Delivering Business Value Through AI To Impact Top Line, Bottom Line And Unlock ROI

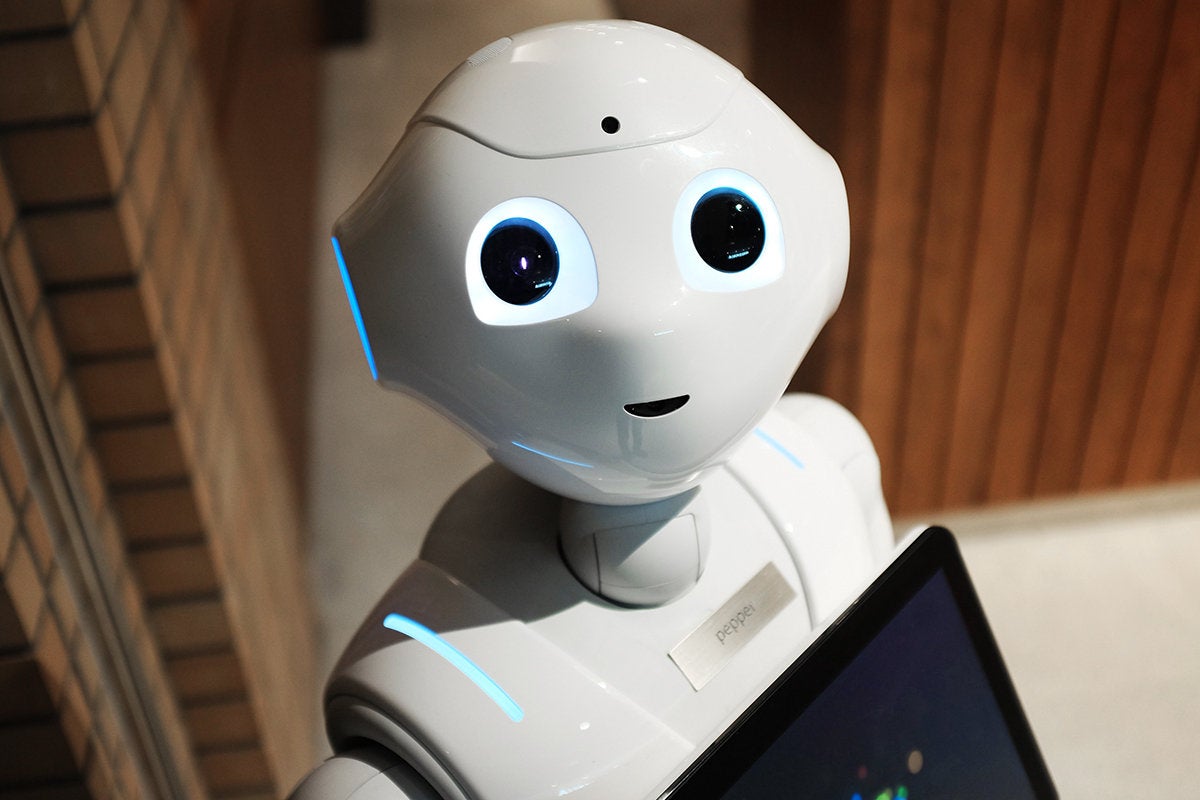
Business leaders need to realize AI’s potential to unlock new sources of revenue in addition to improving customer targeting and loyalty. One of these ways is data monetization. What is data monetization? Simply put, data monetization refers to the act of generating measurable economic benefits from available data resources. According to Gartner, there are two distinct ways in which business leaders can monetize data. The most commonly seen method from the two is Direct Monetization. The way to realize value from this avenue involves directly adding AI as a feature to existing offerings. ... Use cases discovered in this arena span social media sentiment mining, programmatic selection of advertising properties, measuring effectiveness of marketing programs, ensuring customer loyalty and intelligent sales recommendations. AI also has huge potential to drive businesses to explore and exploit eCommerce platforms as a credible channel for sales and to help drive the digital agenda forward.
Has the UK government's cloud-first policy served its purpose?
The obvious concern in all this is that, if the cloud-first mandate is revoked completely, central government IT chiefs might start falling back into bad procurement habits, whereby cloud becomes an afterthought and on-premise rules supreme again. Maybe that is an extreme projection, but there are signs elsewhere that some of the behaviours that G-Cloud, in particular, was introduced to curb could be starting to surface again. One only has to look at how the percentage of deals being awarded to SMEs via G-Cloud has started to slide of late, which has fed speculation a new oligopoly of big tech suppliers is starting to form, who will – in time – dominate the government IT procurement landscape. Where G-Cloud is concerned, there are also rumblings of discontent among suppliers who populate the framework that it is becoming increasingly side-lined for a number of reasons. There are semi-regular grumbles from suppliers that suggestions they have made to CCS or GDS about changes they would like made to the framework being ignored, or not being acted on as quickly as they would like.

There are several reasons why enterprise security threats -- especially malware attacks -- are on the rise, Kudelski Security's Kizziah said. "One of the most interesting is criminal groups' adoption of the latest, freely available malcode, which is quite advanced, easy to modify for different specific purposes, and modular, so it can use different techniques to infect an endpoint," Kizziah said. With over two billion known malware out there and with new malware being introduced every single day, it is impossible to achieve a reasonable level of protection with the traditional approaches to cybersecurity, which is focused on "chasing the bad," Nyotron's Kolga said. Instead, businesses should refocus their efforts on the "ensuring good" approach, Kolga said. This can be achieved through whitelisting approaches for application control and OS behavior, he added. ... Cybercriminals will always find a way to infiltrate businesses, Kujawa believes. He advised companies to adopt a mindset that is not focused solely on prevention. Enterprises should have a plan in place for when threat actors gain access to networks, so that they can protect the most important data with additional layers of security and to ensure that business operations are not disrupted.
FBI and Europol Disrupt GozNym Malware Attack Network
Authorities say this investigation was the result of cooperation between the U.S. and Bulgaria, Germany, Georgia, Moldova and Ukraine. An unusual aspect of the investigation is that charges were brought against suspects in the countries where they reside based, in part, on evidence gathered by the FBI and German authorities. "The prosecutions are based on shared evidence acquired through coordinated searches for evidence in Georgia, Ukraine, Moldova and Bulgaria, as well as from evidence shared by the United States and Germany from their respective investigations," the U.S. Justice Department says. Authorities say five suspects remain at large. All are believed to be in Russia, which did not cooperate with the investigation. The GozNym takedown involved close cooperation between the U.S. Department of Justice and counterparts abroad, supported by coordination from Europol, backed by Eurojust, the EU's agency for handling judicial cooperation on criminal matters among EU member states' agencies.
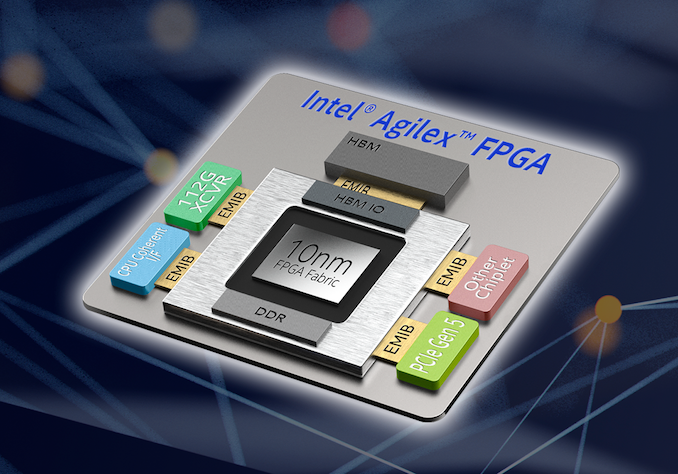
Demystifying Quantum Computing

Importantly, quantum computers aren’t suited for all problems. There are instances where classical computers can perform just as well as a quantum machine. Thus, quantum computers won’t replace classical computers; they’ll operate alongside them. However, more work and research remains to be done. Current quantum computers aren’t powerful or accurate enough yet to offer an advantage over classical computers. Today they can maintain entanglement for just 90 microseconds, and the algorithm can only run during this short timeframe. In quantum computers with superconducting qubits, the chip must be cooled to close to absolute zero, meaning that it must be totally isolated from the environment. Any outside noise or heat is enough to cause an entangled system to collapse. These limitations will have to be overcome before businesses can start using the technology widely. To date, the quantum computers that exist have been used largely for studying quantum computing and developing its potential use cases. Once quantum computers exceed the capabilities of classical computers, they’ll reach what is called quantum supremacy, and the true quantum era will be at hand.
The Evolution Of The Chief Data Officer

“CDOs have emerged from one of two camps: IT or business,” she says. “CDOs that have risen through the ranks of a technology organisation recognise the value of data and see how it can be applied to improve the business. One of their biggest challenges is in building trust and credibility with business leaders, while pushing risk averse technologists outside their comfort zones.” “Meanwhile, CDOs who come from the business side of an organisation have been frustrated with how slow IT may have been to respond to requests for self service analytics, new types of data such as the IoT, and the evolution to AI. They are willing to take more risks and innovate faster because they know that the business livelihood depends upon it. Their biggest challenge is learning just enough of the technology—and there is a lot of it, which changes rapidly—to be respected by IT and to make the right decisions.” For all CDOs, regardless of background, the overarching aim is to create a business culture that is driven by data. How this is achieved may vary according to individual or organisation, but the end goal is the same: capture data, understand it, keep it safe, and use it to make the business better.
Only 9% of companies warn employees about IoT risks

IoT-related data breaches specifically caused by an unsecured IoT device or application increased from 15% in 2017 to 26% in the last year, the report found. It's possible that this number is actually larger, as most organizations said they are not aware of every unsecure IoT device or application in their environment, or introduced by third-party vendors, it noted. Despite these risks, only 9% of companies said their organizations currently inform and educate employees and third parties about the dangers created by IoT devices. The majority of organizations surveyed lack centralized accountability to address and manage IoT risks, according to the report. Only 21% of board members report that they are highly engaged in security practices, and understand third-party and cybersecurity risks in general. About one-third (32%) of the organizations surveyed said no single person or department is responsible for managing or implementing corrective actions to manage IoT risks, the report found.
Podcast: Adopting public cloud as a culture

The key for improved cloud adoption is opening the lines of communication, bridging the divides, and gaining new levels of understanding. As in the restaurant analogy, the chef says, “Well, I can add these ingredients, but it will change the flavor and it might increase the cost.” And then the finance people say, “Well, if we make better food, then more people will eat it.” Or, “If we lower prices, we will get more economies of scale.” Or, “If we raise prices, we will reduce volume of diners down.” It’s all about that balance―and it’s an open discussion among and between those three parts of the organization. This is the digital transformation we are seeing across the board. It’s about IT being more flexible, listening to the needs of the end users, and being willing to be agile in providing services. In exchange, the end users come to IT first, understand where the cloud use is going, and can IT be responsive? IT knows better what the users want. It becomes not just that they want solutions faster but by how much. They can negotiate based on actual requirements.
The Power Of Hidden Teams
A recent Cisco study yielded comparable data. And according to Jones, “We can see from our data that teams with more-frequent check-ins have dramatically higher levels of engagement; so, moving forward, we are going to keep experimenting with smaller, more patient-centered, more agile teams, and keep investigating the link between span of control and patient outcomes — and all because we can see the link between attention, teams, and patient care.” The most-engaged teams — and the most-effective team leaders — understand that the currency of engagement is real, human attention. This helps us answer a long-standing question about the optimal span of control in all organizations. Some research puts the number at eight to 10, whereas some workplaces, such as call centers, push the limits with spans as great as 70 team members to one supervisor. Pinpointing the check in, and the frequent attention it provides, as the key driver of engagement shows that “span of control” is more accurately span of attention. The research reveals that for people to be engaged, the span of control must allow each team leader to check-in, one on one, with each team member every week of the year.
Attackers Exploit WhatsApp Flaw to Auto-Install Spyware

The U.K.'s National Cyber Security Center - the public-facing arm of GCHQ - has published guidance for all WhatsApp users. "The NCSC ... always recommends that people protect their device by installing updates as soon as they become available," it says. "The NCSC also recommends that people switch on automatic updates to install them as quickly as possible." Likewise, the Indian Computer Emergency Response Team, Cert-IN, has warned that attackers could launch further attacks. It's urging all users to upgrade immediately to latest version of WhatsApp. Questions remain about what exactly the exploit might allow attackers to do. For example, could they use it to escape Apple's iOS sandbox, and does updating eliminate any access they may now enjoy to a device? "Does updating the app remove whatever malware was placed on phone? Did they manage to pivot out of the app? I haven't seen any technical analysis of the malware yet so genuinely interested," says Alan Woodward, a professor of computer science at the University of Surrey.
Quote for the day:
"And how does one lead? We lead by doing; we lead by being." -- Bryant McGill