ESG & Climate Risk Management: Integrating Environmental Data In Ratings

Integrating environmental data into investment strategies allows investors to
identify companies proactively addressing environmental challenges. It provides
a comprehensive picture of a company's sustainability practices, particularly
relevant in industries susceptible to climate risks, such as energy,
agriculture, and transportation. By considering environmental data, investors
can assess a company's resilience to climate change, regulatory changes, and
physical risks such as extreme weather events. They can also evaluate how well a
company aligns with global sustainability goals, such as the United Nations
Sustainable Development Goals (SDGs). Moreover, environmental data integration
helps investors identify companies capitalizing on emerging opportunities in the
transition to a low-carbon economy. Companies with innovative solutions,
efficient resource management, and clean technologies will likely thrive in a
future characterized by climate-conscious policies and consumer preferences.
How New Tech Elevates Release Management’s Quality Standards
ML and AI technology can help with intelligently choosing when to deploy and
roll back a release. In order to recommend deployment tactics, machine learning
(ML) models can learn from previous deployment experiences, including success
rates, user input and mistake patterns. In order to ensure a more dependable and
error-resistant deployment process, AI algorithms can track the deployment
process, evaluate the system’s health and initiate automated rollbacks if
anomalies or severe concerns are discovered. In general, ML and AI provide
valuable capabilities to release management, boosting testing and quality
assurance, streamlining release planning, enabling continuous monitoring,
analyzing release risks and simplifying wise deployment decisions. Utilizing
these technologies enables businesses to improve software quality, streamline
release management procedures, and deliver high-performing applications more
effectively and reliably.
Unleash the Power of Open Source: The SONiC Revolution

As businesses embrace connectivity from core to cloud to edge, network
management becomes more complex. Open source networking, specifically SONiC,
simplifies network management by providing a unified fabric across the entire
network ecosystem. SONiC enables organizations to manage and control their
networks seamlessly, regardless of the deployment location. This simplification
allows for a more consistent and streamlined network management experience,
reducing operational complexities and enhancing efficiency. In addition, SONiC
is built on standards-based open APIs, providing organizations numerous
management platform options to choose from, which is particularly useful for
those already invested in other DevOps, Linux-based, or open source solutions.
... Emerging technologies like AI/ML, 5G, and the data boom at the edge are
transforming business operations and service delivery. These technologies
require a modern infrastructure built on containerized architecture, Ansible
automation, and predictive AI/ML monitoring solutions. SONiC easily enables the
adoption of these technologies, providing the foundation for next-generation
networking.
The Art of Reducing 'Technology Debt' & Winning Digital Transformation Race
Almost every organization is undergoing digital transformation hence a
noticeable surge in investments toward cloud automation, cloud computing, and
cybersecurity services. However, in this scenario, not only the pace at which
organizations should attempt transformation but also about choices they make
during this journey is equally important. All transformations are not mandatory.
In the IT industry, there is a term called 'technology debt,' which basically
means that you are at a specific juncture because of decisions you took years
ago. Technical debt is similar to dark matter; you can deduce its impact but
cannot see or measure it. So for any company deliberating on large-scale digital
transformation, it must ensure to partner with the right tech partners/vendors
to get the right perspective on talent and capability. To strike a balance
between reaping the benefits of transformation and ensuring security, companies
must adopt a multi-faceted approach that can be led by experts effectively.
Companies should thoroughly assess potential partners' cybersecurity measures,
track records, and commitment to data protection.
Spare Some Change: Emotional Debt, Technical Debt, & Preparing for Change

The tricky thing about emotional debt, in particular, is that the collectors are
unpredictable — you can defer payments for months or even years without a single
letter or call, then you run into a health scare, an unexpected bill, or just an
especially bad day, and all of these feelings that you’ve been deferring come
crashing down on you all at once. And it’s important to recognize this emotional
debt translates into workplace well-being; a recent Deloitte study indicates
that many employees are struggling with unacceptably low levels of well-being.
... I had one of these moments recently. I ran headlong into a mental and
emotional wall that I didn’t see coming at all, and at first, it made every part
of life overwhelming. These are the moments when understanding and applying a
strategic planning framework like I provided in my book, Building the Business
of You, provides much-needed structure. I’ve never tackled some of the
challenges I’m dealing with in my personal life before, but I have been a
manager, which means I’ve helped create strategies to help to manage change and
facilitate progress, so I know I can do that.
How to account for hidden costs of digital product development and offset them
Once your digital product is developed and deployed, the journey is far from
over. Ongoing software maintenance and troubleshooting are crucial to ensuring
your product's stability, security, and optimal performance. However, these
aspects can bring forth hidden costs that may catch you off guard if not managed
strategically. Software maintenance involves routine updates, bug fixes,
security patches, and performance enhancements. Failing to allocate adequate
resources to these tasks can lead to a deterioration of your product's
functionality and user experience. Additionally, the need for troubleshooting
arises when unforeseen issues or bugs emerge post-launch, demanding swift
resolutions to avoid disruptions and customer dissatisfaction. ... Outsourcing
grants you the flexibility to scale resources based on the current maintenance
requirements, saving you from the burden of hiring and training additional
staff. You can easily add or reduce resources as needed, ensuring
cost-effectiveness and optimized productivity.
India’s Data Privacy Bill is Back

The Bill itself proposes data protection legislation that allows transfer and
storage of personal data in some countries while raising the penalty for
violations. It suggests consent before collecting personal data and provides
stiff penalties to the tune of Rs.500 crore on those that fail to prevent data
breaches. The Bill applies to processing digital personal data within the Indian
territory and processing it outside of India if such processing is in connection
with any profiling or offering goods or services to data principals within
India. However, it does not apply to non-automated processing or processing for
domestic or personal purposes by individuals and data contained in records that
have been in existence for at least 100 years. ... On the issue of consent, the
Bill notes that personal data of an individual can only be processed for a
lawful purpose for which the concerned individual has given consent or is deemed
to have given her consent. It mentions the consent should be free, specific,
informed, and unambiguous.
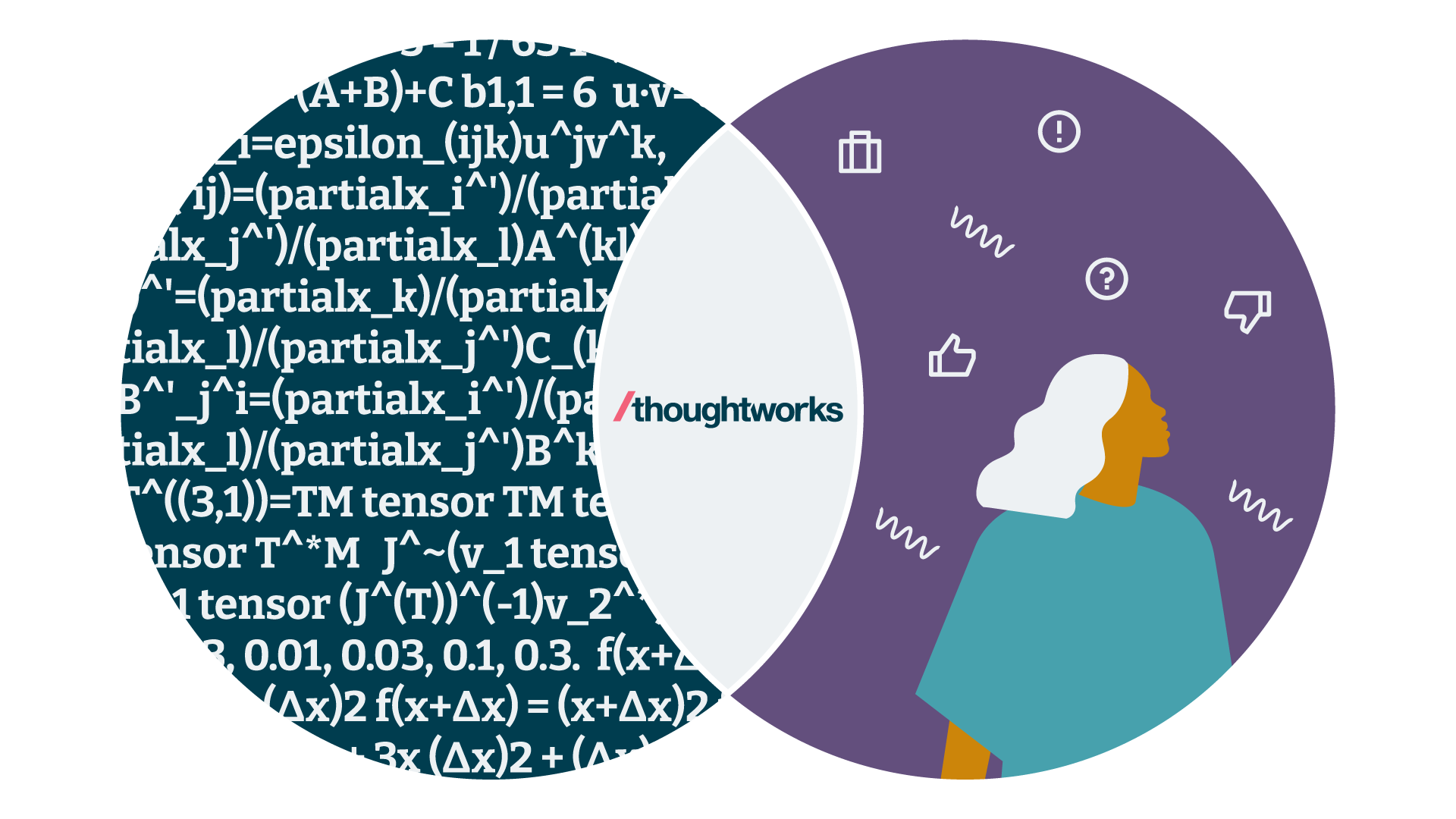
AI Ethics Teams Lack ‘Support Resources & Authority’

Diplomatically approaching one product team after another in hopes of
collaborating only gets ethics workers so far. They need some formal authority
to require that problems be addressed, Ali says. “An ethics worker who
approaches product teams on an equal footing can simply be ignored,” she says.
And if ethics teams are going to implement that authority in the horizontal,
nonhierarchical world of the tech industry, there need to be formal bureaucratic
structures requiring ethics reviews at the very beginning of the product
development process, Ali says. “Bureaucracy can set rules and requirements so
that ethics workers don’t have to convince people of the value of their work.”
Product teams also need to be incentivized to work with ethics teams, Ali says.
“Right now, they are very much incentivized by moving fast, which can be
directly counter to slowly, carefully, and responsibly examining the effects of
your technology,” Ali says. Some interviewees suggested rewarding teams by
giving them “ethics champion” bonuses when a product is made less biased or when
the plug is pulled on a product that has a serious problem.
A 4-pronged strategy to cut SaaS sprawl

IT leaders must conduct regular software audits to identify and assess the usage
of all SaaS applications across the organization. Kamal Goel, senior VP of IT at
Hitachi Systems India, says, “Gather data on software adoption, utilization, and
user feedback to determine which tools are genuinely adding value to the
organization and which ones are underutilized or redundant. This analysis will
help you make informed decisions about which subscriptions to keep, downgrade,
or terminate.” At a previous employer, Goel’s IT department conducted a
comprehensive audit of all SaaS applications and found that multiple teams were
subscribed to a project management tool but most only used a fraction of its
features. “By switching to a more focused and cost-effective project management
tool and discontinuing the old one, the organization saved significant expenses
without compromising productivity,” he says. Oftentimes, teams continue to rely
on existing systems and processes while the quality of data and intelligence in
the new system suffers resulting in its more advanced features becoming
superfluous.
API Standardization and Its Role in Next-gen Networking

APIs are becoming more important because of the way applications are built,
and services are delivered. Applications are composable, relying on integrated
functional elements from different sources. A simple application for most
businesses might need a mobile frontend, a link to a backend database, and a
processing engine in between. And many might use data from third parties.
Standardized APIs would ensure the elements worked together and developers did
not have to start from scratch every time they built a new application. ...
“Increasingly next-generation services like Network-as-a-Service (NaaS)
solutions will be delivered across a system of many providers, and the
networks supporting these services will be fully API-driven,” says Pascal
Menezes, CTO, MEF. “For this to happen, standards-based automation is required
throughout the entire system where all parties adopt a common, standardized
set of APIs at both the business process and operational levels.”
Quote for the day:
"Leadership without mutual trust is a
contradiction in terms." -- Warren Bennis