Rebranding Data Governance

To successfully implement managed self-service business intelligence at any
non-trivial scale, you need data governance. To build and nurture a successful
data culture, data governance is an essential part of the success. Despite this
fact, and despite the obvious value that data governance can provide, data
governance has a bad reputation. Many people – likely including the leaders you
need to be your ally if you’re working to build a data culture in your
organization – have had negative experiences with data governance in the past,
and now react negatively when the topic of data governance is raised. ... Data
governance, and building a data culture in general, is as much about people as
it is about processes and technology, and that means effective communication is
key. Effective communication requires a shared vocabulary, and a shared
understanding of the meaning of key words. It may be time to think about
rebranding. Not unlike how a corporation with a reputation for all the wrong
things might change its name in an effort to leave all those negative
connotations behind without really changing its ways, maybe we need to rebrand
data governance… at least some of the time.
Crypto Banks: The intersection of traditional finance and DeFi?
It is important to note that crypto banks are very much centralized like
traditional banks, something which flies in the face of the true crypto
experience, predicated on decentralisation and a reduction in intermediaries.
This means that the problems of a banking collapse, hacks and attacks can still
impact a person's money and they are not achieving the financial independence
that crypto offers. However, it also means that these crypto banks have
regulatory standing and the ability to be compliant. They are legal entities
that can be subject to laws and legislation; legislation that is constantly
evolving to meet the changing of the times. At face value, it appears that these
Digital Asset Institutions/"Crypto Banks", are appeasing those new to the space
who are willing to join the early majority and move to a more crypto-focused
financial way of life. Good UX, simple integrations with existing financial
platforms, more financial options in a crypto context, and reliable regulation
mean a massive open door for users to flood into if they are looking for this
kind of experience.
Breakthrough Proof Clears Path for Quantum AI – Overcoming Threat of “Barren Plateaus”
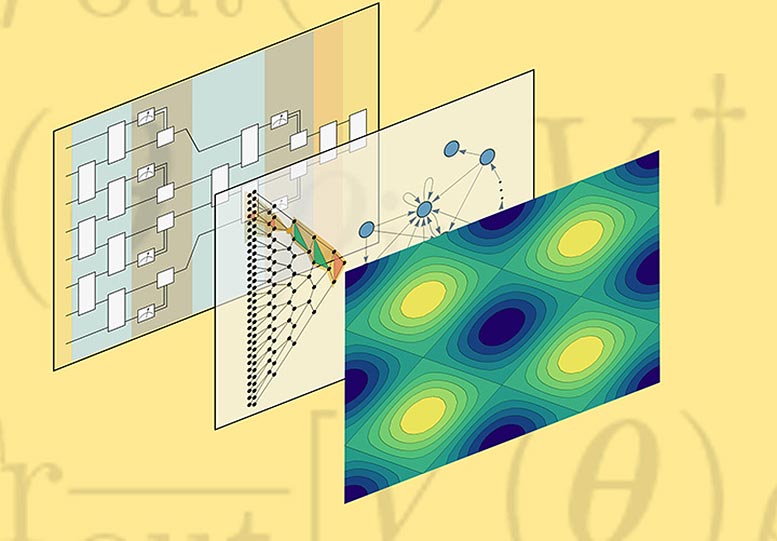
“All hope of quantum speedup or advantage is lost if you have a barren
plateau,” Cerezo said. The crux of the problem is a “vanishing gradient” in
the optimization landscape. The landscape is composed of hills and valleys,
and the goal is to train the model’s parameters to find the solution by
exploring the geography of the landscape. The solution usually lies at the
bottom of the lowest valley, so to speak. But in a flat landscape one cannot
train the parameters because it’s difficult to determine which direction to
take. That problem becomes particularly relevant when the number of data
features increases. In fact, the landscape becomes exponentially flat with the
feature size. Hence, in the presence of a barren plateau, the quantum neural
network cannot be scaled up. The Los Alamos team developed a novel graphical
approach for analyzing the scaling within a quantum neural network and proving
its trainability. For more than 40 years, physicists have thought quantum
computers would prove useful in simulating and understanding quantum systems
of particles, which choke conventional classical computers.
Great Engineering Teams Focus On Milestones Instead of Projects
The problem is that we aspire to unnecessary precision. We don’t need to know
exact estimates to ensure engineering focuses on the most important work. The
cost of producing exact estimates is wasteful. And it doesn’t even produce the
outcome you’re looking for. You don’t need to pretend the feature will be done
on June 20. This date is most certainly incorrect anyway. Milestones reduce
the complexity of putting together high-level estimates. They give a shorthand
that can be good enough for most decision-making, without the overhead of
rigorous estimation. Occasionally, I see people succeed at rigorous
estimation. But it’s rarely systemic – it’s usually one individual that is
good at it. And it relies on them. If they go on vacation for a week, nobody
is able to feed their model, and it collapses. While this is a great skill, to
me it is the exception that proves the rule. Think of it this way: if one in
twenty people can estimate in a high complexity situation, how many could be
more successful in a less complex situation?
Better management through anthropology

Almost all business leaders and policymakers could benefit by asking the basic
question that dogs anthropology: if a Martian was to land here suddenly and look
around, what might they see?” writes Tett. In 1997, when GM was struggling to
get teams of engineers from its small car group, its Saturn subsidiary, and
Germany’s Opel to create a new vehicle together, the company called in
anthropologist Elizabeth Briody to figure out what was wrong. Briody discovered
the source of the dysfunction in differing cultural assumptions about meetings.
The Opel team expected meetings to be agenda-driven, decision-making sessions;
the small car group expected working sessions in which ideas would be shared and
discussed; and the Saturn teams expected consensus-building sessions. As a
result, the meetings were chaotic and frustrating for everyone. Unfortunately,
Briody’s insights came too late, and GM’s senior product development leaders
shut down the project. Lastly and most intriguingly, anthropology can help
surface what Tett calls social silence.
“Curiosity is a skill you can develop”: Microsoft UK’s National Technology Officer on driving innovation forwards
“The pandemic experience has been agreat example of how those values truly
help our decision-making and our approach to markets. We faced unprecedented
demand for our technologies because of the shift to home working. But we only
have finite resources, so we worked out where to focus our attention and apply
the most value. It was a strong statement, which came directly down from
Satya, that we needed to ensure we are preserving life and that our technology
was going to play a critical role.” Of the numerous case studies showing how
Microsoft has used its pioneering technology to help with the response to the
pandemic, Robinson offers two examples. First, Imperial College Healthcare NHS
Trust, one of the largest in England, used mixed-reality HoloLens headsets on
its COVID-19 wards to enable an entire team of specialists to join doctors
virtually on the frontlines of the pandemic, keeping them safe as they helped
patients with the virus. Additionally, Microsoft is driving artificial
intelligence innovation at Alder Hey Hospital, a children’s hospital in
Liverpool, and allowing doctors to make life-changing decisions remotely.
Overcoming Challenges to Automating DevSecOps
When you first move to security automation, you’ll find some security tasks
that can easily be automated and others that are harder to fit in. DevSecOps
teams will need to use many tools to cover all their bases, but no one wants
teams checking lots of different tool outputs. Making it easier to see
what’s going on and where risk lies by consolidating security tools and
results in a central platform is the way to go. This makes life easier by
giving a single pane of glass. Everyone generally agrees that DevOps teams
must adopt cybersecurity best practices, but testing takes time. Development
teams don’t have time to learn, use and check lots of security tools on top
of their existing workload. Automated solutions get to work without any real
need for maintenance or management. These solutions trigger tools to work at
the right time depending on the outcomes found without any manual input
needed. This gives you and your team valuable time back to focus on other
important matters. The goal of CI/CD pipelines is fast delivery of build and
release steps, typically through automation.
Unused identities: A growing security threat

The first step towards taking control over your identities and assets’
authorizations is to know what you have. This starts with scanning across
all your XaaS environments – that’s SaaS, IaaS, and PaaS – and taking an
inventory of which identities have authorization to which assets. This
involves ingesting the data from these different environments, normalizing
the data into a workable model, and then correlating it with your identities
from your identity provider (IDP) like Okta, Ping, Azure AD, or Google. The
goal here is to understand the relationship between the identities and
assets, assessing a wide range of factors including their usage and if they
are right sized to meet the policies/needs of the organization. Are there
identities with permissions to assets that have not been used in at least 60
days? This might be a good time to revoke those authorizations. But that’s
just a surface-level case. Once you start analyzing your entitlements on a
deeper level, you’ll begin to find that there are more permissions granted
to your identities than you’re likely to want to admit.
Digital transformation: 4 CIO tips for 2022

To be more agile, innovation and development teams must be closer to the
business and have the entire team involved in new product development,
testing, and validation. This ensures that their priorities are met from the
beginning and no time or resources are wasted. Performance and regression
testing and security scanning must be baked in throughout, in real-time, to
shorten the development cycle for maximum efficiency. In our organization,
that meant moving to weekly sprints and release cycles for our internal
infrastructure. Each week, our business reps prioritized what was most
important and participated in the testing and validation process. As we
worked to roll out our new partner portal, our marketing and support teams
were involved from the very beginning, advising the development team and
testing features and functionality. By bringing IT and business operations
closer together, we’ve been able to balance innovation and operations
without having to sacrifice either, even when talent or resources have been
limited.
Report Dissects Conti Ransomware Attack on Ireland's HSE
The HSE attack began on March 18 from a malware infection on an HSE
workstation - dubbed "Patient Zero Workstation" - as the result of a user
clicking and opening a malicious Microsoft Excel file that was attached to a
phishing email sent to the user on March 16. "After gaining unauthorized
access to the HSE’s IT environment on March 18, the attacker continued to
operate in the environment over an eight week period until the detonation of
the Conti ransomware on May 14," the report says. "This included
compromising and abusing a significant number of accounts with high levels
of privileges, compromising a significant number of servers, exfiltrating
data and moving laterally to statutory and voluntary hospitals." ... "There
were several detections of the attacker’s activity prior to May 14, but
these did not result in a cybersecurity incident and investigation initiated
by the HSE and as a result, opportunities to prevent the successful
detonation of the ransomware were missed."
Quote for the day:
"Leadership does not always wear the
harness of compromise." -- Woodrow Wilson
No comments:
Post a Comment