10 ways to destroy developer happiness

Who doesn’t get annoyed by endless meetings? Developers are busy people, and
most would rather spend their time coding than talking about it. Meetings that
are not focused and efficient are a frequent source of disenchantment. “Meetings
that drag on without contributing to progress can be very draining,” says Vlad
Gukasov, software development engineer at Amazon. “These often take up valuable
time that could be better spent on actual development work.” ... Unnecessary red
tape can be incredibly frustrating to developers. “Navigating through layers of
bureaucracy can be quite stifling,” Gukasov says. “The complexity of internal
procedures can sometimes hinder the smooth progress of software development.”
Developers like efficiency, says Remi Desmarais, director of engineering and
software development at software company Tempo Software. “They frequently
encounter delays, from waiting for clarification on requirements, to code
processes like compilation, building and testing to seeking approval from code
reviewers, which can hinder their progress,” he says.
Data Center Cooling: Embracing Liquid Cooling for the Era of Sustainable and Efficient Operations

While the adoption of liquid cooling undeniably offers an enticing remedy for
the thermal challenges posed by high-density racks, its integration into data
center management introduces a new set of considerations and complexities. The
deployment of liquid cooling systems necessitates a bespoke infrastructure,
comprising specialized components such as pumps, heat exchangers, and filtration
systems. These elements work in concert to ensure the seamless circulation and
efficient heat dissipation of the liquid coolant throughout the intricate
network of electronic components. Beyond the physical requirements, the use of
liquid coolants imposes a critical need for stringent safety protocols and
specialized training for personnel entrusted with the operation and maintenance
of these systems. The introduction of liquid into the data center ecosystem
marks a shift that extends beyond hardware considerations, demanding a holistic
approach to facility management and personnel training to guarantee the safe and
effective functioning of these advanced cooling solutions.
Meet the industrial metaverse: How Sony and Siemens seek to unleash the power of immersive engineering

According to Siemens CEO Roland Busch, "This will empower customers to
accelerate innovation, enhance sustainability, and adopt new technologies
faster and at scale, leading to a profound transformation of entire industries
and our everyday lives. Together with our customers and partners, Siemens is
proud to announce new products that will bring the industrial metaverse a step
closer to all of us." ... Another interesting phrase Siemens has been using is
immersive engineering. The idea is that engineering, design, and content
creation can be done inside a 3D environment using a toolkit called the
Siemens Xcelerator portfolio. Siemens offers a product called NX Immersive
Designer. This tool is designed to "seamlessly connect the real and digital
worlds." Essentially, users can create a digital twin, a version of a
real-world system modeled and simulated in the virtual world. Digital twins
replicate physical entities with accurate virtual models, helping engineers
simulate performance testing and make predictions about points of failure. The
virtual nature of the twin allows many more variations and usages compared to
the cost and risk of building a single physical prototype.
Leadership opportunities must align with an individual's natural strengths: Gallup’s Rohit Kar
In addressing the correlation between effective leadership and employee
engagement, our approach to leadership development strategy emphasises the
enduring elements that remain constant amid technological advancements and
societal shifts. We prioritise understanding the unchanging fundamental
aspects of human nature, acknowledging that regardless of external influences,
certain core needs persist. At Gallup, when we delve into engagement, we
recognise that employees bring their emotions into the workplace. To measure
these emotions productively, we simplify the process, ensuring it remains
straightforward and outcome-oriented. Our focus lies in enabling managers to
engage in meaningful conversations by providing adaptable frameworks and
tools. We ensure scalability, speed, and agility in our delivery methods to
cater to changing consumption patterns without altering the essence of what we
deliver – because the core principles of management don't require alteration.
Our unique approach lies in retaining fundamental principles while adapting to
the evolving landscape.
New York Times’ blockbuster suit could decide the fate of genAI

Microsoft and OpenAI say their use of copyrighted material is transformative.
They contend the output of the chatbots transforms the original content into
something different. The Times suit claims there’s no real transformation, that
what Microsoft and OpenAI are doing is outright theft. It claims the companies
are not just stealing Times content, but their audience as well, and making
billions of dollars from it. People will have no need to read the Times either
online or in print, if they can get all the newspaper’s information for free
from a chatbot instead, the suit alleges. “There is nothing ‘transformative’
about using The Times’scontent without payment to create products that
substitute for The Times and steal audiences away from it. Because the outputs
of Defendants’ GenAI models compete with and closely mimic the inputs used to
train them, copying Times works for that purpose is not fair use.” ... So, who’s
right? This is not a difficult call. The answer is simple. The Times is right.
Microsoft and OpenAI are wrong. Microsoft and OpenAI are getting a free ride to
use copyrighted material that takes a tremendous amount of time and money to
create, and uses that material to reap big profits.
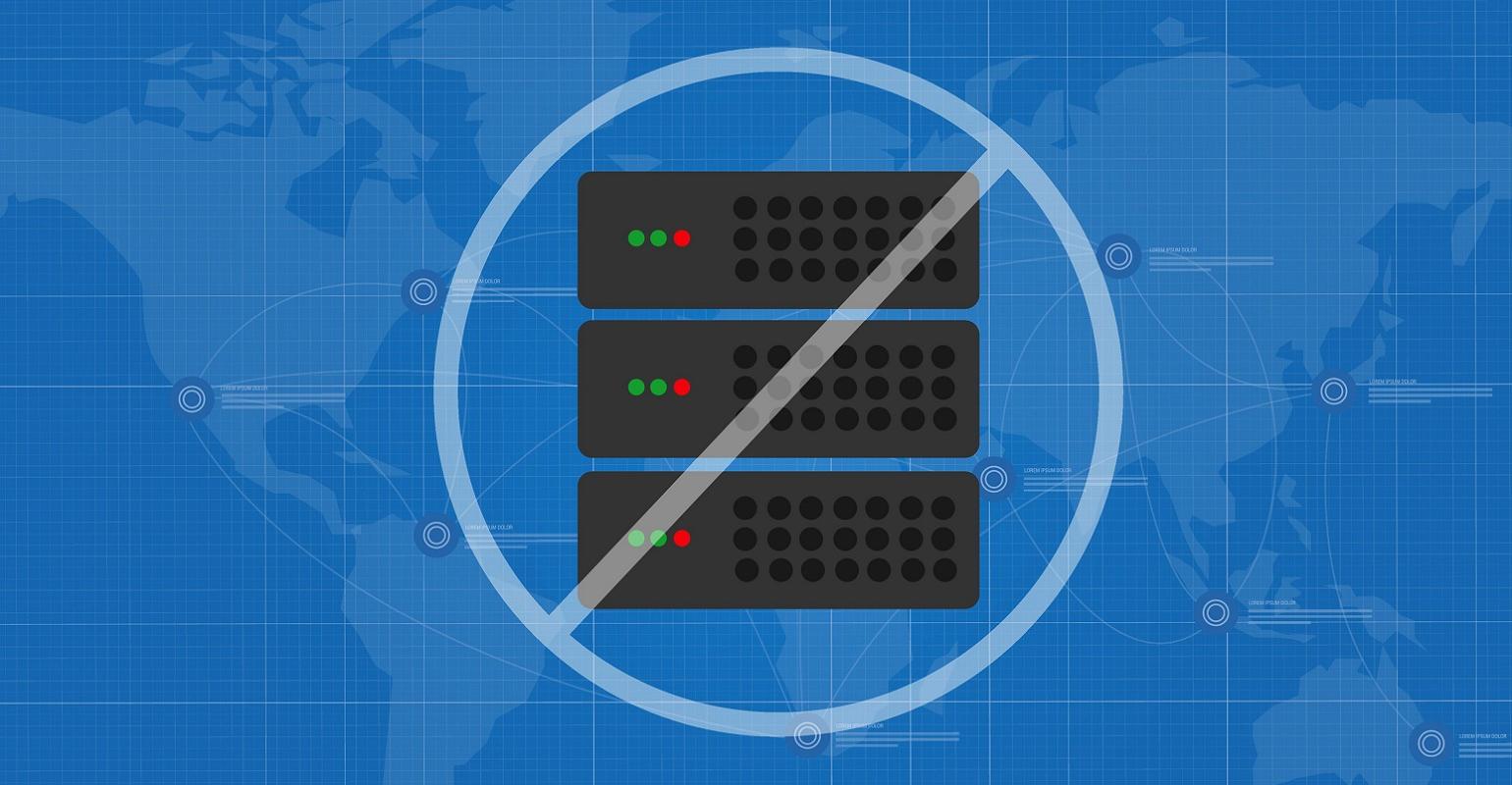
After Orange Disruption, Brace for More BGP Route Hijacking

Orange's attacker appeared to have obtained and used a valid password for the
telco's administrator account with RIPE, for which two-factor authentication
wasn't enabled. Security experts report that the source of the password
appears to have been information-stealing malware called Raccoon. After
gaining access to the account, the attacker used RIPE's hosted RPKI resource
certification service to broadcast a valid, cryptographically signed route
origin authorization to direct traffic to an autonomous system number not
controlled by Orange, resulting in the traffic never reaching its intended
destination. ... The telecommunications giant subsequently told Information
Security Media Group in a statement: "The Orange account in the IP network
coordination center (RIPE) has suffered an improper access that has affected
the browsing of some of our customers." The company said it had immediately
responded and resolved the problem later Wednesday and that "appropriate
measures have been taken to prevent such an incident from happening again."
Data Governance & Controls: An Increasingly Critical Foundation for AML Compliance Programs
Ensuring effective AML compliance necessitates a steadfast commitment to data
accuracy and integrity, achievable only through robust governance. Financial
institutions can only rely on the consistency and correctness of their AML
compliance solutions by establishing stringent controls ensuring accuracy and
integrity. The significance of data accuracy and integrity can easily be seen
in relation to false positive and false negative alerts in transaction
monitoring. False positives, stemming from inaccurate data triggering
unnecessary alerts, can lead to a significant waste of resources and needless
increases in program costs. Conversely, false negatives, arising from
incomplete or unreliable data, may cause suspicious activity to go unreported,
which could lead to potential regulatory action. Financial institutions that
build strong data accuracy and integrity standards into their processes
minimize these risks, thereby enhancing the overall efficiency and efficacy of
their AML compliance program.
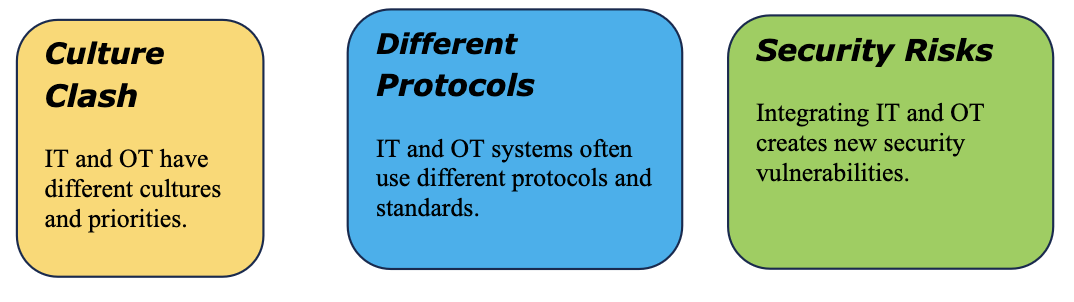
Designing an IT department for a world defined by change

For years, inside the technology department, we’ve referred to “the business”,
meaning everything other than IT, and for its part, “the business” has spent
years trying to isolate IT as a mere cost centre. But nearly a quarter of the
way through the 21st century, the need to integrate digital tools into every
part of business means this splendid isolation no longer really works. Even in
the most performant IT departments, centralised decision-making around tooling
and technology choices falls behind the galloping pace of the market, and it's
difficult to imagine how it could ever be otherwise in a department of finite
resources. ... Still, by refusing to allow the curation of information
technology outside of that provided by the technology function, it becomes a
self-fulfilling prophecy - the only people expected to understand the
challenges of technology are those hired into the IT department. The only way
to break that vicious cycle is to discard the model of the central IT
department. Once you start questioning the existence of the IT department,
it’s only a short journey to rejecting the concept of functional structures
entirely.
Building a Better Analytics Team

Once you have the right group of people on your team, your challenge is to
build an environment where they can work effectively. Ensure that they are
clear about the organization’s mission, vision, values, and objectives. Create
an environment where the connection between your team’s objectives, projects,
and tasks and the targets and objectives of the organization are clear. Team
members need to understand how the data architecture being built will have a
direct impact on the decisions the organization is making and how their
activities further the goal of becoming a more data-driven organization. Team
building is not a one-time activity. It is built into everyday activities,
including goal setting, performance reviews, project planning and execution,
team meetings, and one-on-one meetings between you and your direct reports.
The clarity of purpose is something that increases each time it is reviewed
and as the team’s objectives and goals are refined and realigned. As a leader,
one of your main objectives is to remove obstacles that arise.
The Rise of Dual Ransomware Attacks

Two ransomware attacks mean that companies could be facing more data
encryption, more data exfiltration, more data leaks, and multiple demands for
payment. If an enterprise is dealing with a single attacker behind two
attacks, they could be facing the challenge of different ransomware strains.
How did the two strains impact an organization’s systems, and what will it
take to remediate and return to normal operations? How much data was taken?
Ransomware groups can take that exfiltrated data to leak sites to up the
pressure on victims to pay. If two different attackers are in play, recovery
can be even more complicated. Two different attackers may encrypt the same
files. “We've had a couple of cases where the first ransomware incident
occurs. They encrypted a bunch of files. In the midst of dealing with that a
second attack…those attackers encrypt the encrypted files of the other
attackers,” Minder shares. “If that happens, where you get encrypted files
encrypted again, the likelihood of corruption goes up thousand percent, and
you may not get your files back at all.”
Quote for the day:
“Our greatest fear should not be of
failure but of succeeding at things in life that don't really matter.” --
Francis Chan














:quality(70)/cloudfront-us-east-1.images.arcpublishing.com/archetype/EINOQ3JS4NCVRALXYXLGZV5CYM.jpg)








