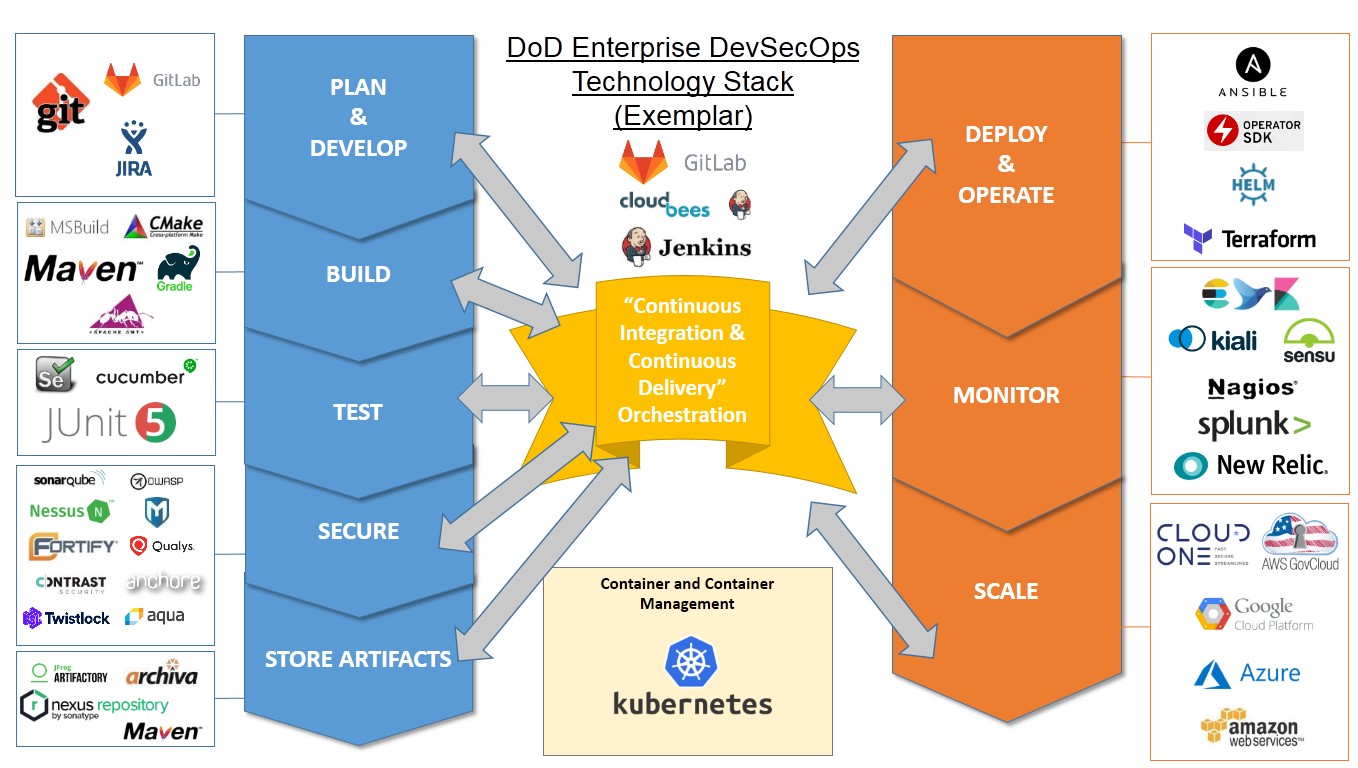
For digital transformation success, get serious about open source

Software is powering almost every business and they want to use that as a
competitive advantage…. [Companies] need [the] ability to move quickly and
they need to be able to change directions quickly to respond to new threats or
seize new opportunities." Similar sentiments were expressed on the earnings
calls of Fastly, Elastic, and Twilio, and no doubt will continue to be
highlighted by others. However, you can't really talk about the importance of
software without calling out just how central open source is to the software
that every organization on earth builds and uses. While you can absolutely pay
others to support open source for you, the companies that want to have the
most control over their digital futures will be those that also contribute
strategically to open source projects. ... The first is simply to provide
funding to a particular project, either to help defray development costs or
something else like stage an (almost certainly online) event. The second is to
commit your own developers to the project. This can be the most effective way
because the more code they contribute, the more influence you can earn over
the direction of the project.
Accurate data in, better insights out

“Ensure data is checked for quality as close to the source as possible,” he
says. “The more accurate it is upstream, the less correction will be needed at
the time of analysis – at which point the corrections are time-consuming and
fragile. You should ensure data quality is consistent all the way through to
consumption.” This means carrying out ongoing reviews of existing
upstream data quality checks. “By establishing a process to report data
quality issues to the IT team or data steward, the data quality will become an
integral part of building trust and confidence in the data. Ensure users are
the ones who advise on data quality,” says Cotgreave. “When you clean data,
you often have to find inaccurate data values that represent real-world
entities like country or airport names. This can be a tedious and error-prone
process as you validate data values manually or bring in expected values from
other data sources,” he adds. “There are now tools that validate the data
values and automatically identify invalid values for you to clean your
data.”
Machine learning in Palo Alto firewalls adds new protection for IoT, containers

“It is very important for us to apply ML when you start collecting huge
amounts of data about your network,” said Sreeni Kancharla, vice president and
CISO of Cadence Design Systems, an electronic design-automation software and
engineering-services company speaking at the Palo Alto PAN 10 introduction.
It’s important to get a faster response time to threats without making the
security environment more complex, Kancharla said. On the IoT front PAN 10.0
supports a subscription service that targets IoT systems. “IoT devices present
unique challenges for security teams. They are connected to an enterprise’s
central network, yet they are generally unmanaged,” Oswal said. “For the most
part, they are also unregulated, shipped with unknown or unpatched
vulnerabilities, and often their useful life exceeds their supported life.”
Oswal noted that a recent Palo Alto Unit 42 IoT threat report that said 57% of
IoT devices are vulnerable to medium- or high-severity attacks, and 98% of all
IoT-device traffic is unencrypted. Unit 42 is the vendor’s threat-research
arm.
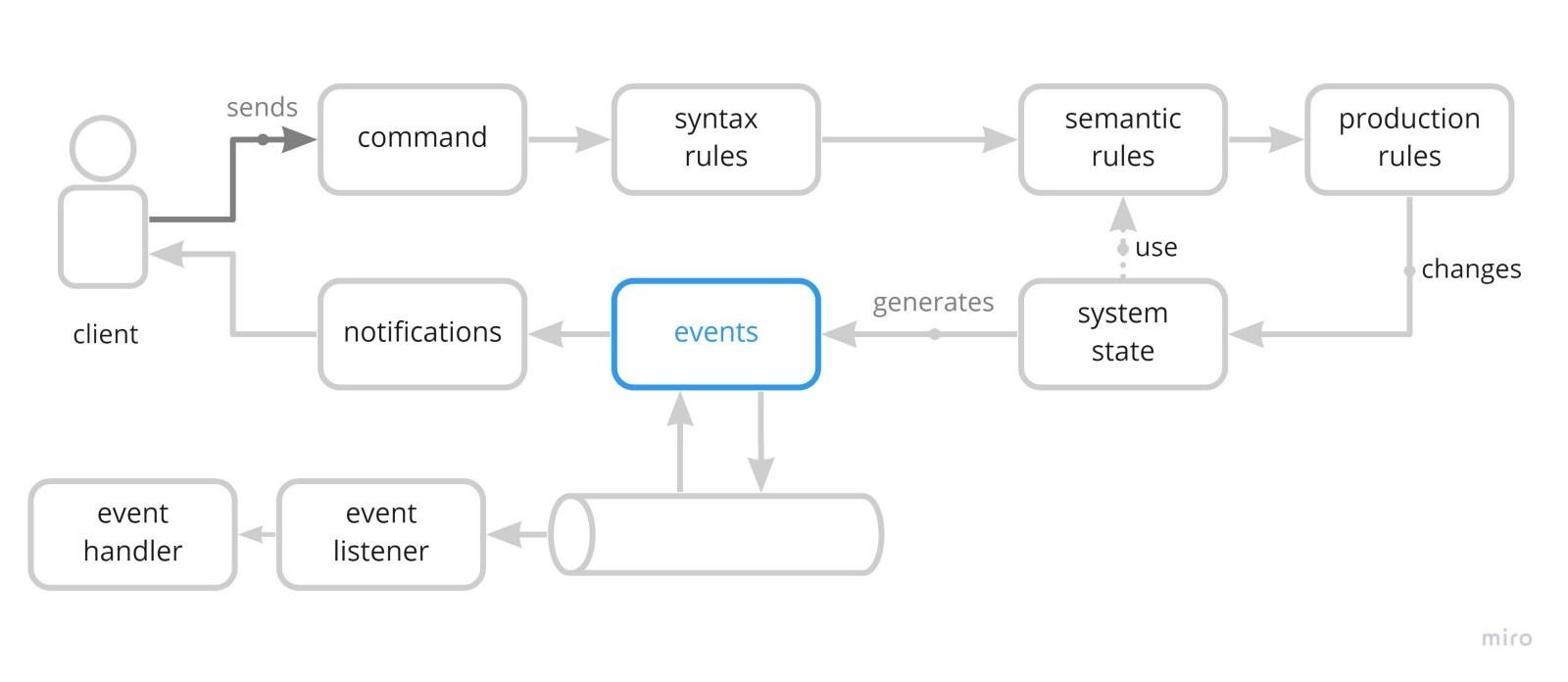
.NET Core: Interaction of Microservices via Web API
Almost everyone who has worked with microservices in the .NET Core probably
knows the book of Christian Horsdal, “Microservices in .NET Core: with
examples in Nancy” The ways of building an application based on microservices
are well described here, monitoring, logging, and access control are discussed
in detail. The only thing that is missing is a tool for automating the
interaction between microservices. In the usual approach, when developing a
microservice, a web client for it is being developed in parallel. And every
time the web interface of the microservice changes, additional efforts have to
be expended for the corresponding changes in the web client. The idea of
generating a pair of web-api / web-client using OpenNET is also quite
laborious, I would like something more transparent for the developer. So, with
an alternative approach to the development of our application, I would like:
The microservice structure is described by the .NET interface using attributes
that describe the type of method, route and way of passing parameters, as is
done in MVC; Microservice functionality is developed exclusively in the
.NET class, implementing this interface...
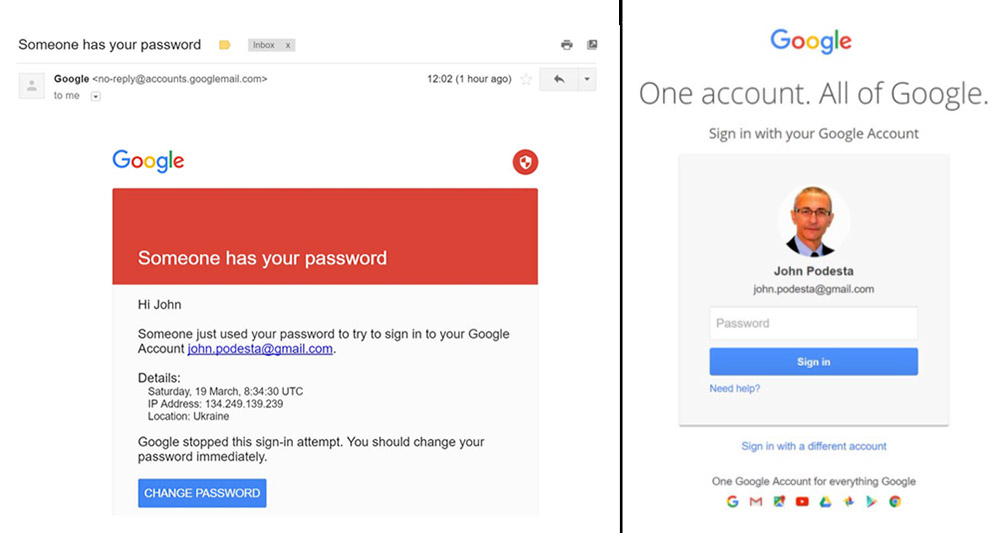
AI: A Remedy for Human Error

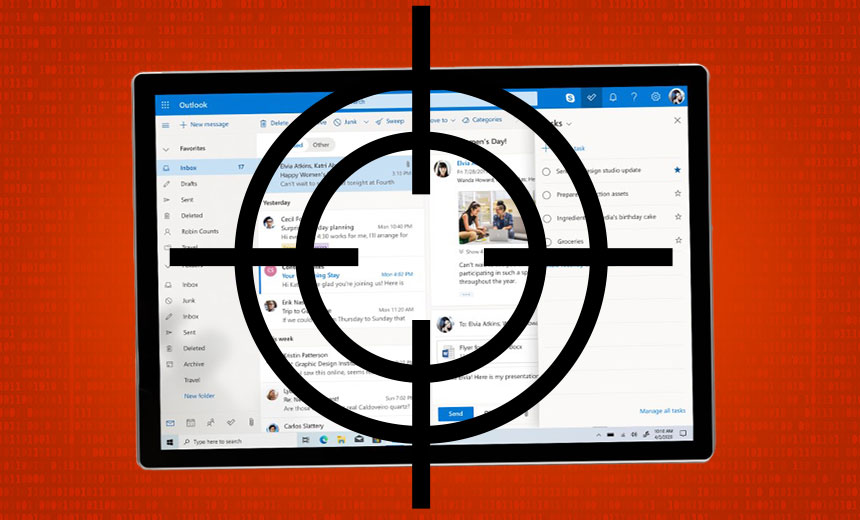
An employee might follow instructions in a phishing email not only because it
looks authentic, but that it conveys some urgency (usually from a manager or
someone else of importance). Employee training can help reduce the likelihood
of error, but solving the technological shortcoming is more effective: if a
phishing email is blocked from delivery in the first place, we can help
mitigate the human error factor. This is where artificial intelligence can be
a game-changer. We already use AI to simplify our home lives, using it to
perform a variety of tasks, from turning on lights, to playing our favourite
music. But if AI solutions are deployed in the workplace, we can help address
the biggest elephant in the IT room: data security. Data security is a major
area of concern, and it’s likely the leading cause for lost hours – and lost
sleep – for security and IT professionals. According to a recent survey of
over 500 IT professionals in the financial services industry, a whopping 94%
said that they lack confidence in the ability of employees, consultants, and
partners to safeguard customer data. And because cybersecurity is a complex
domain – with many unknowns and moving parts – the rigid, conventional
solutions can’t be effective. However, AI solutions can learn, adapt, and
dynamically react to an organisation’s cybersecurity needs.
Quote for the day: