CIOs must play a key role in ecosystem strategies

Digital technologies emphasize the need for a more agile IT strategy with technology investments that support the future needs of the business. IT organizations will need to be multi-speed, taking advantage of business opportunities such as boosting customer engagement via new digital channels or winning emerging markets customers—alongside their traditional role as providers of technology capabilities and solutions. Information technology is critical in satisfying the heightened need for data insights, as today’s executives seek accurate, real-time information that supports decision making, reduces risk, and helps drive improvements. Accenture Strategy research, Cornerstone of future growth: Ecosystems, shows that companies in the United States clearly see advantages in ecosystems, and almost half of those surveyed are actively seeking them. Accenture Strategy surveyed 1,252 business leaders from diverse industries across the world, including 649 in the United States, to better understand the degree to which companies are capturing ecosystem opportunities. Survey results indicated executives’ desire to lead through adaptation and adoption.
There is an appetite to change, with the construction industry looking at a range of technologies, on top of AI, that could help them in the future, with virtual reality (28%), cloud computing (24%), software defined networking (20%), blockchain (19%) and Internet of Things (17%) all seen as key to future development by those in larger organisations. According to Tech Nation’s 2018 report, technology is expanding 2.6 times faster than the rest of the UK economy, and yet the construction industry has been slow to implement digitalisation strategies that could bring increased efficiency and collaboration as well as reduced costs. The majority of the construction firms surveyed said they have either completed a digital transformation project or have one currently underway — over half (61%) noted improved efficiency and reduced operational costs (58%) as direct advantages.
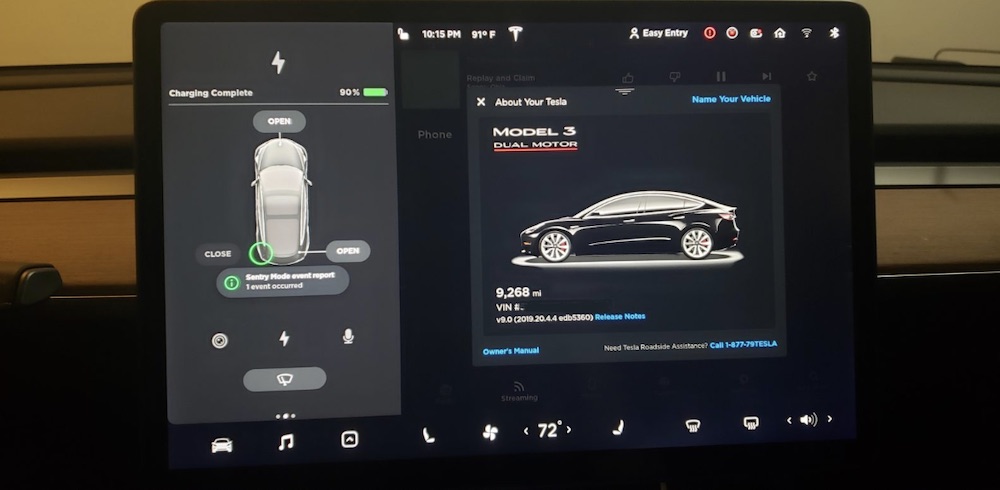
Maintaining Security As You Invest in UCC

Today’s modern workforce expectations for usability are unprecedented. Your users expect all their software to be simple to use and just work, no exceptions. The same goes for your customers – they don’t have the patience for a collaboration tool that isn’t immediately connected or intuitive. Don’t allow this expectation for ease-of-use to push you to security shortcuts. Users and administrators must be sensitive to default settings of the web applications being used to host their online meetings, and ensure permissions are set with both user experience and security at top of mind. Remind users to keep browsers up-to-date, including the latest security patches. Collaboration tools should never bypass operating system or browser security controls for the sake of simplicity to the end user. The risk is far greater than the reward. Meeting spaces should be safe spaces for open collaboration and discussion. But online meetings have opened up every internal conversation to external hackers in a way that in-office meetings never have.
Is It The Platform Or Is It The Ecosystem?
The key to ecosystems is understanding that they represent a whole new economy. Apple’s App Store succeeded in part because of the extensive advocacy for Apple at the launch of the iPhone. At the time, I worked inside Nokia, and we could barely get airtime for Nokia innovations in the face of all the content that encircled an incumbent in a powerful industry like computing. It was only after a year or so that Apple understood it was creating opportunity for ‘the little guy’. It stumbled upon success with apps but its ecosystem was there long before Steve Jobs gave it the red light. Ecosystems thrive on information and content. They also thrive when they create multiple avenues for new businesses, as per the Airbnb example above. Like anything, they need strong branding and that gives incumbents the advantage.They thrive when they breach the walls of an established industry, allowing entrepreneurial passion to pour in. In healthcare, GE tried to establish an ecosystem for breast cancer diagnostics but in reality it only let in established healthcare firms.
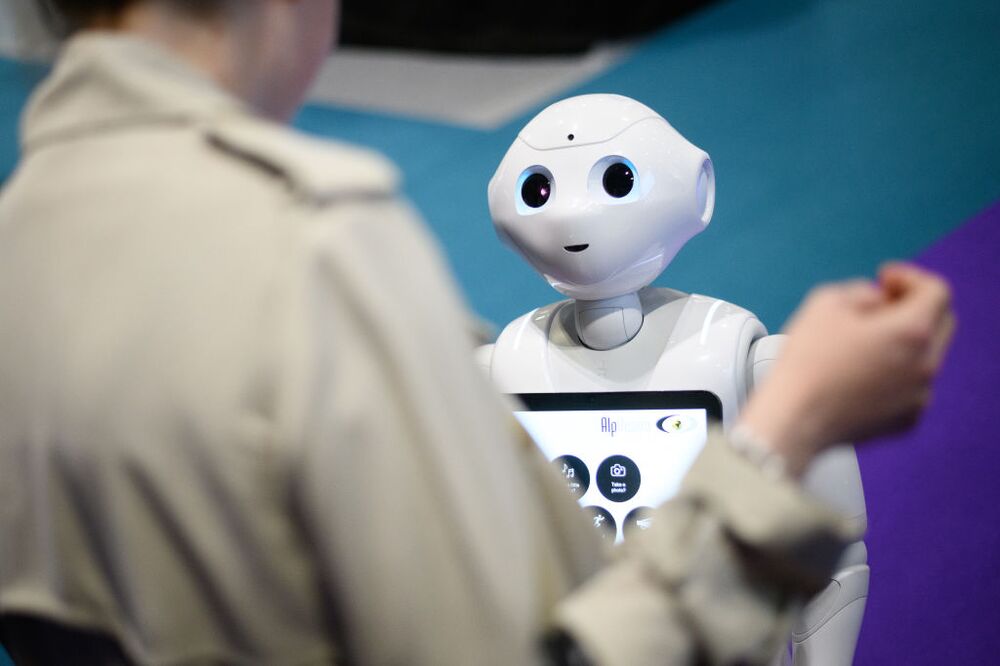
5 Important Ways Jobs Will Change In The 4th Industrial Revolution

Rather than succumb to the doomsday predictions that “robots will take over all the jobs,” a more optimistic outlook is one where humans get the opportunity to do work that demands their creativity, imagination, social and emotional intelligence, and passion. Individuals will need to act and engage in lifelong learning, so they are adaptable when the changes happen. The lifespan for any given skill set is shrinking, so it will be imperative for individuals to continue to invest in acquiring new skills. The shift to lifelong learning needs to happen now because the changes are already happening. In addition, employees will need to shape their own career path. Gone are the days when a career trajectory is outlined at one company with predictable climbs up the corporate ladder. Therefore, employees should pursue a diverse set of work experiences and take the initiative to shape their own career paths. Individuals will need to step into the opportunity that pursuing your passion provides rather than shrink back to what had resulted in success in the past.
Network capacity planning in the age of unpredictable workloads

To plan realistic capacity requirements, formal network engineers dive into the complex math of the Erlang B formula, and if you are inclined to learn it, check out the older book James Martin's Systems Analysis for Data Transmission. However, there are also easier rules of thumb. As a connection congests, it increases the risk of delay and packet loss in a nonlinear fashion. This tenet contributes to network capacity planning fundamentals. Problems ramp up slowly until the network reaches about 50% utilization; issues rise rapidly after that threshold. At 70% utilization, delay doubles, for example. Keep the connection, or gateway utilization, around the 50% level to avoid congestion during peaks. Unexpected traffic peaks often occur when a single transaction launches a complex multicomponent workflow and especially when traffic changes because of failover or scaling. The most significant network capacity planning decision is how to size the DCI network. It is the hub of all workflows, into and out of the cloud and to and from workers and internet users. The DCI network must never become congested.
The lost art of ethical decision making

Ethics need not be wildly complex, nor must you exemplify saintly behaviors or be infallible in your decision making. As you lead your teams, try to apply these guidelines. Implement the "newspaper test": When faced with a complex decision, especially one in which you're faced with a variety of bad options, imagine that an account of your decision and the behaviors and process that got you there were published in a front-page newspaper story. Would you be a sympathetic character who weighed the various options, treated the parties fairly, and respected your obligations as a leader, even though the outcome wasn't all rainbows and unicorns, or would you be portrayed as slyly manipulating circumstances for your benefit? Perhaps one of the most challenging concepts is that of "fairness," particularly around the human tendency to conflate fairness of a process with fairness of outcome. The former should be the goal of your own ethical standards, as that provides all parties with similar consideration, information, and standards. Where trouble arises is when you attempt to create a "fair" outcome that causes you to treat various parties and factors differently to justify an end result.
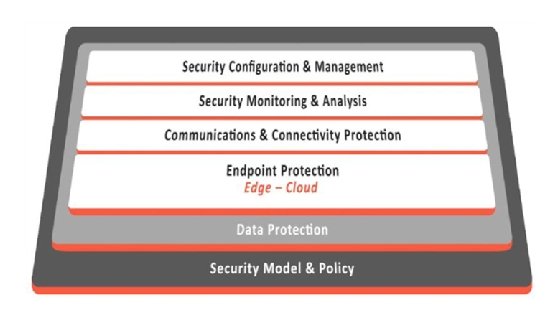
Protecting the edge of IoT as adoption rates for the technology grow

You can see the problem: with the rapid increase of more edge devices, the risk of a data breach only multiplies for enterprises. Last year, for example, there were 1,244 data breaches, exposing 446.5 million records. This not only leads to significant business obstacles, but breaches also come at a high price — Ponemon Institute estimates the average cost of a data breach to exceed $3.5 million. This broader array of environments, coupled with the prevalence of data breaches, make it critical for enterprises to secure their computing infrastructure. “With the growth of IoT and the rising cost of data breaches, enterprises need a secure computing infrastructure more than ever,” confirms Damon Kachur, vice president, IoT Solutions, Sectigo. To meet this demand, Sectigo — the commercial Certificate Authority (CA) — have entered into a secure edge computing technology pact with NetObjex — an intelligent automation platform for tracking, tracing and monitoring digital assets using AI, blockchain, and IoT.
Companies with zero-trust network security move toward biometric authentication

"Fundamentally we've all figured out that you can't trust everything just because it's on the inside of your firewall; just because it's on your network," says Wendy Nather, director of Advisory CISOs at Duo Security, a multi-factor authentication (MFA) solutions provider that is now part of Cisco Systems. "So, if you agree with that, the question becomes: What are we trusting today that we really shouldn't be trusting and what should we be verifying even more than we have been? The answer is really that you have to verify users more carefully than you have before, you have to verify their devices and you need to do it based on the sensitivity of what they're getting access to, and you also need to do it frequently, not just once when you let them inside your firewall." "You should be checking early and often and if you're checking at every access request. you're more likely to catch things that you didn't know before," Nather says.
Lateral phishing used to attack organisations on global scale

Out of the organisations targeted by lateral phishing, more than 60% had multiple compromised accounts. Some had dozens of compromised accounts that sent lateral phishing attacks to additional employee accounts and users at other organisations. In total, researchers identified 154 hijacked accounts that collectively sent hundreds of lateral phishing emails to more than 100,000 unique recipients. A recent benchmarking report by security awareness training firm KnowBe4 shows that the average phish-prone percentage across all industries and sizes of organisations at 29.6% – up 2.6% since 2018. Large organisations in the hospitality industry have the highest phish-prone percentage (PPP) of 48%, and are therefore most likely to fall victim to a phishing attack, while the transportation industry is at the lowest risk, with large organisations in the sector scoring a PPP of just 16%. Because lateral phishing exploits the implicit trust in the legitimate accounts compromised, these attacks ultimately lead to increasingly large reputational harm for the initial victim organisation, the researchers said.
Quote for the day:
"It is not enough to have the right ingredients, you must bake the cake." -- Tim Fargo