
To date, critical infrastructure cybersecurity has relied too much upon network monitoring and anomaly detection in an attempt to detect suspicious traffic before it turns problematic. The challenge with this approach is that it is reactionary and only effective after an adversary has breached some level of defenses. We take an entirely different approach, focusing on prevention by denying malware the uniformity it needs to propagate. To do this, we use a binary randomization technique that shuffles the basic constructs of a program, known as basic blocks, to produce code that is functionally identical, but logically unique. When an attacker develops an exploit for a known vulnerability in a program, it is helpful to know where all the code is located so that they can repurpose it to do their bidding. Binary randomization renders that prior knowledge useless, as each instance of a program has code in different locations. One way to visualize the concept of binary randomization is to picture the Star Wars universe at the time when Luke Skywalker and the Rebel Alliance set off to destroy the Death Star.
How to eliminate project noise

Once the requirements and project scope are clearly set, it's important to operate within those boundaries and not fold in additional enhancements that will affect timelines and deliverables. Enhancement requests usually come from end users. If the request is easy to satisfy, like altering a screen layout or adding a data field edit, it likely can be added without much impact. But if the enhancement impacts multiple programs, it's time to redefine the project scope and timeline. Communicate it to all stakeholders, and make sure they are on board with any project changes. ... You can't control a change in business direction your boss makes. However, you can control your project timelines, resources, and how they will be impacted by these new priorities. When a priority change occurs, evaluate impact, and then define a new set of timelines for projects that were already underway. Communicate the impact to your staff and your superiors immediately. One mistake newer project managers make is that they are so eager to please that they try to maintain the original timelines of their projects and just add new projects.
Throwing more people at the problem no longer works
To understand how to proceed forward, we need to unpack the problem a bit. The first, and guiding factor is by understanding the nature of your business. I often go into organizations where the IT leadership has a limited understanding of their business…and not at the level they need today. To complicate matters, beyond the senior most IT leader, the level of business knowledge drops off precipitously. IT staff further into the organization know little more than what a common person knows about their company. While this has worked (marginally) in the past, it will not serve the company moving forward. We have long since passed the point where a company can function without the use of technology. Likewise, we have also passed the point where a CIO or IT leader can survive by technology knowledge alone. Hence why the value of the traditional CIO is in decline while the value of the transformational CIO is on the upswing. See my post on The difference between the traditional CIO and the transformational CIO for more specifics.
Facing competing objectives, CIOs share prioritization strategies
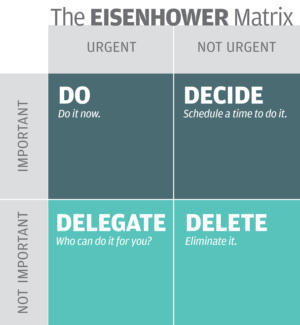
Effective governance is not something you can do alone. You need a decision-making body to help prioritize IT investment, to establish transparency to your processes and decisions, and to share ownership of those decisions with the other decision makers. This piece is critical because face it: The “tyranny of now” is really the tyranny of your customers’ demands. And since there will never be enough money or bandwidth to meet all those demands at once, managing those expectations must be a team sport. Governance does that for you. To be proactive rather than reactive, CIOs must be realistic about capacity. Don’t promise what you can’t deliver. You can’t manage 45 concurrent major IT projects, so narrow the list and focus on 10. Is that painful? Sure, but it’s also effective. Finally, remember that flexibility is key. When something new emerges, line it up against your current top 10. If necessary, reprioritize. Governance doesn’t mean being rigid. It means being flexible. ... Of course, we need to get down to one to work efficiently and effectively as a single company. So, we held 14 workshops in the first four weeks after the acquisition, meeting with every part of the business, from accounting to legal to program execution.
Moving apps to the cloud? 3 steps to ensure good customer experiences

If your business is like most enterprises today, chances are good it's moving toward a best-of-breed, multi-cloud strategy. You're looking for applications best suited to the business's IT needs and want to run each of those apps in the optimal cloud environment. But if you're going to be mixing and matching cloud architectures and workloads to optimize performance, you need openness and flexibility. You need to select cloud providers and software vendors who embrace open standards, open source technologies, and who excel at ensuring cross-platform interoperability. Look for cloud providers and software companies who make it relatively easy for you to move workloads between on-premises data centers, their cloud and other clouds. Developers on your team will also be pleased with this commitment to openness. Today's developers expect to use modern, open source tools for management and customization. The last thing they want is to get boxed into using subpar, proprietary development tools simply because a software partner deems it necessary.
Cryptojacking campaign exploiting Apache Struts 2 flaw kills off the competition
Researchers from F5 Labs say the Apache bug is being used in a new cryptomining campaign which impacts Linux machines. According to the team, threat actors are harnessing PoC code for the Apache Struts 2 critical remote code execution vulnerability posted to Pastebin to infiltrate Linux systems for the purpose of mining Monero. Mining for cryptocurrency, such as Bitcoin (BTC), Ethereum (ETH), and Monero (XMR), is a completely legitimate activity which uses computing power to find virtual coins. However, when this power is taken without consent, such activities are considered cryptojacking. The most common tactic used by criminals in cryptojacking campaigns is the Coinhive script, a legitimate system which is being widely abused. In July, a massive cryptojacking campaign was uncovered in which a botnet used enslaved MikroTik routers to mine for Monero. Dubbed CroniX, the new attack exploits the Apache bug to send a single HTTP request at the same time as injecting an Object-Graph Navigation Language (OGNL) expression containing malicious JavaScript code.
How Do You Develop A Data Strategy? Here’re 6 Simple Steps That Will Help
There are millions of ways data can help a business but, broadly speaking, they fall into two categories: one is using data to improve your existing business and how you make business decisions. The second is using data to transform your day-to-day business operations. In practice, most companies start out wanting to improve their decision making and take it from there. However, if you want to use data, you must always start with a data strategy. What data you gather and how you analyse it will depend entirely on what you’re looking to achieve – so you need to have thought about this at the outset. Having a data strategy helps the whole process run more smoothly and prepares you and your people for the journey ahead. ... Getting the key company players and decision makers involved will help you create a better data strategy overall, and getting their buy-in at this crucial early stage means they’re more likely to put all that data to good use later on. Keep in mind that, like any business improvement process, things may shift or evolve along the way.
Securing IoT devices: Fortinet's FortiNAC automates the process

This week, security vendor Fortinet announced its new FortiNAC solution aimed at addressing many of the limitations of current NAC products. FortiNAC came to Fortinet via the acquisition of Bradford Networks made earlier this year and fills a hole in the vendor's “Security Fabric” story that delivers consistent, end-to-end threat protection. The strength of FortiNAC is visibility and how it discovers all the endpoints. Instead of relying on a database or endpoint agents, FortiNAC is completely agentless and automates the discovery of endpoints by ingesting a wide range of data sources, such as RADIUS, SNMP, DHCP, LDAP and others, as well as behavioral information. This lets FortiNAC identify over 1,500 device types compared to other solutions that can identify 500 to 1,000. ... Also, because it pulls information from a wide range of sources, it can identify devices connected on Wi-Fi or the wired network. The majority IoT devices use Wi-Fi, which is where much of the focus has been from the NAC vendors, but the wired IoT endpoints are used widely in many verticals.
Making Change Is Not a Matter of Willpower

“Employees had to revisit their decisions about how to get to work. They could not just mindlessly repeat their old habits. The new office location turned out to be an opportunity for those with strong environmental values to take mass transit rather than drive to work every day.” Changing contexts gave people the opportunity to think about what they were doing. That changed the habit triggers, which in turn created the opportunity to change behavior. “People have challenges in changing behavior because of a misunderstanding about what controls many of our everyday actions,” she says. “Motivation and understanding just aren’t enough on their own to effect change.” Old habits can endure longer than the motivation to try something new, even for the most dedicated of employees. “As leaders, we need to ask: ‘What do I want people to do on a daily basis in this environment?’” She advises, “Understand the underlying context, and make changes needed so that the desired behavior is easy and rewarding.... Everyone responds to that. When your focus is on the behavior, you can create change that outlasts people’s old habits.”
Notes from the frontier: Modeling the impact of AI on the world economy
New research from the McKinsey Global Institute attempts to simulate the impact of AI on the world economy. First, it builds on an understanding of the behavior of companies and the dynamics of various sectors to develop a bottom-up view of how to adopt and absorb AI technologies. Second, it takes into account the likely disruptions that countries, companies, and workers are likely to experience as they transition to AI. There will very probably be costs during this transition period, and they need to be factored into any estimate. The analysis examines how economic gains and losses are likely to be distributed among firms, employees, and countries and how this distribution could potentially hamper the capture of AI benefits. Third, the research examines the dynamics of AI for a wide range of countries—clustered into groups with similar characteristics—with the aim of giving a more global view.
Quote for the day:
"When a man assumes leadership, he forfeits the right to mercy." -- Gennaro Angiulo
No comments:
Post a Comment