SDM and the DevOps Delusion of Connected Organizations

Looking across the enterprise, DevOps cultures fray further. A perfect DevOps
practice envisions teams in different departments, business units and
geographies all in sync, delivering value via software on a reliable cadence.
In reality, enterprise DevOps is difficult to pull off because most
organizations haven’t implemented shared languages, comment processes and best
practices across all of their teams with management buy-in. ... Adopting an
SDM strategy on top of an existing DevOps culture can help an organization in
a number of ways. Having disconnected tools, disconnected data and a lack of
common language make it difficult for one side of the organization to know
what the other wants. Even in mature DevOps implementations, software delivery
ends up being a patchwork of different processes for different teams. It’s
also difficult to determine if our teams are delivering the right end product
if there’s no shared visibility and insight. SDM helps by establishing common
data and common processes, giving visibility and insights across teams of
different maturities, different tools and different technologies so you get
all functions to collaborate. That way you can be sure you’re not just
deploying more—you’re actually delivering continuous value.
Legal Framework Around Blockchain Technology Applications
Firstly, blockchain transactions have no borders and hence, jurisdiction is a
vexed issue. Where and how a dispute can be raised remains an unanswered
question. Blockchain technology depends upon public and private keys allotted
to users and their interface with the hash function. Transactions conducted
through blockchains have a sense of permanence. Though verification and
authentication is the fulcrum of this technology, there is no means of
enforcing a transaction in a court of law. Mistakes cannot be corrected and
hence, the jurisprudence under the Indian Contract Act, 1847 relating to
mistake of fact or law is wholly alien to these transactions. How is one to be
held to a promise made in an entry in a ledger? When does the promisor and the
promisee relation get established? These are all questions for which answers
would have to be found. What happens if a private key is misused or tampered
with? Are there any legal remedies? One doesn't know. There is no central
authority which monitors BT, however, recent adaptations of BT are being used
by governmental authorities for verifying and authenticating ownership of
moveable/immovable assets. What are the responsibilities of such an authority?
The year ahead in DevOps and agile: still some missing pieces to plug in

A big obstacle preventing the success of DevOps is quality control, Jainendra
points out. "Teams are now able to move more quickly. However, error rates are
not decreasing. For now, this can be more easily managed since so many of the
changes are smaller and easier to revert. But as DevOps scales throughout the
enterprise, this will add a layer of complexity to the process. Many
organizations are still seeing quality issues in both their program and
infrastructure code; maintaining low error rates is key for creating a
successful DevOps practice by helping streamline larger releases." There has
been more progress with agile, Jainendra believes. "There's been an increased
interest in scaling agile methods by implementing broader agile management
such as Scaled Agile Framework," he says. "Additionally, teams have benefited
greatly from agile methodology and are seeing productivity boosts as a result
of its ability to create a culture of efficiency. Even as everyone began to
work remotely, we are still experiencing the same team collaboration benefits
as we were before Covid-19." What lies ahead, he states, is a need for
greater customization of agile efforts. "Organizations often fail to tailor
their agile initiatives to their organizations. ..."
The Importance of Technology in the Strategic Design of Workplaces in the COVID-19 Era

One of the principal problems of the shift to working virtually is the feeling
of personal disconnect. Working from home can lead to isolation. For
companies, this means that successfully transmitting their mission and values
can be a difficult task. The problem is exacerbated when you consider that
corporate culture currently drives office design. Co-creation platforms allow
us to carry out interactive activities with employees and receive feedback in
real-time. We use gamification techniques to increase engagement and ensure
employees take ownership of the office design project. These platforms and
activities give us an understanding of the company culture; the unwritten
rules that define the behavior of people in a group. This critical information
helps companies build a more flexible culture that encourages continuous
learning and lets interior design strategists design an office that transmits
and reinforces its values. ... Designing, and above all, explaining online
projects can be complex. We often find that it’s difficult for customers to
understand detailed plans and schematics from behind a screen. With the
integration of the BIM (Building Information Modeling) methodology and virtual
reality technologies, designers can offer companies virtual tours of their
future workspaces.
Are you ready for multicloud? A checklist

IT leaders know the complexities of setting up secure and robust cloud
infrastructures. Naturally, these complexities multiply when you combine
multiple clouds. You should strive to avoid dealing with them all at
once. Operating across multiple clouds is complex because of the required
governance, technical expertise, and integrations. As Sarbjeet Johal, an
independent technology strategist, puts it, “Nobody gets up in the morning and
says we are going to do multicloud today. They just fall into it, mainly due
to organizational silos. Multicloud is as easy as 1-2-3... said no one ever!”
Joanne Friedman, Ph.D. and CEO of Connektedminds, suggests that IT teams
leverage their primary cloud provider wherever possible, rather than hunt for
new or better capabilities in a second provider. ... Other IT leaders share
pragmatic viewpoints on how multiclouds evolve and how to navigate initial
complexities. Travis Campbell, a big data consultant, offers this insight into
where the multicloud journey begins: Companies doing ‘multicloud’ but really
treating it as a single cloud by each line of business are a special case
here. For example, finance may have applications on cloud X, while engineering
is deploying to cloud Y, and there’s no cross-pollination of work and data.
It’s multicloud without hard problems.
Why JSON Isn't a Good Configuration Language
Compared to many other configuration languages, JSON is pretty noisy. There is
a lot of punctuation that doesn't aid human readability, although it does make
it easier to write implementations for machines. In particular, for
configuration files, the keys in objects are almost always identifiers, so the
quotation marks around the keys are redundant. Also, JSON requires curly
braces around the entire document, which is part of what makes it an (almost)
subset of JavaScript and helps delimit different objects when multiple objects
are sent over a stream. But, for a configuration file, the outermost braces
are just useless clutter. The commas between key-value pairs are also mostly
unnecessary in config files. Generally, you will have a single key-value pair
per line, so it would make sense to accept a newline as a delimiter. Speaking
of commas, JSON doesn't accept trailing commas. If you need commas after each
pair, it should at least accept trailing commas, since trailing commas make
adding new entries to the end easier and lead to cleaner commit diffs. Another
problem with JSON as a configuration format is it doesn't have any support for
multi-line strings.
A tech reboot of retail

Looking at the global figures, Michael O’Grady, principal forecast analyst at
Forrester, says: “Retail categories like grocery and essential consumables are
performing well, while other categories like fashion, beauty and cosmetics are
seeing a marked decline in consumer spend.”Predictably, the coronavirus
lockdowns have benefited e-commerce. ... “It’s really important to
understand what people are wearing,” says Capgemini’s Peplow. Image analysis
on social media may be among the approaches fashion retailers will need to use
to remain relevant to high street shoppers. Clearly, operating seamlessly
across multiple channels will become a key line of defence for
bricks-and-mortar retailers to compete with internet retailers. But while
online shopping is convenient and may well offer an item at the cheapest
price, in-store shopping is more than just transactional. There is strong
evidence that high street retailing needs to become more experiential, such as
the way Natuzzi is using mixed reality in its showroom. And while the idea of
stores “3D printing” products may seem far-fetched, Decathlon’s use of the
technology shows there are niches where it works extremely well.
Startups Should Do Things That Don't Scale, but Security Isn't One of Them
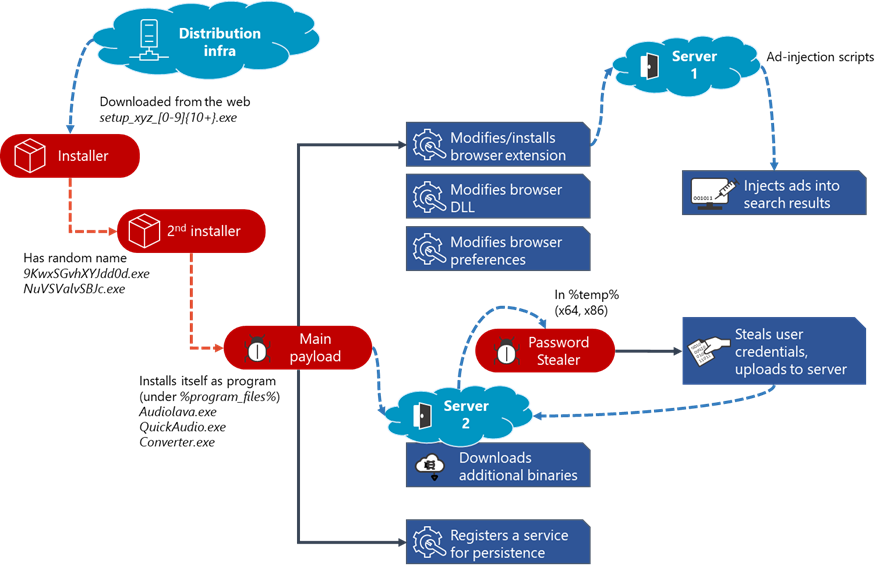
Startups are especially attractive targets to hackers due to a combination of
limited resources and the proliferation of business models that revolve around
collecting customer data. In fact, research shows over 67% of companies with
under 1,000 workers have experienced a cyberattack, and 59% were successfully
breached. Investing in scalable security is a startup's best hope at defending
against an attack that statistics say it should expect. Lack of scalability in
security detracts from efficiency and opens gaps in a startup's networks. It
forces IT to preoccupy itself with the endless application of security to new
resources and users rather than with optimizing or monitoring. In these cases,
companies are often too busy working in the trenches to notice they've been
hacked until it's far too late. It's not all bad news, however. Security is no
longer a zero-sum game. It has been commoditized into various products in recent
years, allowing young companies to balance its risks and rewards by scaling in
pieces that won't become obsolete or demand too much attention from IT. Security
processes like encryption, firewalls, and authorized access once required
hardware and lots of work to operate at scale.
Hacked: US Commerce and Treasury Departments

Reuters first reported the incidents, with The Washington Post suggesting that
a Russian hacking group known as Cozy Bear, aka APT29, is the source. The Post
reported last week that the same group was behind an attack against
cybersecurity firm FireEye. In an update late Sunday, FireEye warned that
starting around March and continuing through May, software updates for
SolarWinds' Orion product had been subverted with backdoors, which it has
dubbed "Sunburst." The malicious software updates were signed using valid
digital signatures, and could steal files, profile systems and disable system
services, it says. FireEye warns that "the actors behind this campaign gained
access to numerous public and private organizations around the world." "We can
confirm there has been a breach in one of our bureaus," the Commerce
Department says in a statement. "We have asked CISA and the FBI to
investigate, and we cannot comment further at this time." The U.S.
Cybersecurity and Infrastructure Agency, or CISA, on Sunday issued an
emergency directive "in response to a known or reasonably suspected
information security threat," noting that the affected Orion products are
versions are 2019.4 through 2020.2.1 HF1.
Moving from Agile Teams towards an Agile Organization
It is not unusual to see different levels across the organization of a large
program talking in different terms. This is normal and expected. The level of
detail that senior management has to deal with cannot be the same as that of the
engineers modifying the cloud infrastructure of the deployment pipeline.
However, when talking about progress, if we have some talking about epics,
others about features, implementation teams discussing stories, and others
working on tasks, it shouldn’t be surprising that nobody really knows what the
actual progress is. In the same way that it is important to agree on the moment
in which progress is measured (e.g. when deploying in production, or when there
is a certain change in some indicator), it is also important to agree on the
unit of measurement to be used. Then we have a common unit of progress that is
atomic. And by making this progress clearly visible, we raise the overall
awareness. This results in a velocity increase that can be potentiated by other
elements of the context. From a systemic point of view, everything matters. Not
only are all elements important, but the relationships between them are
especially meaningful. It is like those images we used to draw when we were
kids, connecting the dots to see the figure hidden in between.
Quote for the day:
"You can discover what your enemy fears most by observing the means they use to frighten you." -- Eric Hoffer