Artificial intelligence: Germans see no reason to fear robot coworkers
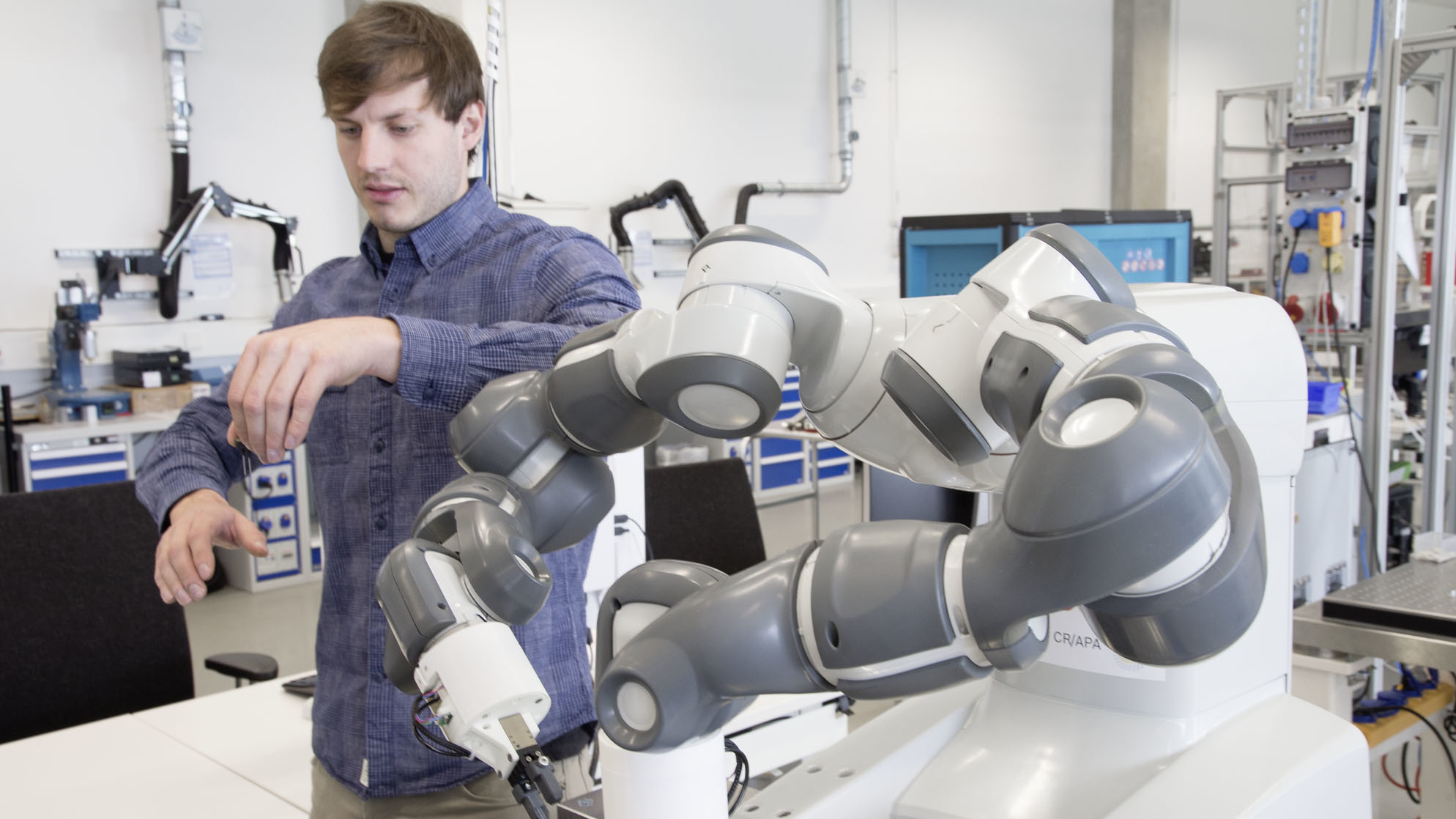
One example of how AI can benefit people is automated driving. Bosch is striving to make road transportation emissions-free, accident-free, and stress-free. With nine out of ten accidents are currently attributable to human error, smart technology could use AI to prevent many of these from happening in the first place. Connected manufacturing is another banner field for AI. In a smart factory, people and machines will work together as an intelligent team. Robots will relieve people of strenuous and dangerous tasks and learn from experience. This will reduce people’s burden. The Bosch survey found that many Germans could imagine being able to accept this situation. Two-thirds of respondents – 67 percent – believe that manufacturing and mobility are going to benefit greatly from artificial intelligence. They are also open to working with a robot if it takes over routine chores. Half of all respondents could well imagine such a situation, and would above all devote the free time gained to social or creative activities.
Women in Blockchain: CryptoWendyO talks about her motivation
There’s so much negative energy directed at crypto from mainstream financial institutions because the public “doesn’t like change.” “Because crypto is intangible, it’s hard for the masses to understand. “We saw this with the internet and credit cards. If you notice, the group of folks present when credit cards became mainstream still write cheques – as time progresses, so will the masses.” The recent falls after the hard fork mean the market – which is basic supply and demand – needs a “catalyst to bring in new money.” WendyO says: “There’s nothing we can do individually to stop negative price action. What we can do is support one another and continue to support the entrepreneurs building in the space. They are the key to mass adoption. “Once Blockchain projects are seamless and make life easier for the masses, they will come.” Asked by me why people are panicking so much, she believes: “Price impacts the human psyche so much. People are entering into positions without proper risk management and education.

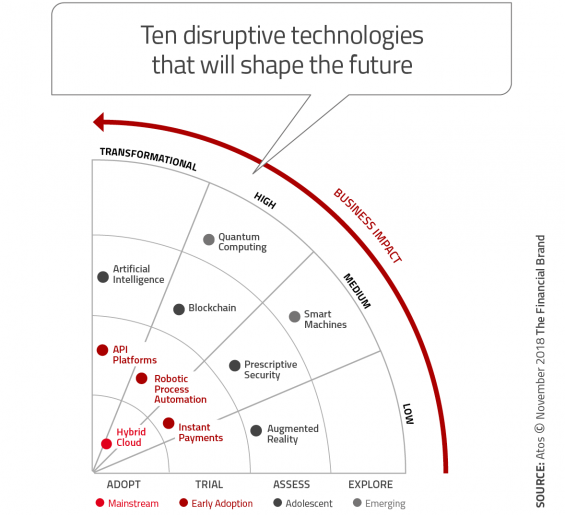
We all know how the media and the film industry are overhyping AI with androids and over-intelligent systems. Some computer pioneers, Alan Turing (you may want to watch The Imitation Game to appreciate the legend he is) at the forefront, did set off on projects with a view to making machines that think. Turing, however, did realise that this would be abysmally difficult, and in 1950 proposed: Instead of trying to produce a programme to simulate the adult mind, why not rather try to produce one which simulates the child’s? If this were then subjected to an appropriate course of education, one would obtain the adult brain. This idea grew on to become Deep Learning. Fast forward to 2018: we have, and are still gathering, massive amounts of data. We have and are still developing more and more advanced algorithms. But do we have the hardware to crunch all those calculations within reasonable time? And if we do, can it be done without having all those GPUs cause another global warming on their own by literally heating up from all the processing?
Forget Robots, Blockchain Technology May Be the Real Threat to Your Job

Traditionalists say this is a necessary component of an organization, freeing senior management to think strategically and move away from the day-to-day, while building a talent bench of the next generation of senior managers. Detractors ask what a middle manager actually adds to the bottom line, pointing to an unclear or difficult to define return on investment. The truth, as is often the case, lies somewhere in the middle. But it may not matter. Many organizations have clear, tangible, quantifiable key performance indicators for day-to-day functions, like sales closed or widgets shipped. With the advent of smart contracts on blockchain, it’s clear: robots aren’t the only ones gunning for your job. Blockchain technology is too. A smart contract is code designed to facilitate, verify or enforce performance of set terms. ... Notably, this is not a far-off concept—it’s something that, in many situations, could be implemented tomorrow.

CAOs often find themselves doing this heavy lifting with a limited sphere of influence. They typically do not have the profit-and-loss or revenue accountability that would grant them due power in the organization. Moreover, like chief marketing officers a decade ago, CAOs need—but typically lack—a true seat at the C-suite table, placing them at a disadvantage when trying to obtain adequate funding or resources to power the analytics agenda. ... Arguably, none of the previous CAO personas could succeed in today’s landscape. We’ve entered an era that requires a new CAO persona—the Catalyst—who embraces a style of leadership geared toward addressing the current demands, roadblocks, and scrutiny most companies face today when it comes to deploying AI and advanced analytics at scale. Catalysts approach their role very differently than did past CAO personas, in ways that those with more scientific and technical career backgrounds might not have ever done before.
How voice biometrics catches fraudsters

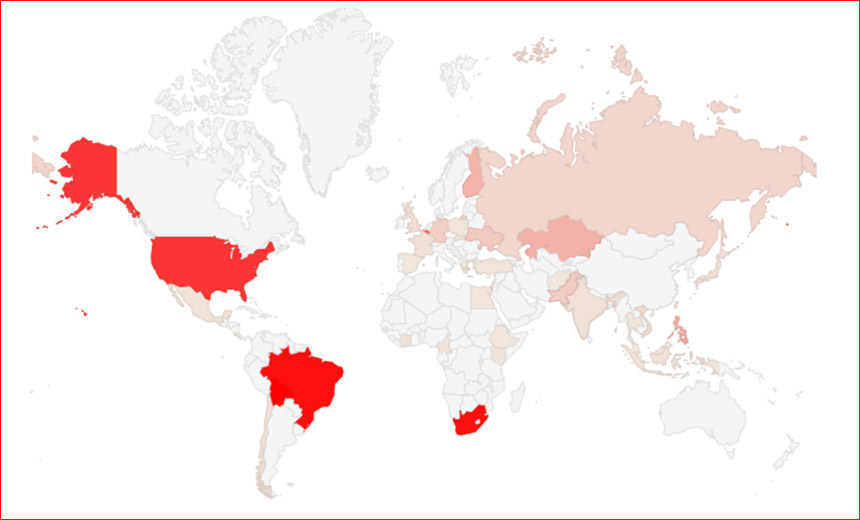
According to Costain, it is relatively easy for the system to identify a new voice. Often, a fraudster will phone in to check whether stolen credentials are valid, but in certain cases, the fraudster may scam the customer to obtain these credentials. “It’s a bit like epidemiology with Patient Zero,” he said. The same voice may try to access multiple accounts, which would signal an attempted fraud. RBS has also been compiling a database of evidence, which Costain said has led to a few police arrests of people who have made fraudulent calls. Over the next six months, the bank will have technology to enable customers to determine whether a call they receive from the bank is genuine, he said. Experian’s Global fraud report 2018 found that customers want to be recognised, while businesses want to address the growing fraud they are experiencing.
AI and Neuroscience: A virtuous circle

Another key challenge in contemporary AI research is known as transfer learning. To be able to deal effectively with novel situations, artificial agents need the ability to build on existing knowledge to make sensible decisions. Humans are already good at this - an individual who can drive a car, use a laptop or chair a meeting are usually able to cope even when confronted by an unfamiliar vehicle, operating system or social situation. Researchers are now starting to take the first steps towards understanding how this might be possible in artificial systems. For example, a new class of network architecture known as a “progressive network” can use knowledge learned in one video game to learn another. The same architecture has also been shown to transfer knowledge from a simulated robotic arm to a real-world arm, massively reducing the training time. Intriguingly, these networks bear some similarities to models of sequential task learning in humans. These tantalising links suggest that there are great opportunities for future AI research to learn from work in neuroscience.
6 ways to include dark data in analytic strategies

The goal for CIOs is simple: Find out what data is under company management, but that it possibly didn't know that it had. Then, develop a strategic data plan with executives that addresses what do with this data so that it delivers its highest value to the company. ... As soon as it is determined that certain areas of data are useful, begin to digitalize and exploit it for value so you can get it working for you. ... Outside data sources can enhance the value of data you already have under management. A prime example is the monitoring of Greenland's ice pack. If you monitor climate change and are concerned about the pace of global warming, you can study historical photos of Greenland's land mass from decades ago. Comparison of Greenland against how it was decades ago to how it is today can demonstrate both the impact and progression of global warming. ... As paper-based forms of unstructured data are digitalized, it is essential for data to undergo quality assurance checks for data integrity and quality.
Generative Adversarial Networks (GANs) – The Basics You Need To Know

So as name suggest it is called as Adversarial Networks because this is made up of two neural networks. Both neural networks are assigned different job role i.e. contesting with each other. Neural Network one is called as Generator, because it generate new data instances. Other neural net is called as Discriminator, evaluates work for first neural net for authenticity. The cycle continue to obtain accuracy or near perfection results. ... To understand “Generative Adversarial Networks”, its very important to differentiate between supervised learning and unsupervised learning. ... GAN’s are fairly new architecture in the deep learning domain. They fall under unsupervised neural network category. The performance measure is far better then traditional neural nets. When we use google search engine we use GANs at time of typing, what we want to search.
Distributed Machine Learning Is The Answer To Scalability And Computation Requirements

It was this challenge to handle large-scale data due to scalability and efficiency of learning algorithms with respect to computational and memory resources that gave rise to distributed ML. For example, if the computational complexity of the algorithm outpaces the main memory then the algorithm will not scale well and will not be able to process the training data set or will not run due to memory restrictions. Distributed ML algorithms rose to handle very large data sets and develop efficient and scalable algorithms with regard to accuracy and to requirements of computation. Distributed ML algorithms are part of large-scale learning which has received considerable attention over the last few years, thanks to its ability to allocate learning process onto several workstations — distributed computing to scale up learning algorithms. It is these advances which make ML tasks on big data scalable, flexible and efficient.
Quote for the day:
"You can't just wish change; you have to live the change in order for it to become a reality." -- Steve Maraboli