The evolving role of the CHRO in the post-pandemic era

A major landscape shift for CHROs is the advent of HR technologies that can be
used as hiring as well as learning and development tools. By collecting and
analysing critical HR data, companies can derive actionable insights to improve
workforce, people, and talent management performance. Case in point, TDCX’s
proprietary Flash Hire recruitment platform enables hiring managers to gauge a
candidate’s competency and alignment with the job requirements more quickly
through its artificial intelligence (AI) capabilities. ... Actionable insights
can be combined with digital tools to boost employee productivity and encourage
workers to further their career trajectories through learning and coaching for
better outcomes. Additionally, digital tools can help organisations reach out
and engage talent globally. While companies innovate their HR strategies by
leveraging data analytics and digital tools, such efforts should also be
balanced with a human touch. Many companies are already using technology such as
robotic process automation and AI to improve hiring, boost employee productivity
and encourage learning and career growth, and such instances will only continue
to increase.
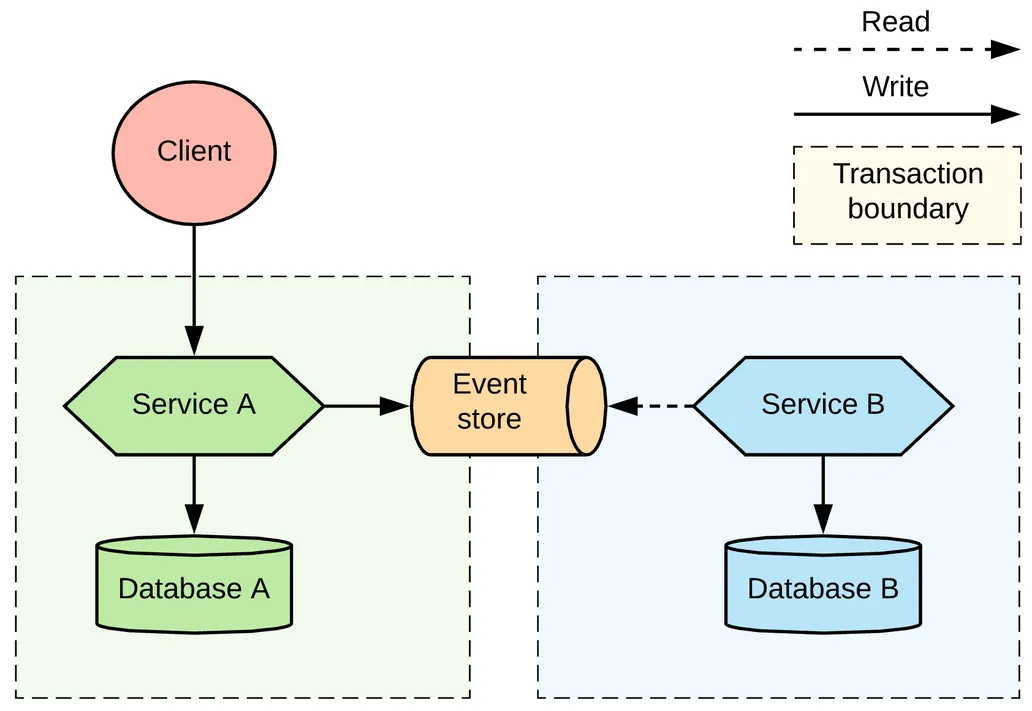
Three Trends in Enterprise Architecture to Optimize IT Operations
A shift to Continuous Delivery sees each team organize itself around an
end-to-end value stream that brings ongoing and longer-term benefits to the
business rather than short-term and time-bounded “wins” for individual
departments. In addition, a Continuous Delivery approach aims to change the
delivery model so that teams can work independently and with less direction
rather than competing with one another for resources. ... In this model, each
team holds responsibility for the design, operation, realization and
future-state direction of their own semi-independent business area. Empowering
teams in this way causes a shift in power control, making decision-making more
democratic and less centralized. In addition, optimizing collaboration between
teams brings about more active conversation and facilitation, resulting in a
freer flow of information across the business. In shifting the Enterprise
Architect role to a facilitator role than that of a data warden, the
democratization of Enterprise Architecture significantly impacts the enterprise,
evolving how it operates and the type of tooling it needs for success.
IT Leaders as Advocates for Continual Change
“All IT leaders should keep the concept of constant change top of mind, as it is
essential for driving innovation, staying ahead of the curve, and responding
quickly to new challenges and opportunities,” he says. Dennis Monner, chief
commercial officer at Aryaka, explains businesses are coming to realize that
digital transformation is a never-ending process. “As environments change and
are on the verge of more change, IT leaders want to be well-prepared and be able
to adapt,” he says. This means they need to be continuously evaluating their
businesses, as well as different models of operation that may facilitate
transformation more smoothly. “IT leaders must recognize when a particular
approach may not be working as expected and when a pivot may be necessary,” he
says. “Keeping an open mind to continual change means a business is putting the
needs of its customers first, rather than forcing customers to adapt and settle
for less than they deserve.” If a product or service isn’t resonating with
customers, business leaders need to be willing to shake things up, as opposed to
continuing down a path that will not yield results.
Top Digital Communication Skills You’ll Need For 2023

Cultural and social sensitivity is a significant part of d igital communication
management. Understanding different cultural and social dynamics enables you to
become a better business leader, and will help you to develop relevant
communication strategies. This is why at BI students receive a grounding
in psychological and sociological concepts underlying communication process.
Modules such as ‘human interaction’ and ‘human-technology interaction’ educates
students on different theories related to identity and diversity. Along with an
extensive understanding of how people interact and communicate with each other
through technology. ... To excel in a career management, it is vital that you
have a clear understanding of the dynamics of communication. At BI, you will be
introduced to solid theories and research which revolve around digital
communication strategy, social media, network theory, and innovation and
corporate storytelling. Our methods course covers the basics of qualitative and
quantitative methods such as data handling, recoding, experimental statistics,
and digital and social network data analysis.
How Unregulated Access and Advanced Processing Threaten Personal Privacy

Powerful tech companies like Google, Amazon, Meta, and Apple revolutionized data
analytics and its use in the private sector. By combining widely collected user
activity with behavioral psychology, commercial organizations alter choices that
people make, often in the interest of profit maximization. While not illegal,
such manipulation challenges the notions of individual choice in a liberal
society. However, while processing capabilities have matured, the requirements
to secure data during the collection, storage, and analysis phases grow
increasingly complex. Companies face endless attempts to exploit networks and
servers, keeping cyber security teams busy with ever-evolving threats.
Preventing data breaches, such as the 2013-2015 exfiltration of personal
information from the United States Office of Personnel Management (OPM),
requires skilled technicians and powerful software working around the clock.
Perhaps more concerningly, the proliferation of commercially-collected data has
led to the rise of data brokers, who profit off the collection and sale of
personal information within the current legal limitations of consumer data
usage.
Should Every Incident Get a Retrospective?

Try to do this for every incident, and you’ll quickly run into practical
limitations. Each incident can take tens of person-hours to study, and
meanwhile, more incidents may stack up. At some point, there won’t be enough
hours in the day, incident analysts to run investigations or money to spend.
You’ll also soon exhaust your organization’s goodwill. Earlier in my career, I
learned this lesson the hard way. My site reliability engineering (SRE) team had
a keen interest in getting a handle on the growing number of production
incidents in our cloud infrastructure. ... High-profile incidents as a whole
should give you pause. These are exactly the kinds of incidents that we can
learn the most from. However, tensions will run high, and even a company that
normally embraces a blameless approach to retrospectives might look for someone
to take the fall. Does your incident retrospective have the potential to cause
harm to incident participants, or perhaps even termination? It might be best to
focus on incidents that are less emotionally charged, especially at companies
that are still early on the path toward blameless retrospectives.
UK data regulator issues warning over generative AI data protection concerns
“Organisations developing or using generative AI should be considering their
data protection obligations from the outset, taking a data protection by design
and by default approach,” said Stephen Almond, the ICO’s director of technology
and innovation, in the post. Almond also said that, for organizations processing
personal data for the purpose of developing generative AI, there are various
questions they should ask themselves, centering on: what their lawful basis for
processing personal data is; how they can mitigate security risks; and how they
will respond to individual rights requests. “There really can be no excuse for
getting the privacy implications of generative AI wrong,” Almond said, adding
that ChatGPT itself recently told him that “generative AI, like any other
technology, has the potential to pose risks to data privacy if not used
responsibly.” “We’ll be working hard to make sure that organisations get it
right,” Almond said. The ICO and the Italian data regulator are not the only
ones to have recently raised concerns about the potential risk to the public
that could be caused by generative AI.
The Data Trifecta: Privacy, Security, and Governance from Reactivity to Resilience

The panelists broadly agreed that bringing together privacy, security, and
governance teams to develop a tech-driven model of unified engagement can
revolutionize a business’s efficiency and effectiveness. In Sommer’s
observations, this form of platform approach cuts down on the number of
individual interactions between teams, while at the same time distilling the
load of regulatory obligations, all of which makes operations more manageable
to support. Streamlining this process allows managers to automate rules and
controls into the data in a manner that lets the data flow, “which ultimately
means that our privacy teams and security teams can say yes to more projects,”
noted Prestidge. “Then our data teams can get access to that approved data
much quicker, speeding up all of the processes and reducing the risk.” ... “At
the end of the day, the intentions behind most privacy regulations tend to be
focused around protecting the consumer,” reflected Sommer. It’s therefore
essential for data teams to implement a degree of consistency between promises
made to consumers in initial privacy disclosures and the ways in which data is
used – and shared – in current operations.
Designing Tabletop Exercises That Actually Thwart Attacks

"The big thing that we want to shoot for in these tabletops is as much realism
as we can possibly get," Durrin says. But realism is difficult to simulate.
Davidoff jokes about how "we tried using ChatGPT to run a tabletop exercise,"
and it didn't turn out so well. "It's like: 'I am the facilitator,' and starts
walking you through the steps. But it's very boring. It doesn't give you any
curveballs." Simulating realism, ironically, requires a good deal of
showmanship: storytelling, audio and visual materials, and a certain
creativity to generate the chaos and unpredictability you'd find in a
cyberattack in real life. But little of this theater is completely made-up.
"We try to leverage the experience that we've gained over the years of
actually dealing with these attacks in the wild," Durrin notes, ...
Enterprises that run these kinds of simulations tend to avoid those mistakes.
"We've actually been able to see how those changes that we've made and tested
inside of an incident response plan have benefited organizations in a very
tangible and real sense," Durrin says, "in the speed of recovery, the quality
of recovery and how the organization is actually able to get back on their
feet after suffering from an incident."
Attention to detail matters
What about O’Brien’s theory that caring about details is something that you’re
born with? I think people can learn to apply more attention to detail. If you
give people enough context about why they should care about the little things,
they should make the effort to internalize the lesson. That must be what
happens in work environments in which people’s lives are on the line, such as
operating rooms and airplane cockpits. But what about in the office? In the
many years I spent as an editor managing teams of reporters, I learned it was
a good practice, when I moved into a role, to tell my new colleagues that I
didn’t like corrections—the notes reporters add at the end of an online
article that explain how an earlier version got some spelling or fact wrong. I
didn’t say it in a threatening way. I just shared it as a fact about me. That
approach sent a clear signal that I expected people to check their facts
before their piece was published. So, on the nature-or-nurture question, the
answer is probably a bit of both—but the advice would be to cultivate a
detail-oriented approach if you sense you might not be born with one.
Quote for the day:
"Listening & trusting the inner
voice is one of the most important lessons of leadership." --
Warren Bennis