How Financial Institutions Can Put Risk Management Back in the Driver’s Seat
The benefits of putting the business clearly in charge of risk management — and holding it accountable — are significant. First, holding the first line accountable for risk management aligns the interests of internal revenue generators with those of the overall firm. When first-line salespeople do their own risk generation “driving,” they gain an understanding of their firm’s position and reputation that they otherwise might not get. They are thus less likely to try to on-board a questionable client or put together loan proposals that may be rejected. In general, the business needs to be clearly accountable for managing the risks it takes in pursuit of its objectives. A system of first-line front-seat drivers also encourages people to keep their eye out for risks wherever they pop up, rather than relying on the oversight specialist — the backseat driver — to point them out. This improves performance by allowing the business to spot some risks sooner, manage them more nimbly, and react more quickly when things do go wrong.

Too many business executives view the analytics transformation too narrowly: They tend to view it as centering on tools or being driven by the hiring of "big data" analysts or machine learning expertise. Almost without exception, every successful analytics transformation that I've seen or experienced has started at the top - this transformation is as much, perhaps, even more, driven by a cultural change as it is by your hiring of new resources and technical expertise. Even today, however, too many business leaders and executives tend to be intimidated by analytics and math. My guidance to you (and you know who you are) is to get educated - fast. That does not mean that you have to get the equivalent of a Masters Degree in operations research or machine learning. It does mean seeking out an expert who can frame these capabilities in the language and the vernacular of a senior executive. This is the most perilous part of the journey because too many senior executives delegate this transformation to lower levels of the organization where it gets lost in a sea of other priorities.
The Future of the Cloud Depends on Magnetic Tape

Although the century-old technology has disappeared from most people’s daily view, magnetic tape lives on as the preferred medium for safely archiving critical cloud data in case, say, a software bug deletes thousands of Gmail messages, or a natural disaster wipes out some hard drives. The world’s electronic financial, health, and scientific records, collected on state-of-the-art cloud servers belonging to Amazon.com, Microsoft, Google, and others, are also typically recorded on tape around the same time they are created. Usually the companies keep one copy of each tape on-site, in a massive vault, and send a second copy to somebody like Iron Mountain. Unfortunately for the big tech companies, the number of tape manufacturers has shrunk over the past three years from six to just two—Sony Corp. and Fujifilm Holdings Corp.—and each seems to think that’s still one too many. The Japanese companies have said the tape business is a mere rounding error as far as they’re concerned, but each has spent millions of dollars arguing before the U.S. International Trade Commission to try to ban the other from importing tapes to America.
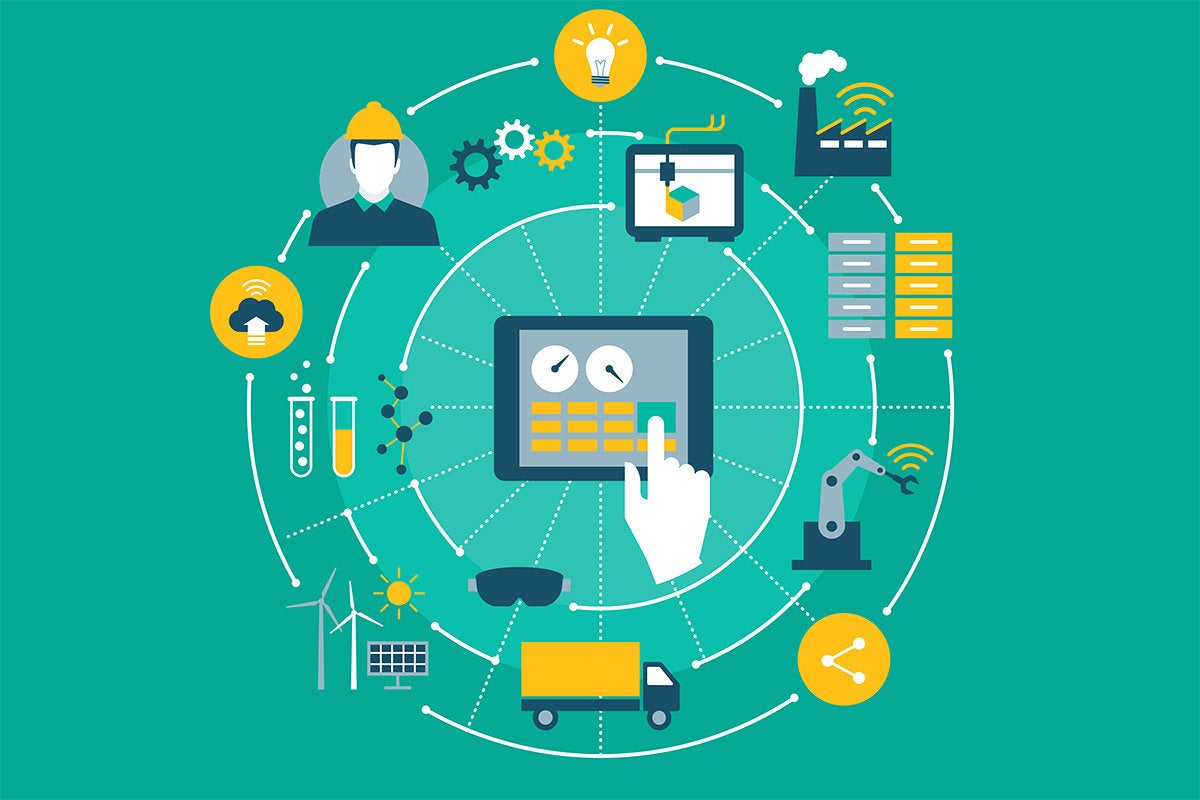
Solving the cloud infrastructure misconfiguration problem
The threats to cloud infrastructure are automated, so automated remediation is a requirement to effectively manage misconfiguration risk. His advice to CISOs is to set up a team that includes developers who understand cloud APIs and can automate every repetitive aspect of cloud security, starting with cloud configuration. “In order to be effective, the CISO needs to view their security team as an internal tool vendor in the cloud ecosystem. Development teams need support from security to move quickly, but also require good guard rails and feedback for how to do cloud securely,” he opines. “This security automation team led by the CISO needs to work closely with development teams to establish known-good configuration baselines using a whitelist approach that conforms with compliance and security policy. Once you have a known-good baseline, you can automate the remediation process for misconfiguration without running the risk of false positives leading to bad changes that can cause system downtime events.”
Quantum Computing: Why You Should Pay Attention

As databases continue to grow in size, this improvement can make it more feasible to handle the large volumes of data expected to come online in the coming years and decades as we reach physical limits in storage device latencies. Another practical advantage lies in our understanding of the world. Simulating quantum effects is notoriously difficult using the computers we rely on today, as the very fundamentals of quantum mechanics are vastly at odds with today’s devices. Using quantum computers, simulating these effects will be far simpler, allowing us to better unravel the mysteries of quantum mechanics. Even when quantum computing becomes common, it’s difficult to envision it completely replacing traditional computer devices. The types of applications at which quantum computers excel don’t seem to have much practical use for typical computer users. Furthermore, it will take some time for quantum computers to become smaller and more affordable, and there may be barriers preventing its widespread use.
Authentication Bypass in libSSH Leaves Servers Vulnerable
“Careful reading of code for the affected libSSH library indicated that it was possible to bypass authentication by presenting to the server an SSH2_MSG_USERAUTH_SUCCESS message in place of the SSH2_MSG_USERAUTH_REQUEST message which the server would expect to initiate authentication. The SSH2_MSG_USERAUTH_SUCCESS handler is intended only for communication from the server to the client,” an advisory by Peter Winter-Smith of NCC Group, who discovered the bug, says. In other words, an attacker can connect to any vulnerable server, without authentication, just by sending one message to the server. ... “Not all libSSH servers will necessarily be vulnerable to the authentication bypass; since the authentication bypass sets the internal libSSH state machine to authenticated without ever giving any registered authentication callbacks an opportunity to execute, servers developed using libSSH which maintain additional custom session state may fail to function correctly if a user is authenticated without this state being created,” the advisory says.
Learn Why Doctors Look To Data To Increase Patient Engagement

We’re positively swimming in data. But all that noise stands a good chance of confusing or distracting patients from their ultimate goal of ongoing good health if doctors and patients don’t come to the table together with a plan and a common understanding of which data points are meaningful in context and which are not. There’s no doubt anymore: Big data is going to revolutionize the way we administer health care throughout the world and help us achieve financial savings. But as doctors look to leverage modern tools for interacting with and sharing patient health data, there are several factors to remember and several key advantages worth checking out. Here’s a rundown. Regrettably, we still lack a cure for many chronic diseases. Therefore, doctors and their patients must instead “manage” these conditions. It’s possible to live a full and active life while undergoing treatment for severe diseases and conditions, but only with the right levels of vigilance and engagement. Patients with chronic illnesses must maintain their motivation, their attention to treatment and medication schedules and their general knowledgeability about their condition.
Wärtsilä Opens World's First International Maritime Cyber Centre

“Cyber is such a critical topic to all players in marine. Taking stewardship in something as important as this, shows that Wärtsilä is committed to transform and digitalize the marine industry. This is the next step in our Smart Marine vision and supports our Oceanic Awakening and Sea20 initiatives,” says Marco Ryan, Chief Digital Officer at Wärtsilä. “There are three main drivers for the maritime industry to collaborate in improving our cyber resiliency: the vast attack surface that the maritime industry offers to cyber criminals; the inclusion of maritime into the critical national infrastructure of nation states and the pending cyber security regulation by the International Maritime Organisation in 2021,” says Mark Milford, Vice President, Cyber Security at Wärtsilä. The MCERT is an international cyber intelligence and incident support platform enhancing cyber resilience for the entire maritime ecosystem. It provides international intelligence feeds, advice and support, including real-time assistance to members on cyber attacks and incidents, and a Cyber Security Reporting Portal (CSRP) for its members.
Arm’s Neoverse will be the infrastructure for a trillion intelligent devices

Arm’s Neoverse intellectual property will take advantage of high-end manufacturing equipment in chip factories. The Ares platform will debut in 2019 with 30 percent per generation performance improvements, Henry said. The designs will be flexible for customer purposes and security will be a crucial part of the platform, Henry said. Ares will be built on seven-nanometer circuitry in the newest chip factories. Follow-up chips include the Zeus at seven nanometers and Poseidon at 5 nanometers. The Arm Neoverse will include advanced processor designs as well as solutions and support for hardware, software, tools, and services. The company announced the platform at the Arm TechCon event in San Jose, California. “Arm has been more successful in infrastructure than many knew. This makes sense as many networking and storage systems have Arm-based chips inside, albeit with smaller cores,” said Patrick Moorhead, analyst at Moor Insights & Strategy, in an email.
What Innovative CEOs and Leaders Need to Know about AI

The authors view AI as “performing tasks, not entire jobs.” Out of the 152 AI projects, 71 were in the automation of digital and physical tasks, 57 were using algorithms to identify patterns for business intelligence and analytics, and 24 were for engaging employees and customers through machine learning, intelligent agents, and chatbots. In the Harvard Business Review article, a 2017 Deloitte survey of 250 executives who were familiar with their companies’ AI initiatives, revealed that 51 percent responded that the primary goals were to improve existing products. 47 percent identified integrating AI with existing processes and systems as a major obstacle. ... Early adopters of AI in the enterprise are reporting benefits — 83 percent indicated their companies have already achieved “moderate (53 percent) or substantial (30 percent) economic benefits. 58 percent of respondents are using in-house resources versus outside expertise to implement AI, and 58 percent are using AI software from vendors.
Quote for the day:
"Leadership is a potent combination of strategy and character. But if you must be without one, be without the strategy." -- Norman Schwarzkopf