Bridging the GRC and Security Divide

Much like the parable of the blind men and the elephant, many GRC and security
teams are only able to test a small sample of security controls, or have
siloed visibility into different asset types like devices, accounts, and
databases. This disconnect leads to gaps in coverage and misplaced confidence
in reporting. Also, while GRC teams have GRC tools that manage policies,
these tools are ill-equipped to take advantage of existing data from security
controls to demonstrate that these policies are being followed. Bringing
control data into GRC tools also requires cybersecurity experts to capture and
input data manually. If you had to categorize the relationship between GRC and
cyber, you’d at best have to say: ‘it’s complicated.’ The ideal solution is
one where GRC teams are capable of confidently meeting regulators’ demands in
a timely fashion, with data that is automated rather than manual, and where
they can access security data to ensure complete assessments of every instance
of every security control is available automatically. With a consistent
up-to-date view of control deployments, accuracy and confidence is improved
since assessments will be based on facts instead of subjective opinions.
Cybercrime Infrastructure Never Really Dies
The analysis yields interesting insight into the scale of operations of a
well-known cybercriminal operation. A significant number of cybercriminal
operations that used the CyberBunker services appear to have left behind their
automated infrastructure, and that — despite being closed down the prior year
— many continue to reach out to the shuttered service. "One thing we tried to
keep in mind is that the networks haven't been 'active' in several months, so
while attempts to uncover drug market activity, stolen goods, and illicit
content yielded few results, they were very likely there at some point," Lalji
says. "The data also had to be sampled due to the sheer size." The CyberBunker
operated in Germany is the second such facility raided by police. In 2013, the
first CyberBunker — based in Amsterdam and operated by some of the same people
— was shut down by police, following extended distributed denial-of-service
attacks against anti-spam coalition SpamHaus. The facility shut down in
2019, dubbed "CyberBunker 2.0" by the group operating the service, was based
on three-acre property in the German town of Traben-Trarbach.
Exploring the growing use of IT in B2B customer experience projects

IT is needed to deliver the expected customer experience and “collaboration is
increasingly becoming the norm as more and more departments with fervent
leaders want to help shape and create the experience the customer has with
their brands,” continues Whitcombe. Referring to the importance of digital
tools, she adds: “Expedited somewhat by the current Covid-19 pandemic but
heading this direction organically anyway, digital workshopping tools with
breakout rooms, online real-time white boards, customer journey mapping
software, and cloud hosted real time project management programmes are fast
evolving into the tools used by businesses to deliver this. “The next best
thing to a crystal ball forecasting every need of our customers, is an
optimised and measured customer experience that has all parts of the business
represented and culpable for the overall experience of their customers. Based
on this, we as CTO’s are in a wonderful place to facilitate and ultimately
hero the rise of the customer throughout our organisations.”
What Developers Really Think About Pentesting

A developer’s highest priority will always be the building of features, and in
this crazy world of rapid digitization, it will have to be done at speed.
While some coders have a personal interest in security and secure coding, the
general sentiment is that security is “someone else’s problem,” which
inevitably includes pentesters. Most common vulnerabilities are indeed
minor issues to remediate — once known, the fixes are simple to execute for
things like cross-site scripting (XSS) and SQL injection. The problem is, many
developers don’t realize they’re introducing them in the first place, and
these seemingly minor issues are the small window of opportunity an attacker
needs to cause devastating problems for a company. According to Akamai,
between November 2017 and March 2019, SQL injection vulnerabilities accounted
for 65% of all web-based attack vectors. For a vulnerability that has had a
known fix for more than 20 years, that is a sobering statistic. Some
pentest teams do assist in the remediation of security bugs, but others will
provide a report of the bad news and expect developers to work through
hotfixes, even if they have moved onto a different project by the time this
happens.
Brits will sell their personal data for pennies

“It’s clear there is a cost when it comes to privacy – the question is, how
much,” said Jesper Frederiksen, Okta’s EMEA vice-president and general
manager. “Okta’s research shows that consumers would generally be willing to
accept between £10 and £50 for their location data (31%) or browsing history
(30%). Surprisingly, 10% would be willing to give away their password data for
less than £30. “If companies can strike a balance between privacy and
innovation, consumers can have control over their data, including where it
goes and whether they are compensated, while companies can still build
products that benefit the world.” While these findings might make worrying
reading, the research showed encouraging signs that people are at least
becoming more aware of how their data is collected, used and potentially sold,
not least because of the high-profile failure of the UK government’s Covid-19
contact-tracing app. When asked about the app specifically, 84% said they were
concerned that if they used it, their data would be used by organisations for
purposes unrelated to contact tracing, such as advertising.
New tech and Wi-Fi 6 tools aim to make high-speed internet more accessible

Wi-Fi 6 is the new generation of wireless technology, which aims to bring
speeds up to 30% faster than its predecessor, Wi-Fi 5. Speed is not its only
asset –– the wireless local area network (WLAN) also boasts lower latency,
increased power efficiency, and a more streamlined delivery of data. As such,
it's essential for enterprises to get on board to stay ahead of the curve. ...
In a survey of more than 800 respondents, across 82 countries, there seemed to
be a high level of enthusiasm for "delivering broadband wireless internet
service for urban, suburban, enterprise and industrial environments," the
release states, which can be accomplished through Cambium's new 60 GHz
products. "In today's world, high-speed Internet access is as fundamental
as having access to water and electricity," said Scott Imhoff, SVP of product
management, Cambium Networks. "Our 60 GHz product strategy is designed to
deliver fiber-like throughput at a fraction of the cost." A majority of
respondents (57%) say that "building-to-building wireless multigigabit
point-to-point links for business" was the top priority. Following that, at
46%, was residential connectivity, and Wi-Fi backhaul represented 30%.
Microsoft Authenticator for Android update adds options

The features in this update were made available in the iOS version of the app
last spring. Holger Mueller, vice president and principal analyst at
Constellation Research, said Microsoft's continued support of the feature
could prove helpful to IT admins looking to make logging in to enterprise
accounts easier. "Microsoft makes strides to support the future of work by
bringing key admin and security features to mobile devices" with this move, he
said. "Combining smartphone and other platforms for admin and security
purposes is a successful strategy that finds the right compromise between
security and convenience." Forrester Research analyst Andrew Hewitt noted that
having passwords that are frequently updated and sufficiently complex was
important for businesses to remain secure. That can be difficult for the user,
who must routinely pick passwords that are easy to remember, but difficult to
break. "That's one of the big issues: getting people to have those updated
passwords, and make sure you're doing that on a regular cadence," he said.
Why collaboration is the key to true business intelligence

Sadly, until now, many organisations have suffered from a lack of connection
between those departments that directly or indirectly touch with the customer.
Seamless data collaboration between departments that covers the entire
customer journey, such as sales, marketing, renewals, and customer success,
plays a crucial role as it offers the organisation a reliable picture of how
its customer base behaves. In this way, businesses can find out what outcomes
customers and prospects are looking for, what adoption rates look like for
each of its products, and how unsatisfied customers might be helped. Then, the
organisation can continuously improve customer experience and ensure customers
are happy with their product and getting their ROI. What is needed is a firm
alliance between all teams that interact with the customer. Sales and
marketing are the two most important, yet they have historically had
challenges in staying aligned around the needs of their customers. Research
found that 68% of marketers believe their sales colleagues do not use their
content correctly. Meanwhile, 74% of sales reps think marketers don’t even
know what content is useful to them.
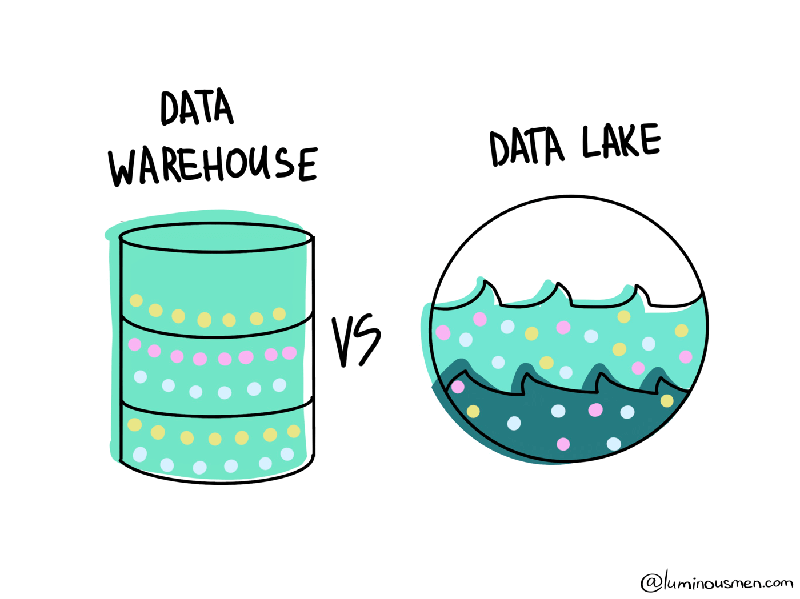
How Technology Will Change The Role of CIOs in 2020

Having an appropriate cloud strategy is essential for any business. A cloud
strategy helps businesses to determine how to adopt and make the most
effective use of cloud technology. This strategy should be integrated with
your wider business goals. It should serve as an effective complement to
meeting them. In developing a cloud strategy, CIOs must pay close attention to
both the anticipated benefits of cloud technology and any changes that might
need to be made elsewhere in order to accommodate it. So, for example, if
you’re planning to introduce a cloud phone system to your business, you need
to be clear when weighing up the potential pros and cons. What sort of savings
can you expect to make? How does it compare, in terms of cost, convenience,
and overall reliability, to ordinary landline calls? Would a cloud contact
centre be adequate for meeting the needs of your customers? These are just
some of the questions CIOs will need to consider. Over the last few years, new
technologies have been introduced at a breakneck speed.
DeepMind sets AI loose on Diplomacy board game, and collaboration is key

AI systems have proved to be far superior to even the best human beings at
zero-sum games like chess and Go. In this type of gameplay, there can only be
one winner and one loser. Dissimilarly, Diplomacy requires agents to build
alliances and foster collaboration. "On the one hand, it is difficult to make
progress in the game without the support of other players, but on the other
hand, only one player can eventually win. This means it is more difficult to
achieve cooperation in this environment. The tension between cooperation and
competition in Diplomacy makes building trustworthy agents in this game an
interesting research challenge," said Tom Anthony, a research scientist at
DeepMind. The ability to expeditiously vanquish a human player in a zero-sum
game is certainly impressive, however, a richer layering of skills opens up
another world of AI potential. Our day-to-day lives involve an intricate
patchwork of balanced synergies; our individual needs often packaged within a
larger group effort. That said, this research could enhance agents' ability to
collaborate with us and one another, leading to a vast spectrum of real-world
applications.
Quote for the day: