There seems to be an obvious and somewhat necessary solution here to ensure that employees within an organisation are able to understand their IoT data and apply it to their own sector of expertise for maximum business benefit. One of the ways to resolve this skills shortage is to think about training Millennials to drive IoT projects forward in the future. Millennials are our future workforce and, given they are used to being constantly connected, they are perfectly placed to drive further connectivity. You’ll hear this described as entering the sharing economy. Therefore, as we enter this more circular economy, we need to equip employees with the necessary skills in AI, ML and deep learning (DL). By opening up the opportunity for individuals to specialise in these areas, businesses will be able to apply analytics to streaming data for deeper insights. This will enable more predictive decisions to be made and falls into sync with what a data scientist would be doing day by day.
Blockchain Technology A Global Perspective!
The world is innovating without permission. The real essence of Blockchain Technology lies in innovating the Government based applications. The Deleware company corporation records stored on Blockchain, The Sweden operating now real-estate transaction on Blockchain, Singapore issuing invoicing into the Blockchain, The UK using Blockchain based monitors for distribution of grants. In Estonia, e-Citizens records, e-Payments key, medical records secured on Blockchain and the Ghana recording land registry using Blockchain Technology. Last but not the least. The most promising initiative of Smart Dubai — Dubai Blockchain Strategy. The Dubai is on the fast track to implement Blockchain in government operations and it will be the First City in the World to be completely powered by the Blockchain by 2020. After producing bunch of POCs and evaluating hundreds of Blockchain Innovations, with supporting tens of game changing startups around the globe. Now, sharing few easy to implement and potential Blockchain Use Cases to change the society in phenomenal way, all for public and private sectors.
Is It Possible To Learn Data Science & Machine Learning Without Mathematics?

For machine learning, the real prerequisite skill that one needs to learn is data analysis, beginners and there is no need to know calculus and linear algebra in order to build a model that makes accurate predictions. The role of mathematics is particularly significant only if one is involved in machine learning research in an academic setting or for few subsets of more advanced data scientists. There are people in the industry at high levels who are also using advanced math on a regular basis. There are who are pushing the boundaries of machine learning people working on bleeding edge tools. People at companies like Google and Facebook are only ones who certainly use calculus, linear algebra, and more advanced math routinely in their work. The bottom line is that in industry, data scientists just don’t do much higher-level math but I reality they do is they spend a huge amount of their time getting data, cleaning data, and exploring data. The truth is that 80% of what people do is data munging and data visualization.
This Trojan infects Chrome browser extensions, spoofs searches to steal cryptocurrency
Different infection vectors are in place depending on the type of browser found on an infected system. Razy is able to install malicious browser extensions, which is nothing new. However, the Trojan is also able to infect already-installed, legitimate extensions, by disabling integrity checks for extensions and automatic updates for browsers. In the case of Google Chrome, Razy edits the chrome.dll file to disable extension integrity checks and then renames this file to break the standard pathway. Registry keys are then created to disable browser updates. "We have encountered cases where different Chrome extensions were infected," the researchers say. "One extension, in particular, is worth mentioning: Chrome Media Router is a component of the service with the same name in browsers based on Chromium. It is present on all devices where the Chrome browser is installed, although it is not shown in the list of installed extensions."
Machine Learning on Code is actually a field of research that is just starting to materialize into enterprise products. One of the pioneers of movement is a company called source{d}, which is building a series of open source projects turning code into actionable data and training machine learning models to help developers respect technical guidelines. With every company quickly becoming a software company, intangible assets such as code represent a larger share of their market value. Therefore companies should strive to understand their codebase through meaningful analytic reports to inform engineering decisions and develop a competitive advantage for the business. On one hand, managers can use tools like the open source source{d} engine to easily retrieve and analyze all their Git repositories via a friendly SQL API. They can run it from any Unix system, and it will automatically parse their companies’ source code in a language-agnostic way to identify trends and measure progress made on key digital transformation initiatives.
Information theory holds surprises for machine learning
Information theory provides bounds on just how optimal each layer is, in terms of how well it can balance the competing demands of compression and prediction. "A lot of times when you have a neural network and it learns to map faces to names, or pictures to numerical digits, or amazing things like French text to English text, it has a lot of intermediate hidden layers that information flows through," says Artemy Kolchinsky, an SFI Postdoctoral Fellow and the study's lead author. "So there's this long-standing idea that as raw inputs get transformed to these intermediate representations, the system is trading prediction for compression, and building higher-level concepts through this information bottleneck." However, Kolchinsky and his collaborators Brendan Tracey (SFI, MIT) and Steven Van Kuyk (University of Wellington) uncovered a surprising weakness when they applied this explanation to common classification problems, where each input has one correct output (e.g., in which each picture can either be of a cat or of a dog). In such cases, they found that classifiers with many layers generally do not give up some prediction for improved compression.
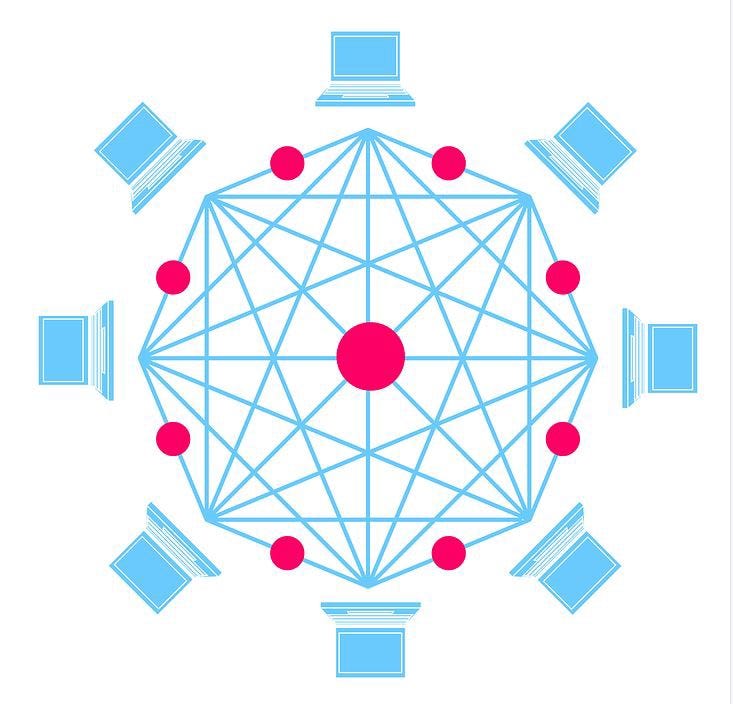
The controversies of blockchain governance and rough consensus
On-chain governance describes the manner of proposing changes to a cryptocurrency and its underlying blockchain by a certain set of processes, rather than a simple majority consensus. The core differences between blockchains can be highlighted by examining exactly how these decisions are made, and by whom. To understand the concept, it’s important to identify all the participants in the network and how they work together. Miners are a core component in a decentralized public blockchain network because they help sustain it. They are incentivized by transaction fees and block rewards. Developers create the protocol and maintain the blockchain. They are also responsible for enforcing changes such as hard or soft forks. Like miners, developers are also incentivized to keep the network going. When developers propose a change to the network, a core group is tasked with achieving consensus over whether to accept or reject them. For miners, they back changes by contributing their hash power to one of the blockchains borne from a hard fork.
Hacking enterprise architecture and service design
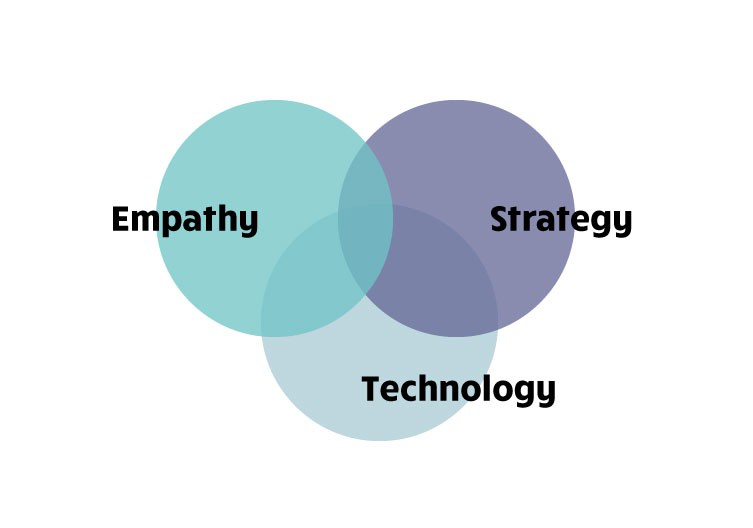
It is not very common for IT architects and service designers to work together. We are usually at the different ends of digital projects. We speak a different language, and often even physically sit in different buildings. As a service designer and enterprise architect, we had the unique opportunity to work together in various projects at D9. We began to identify strengths and weaknesses of each approach and expertise. There are clear commonalities, and in many ways our expertise complements each other. Government is transforming in the wider context of global and societal issues, complex systems and technological change. Our approach is that the traditional role and structures of government are challenged by new technology, human centred design and internal and external strategic drivers of change. To us, digital transformation is about human, strategy and technology. We work in transformation that requires multidisciplinary work in all the three elements. Throughout our work, we identified that a core challenge for digital transformation is a lack of active dialogue between strategy and development.
'Bitcoin will go to zero': Davos talks up the future of blockchain tech

Schumacher said the industry is now trying to create "open decentralized systems." These would essentially be next generation protocols or infrastructure that businesses could run on, similar to cloud computing today. The next generation of blockchain technology is currently being developed. Yeung said that she sees blockchain adoption happening quickly in the area of payments, particularly in Asia. "Many developing countries, where just to start with they don't even have credit cards, there's no particular infrastructure, it's almost easier to see sort of blockchain-enabled payments, to see in Asia, you will see more action happening in Asia more than U.S. and Europe," Yeung told CNBC. Ripple CEO Garlinghouse said he expects more widespread adoption of blockchain in about five years, while Schumacher said that it is three years off. However, Hutchins said that ultimately, consumers will not be talking about what blockchain is being used, they will just care how good the use case of a product is.
The future of code quality, security and agility lies in machine learning

Source code repository analysis can also reveal information about the developers writing it. Team dynamics can be highlighted by analyzing commits time and content: managers can identify when software engineers are the most productive, arranging meetings and encouraging cross-team collaboration accordingly. Looking at programming languages and frameworks trend can inform hiring managers on what type of talent to hire and what upskilling education resources can they provide. Adding source code as a new dataset in enterprises’ data warehouses and visualization platforms such as Power BI, Looker or Tableau will provide everyone in the engineering organization with a whole new level of source code and development process observability. Yet the most exciting aspect of looking at code as a dataset is that it can be used to train Machine Learning models that can automate many different repetitive tasks for developers. We’re already starting to see new machine learning based applications for assisted code review or suggestions on GitHub.
Quote for the day:
"It is easier to act yourself into a new way of thinking, than it is to think yourself into a new way of acting." -- A.J. Jacobs