How software-defined storage (SDS) enables continuity of operations

Creating a new layer completely based on software in your infrastructure stack
means that costs for hardware can be minimised, while boosting multi-cloud
strategies. “Traditionally, regardless of how complex and well maintained your
data centre, its fixed position was a weakness easily exploited or corrupted
by theft, disaster or power-related issues,” said Ben Griffin, sales director
at Computer Disposals Ltd. “It’s for precisely this reason that SDS is a
reliable partner – offering a means of continuation should the worst happen.
“Decoupling storage from hardware, as is the case with SDS, brings a huge
range of benefits for the day-to-day duties of IT personnel. And, from a
broader company-wide perspective, it enables simpler continuity through
challenging periods by relying less on owned hardware and more on flexible,
accessible and affordable multi-cloud environments. “One of the great
attributes of SDS is scalability, and this, in turn, is often one of the
principal means of business continuity. Should a business need to downsize in
challenging times, with a view to reinvesting in personnel later down the
line, SDS provides this ability with none of the usual challenges associated
with managing a physical data centre.”
A perspective on security threats and trends, from inception to impact
The abuse of legitimate tools enables adversaries to stay under the radar while
they move around the network until they are ready to launch the main part of the
attack, such as ransomware. For nation-state-sponsored attackers, there is the
additional benefit that using common tools makes attribution harder. In 2020,
Sophos reported on the wide range of standard attack tools now being used by
adversaries. “The abuse of everyday tools and techniques to disguise an active
attack featured prominently in Sophos’ review of the threat landscape during
2020. This technique challenges traditional security approaches because the
appearance of known tools doesn’t automatically trigger a red flag. This is
where the rapidly growing field of human-led threat hunting and managed threat
response really comes into its own,” said Wisniewski. “Human experts know the
subtle anomalies and traces to look for, such as a legitimate tool being used at
the wrong time or in the wrong place. To trained threat hunters or IT managers
using endpoint detection and response (EDR) features, these signs are valuable
tripwires that can alert security teams to a potential intruder and an attack
underway.”
Evolution of Emotet: From Banking Trojan to Malware Distributor
Ever since its discovery in 2014—when Emotet was a standard credential stealer
and banking Trojan, the malware has evolved into a modular, polymorphic
platform for distributing other kinds of computer viruses. Being constantly
under development, Emotet updates itself regularly to improve stealthiness,
persistence, and add new spying capabilities. This notorious Trojan is one of
the most frequently malicious programs found in the wild. Usually, it is a
part of a phishing attack, email spam that infects PCs with malware and
spreads among other computers in the network. ... In recent versions, a
significant change in the strategy has happened. Emotet has turned into
polymorphic malware, downloading other malicious programs to the infected
computer and the whole network as well. It steals data, adapts to various
detection systems, rents the infected hosts to other cybercriminals as a
Malware-as-a-Service model. Since Emotet uses stolen emails to gain victims'
trust, spam has consistently remained the primary delivery method for
Emotet—making it convincing, highly successful, and dangerous.
Decentralised Development: Common Pitfalls and how VSM can Avoid Them
A value stream mapping exercise should involve all of the teams that would ever
collaborate on a release. Bringing everyone together ensures that all parts of
the process are being recognised and tracked on the map. Ideally, there should
be two sessions, the first focused on building a map of the current value
stream. This is essentially a list of every single action that is completed from
start to finish in the delivery pipeline. It includes all of the governance
tests that need to be conducted, how all of the individual actions relate to
each other, and which actions cannot be completed until something else has been
done first. It’s important to be very thorough during this process, and make
sure that every action is accounted for. Once the entire map is complete, you
are left with an accurate picture of everything that needs to be done as part of
the release pipeline. Not surprisingly, most companies don’t have this
visibility today, but it will be invaluable moving forward. For product managers
in particular, having a concrete outline of all of the processes that are
occurring gives them a clear sense of all the moving parts.
Now Available: Red Hat Ansible Automation Platform 1.2

The Ansible project is a remarkable open source project with hundreds of
thousands of users encompassing a large community. Red Hat extends this
community and open source developer model to innovate, experiment and
incorporate feedback to satisfy our customer challenges and use cases. Red Hat
Ansible Automation Platform transforms Ansible and many related open source
projects into an enterprise grade, multi-organizational automation platform
for mission-critical workloads. In modern IT infrastructure, automation is no
longer a nice-to-have; it’s often now a requirement to run, operate and scale
how everything is managed: including network, security, Linux, Windows, cloud
and more. Ansible Automation Platform includes a RESTful API for seamless
integration with existing IT tools and processes. The platform also includes a
web UI with a push-button intuitive interface for novice users to consume and
operate automation with safeguards. This includes Role Based Access Controls
(RBAC) to help control who can automate what job on which equipment, as well
as enterprise integrations with TACACS+, RADIUS, and Active Directory. Ansible
Automation Platform also enables advanced workflows.
How Cyberattacks Work
Cyberattacks have been increasing in number and complexity over the past several
years, but given the prevalence of events, and signals that greater attacks
could be on the horizon, it’s a good time to examine what goes into a
cyberattack. Breaches can occur when a bad actor hacks into a corporate network
to steal private data. They also occur when information is seized out of
cloud-based infrastructure. Many people think that security breaches only happen
to sizable corporations, but Verizon found that 43% of breaches affect small
businesses. In fact, this was the largest cohort measured. And the damage such
businesses experience is considerable — 60% go out of business within six months
of an attack. Small businesses make appealing targets because their security is
usually not as advanced as that encountered within large enterprises. Systems
may be outdated, and bugs often go unpatched for lengthy periods. SMBs also tend
to have fewer resources available to manage an attack, limiting their ability to
detect, respond, and recover. Additionally, small businesses can serve as
testing grounds for hackers to test their nefarious methods before releasing an
attack on another, bigger fish.
Time to Rethink Your Enterprise Software Strategy?

The response to process and software changes depends on where you are in your
digital transformation journey. Early adopters of digital transformation could
be hailed as genius in hindsight. Those still in their journey are speeding up
to make that last push to completion in case another round of pandemic,
locusts, or other plagues circle the globe. Those followers and laggards who
treated digital transformation as if it were a passing trend may find
themselves the proverbial coyote riding their “Acme Digital Transformation
Rocket” off the COVID cliff. But, thanks to technology (NOT from Acme), there
is hope. As organizations, including major software vendors, moved to Agile
frameworks to deliver software and implementations more quickly, a convergence
of technologies and services fell into place. Cloud services have been around
for a while, but the incredible push to move infrastructure to cloud platforms
and software as a service (SaaS) has been nothing short of amazing. With the
latest release of rapid deployment low-code/no-code tools from Salesforce,
Microsoft, Amazon, and Google/Alphabet, the toolsets are now designed for two
speeds: fast and faster. Changing the software and changing the processes are
related, but two different paths.
The Fintech Future: Accelerating the AI & ML Journey

Fintechs across the world are dealing with the effects of Covid-19 and face an
uphill challenge in containing the impact of it on the financial system and
broader economy. With rising unemployment and stagnated economies, individuals
and companies are struggling with debt, while the world in general is awash in
credit risk. This has pushed operational resilience to the top of fintech
CXOs’ agendas, requiring them to focus on systemic risks while continuing to
deliver innovative digital services to customers. To make matters worse,
criminals are exploiting vulnerabilities imposed by the shift to remote
operations post-Covid-19, increasing the risk of fraud and cybercrime. For
fintechs, building and maintaining robust defences has, therefore, become a
critical priority. Organisations around the globe are forging new models to
combat financial crime in collaboration with governments, regulators, and even
other fintechs. The technological advances in data analytics, AI and machine
learning (ML) have been driving fintechs’ response to the crisis, accelerating
the automation journey many had already embarked on. Until recently, fintechs
have used traditional methods of data analysis for various applications,
including the detection of fraud and predicting defaults, that require complex
and time-consuming investigations.
Managing Metadata: An Examination of Successful Approaches

Metadata turns critical ‘data’ into critical ‘information.’ Critical
information is data + metadata that feeds Key Performance Indicators (KPIs).
He recommends asking: “What will change with a better understanding of your
data?” Getting people on board involves understanding how metadata can solve
problems for end users while meeting company objectives. “We want to be in a
position to say, ‘I do this and your life gets better.’” To have a greater
impact, he said, avoid ‘data speak’ and engage with language that the business
understands. For example, the business won’t ask for a ‘glossary.’ Instead
they will ask for ‘a single view of the customer, integrated and aligned
across business units.’ An added benefit of using accessible language is being
perceived as helpful, rather than being seen as adding to the workload. ...
When documenting the Information Architecture, Adams suggests focusing on how
the information flows around the architecture of the organization, rather than
focusing on specific systems. Start with the type of information and where it
resides and denote broad applications and system boundaries. Include data
shared with people outside the organization.
Meet the Microsoft Pluton processor – The security chip designed for the future of Windows PCs
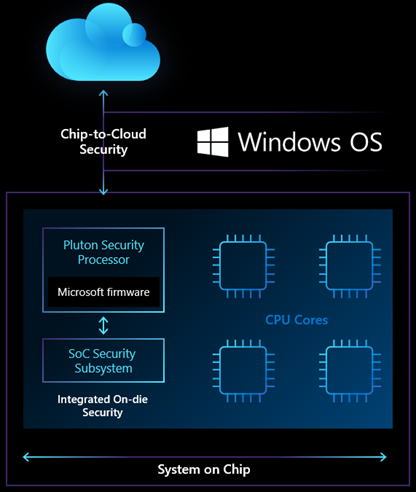
The Microsoft Pluton design technology incorporates all of the learnings from
delivering hardware root-of-trust-enabled devices to hundreds of millions of
PCs. The Pluton design was introduced as part of the integrated hardware and OS
security capabilities in the Xbox One console released in 2013 by Microsoft in
partnership with AMD and also within Azure Sphere. The introduction of
Microsoft’s IP technology directly into the CPU silicon helped guard against
physical attacks, prevent the discovery of keys, and provide the ability to
recover from software bugs. With the effectiveness of the initial Pluton design
we’ve learned a lot about how to use hardware to mitigate a range of physical
attacks. Now, we are taking what we learned from this to deliver on a
chip-to-cloud security vision to bring even more security innovation to the
future of Windows PCs. Azure Sphere leveraged a similar security approach to
become the first IoT product to meet the “Seven properties of highly secure
devices.” The shared Pluton root-of-trust technology will maximize the health
and security of the entire Windows PC ecosystem by leveraging the security
expertise and technologies from the companies involved.
Quote for the day:
"If we were a bit more tolerant of each other's weaknesses we'd be less alone." -- Juliette Binoche
No comments:
Post a Comment