How Innovation Works And How To Lead It
As a leader, one should always look for the opportunities to develop the team and self to strengthen the delivery and keep the team spirit up. There is always a scope for the leader to improve; it is just a matter to understand why there is an opportunity and what needs to be changed. Once the leader knows why, the next thing is to delimit “HOW”, once the problems are known and the opportunities are identified, then leaders must outline how to tie the loose ends and handle the situation. Some companies and people know HOW they do what they do. Whether you call them a ‘’differentiating value proposition’’ or ‘’unique selling proposition,’’ HOWs are often given to explain how something is different or better. Not as obvious as WHATs , and many think these are the differentiating or motivating factors in a decision. It would be false to assume that’s all that is required.
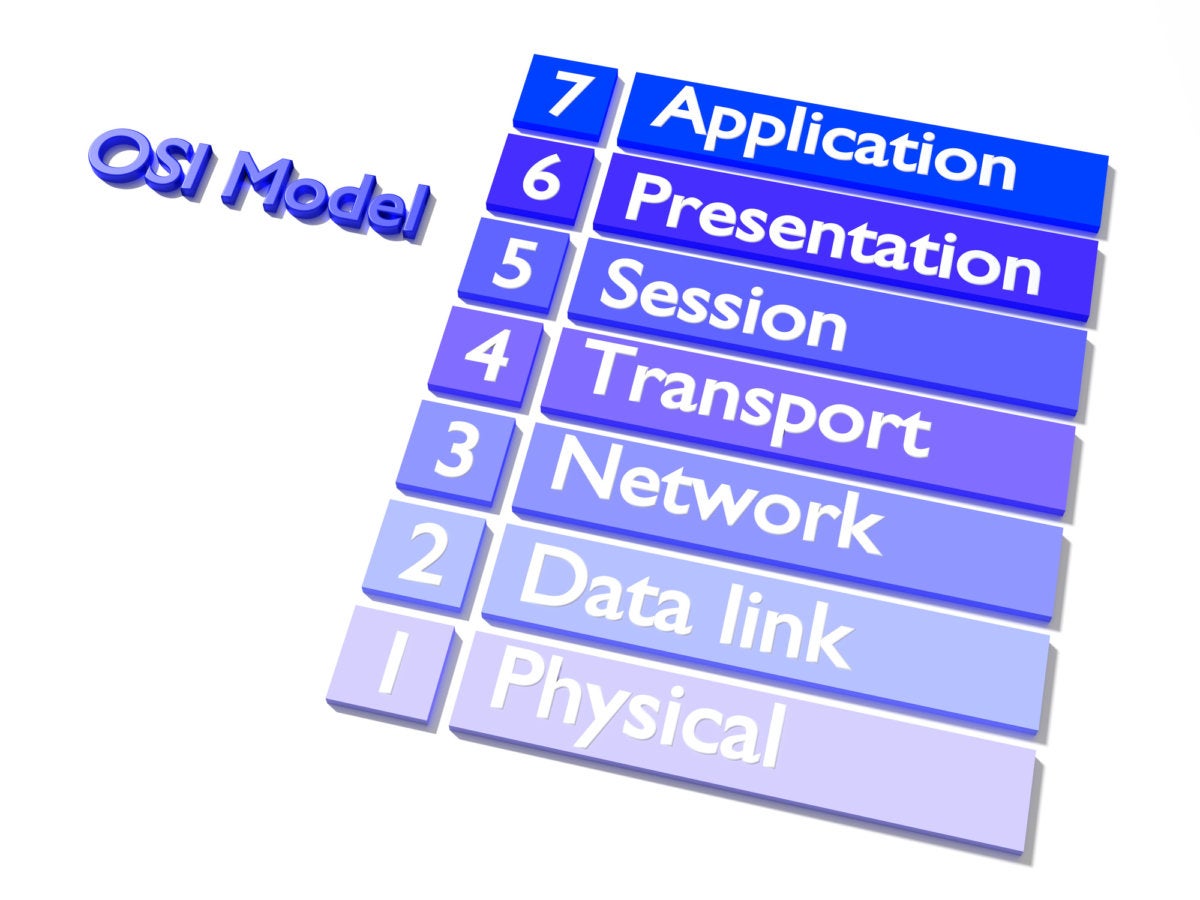
Why Enterprise Security Is A Matter Of Policy
As the most common trigger for policy changes are changes to an application, it’s critical that teams understand exactly what devices and connectivity each application needs in order to function correctly and deliver its benefits, while remaining secure. Therefore, the automation solution should be able to automatically discover and map the connectivity flows for all of the enterprise’s business applications, to show IT and security staff exactly how data flows across the network. ... The automation solution should also enable IT teams to perform proactive risk analysis on planned application connectivity or security policy changes before they are made, to ensure that they don’t introduce security gaps or compliance violations. Then, if no exceptions or issues are identified, the approved changes can be rolled out to the relevant security devices with zero touch – thereby saving significant time, effort, and most importantly helping to prevent misconfigurations which cause outages and security holes.
Why Third-Party Security is your Security
This third-party standard establishes the baseline that third parties must meet, so communicate it to them before you have to rely on them. The standard also serves as the benchmark that your organization will use to measure the third-party security. According to the survey, 57% of respondents suggest establishing a process for evaluating the security protection capability of third parties before engaging in business activities, while 52% recommend establishing a vetting process to ensure all third parties are evaluated and screened against objective security requirements. With a policy and standard in place, now you can set up on-going processes to do that measuring and feedback. Survey results show that 54% of respondents monitor third parties to ensure continued compliance with contractually required security requirements while 44% say they periodically review third parties to objective security requirements.
3 common cybersecurity maturity failings

There’s a common misunderstanding about what constitutes “good security.” Many organizations have reduced this concept to a pure checkbox exercise, without understanding why the boxes must be checked. Good cyber security is not determined by an organization itself, or by comparison with other enterprises. Good cyber security is measured by the success or failure of our adversaries. It is the attackers who determine most of the rules of engagement. IT security’s job is to prevent them from gaining access to the infrastructure, data and whatever else they consider valuable assets. Anything short of that, and the organization is in a security “bad” place. Security maturity helps prevent adversaries from completing the full cyber kill chain. Yet there are many “failings” when it comes to understanding what maturity represents. Let’s consider the top three.
Google ups Chrome security for business users with new features and policies

Chrome admins will now be able to whitelist and blacklist specific extensions in a more scalable way as well. With an updated extensions policy (available now), IT admins can create a policy that will restrict extension access based on permissions, the post said. One example provided would be admins blocking all extensions that need to use a device's camera or microphone. The newest Chrome version also supports the latest version of Transport Layer Security (TLS)—version 1.3—in Gmail, which could improve security and speed. According to the post, Google will be bringing support for TLS 1.3 to the broader web sometime in 2018. Chrome users won't immediately notice any difference with the support of TLS 1.3. However, Google urged admins to make note of any incompatible systems in the Chrome admin forum. In its post, Google also outlined some of the security features that will be coming in 2018.
Shadow IT: How Today's CIOs Graple With Unsanctioned Tech

Shadow IT is a serious affair at SAIC, a $5 billion provider of IT services to government agencies. Because SAIC employs 10,000 people building IT solutions, CIO Bob Fecteau sees shadow IT as essentially DevOps. That is, some groups are building, testing and running their own IT capabilities. “The business says they won’t give me IT support, so we’re going to create operational development capability called DevOps," Fecteau says. "IT occurs in those spaces." While he accepts that IT work is happening outside his purview, he says he is still responsible for knowing how much of the corporate budget is going to IT — whether he sanctions it or not. "What’s relevant is: Can I account for it? Do I understand how much it costs? And do I understand how much it impacts the business," Fecteau says. "If I can answer yes to most of those questions then I’m probably doing my job."
How do you turn these islands into a living IoT lab?

For Villoslada, this IoT infrastructure is in line with the Spanish archipelago's 'sun and data' model and can help turn it into a "lab for IoT technologies and products of the fourth industrial revolution". "IoT will have a profound impact in our digital world. We have the elements to offer citizens a range of services that can be useful," he says. For the moment, a pilot is being carried in the parking lot of the Balearic Technology Innovation Park, or ParcBit, where the technology monitors the occupancy and availability of 1,200 parking spaces. Google has also bought into the idea. It's already offered the Balearic government its own IoT platform and a partner in the form of Spanish consultancy Beeva to conduct another pilot project to optimize the use of moorings in Pollença harbor. According to Villoslada, the Balearic Islands are the first autonomous community in Spain to support this kind of deployment.
Deduplicating Massive Datasets With Locality Sensitive Hashing
Many online platforms that deal with natural language documents face a big problem: thousands of duplicate documents. Duplicates are easily produced in news media when a content producer like Reuters or the Associated Press distributes an article to a number publishers. Each publisher will typically add a paragraph or a footer making each copy slightly different from the others. A web crawler that monitors the sites of the individual publishers will see many almost identical articles as each copy was essentially written by Reuters and only slightly modified by the other publishers. Quora also recently released the Quora Question Pairs dataset. The dataset contains pairs of user generated questions, some of which are semantically the same Here the aim is specifically to find questions that are semantically the same, often those questions are just slighty paraphrased ones.
Why this venture capitalist says blockchain technology and “cryptoassets” are the future of fintech

“We’ve been living in the internet application world, and we’re starting to see peer-to-peer networks forming, but blockchain is really going to be the enabling technology moving forward,” Deaker told the conference. ... The opportunity for blockchain as a massive disruptor lies in the vast amount of “unbanked opportunities” around the world that blockchain technology can solve, said Deaker. She also believes the want from consumers for ease, flexibility, openness, and personalisation (coupled with a prevalence of mobile technology) will drive use cases for blockchain tech. And while the discussion around blockchain usually focuses firmly on the underlying technology, eschewing the tradeable asset parts commonly associated with projects, Deaker said the future of fintech sits in “a bucket broadly defined as cryptoassets”.
Human Resource (HR) staff to be replaced by robots (AI) within 10 years

As McKinsey shows, certain types of tasks are more likely to be automated than others. Technical activities, such as data collection and data processing, are very likely to be automated. (Your company may have already begun automating some of these functions.) Other types of work, such as managing people, planning, or creative work are much less likely to be automated somewhat probably impossible in task. This explains why HR administrative jobs have a 90% chance of being automated by 2035, according to a study from Oxford University, but HR managers, directors and officers are much less likely to be replaced by robots. A robot can spit out data, but it can’t create a strategic plan or mediate a conflict between two employees. In short, robots are likely to take over mundane HR tasks, while the HR tasks that require creativity, problem-solving, decision-making, or people skills will remain the domain of humans.
Quote for the day:
"People tend to make rules for others and exceptions for themselves." -- Anonymous