Quote for the day:
“There is only one thing that makes a dream impossible to achieve: the fear of failure.” -- Paulo Coelho
7 signs your cybersecurity framework needs rebuilding
 The biggest mistake, Pearlson says, is failing to recognize that the current
plan is out of date or simply not working. Breaches happen, but that doesn’t
always mean your cyber framework needs rebuilding. It does, however, indicate
that the framework needs to be rethought and redesigned. ... “If your
framework hasn’t kept pace with evolving threats or business needs, it’s time
for a rebuild.” Cyber threats are always evolving, so staying proactive with
regular reviews and fostering a culture of cybersecurity awareness will help
catch issues before they become crises, Bucher says. ... “The cybersecurity
landscape has evolved rapidly, especially with the rise of generative AI —
your framework should reflect these shifts.” McLeod recommends a complete a
biannual framework review combined with a cursory review during the gap years.
“This helps to ensure that the framework stays aligned with evolving threats,
business changes, and regulatory requirements.” Ideally, security leaders
should always have their security framework in mind while maintaining a rough,
running list of areas that could be improved, streamlined, or clarified,
McLeod suggests. ... If an organization is stuck in a cycle of continually
chasing alerts and incidents, as well as reporting events after the fact
instead of performing predictive threat assessments, data analysis, and
forward planning, it’s time for a change, Baiati advises.
The biggest mistake, Pearlson says, is failing to recognize that the current
plan is out of date or simply not working. Breaches happen, but that doesn’t
always mean your cyber framework needs rebuilding. It does, however, indicate
that the framework needs to be rethought and redesigned. ... “If your
framework hasn’t kept pace with evolving threats or business needs, it’s time
for a rebuild.” Cyber threats are always evolving, so staying proactive with
regular reviews and fostering a culture of cybersecurity awareness will help
catch issues before they become crises, Bucher says. ... “The cybersecurity
landscape has evolved rapidly, especially with the rise of generative AI —
your framework should reflect these shifts.” McLeod recommends a complete a
biannual framework review combined with a cursory review during the gap years.
“This helps to ensure that the framework stays aligned with evolving threats,
business changes, and regulatory requirements.” Ideally, security leaders
should always have their security framework in mind while maintaining a rough,
running list of areas that could be improved, streamlined, or clarified,
McLeod suggests. ... If an organization is stuck in a cycle of continually
chasing alerts and incidents, as well as reporting events after the fact
instead of performing predictive threat assessments, data analysis, and
forward planning, it’s time for a change, Baiati advises. Your Million-Dollar IIoT Strategy is Being Sabotaged by Hundred-Dollar Radios
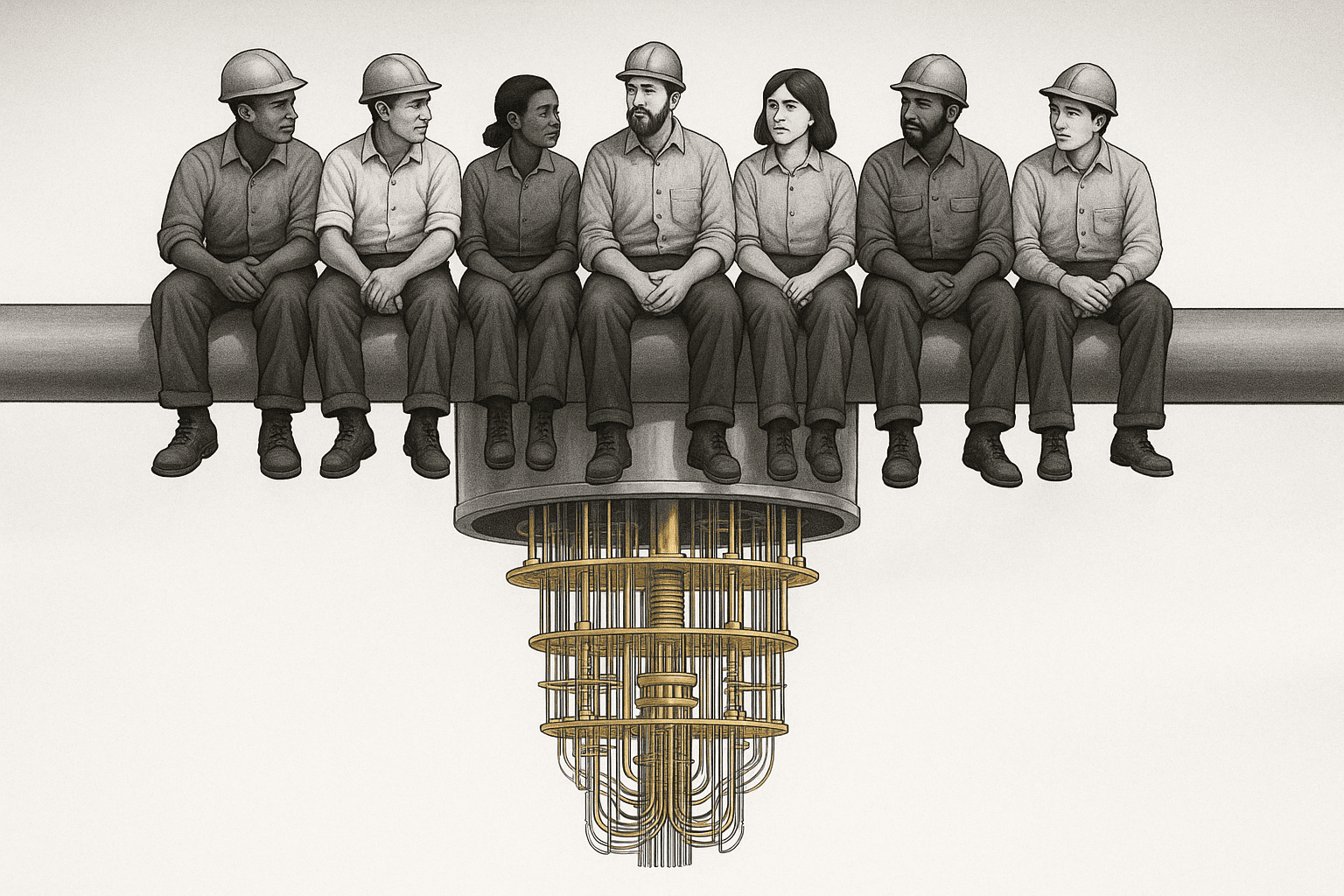
 The ambition is clear: to create hyper-efficient, data-driven operations in a
market expected to exceed $1.6 billion by 2030. Yet, a fundamental
paradox lies at the heart of this transformation. While we architect complex
digital twins and deploy sophisticated AI models, the foundational tools
entrusted to our most valuable asset—the frontline workforce—are often decades
old, disconnected, and failing at an alarming rate. ... Data shows that one in
four organizations loses more than an entire day of productivity every month
simply dealing with broken technology. The primary culprits are as predictable
as they are preventable: nearly half of workers cite battery problems (48.4%)
and physical damage (46.8%) as the most common causes of failure. ... While
conversations about this crisis often focus on pay and career paths, Relay’s
research reveals a more immediate, tangible cause: the daily frustration of
using broken tools. 1 in 4 frontline workers already feel their equipment is
second-class compared to what their corporate counterparts use, and a
staggering 43% of workers saying they’d be less likely to quit if guaranteed
access to modern, automatically upgraded devices. ... Beyond reliability, it’s
important to address the data black hole created by legacy, disconnected
tools. Every day, frontline teams generate thousands of hours of spoken
communication—a rich stream of unstructured data filled with maintenance
alerts, safety concerns, and process bottlenecks.
The ambition is clear: to create hyper-efficient, data-driven operations in a
market expected to exceed $1.6 billion by 2030. Yet, a fundamental
paradox lies at the heart of this transformation. While we architect complex
digital twins and deploy sophisticated AI models, the foundational tools
entrusted to our most valuable asset—the frontline workforce—are often decades
old, disconnected, and failing at an alarming rate. ... Data shows that one in
four organizations loses more than an entire day of productivity every month
simply dealing with broken technology. The primary culprits are as predictable
as they are preventable: nearly half of workers cite battery problems (48.4%)
and physical damage (46.8%) as the most common causes of failure. ... While
conversations about this crisis often focus on pay and career paths, Relay’s
research reveals a more immediate, tangible cause: the daily frustration of
using broken tools. 1 in 4 frontline workers already feel their equipment is
second-class compared to what their corporate counterparts use, and a
staggering 43% of workers saying they’d be less likely to quit if guaranteed
access to modern, automatically upgraded devices. ... Beyond reliability, it’s
important to address the data black hole created by legacy, disconnected
tools. Every day, frontline teams generate thousands of hours of spoken
communication—a rich stream of unstructured data filled with maintenance
alerts, safety concerns, and process bottlenecks. Ask the Experts: Validate, don't just migrate
 "Refactoring code is certainly a big undertaking. And if you start before you
have good hygiene and governance, then you're just setting yourself up for
failure. Similarly, if you haven't tagged properly, you have no way to
attribute it to the project, and that becomes a cost problem." ... "If you do
conclude [that migration is necessary], then you really must make sure the
application is architected right. A lot of times, these workloads weren't
designed for the cloud world, so you must adapt them and deliberately
architect them for a cloud workload. "[To prepare a mission-critical
application], it's key to look at the appropriateness, operating system [and]
licenses. Sometimes, there are licenses tied to CPUs or other things that
might introduce issues for you as well, so regression, latency and performance
testing will be mandatory. ... "[IT leaders must also understand] the risks
and costs associated with taking things into the cloud, and the pros and cons
of that versus leaving it alone. Because old stuff, whether it was [procured]
yesterday or five years ago, is inherently going to be vulnerable from a
cybersecurity standpoint. Risk No. 2 is interoperability and compatibility,
because old stuff doesn't talk to new stuff. And the third one is
supportability, because it's hard to find old people to support old systems.
... "Sometimes, people have the false sense that if it's in cloud, then I'm
all set. Everything is available, and everything is highly redundant. And it
is, if you design [the application] with those things in mind.
"Refactoring code is certainly a big undertaking. And if you start before you
have good hygiene and governance, then you're just setting yourself up for
failure. Similarly, if you haven't tagged properly, you have no way to
attribute it to the project, and that becomes a cost problem." ... "If you do
conclude [that migration is necessary], then you really must make sure the
application is architected right. A lot of times, these workloads weren't
designed for the cloud world, so you must adapt them and deliberately
architect them for a cloud workload. "[To prepare a mission-critical
application], it's key to look at the appropriateness, operating system [and]
licenses. Sometimes, there are licenses tied to CPUs or other things that
might introduce issues for you as well, so regression, latency and performance
testing will be mandatory. ... "[IT leaders must also understand] the risks
and costs associated with taking things into the cloud, and the pros and cons
of that versus leaving it alone. Because old stuff, whether it was [procured]
yesterday or five years ago, is inherently going to be vulnerable from a
cybersecurity standpoint. Risk No. 2 is interoperability and compatibility,
because old stuff doesn't talk to new stuff. And the third one is
supportability, because it's hard to find old people to support old systems.
... "Sometimes, people have the false sense that if it's in cloud, then I'm
all set. Everything is available, and everything is highly redundant. And it
is, if you design [the application] with those things in mind.
Heineken CISO champions a new risk mindset to unlock innovation
Starting as an auditor and later leading a cyber defense team. It’s easy to
fall into the black-and-white trap of being the function that always says “no”
or speaks in cryptic tech jargon. It’s a scary world out there with so many
attacks happening in every industry. The classical reaction of most security
professionals is to tighten defences and impose even more rules. ... CISOs
need to shift the mindset from pure compliance to asking: How does our cyber
strategy support the business and its values? What calculated risks do we want
the business to take? Where do we need their attention and help to embed
security into the DNA of our people and our company? ... Be visible and
approachable. Share the lessons that shaped you as a leader, what worked, what
didn’t, and the principles that guide your decisions. I’m passionate about
building diverse teams where everyone gets the same opportunities, no matter
age, gender, or background. Diversity makes us stronger, and when there’s
trust and openness, it sparks mentoring, coaching, and knowledge sharing. Make
coaching and mentoring non-negotiable, and carve out time for it. It’s easy to
push aside when you’re busy putting out security fires, but neglecting
people’s growth and well-being is a big miss. Be authentic and vulnerable,
walk the talk. Share the real stories, including failures and what made you
stronger. Too often, people focus only on titles, certifications, and tech
skills.
Data-Driven Enterprise: How Companies Turn Data into Strategic Advantage
 A data-driven enterprise is not defined by the number of dashboards or
analytics tools it owns. It’s defined by its ability to turn raw information
into intelligent action. True data-driven organizations embed data thinking
into every level of decision-making from boardroom strategy to day-to-day
operations. ... A modern data architecture is not a single platform, but
an interconnected ecosystem designed to balance agility, governance, and
scalability. ... As organizations mature in their data journey, they are
moving away from rigid, centralized models that rely on a single source of
truth. While centralization once ensured control, it often created bottlenecks
slowing down innovation and limiting agility. ... We are entering an era
of data agents self-learning systems capable of autonomously detecting
anomalies, assessing risks, and forecasting trends in real time. These
intelligent agents will soon become the invisible workforce of the enterprise,
operating across domains: predicting supply chain disruptions, optimizing IT
performance, personalizing customer journeys, and ensuring compliance through
continuous monitoring. Their actions will reshape not only operations but also
how organizations think about governance, accountability, and human oversight.
For architects, this shift represents both a challenge and an extraordinary
opportunity. The role is evolving from that of a data custodian focused on
structure and governance to an ecosystem designer who engineers environments
where data and AI can coexist, learn, and continuously create value.
A data-driven enterprise is not defined by the number of dashboards or
analytics tools it owns. It’s defined by its ability to turn raw information
into intelligent action. True data-driven organizations embed data thinking
into every level of decision-making from boardroom strategy to day-to-day
operations. ... A modern data architecture is not a single platform, but
an interconnected ecosystem designed to balance agility, governance, and
scalability. ... As organizations mature in their data journey, they are
moving away from rigid, centralized models that rely on a single source of
truth. While centralization once ensured control, it often created bottlenecks
slowing down innovation and limiting agility. ... We are entering an era
of data agents self-learning systems capable of autonomously detecting
anomalies, assessing risks, and forecasting trends in real time. These
intelligent agents will soon become the invisible workforce of the enterprise,
operating across domains: predicting supply chain disruptions, optimizing IT
performance, personalizing customer journeys, and ensuring compliance through
continuous monitoring. Their actions will reshape not only operations but also
how organizations think about governance, accountability, and human oversight.
For architects, this shift represents both a challenge and an extraordinary
opportunity. The role is evolving from that of a data custodian focused on
structure and governance to an ecosystem designer who engineers environments
where data and AI can coexist, learn, and continuously create value.10 benefits of an optimized third-party IT services portfolio
 By entrusting day-to-day IT operations to trusted providers, organizations can
reallocate internal resources toward higher-value initiatives such as digital
transformation, automation, and product innovation. This accelerates adoption
of emerging technologies, and allows internal teams to deepen business
expertise, strengthen cross-functional collaboration, and focus on driving
growth where it matters most. ... A well-structured third-party IT services
portfolio can provide flexibility to scale up or down based on business needs.
This is particularly valuable for CEOs who need to adapt to changing market
conditions and seize growth opportunities. Securing talent in the market today
is challenging and time consuming, so tapping into the talent pools of your
strategic IT services partner base allows organizations to leverage their
bench strength to fill immediate needs for talent. ... IT service providers
continuously invest in advanced tech and talent development, enabling clients
to benefit from cutting-edge innovations without bearing the full cost of
adoption. As AI, automation, and cybersecurity evolve, providers offer the
subject matter expertise and tools organizations need to stay ahead of
disruption. ... With operational stability ensured through a balance of
internal talent and trusted third parties, CIOs can dedicate more focus to
long-term strategic initiatives that fuel growth and innovation.
By entrusting day-to-day IT operations to trusted providers, organizations can
reallocate internal resources toward higher-value initiatives such as digital
transformation, automation, and product innovation. This accelerates adoption
of emerging technologies, and allows internal teams to deepen business
expertise, strengthen cross-functional collaboration, and focus on driving
growth where it matters most. ... A well-structured third-party IT services
portfolio can provide flexibility to scale up or down based on business needs.
This is particularly valuable for CEOs who need to adapt to changing market
conditions and seize growth opportunities. Securing talent in the market today
is challenging and time consuming, so tapping into the talent pools of your
strategic IT services partner base allows organizations to leverage their
bench strength to fill immediate needs for talent. ... IT service providers
continuously invest in advanced tech and talent development, enabling clients
to benefit from cutting-edge innovations without bearing the full cost of
adoption. As AI, automation, and cybersecurity evolve, providers offer the
subject matter expertise and tools organizations need to stay ahead of
disruption. ... With operational stability ensured through a balance of
internal talent and trusted third parties, CIOs can dedicate more focus to
long-term strategic initiatives that fuel growth and innovation. Modernizing SOCs with Agentic AI and Human-in-the-Loop: A Guide to CISOs
 Traditional SOCs were not built for today’s speed and scale. Alert fatigue,
manual investigations, disconnected tools, and talent shortages all contribute
to the operational drag. Many security leaders are stuck in a reactive loop
with no clear path to improvement. ... Legacy SOCs rely heavily on outdated
technologies and rule-based detection, generating high volumes of alerts, many
of which are false positives, leading to analyst burnout. Analysts are
compelled to manually inspect and triage a deluge of meaningless signals,
making the entire effort unsustainable. ... Before transformation can happen,
one needs to understand where one stands. This can be accomplished with key
benchmarking metrics for SOC performance, such as MTTD (Mean time to detect),
MTTR (Mean time to respond), case closure rates, and tool effectiveness. ...
Agentic AI represents the next evolution of AI-powered cybersecurity, which is
modular, explainable, and autonomous. Through a coordinated system of AI
agents, the Agentic SOC continuously responds and adapts to the evolving
security environment in real time. It is designed to accelerate threat
detection, investigation, and response by 10x, bringing speed, precision, and
clarity to every function of SecOps. Agentic AI is the technology shift that
changes the game. Unlike traditional automation, Agentic AI is
decision-oriented, self-improving, and always operating with human-in-the-loop
for oversight.
Traditional SOCs were not built for today’s speed and scale. Alert fatigue,
manual investigations, disconnected tools, and talent shortages all contribute
to the operational drag. Many security leaders are stuck in a reactive loop
with no clear path to improvement. ... Legacy SOCs rely heavily on outdated
technologies and rule-based detection, generating high volumes of alerts, many
of which are false positives, leading to analyst burnout. Analysts are
compelled to manually inspect and triage a deluge of meaningless signals,
making the entire effort unsustainable. ... Before transformation can happen,
one needs to understand where one stands. This can be accomplished with key
benchmarking metrics for SOC performance, such as MTTD (Mean time to detect),
MTTR (Mean time to respond), case closure rates, and tool effectiveness. ...
Agentic AI represents the next evolution of AI-powered cybersecurity, which is
modular, explainable, and autonomous. Through a coordinated system of AI
agents, the Agentic SOC continuously responds and adapts to the evolving
security environment in real time. It is designed to accelerate threat
detection, investigation, and response by 10x, bringing speed, precision, and
clarity to every function of SecOps. Agentic AI is the technology shift that
changes the game. Unlike traditional automation, Agentic AI is
decision-oriented, self-improving, and always operating with human-in-the-loop
for oversight.3 SOC Challenges You Need to Solve Before 2026
 2026 will mark a pivotal shift in cybersecurity. Threat actors are moving from
experimenting with AI to making it their primary weapon, using it to scale
attacks, automate reconnaissance, and craft hyper-realistic social engineering
campaigns. ... Attackers have mastered evasion. ClickFix campaigns trick
employees into pasting malicious PowerShell commands by themselves. LOLBins
are abused to hide malicious behavior. Multi-stage phishing hides behind QR
codes, CAPTCHAs, rewritten URLs, and fake installers. Traditional sandboxes
stall because they can't click "Next," solve challenges, or follow
human-dependent flows. Result? Low detection rates for the exact threats
exploding in 2025 and beyond. ... Thousands of daily alerts, mostly false
positives. An average SOC handles 11,000 alerts daily, with only 19% worth
investigating, according to the 2024 SANS SOC Survey. Tier 1 analysts drown in
noise, escalating everything because they lack context. Every alert becomes a
research project. Every investigation starts from zero. Burnout hits hard.
Turnover doubles, morale tanks, and real threats hide in the backlog. By 2026,
AI-orchestrated attacks will flood systems even faster, turning alert fatigue
into a full-blown crisis. ... From a financial leadership perspective,
security spending often feels like a black hole: money is spent, but risk
reduction is hard to quantify. SOCs are challenged to justify investments,
especially when security teams seem to be a cost center without clear profit
or business-driving impact.
2026 will mark a pivotal shift in cybersecurity. Threat actors are moving from
experimenting with AI to making it their primary weapon, using it to scale
attacks, automate reconnaissance, and craft hyper-realistic social engineering
campaigns. ... Attackers have mastered evasion. ClickFix campaigns trick
employees into pasting malicious PowerShell commands by themselves. LOLBins
are abused to hide malicious behavior. Multi-stage phishing hides behind QR
codes, CAPTCHAs, rewritten URLs, and fake installers. Traditional sandboxes
stall because they can't click "Next," solve challenges, or follow
human-dependent flows. Result? Low detection rates for the exact threats
exploding in 2025 and beyond. ... Thousands of daily alerts, mostly false
positives. An average SOC handles 11,000 alerts daily, with only 19% worth
investigating, according to the 2024 SANS SOC Survey. Tier 1 analysts drown in
noise, escalating everything because they lack context. Every alert becomes a
research project. Every investigation starts from zero. Burnout hits hard.
Turnover doubles, morale tanks, and real threats hide in the backlog. By 2026,
AI-orchestrated attacks will flood systems even faster, turning alert fatigue
into a full-blown crisis. ... From a financial leadership perspective,
security spending often feels like a black hole: money is spent, but risk
reduction is hard to quantify. SOCs are challenged to justify investments,
especially when security teams seem to be a cost center without clear profit
or business-driving impact.Digital surveillance tools are reshaping workplace privacy, GAO warns
 Privacy concerns intensify when surveillance data feeds into automated systems
that evaluate performance, set productivity metrics, or flag workers for
potential discipline. GAO found that employers often rely on flawed benchmarks
and incomplete measurements. Tools rarely capture the full range of work
performed, such as research, mentoring, reading, or off-screen tasks, and
frequently misinterpret normal behavior as inefficiency. When employers trust
these tools “at face value,” the report notes, workers can be unfairly labeled
unproductive or noncompliant despite doing their jobs well. ... Meanwhile,
past federal efforts to issue guidance on reducing surveillance related harms
such as transparency practices, human oversight, and safeguards against
discriminatory impacts have been rescinded or paused since January by the
Trump administration as agencies reassess their policy priorities. GAO also
notes that existing federal privacy protections are narrow. The Electronic
Communications Privacy Act restricts covert interception of communications,
but it does not cover most forms of digital monitoring, such as keystroke
logging, location tracking, biometric data collection, or algorithmic
productivity scoring. ... The report concludes that while digital surveillance
can improve safety, efficiency, and health monitoring, its benefits depend
wholly on how employers use it.
Privacy concerns intensify when surveillance data feeds into automated systems
that evaluate performance, set productivity metrics, or flag workers for
potential discipline. GAO found that employers often rely on flawed benchmarks
and incomplete measurements. Tools rarely capture the full range of work
performed, such as research, mentoring, reading, or off-screen tasks, and
frequently misinterpret normal behavior as inefficiency. When employers trust
these tools “at face value,” the report notes, workers can be unfairly labeled
unproductive or noncompliant despite doing their jobs well. ... Meanwhile,
past federal efforts to issue guidance on reducing surveillance related harms
such as transparency practices, human oversight, and safeguards against
discriminatory impacts have been rescinded or paused since January by the
Trump administration as agencies reassess their policy priorities. GAO also
notes that existing federal privacy protections are narrow. The Electronic
Communications Privacy Act restricts covert interception of communications,
but it does not cover most forms of digital monitoring, such as keystroke
logging, location tracking, biometric data collection, or algorithmic
productivity scoring. ... The report concludes that while digital surveillance
can improve safety, efficiency, and health monitoring, its benefits depend
wholly on how employers use it.How to avoid becoming an “AI-first” company with zero real AI usage
 A competitor declared they’re going AI-first. Another publishes a case study
about replacing support with LLMs. And a third shares a graph showing
productivity gains. Within days, boardrooms everywhere start echoing the same
message: “We should be doing this. Everyone else already is, and we can’t fall
behind.” So the work begins. Then come the task forces, the town halls, the
strategy docs and the targets. Teams are asked to contribute initiatives. But
if you’ve been through this before, you know there’s often a difference
between what companies announce and what they actually do. Because press
releases don’t mention the pilots that stall, or the teams that quietly revert
to the old way, or even the tools that get used once and abandoned. ... By
then, your company’s AI-first mandate will have set into motion departmental
initiatives, vendor contracts and maybe even some new hires with “AI” in their
titles. The dashboards will be green, and the board deck will have a whole
slide on AI. But in the quiet spaces where your actual work happens, what will
have meaningfully changed? Maybe you'll be like the teams that never stopped
their quiet experiments. ... That’s invisible architecture of genuine
progress: Patient, and completely uninterested in performance. It doesn't make
for great LinkedIn posts, and it resists grand narratives. But it transforms
companies in ways that truly last. Every organization is standing at the same
crossroads right now: Look like you’re innovating, or create a culture that
fosters real innovation.
A competitor declared they’re going AI-first. Another publishes a case study
about replacing support with LLMs. And a third shares a graph showing
productivity gains. Within days, boardrooms everywhere start echoing the same
message: “We should be doing this. Everyone else already is, and we can’t fall
behind.” So the work begins. Then come the task forces, the town halls, the
strategy docs and the targets. Teams are asked to contribute initiatives. But
if you’ve been through this before, you know there’s often a difference
between what companies announce and what they actually do. Because press
releases don’t mention the pilots that stall, or the teams that quietly revert
to the old way, or even the tools that get used once and abandoned. ... By
then, your company’s AI-first mandate will have set into motion departmental
initiatives, vendor contracts and maybe even some new hires with “AI” in their
titles. The dashboards will be green, and the board deck will have a whole
slide on AI. But in the quiet spaces where your actual work happens, what will
have meaningfully changed? Maybe you'll be like the teams that never stopped
their quiet experiments. ... That’s invisible architecture of genuine
progress: Patient, and completely uninterested in performance. It doesn't make
for great LinkedIn posts, and it resists grand narratives. But it transforms
companies in ways that truly last. Every organization is standing at the same
crossroads right now: Look like you’re innovating, or create a culture that
fosters real innovation.












/dq/media/media_files/2025/11/24/medtech-2025-11-24-09-59-39.png)
/articles/adopt-micro-frontends/en/smallimage/adopt-micro-frontends-thumbnail-1762948103768.jpg)