Generative AI Strategy For Enterprise

The guidelines to align with enterprise business Initiatives. Identify the
business challenges that require attention. Also, understand the business
benefits of AI adoption that are critical for the success of enterprise. Select
the targeted use cases and perform the Proof of Concepts (POC) that can deliver
desired business and operational outcomes. AI use cases should not be viewed in
isolation. AI initiatives and technology should be integrated into existing
business processes and workflows to optimize and streamline them. Build value
through improved productivity, growth, and new business models. ... Prioritize
GenAI usecase initiatives based on highest potential value and feasibility to
execute. Implement model development lifecycle that includes products and
services, rigorous testing, validation, and documentation. Build Roadmap that
provides a plan to deliver the identified GenAI applications by prioritizing and
simplifying the actions required to deliver identified initiatives. Create
processes for ongoing monitoring and auding of GenAI systems for responsible use
of AI to ensure compliance with legal, ethical standards and algorithmic biases.
Do cloud-based genAI services have an enterprise future?

“Given the data gravity in the cloud, it is often the easiest place to start
with training data. However, there will be a lot of use cases for smaller LLMs
and AI inferencing at the edge. Also, cloud providers will continue to offer
build-your-own AI platform options via Kubernetes platforms, which have been
used by data scientist for years now,” Sustar said. “Some of these
implementations will take place in the data center on platforms such as Red Hat
OpenShift AI. Meanwhile, new GPU-oriented clouds like Coreweave will offer a
third option. This is early days, but managed AI services from cloud providers
will remain central to the AI ecosystem.” And while smaller LLMs are on the
horizon, enterprises will still use major companies’ AI cloud services for when
they need access to very large LLMs, according to Litan. Even so, more
organizations will eventually be using small LLMs that run on much smaller
hardware, “even as small as a common laptop. “And we will see the rise of
services companies that support that configuration along with the privacy,
security and risk management services that will be required,” Litan
said.
6 bad cybersecurity habits that put SMBs at risk

Cybersecurity can’t be addressed with technology alone and in many ways it’s a
human problem, according to Sage. “Technology enables attacks, technology
facilitates preventing attacks, technology helps with cleaning up after an
attack, but that technology requires a knowledgeable human to be effective, at
least for now,” they say. This also feeds into other problems, which are a lack
of budget and no dedicated responsibility for cybersecurity. “These are
significant challenges for SMBs, leaving them without guidance on compliance
frameworks and a clear direction, and reliant on providers for support,” says
Iqbal. ... Adopting good cyber hygiene habits should be a no brainer, although
it can be a hit and miss. For instance, allowing the use of weak passwords is
all too common, according to Iqbal. He’s also found instances where the default
password for logins has not been changed or all the passwords for security
servers are changed to a single password and there isn’t a separate
administrative password. “The admin account is the most lucrative account threat
actors are looking to compromise. It just takes one compromise and then the keys
to the kingdom are flung open to all your potential threat actors,” he says.
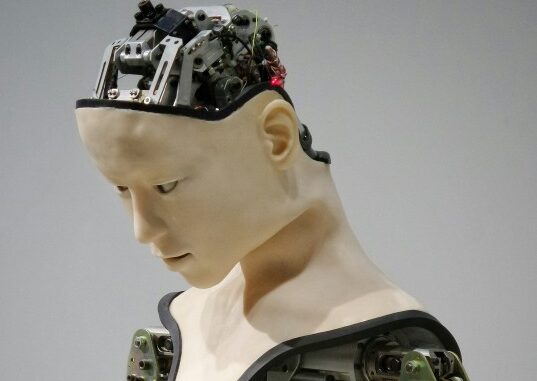
Generative AI is coming for healthcare, and not everyone’s thrilled
While generative AI shows promise in specific, narrow areas of medicine, experts
like Borkowski point to the technical and compliance roadblocks that must be
overcome before generative AI can be useful — and trusted — as an all-around
assistive healthcare tool. “Significant privacy and security concerns surround
using generative AI in healthcare,” Borkowski said. “The sensitive nature of
medical data and the potential for misuse or unauthorized access pose severe
risks to patient confidentiality and trust in the healthcare system.
Furthermore, the regulatory and legal landscape surrounding the use of
generative AI in healthcare is still evolving, with questions regarding
liability, data protection and the practice of medicine by non-human entities
still needing to be solved.” Even Thirunavukarasu, bullish as he is about
generative AI in healthcare, says that there needs to be “rigorous science”
behind tools that are patient-facing. “Particularly without direct clinician
oversight, there should be pragmatic randomized control trials demonstrating
clinical benefit to justify deployment of patient-facing generative AI,” he
said.
State of the CIO, 2024: Change makers in the business spotlight

The push for innovation requires a steady hand, and CIOs are stepping in to
provide guidance, including orienting the greater enterprise to the potential —
and the pitfalls — of new technologies like AI. Eighty-five percent of
respondents to the 2024 State of the CIO survey view the CIO as a critical
change maker and a much-needed resource given the pace and scale of change,
amplified by the frenzy around AI. “With all the hype of AI and the velocity at
which technology is evolving, my focus as a CIO continuously and relentlessly
has to be through the lens of strategy, execution, and culture,” says Sanjeev
Saturru, CIO at Casey’s, the third-largest convenience store chain in the United
States. ... “Eighteen months ago, AI was an interesting topic, but today, if you
don’t have a plan to elevate experience via AI you are behind,” says LaQuinta.
“We have a maniacal focus on maximizing the contribution of advanced
intelligence, supported by AI. That could be making information available at the
click of a button to help advisors be more efficient with their time or to serve
clients better in a hyperpersonalized way.”
Cloned Voice Tech Is Coming for Bank Accounts

At many financial institutions, your voice is your password. Tiny variations in
pitch, tone and timbre make human voices unique - apparently making them an
ideal method for authenticating customers phoning for service. Major banks
across the globe have embraced voice print recognition. It's an ideal security
measure, as long as computers can't be trained to easily synthesize those pitch,
tone and timbre characteristics in real time. They can. Generative artificial
intelligence bellwether OpenAI in late March announced a preview of what it
dubbed Voice Engine, technology that with a 15-second audio sample can generate
natural-sounding speech "that closely resembles the original speaker." While
OpenAI touted the technology for the good it could do - instantaneous language
translation, speech therapy, reading assistance - critics' thoughts went
immediately to where it could do harm, including in breaking that once ideal
authentication method for keeping fraudsters out. It also could supercharge
impersonation fraud fueling "child in trouble" and romance scams as well as
disinformation.
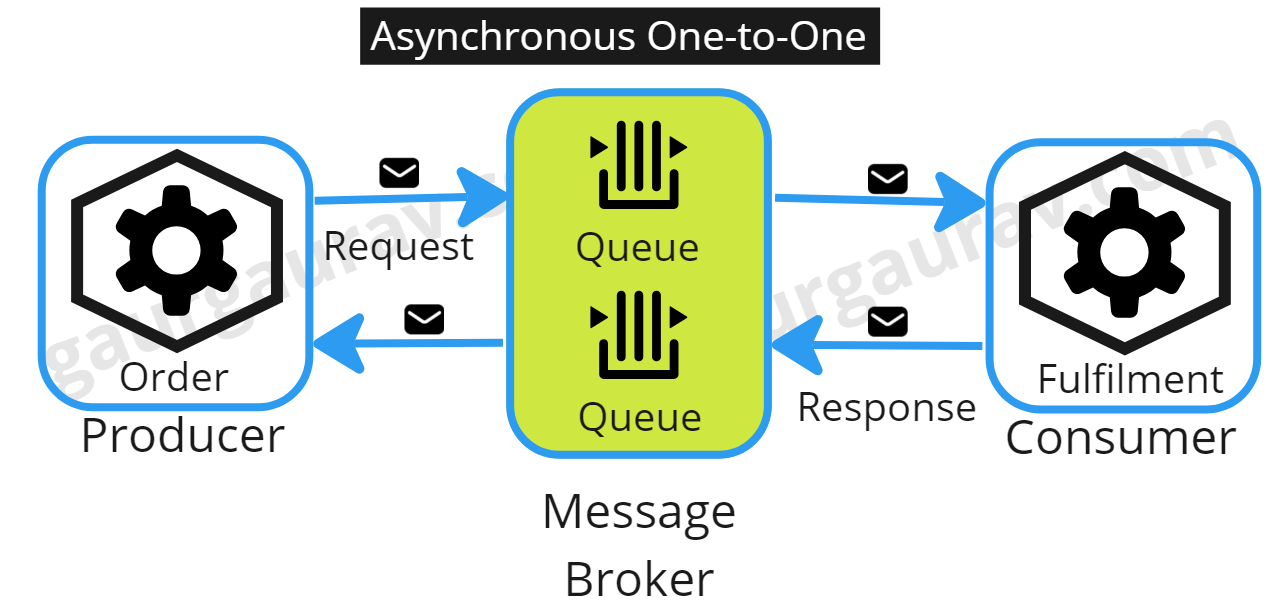
Data pipelines for the rest of us

In some ways, Airflow is like a seriously upgraded cron job scheduler. Companies
start with isolated systems, which eventually need to be stitched together. Or,
rather, the data needs to flow between them. As an industry, we’ve invented all
sorts of ways to manage these data pipelines, but as data increases, the systems
to manage that data proliferate, not to mention the ever-increasing
sophistication of the interactions between these components. It’s a nightmare,
as the Airbnb team wrote when open sourcing Airflow: “If you consider a
fast-paced, medium-sized data team for a few years on an evolving data
infrastructure and you have a massively complex network of computation jobs on
your hands, this complexity can become a significant burden for the data teams
to manage, or even comprehend.” Written in Python, Airflow naturally speaks the
language of data. Think of it as connective tissue that gives developers a
consistent way to plan, orchestrate, and understand how data flows between every
system. A significant and growing swath of the Fortune 500 depends on Airflow
for data pipeline orchestration, and the more they use it, the more valuable it
becomes.
The 5 Steps to Crafting an Impactful Enterprise Architecture Communication Strategy

To successfully convey the significance of enterprise architecture within an
organization, a structured and strategic approach to communication is crucial.
Here’s an overview of the five pivotal steps to create an impactful enterprise
architecture communication strategy: Clarify Strategic Objectives: Define
clear-cut enterprise architecture objectives that align with the broader vision
of the organization. ... Contextual Understanding: Assess the current state of
enterprise architecture in your organization and the specific goals you seek to
achieve through this communication strategy. ... Audience Insights: Segment your
internal audience to understand the varying levels of EA awareness and the
distinct needs across departments. ... Selecting Suitable Communication Tools:
With a plethora of digital tools available, it’s essential to choose those that
best align with your enterprise architecture communication goals.
... Developing the EA Communication Plan: Integrate all insights and
choices into a coherent communication plan that outlines how enterprise
architecture will be communicated across the organization.
A Call for Technology Resilience
A major inflection point in application development has been the adoption of
Agile. With iterative, Agile application development, an application or system
is never finished. It’s continuously changing as business conditions and
circumstances change. Both users and IT accept this iterative development
without endpoints. On the other hand, end points (and more of them!) in IT
projects also can foster technology resilience. They achieve resilience because
a large project that gets interrupted by an immediate and overriding business
necessity is more easily paused if it is structured as a series of mini projects
that deliver incremental functionality. ... Your network goes down under a
malware attack, but your network guru has just left the company for another
opportunity. Do you have someone who can step in and do the work? Or, what if
your DBA leaves? How long can you delay defining an AI data architecture, and
will it harm the company competitively? To achieve IT roster depth, staff must
be trained in new responsibilities, or at least cross-trained in different roles
that they can assume if needed.
SaaS Tools: Major Threat Vector for Enterprise Security
When considering SaaS security risks, organizations have to take into account
whether the SaaS provider is an established player or a startup, Lobo said.
Established players have the resources to invest heavily in the security of
their applications, and are less vulnerable to code injection attacks.
Organizations do not have the auditing powers to measure an established vendor's
security credentials and have no recourse but to trust the vendor. But when it
comes to dealing with smaller companies, organizations can scrutinize encryption
and cloud security practices, evaluate supply chains, check for vulnerabilities
in the application code and conduct frequent security assessments. Lobo
said many organizations today rely on services such as SecurityScorecard,
UpGuard and similar companies that keep track of vulnerabilities in enterprise
software and alert users, giving them the opportunity to patch third-party
software prior to exploitation. Shankar Ramaswamy, solutions director at
Bangalore-based IT consultancy giant WiproThe only way to do great work is to love what you do. –Steve Jobs, said organizations using third-party SaaS applications must focus on three
major aspects - strengthen endpoint security, minimize the application' access
to internal resources and replace passwords with multi factor authentication.
Quote for the day:
"The only way to do great work is to
love what you do." -- Steve Jobs