Quote for the day:
“In my experience, there is only one motivation, and that is desire. No reasons or principle contain it or stand against it.” -- Jane Smiley
Synthetic identity blends real and fake data to enable fraud, demanding new protections

Manufactured synthetic identities merge and blend real identity details from
different stolen identities. A real ID number might be paired with a fake name
or address and linked to a deepfaked image that lines up with the hacked
identity data. Manipulated synthetic identities are real identities that alter
an existing identity document. The widespread shift toward digital identity
verification and authentication processes, as illustrated by the EUDI Wallet
scheme, brings new risks: “the transition to digital identity opens up new areas
of attack – precisely because AI-supported fraud scams are likely to become
increasingly sophisticated in the future.” ... “The rate of development of
generative AI presents a problem to not just ensuring a person is who they say
they are, but also to content platforms who need to be sure that the content
added by a user is genuine,” says the paper. “Given the potential risks and
challenges in detecting generative AI, Yoti’s strategy emphasises early
detection at the source, addressing both direct and indirect attack vectors.”
While presentation attacks (PAD) are a “relatively mature and well understood
issue across the verification space,” well defended by effective liveness
detection, more recently popularized injection attacks attempt to bypass
liveness detection by hacking directly into a hardware device or virtual
camera.
When to choose a bare-metal cloud

Bare-metal cloud services, by contrast, provide users with exclusive access to
the underlying physical server hardware: no hypervisor, no virtual machines, no
additional abstraction. This purity means full access to raw compute power, such
as CPU, GPU, and memory resources, without virtualization’s added latency or
restrictions. In essence, bare-metal clouds bridge the gap between the
flexibility of cloud computing and the robust performance of dedicated
on-premises servers. ... Certain applications can benefit from hardware
architectures beyond the standard x86 processors, such as Arm’s or IBM’s Z
mainframe architecture. Bare-metal clouds allow users to access these
nonstandard architectures for testing or running workloads designed explicitly
for them—another area where traditional virtual environments fall short. ...
Government, finance, healthcare, and other regulated industries may need
dedicated servers to meet regulatory or compliance mandates. Bare-metal clouds
provide the necessary isolation while maintaining the flexibility of cloud
deployment. ... Using bare-metal hardware often offers little room for
provisioning beyond what’s physically available; no additional memory or
hardware expansions can be made dynamically.
Is Gen Z to Blame? Why Cybersecurity Feels Harder for IT Pros

Gen Z’s trust in social media is another cultural difference to be aware of.
They’re not only listening to and watching a cohort of self-made influencers,
but they’re also following their advice — some of which isn’t sound. Young
adults glean a lot of information from social media sites and this raises a few
concerns for employers. Young workers have a propensity to believe in what they
learn from social media, making them susceptible to scams such as online fraud
and get-rich-quick schemes. ... A younger workforce brings fresh pairs of eyes
and new ideas to the table. They’re also looking for employers who reflect their
preferences, including ones with familiar technologies. Chief information
security officers (CISOs) are often dealing with legacy infrastructure and
outdated solutions as a primary barrier preventing them from addressing
cybersecurity obstacles — and hindering them from meeting Gen Z’s needs. Another
challenge is that Gen Z newcomers have shorter work histories and may lack
critical in-office and work-from-home experience to recognize phishing, job
recruitment, social engineering and deepfake scams. Gen Z is disclosing higher
rates of phishing victimization than any other generation, according to National
Cyber Security Alliance.
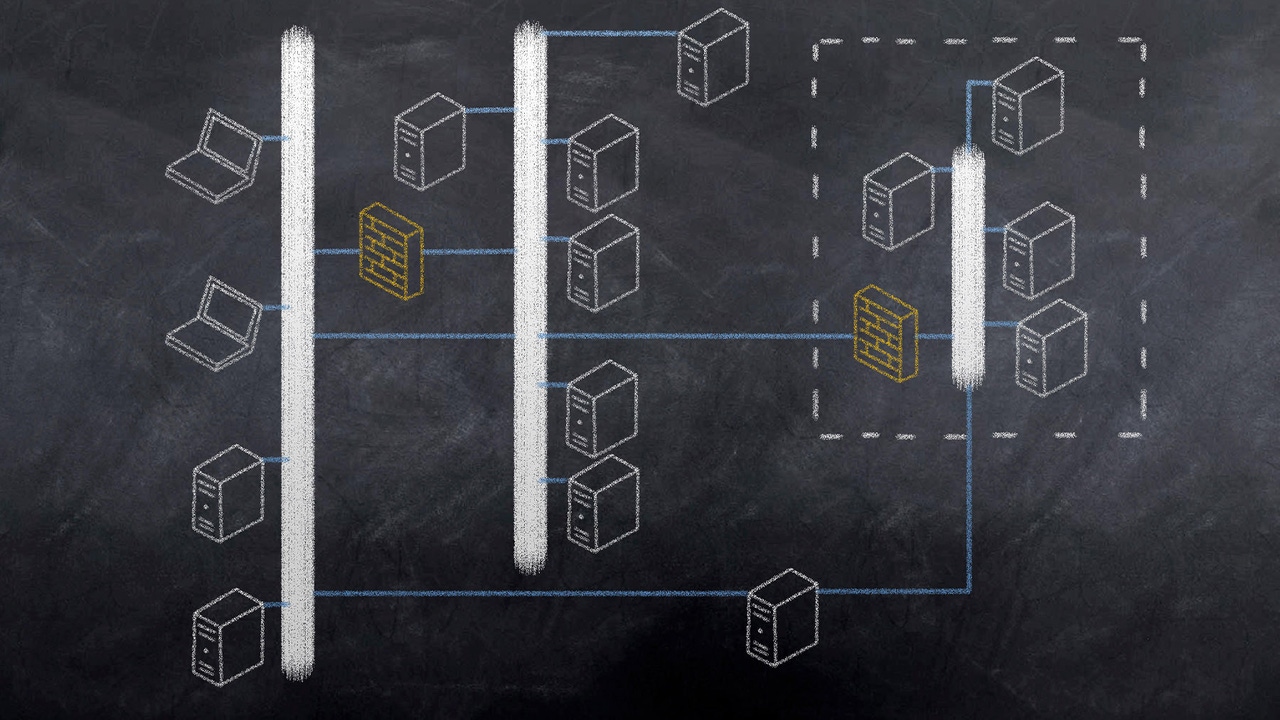
APM Tools and High-Availability Clusters: A Powerful Combination for Network Resiliency
APM tools are well-positioned as a means of feeding better data into the
platforms enterprises use to monitor and manage IT infrastructure. Data provided
by APM provides a more precise understanding of system health, enabling IT
management to establish more precise parameters for making decisions with the
confidence of good, timely data. High availability clusters are either hardware
(SAN-based clusters) or software (SANless clusters) that support seamless
failover of services to backup resources in the event of an incident. ... The
combination of APM and HA makes it easier for enterprises to improve network
resiliency by supporting and injecting better decision making and the use of
automation to enable seamless failover, predictive analytics, self-healing, and
other capabilities consistent with maximizing network performance, uptime, and
operational resilience. When used in a multi-cloud environment, services can
failover to the organization's secondary cloud provider, which is a major
advantage when an outage affects a cloud services provider. ... As some
enterprises evolve toward autonomous IT, data provided by APM provides a more
precise understanding of system health, enabling IT management to establish more
precise parameters for making decisions with confidence.
Why Enterprise Architecture Is Having A Moment

One can think of enterprise architecture as the description and design of the
complex web of technologies that supports a particular set of business
capabilities. I say “description” because most companies don’t initially have
an enterprise architect. Instead, they let their technology landscape grow
organically. ... Think about everything an organization would need to do
to move from its current state to one that reflected “modern standards.”
Describing and inventorying the current state would naturally be part of that.
But more important would be defining those standards. In today’s world, such
standards would include prioritizing cloud technology, adopting a
service-oriented architecture for software built in-house, working with open
APIs, and so forth. Enterprise architects are in the business of both defining
the technology standards for the business as well as governing the adoption of
new and emerging technology in conformity with those standards. ... But the
definition of standards does not take place in a vacuum. Instead, this work is
guided by the strategic aims of the organization. These aims, in turn, can be
viewed through the lens of business capabilities. Specifically, the business
must determine what capabilities it will need to realize its strategy in the
future.
Bridging Europe's Cybersecurity Divide Through Political Will

The debate over cybersecurity regulation has been contentious in recent years,
with strong positions on all sides. Europe has introduced multiple pieces of
regulation, which has led to growing complaints about overlapping requirements
and duplications. Which regulations apply to my company, among all existing
ones? Which frameworks should I use to improve security and then demonstrate
compliance? Which authorities should I report incidents to? Is there a
standardized approach to managing and monitoring third parties? ... There is a
broad consensus that cybersecurity regulatory requirements should be improved
in Europe and beyond. We need to build an effective and efficient legislative
framework for both functional and political reasons. On one hand, resources
are limited and have to be allocated efficiently to meaningful security
measures. On the other hand, frustration with redundant or unclear
requirements risks undermining the achievements achieved so far, empowering
those who oppose regulation entirely. ... While these operations require time
and resources, the main obstacle is not technology. The real challenge lies in
negotiating and agreeing on what an efficient system looks like in terms of
governance and minimum standards to follow.
What is risk management? Quantifying and mitigating uncertainty

Risk management is the process of identifying, analyzing, and mitigating
uncertainties and threats that can harm your company or organization. No
business venture or organizational action can completely avoid risk, of
course, and working too hard to do so would mean foregoing potentially
lucrative opportunities and strategies. ... IT leaders in particular must be
able to integrate risk management philosophies and techniques into their
planning, as IT infrastructure and spending can represent within the company
an intense combination of risk (of cyberattacks, downtime, or botched
rollouts, for instance) and benefits realized as increased capabilities or
efficiencies. Some companies, particularly those in heavily regulated
industries, such as banks and hospitals, centralize risk in a single
department under a top-level chief risk officer (CRO) or similar executive
role. A CRO might find themselves with responsibilities that overlap or
conflict with CSOs, CISOs, and CIOs, and in some orgs without a clearly
defined risk leader, ambitious infosec or infosecurity execs might try to
take on that role for themselves. In any case, IT leaders need to understand
and apply risk management in the areas under their purview.
Why Using Multiple AIs Is Trending Now
“Companies are building sophisticated AI stacks that treat general-purpose
LLMs as foundational utilities while deploying specialized AI copilots and
agents for coding, design, analytics, and industry-specific tasks. This
fragmentation exposes the hubris of incumbent AI companies marketing
themselves as complete solutions,” Moy adds. ... “Multimodality may sound
like a remedy for generative AI’s shortcomings in multifaceted processes,
but this, too, is more effective in the context of purpose-specific models,”
says Maxime Vermeir. “Multimodality doesn’t imply an AI multitool that can
excel in any area, but rather an AI model that can draw insights from
various forms of ‘rich’ data beyond just text, such as images or audio.
Still, this can be narrowed for businesses’ benefit, such as accurately
recognizing images included in specific document types to further increase
the autonomy of a purpose-built AI tool. While having multiple generative AI
tools may sound more cumbersome than a single catch-all solution, the
difference in ROI is undeniable,” Vermeir adds. ... “Using the different
language models in the same tool has multiple reasons, the main ones being
that every model has its strengths and weaknesses and therefore different
types of queries to ChatGPT may be handled better or worse depending on the
model. ... ” Feinberg adds.
8 obstacles women still face when seeking a leadership role in IT

When women are subjected to undermining stereotypes, have few female role
models, are spoken over, or treated as if their contribution isn’t welcome,
imposter syndrome is difficult to avoid. “When a woman looks at a job, she’s
only going to apply if she meets 90% of the criteria,” agrees Debby Briggs,
CISO at NetScout. ... Being seen as an outsider also costs women
opportunities, since leaders tend to promote people they know. All the women
I spoke to told me they survive this by building their own network.
... “A mentor can provide guidance, and a sponsor is someone who
actively opens doors for you.” “This is a must-have,” says Briggs, who adds
that she collects mentors. Anytime she finds someone she admires or who has
a skill she lacks, she reaches out. “Your mentors don’t have to be women,”
she says. ... Women say they feel invisible. “If I am at a tech event
standing next to a man and another man walks up to us, more than 50% of the
time he will address the man,” says Briggs. This invisibility happens in
small interactions and large ones. The website for tech companies is often
filled with the faces of white men. The speakers at tech events are all
male. How do you scale this obstacle? “If someone invites me to an event, I
look at who is on the panel. If it’s all white men, I tell them they don’t
have a diverse enough perspective and choose not to go,” says Briggs.
How To Handle "Urgent Request" in Scrum

The first step the Product Owner needs to take is to assess whether the
request aligns with the current Sprint Goal. However, based on my
experience, most 'urgent requests' are unrelated to the Sprint Goal. They
often come from individuals who are detached from the Scrum team's way of
working. In many cases, those people are not even aware of what a 'Sprint
Goal' is. If the request does not align with the Sprint Goal, I use a tool
called the Financial Impact vs. Reputation Impact Matrix. As a Product
Owner, I want the impact or potential damage to the company to be visualized
in two dimensions so that I do not make decisions based on a single factor.
The main purpose of this tool is to quantify the urgency of those "urgent
requests." As a Product Owner, we do not want our team to work based on
opinions or, even worse, political power; we want them to work based on
facts or data. Many Scrum teams order their Product Backlog based on value,
and they use potential revenue as the value attribute. Unlike potential
revenue, which is expressed in positive terms, financial impact and
reputation impact are negative. If the impact is not negative, as a Product
Owner, I would not consider the request as urgent. Instead, it can wait and
be stored in the Product Backlog for further discussion.

_Borka_Kiss_Alamy.jpg?width=1280&auto=webp&quality=95&format=jpg&disable=upscale)