3 data privacy principles to adopt now, even while governments still debate

Fairness is one of the most powerful guiding principles any brand can adopt for
its use of data, but what does it mean in practice? On the one hand, it’s about
considering how you’re using not just data but the tools and technologies that
help you harness data in your marketing and decision-making. On the other hand,
it’s important to remember we’re not just talking about one moment in time, like
the moment when someone gives you their data, or the moment of an interaction
between them and you, in a store or on your website. It’s about the potential
implications that these moments can have down the line. Could it lead to an
unfair, harmful, or discriminatory outcome for them? Could it keep them from
getting credit? Or a job offer? Could it perpetuate a stereotype about a
protected class of people? Building a foundation of fairness, for example, could
mean implementing policies and procedures to regularly assess the data and tech
you use to ensure they do not have a disparate impact on vulnerable consumers.
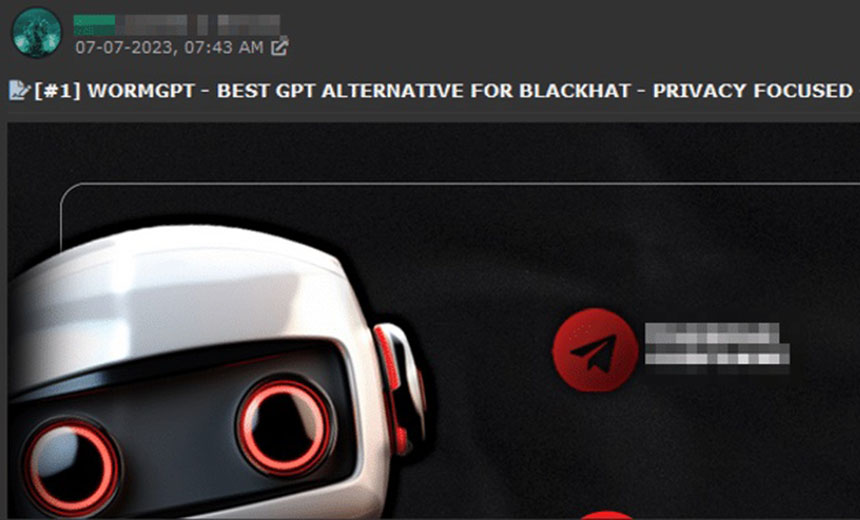
Cyber attackers using Gen AI more effectively than defenders
Both cyber attackers and defenders employ generative AI, but attackers use it
more effectively. Adversaries capitalise on AI/ML, deepfake, facial
recognition, and Augmented Reality/Virtual Reality (VR) (AR/VR) to enhance
hacking strategies against government agencies, businesses, and strategic
targets, surpassing cyber defenders in technological adaptation. Facial
recognition and AR/VR systems illustrate the extensive use of deepfake
technology by cybercriminals. We predict that within two years, social
engineering and phishing attacks will predominantly employ deep fakes, making
defenders' tasks much harder. Malware capabilities have evolved significantly.
Instead of creating static malware, hackers now build multi-behavioural
malware that adapts in real-time. Upon reaching a target, this malware
assesses the environment and generates tailored malicious code, targeting
various systems like Windows, Linux, Outlook, and mobile devices. This is
powered by AI/ML engines, resulting in multi-behavioural, metamorphic, and
polymorphic malware that dynamically alters their code as they spread.
Cloud Robotics: A New Frontier for Internet Technology

Robots connected to the cloud are being used in warehouses and distribution
centers for material handling, order fulfillment, and inventory management
duties. These robots are capable of independent navigation, object recognition
and picking, and teamwork with human personnel. The medical sector is likewise
ripe for transformation because to cloud robots. Robots connected to the cloud
can access patient information, medical records, and cutting-edge
disease-diagnosis algorithms. Cloud robotics alters how we connect with our
domestic environment regarding home automation. Robots with cloud capabilities
can automate harvesting, monitor crop health, and manage resource usage in
agriculture. These robots can use the cloud to evaluate massive volumes of
field data, forecast agricultural yields, and make quick judgments. Cloud
robotics has tremendous promise as we look to the future. Advanced artificial
intelligence (AI) and cloud robotics are being combined as a new trend,
allowing robots to act more intelligently and quickly adapt to their
surroundings.
Organizing Around Business Capabilities

A Value Structure is an idealized teaming structure illustrating how the
organization delivers benefits to its customers. The idealized structure
includes teams and roles to not only operate a capability, but also to build
it. We call this structure the value structure to differentiate it from two
other structures within an organization: formal structure and learning
structure. The formal structure represents the way an organization structures
its activities into jobs and job families, manages compensation and other
aspects of human resources. The learning structure represents the way an
organization learns to improve its performance, including role-based learning,
team-based learning, and establishing a culture of relentless improvement
without guilt or blame. Establishment of a value structure independent from
formal and learning structures enables an organization to begin to change how
it delivers value to customers without the overhead of changing formal
reporting or job titles. The value structure makes impediments to the flow of
value clearly visible so we can either eliminate them or explicitly
orchestrate them.
How to Build True Cyber Resilience

Cyber resilience cannot be achieved by implementing one initiative or
investing in one new technology. “CISOs should focus on the question, ‘How
ready are we?’" says Hopkins. Are organizations ready to detect threats,
respond to them, recover, and adapt to an ever-changing threat landscape? “The
first step to building cyber resilience involves understanding which
cyberattacks are most relevant to an organization based on its industry,
location, IT ecosystem, data type, users, etc.,” says Tony Velleca, CISO at
digital technology and IT service company UST and CEO of CyberProof, a UST
security services company. Once an organization understands its risks, the
question becomes how to detect those threats, stop them, and contain them if
and when they become cybersecurity incidents. The answer lies in a blend of
technology and talent. Combining the power of cybersecurity tools, such as
zero trust and managed detection and response, can help organizations achieve
cyber resilience, but they need to ensure the strategies they deploy make
measurable progress toward that goal.
AI and the evolution of surveillance systems
AI models are influenced by the datasets used to train them. It is imperative
that AI vendors carefully tune and balance their datasets to prevent biases
from occurring. Balancing datasets is a manual process that requires making
sure that the humans visible in the datasets are a good representation of
reality, and do not have biases towards certain human traits. In our case, we
use diverse groups of actors, from all over the world, to play out violence
for our training datasets to ensure they are balanced. Furthermore, testing
regularly for such biases can go a long way. A carefully designed system can
protect and help people without significantly impacting their privacy. This
requires considering privacy from designing to implementing AI systems. I
believe that the future of AI-powered surveillance will see reduced privacy
infringement. Currently, large surveillance installations still require humans
looking at camera streams all the time. In a trigger-based workflow, where
humans take actions after an AI has alerted them, the amount of security
camera footage seen by humans is much less, and thus the risk of privacy
infringement decreases.
Controversial Cybercrime Law Passes in Jordan

A joint statement by Human Rights Watch, Access Now, Article 19, and 11 other
organizations said the bill has several provisions threatening freedom of
expression, the right to information, and the right to privacy, as well as
tightening government control over the Internet. The groups also claimed the
bill will introduce new controls over social media, weaken online anonymity,
hamper free expression and access to information, and increase online
censorship. Meantime the European Union says it recognizes and supports
Jordan's objective to create a strong legislative framework to deal with and
counter cybercrime efficiently, but it contends that some of the provisions of
the new cybercrime law depart from international human rights standards and
could result in limiting freedom of expression online and offline. Liz
Throssell, the United Nations' spokesperson for the UN High Commissioner for
Human Rights, said countries indeed need to take steps to combat cybercrime,
but protecting security online and ensuring online freedoms must be treated as
complementary goals.
Evaluating Open Source: Green Flags to Look For

First and foremost, is the open-source community for the solution vibrant; is
it widely adopted and does the community regularly contribute updates? A
healthily engaged community is a sign that the technology has legs and that
companies are successful with it; it often indicates the extent to which
companies are employing staff to contribute to the community. Closely related
to this point, does the open source technology actually solve the problems you
need solved? With the enormous popularity of open source comes the enormous
hype around novel technologies, but are those technologies actually something
that help solve your business problems in a sustainable way such that you can
be confident that your investments may carry you several years? You should
evaluate the suitability of open source technology in the same way you
evaluate proprietary technology and not let the free or low-cost factors lead
to hasty decisions. Finally, are vendors providing software, services, and
support for the open source technology?
How Threat Research Can Inform Your Cloud Security Strategy

The most important thing to remember about cybersecurity is that it’s not an
action you take, but a practice you follow. Implementing a strong cloud
security posture requires regularly assessing and updating your cloud security
policies in light of new threats or not. This means being proactive in your
protection strategies and planning for the unexpected. Creating an incident
response plan is a great place to start, and continuing employee education and
training will help embed a security-focused mindset across the organization as
a whole. There is no “one right way” to establish a cloud security strategy,
but it’s a sure bet that being informed is a good move. Keeping up to date on
the latest cybersecurity threats and vulnerabilities through sources like the
National Vulnerability Database and Orca Research Pod is a good place to
start. However, proactive measures like implementing best practices,
organizational training, and even bug bounties and other security policies can
go a long way toward creating a well-informed cloud security posture.
Regulatory uncertainty overshadows gen AI despite pace of adoption

In traditional application development, enterprises have to be careful that
end users aren’t allowed access to data they don’t have permission to see. For
example, in an HR application, an employee might be allowed to see their own
salary information and benefits, but not that of other employees. If such a
tool is augmented or replaced by an HR chatbot powered by gen AI, then it will
need to have access to the employee database so it can answer user questions.
But how can a company be sure the AI doesn’t tell everything it knows to
anyone who asks? This is particularly important for customer-facing chatbots
that might have to answer questions about customers’ financial transactions or
medical records. Protecting access to sensitive data is just one part of the
data governance picture. “You need to know where the data’s coming from, how
it’s transformed, and what the outputs are,” says Nick Amabile, CEO at DAS42,
a data consulting firm. “Companies in general are still having problems with
data governance.”
Quote for the day:
"The leader has to be practical and a
realist, yet must talk the language of the visionary and the idealist." --
Eric Hoffer