Finding the Nirvana of information access control or something like it

In the mythical land of Nirvana, where everything is perfect, CISOs would have
all the resources they needed to protect corporate information. The harsh
reality, which each CISO experiences on the daily, is that few entities have
unlimited resources. Indeed, in many entities when the cost-cutting arrives,
it is not unusual for security programs that have not (so far) positioned
themselves as a key ingredient in revenue preservation to be thrown by the
wayside — if you ever needed motivation to exercise access control to
information, there you have it. ... For those who thought they were finished
with Boolean logic in secondary school, its back — and attribute-based access
control (ABAC) is a prime example of the practicality of utilizing the logic
in decision trees to determine access permission. The adoption of ABAC allows
access to protected information to be “hyper-granular.” An individual’s access
may be initially defined by one’s role and certainly fall within the
established policies.
Goodbyes are difficult, IT offboarding processes make them harder
To ensure that the business continues even though the employee is gone, stale
accounts are created with grace periods during which the employee’s
credentials can still be used to access the organization’s networks. This is
great for retaining the knowledge this employee accumulated and ensuring that
their replacement is well-briefed, but since the employee is gone, nobody will
remember to monitor their account, as malicious actors will soon notice. This
employee may also have been forwarding emails to their personal email account
or accessing their work email from personal devices for business purposes,
making it easier for hackers to obtain sensitive company data and impossible
for the organization to know. Existing offboarding processes may frustrate
business executives due to their rigidity – and they aren’t alone in their
annoyance. What’s bad for security is also, inevitably, bad for business.
Security teams today must manually ensure that all access privileges,
including access to various systems, applications, databases and physical
facilities, be promptly terminated.

Leaders are made, not born: Although this is technically correct, which is why
we rarely see 5 year olds running companies or countries (though, in fairness,
the adults that do often fail to provide convincing signs of superior
emotional or intellectual maturity), people’s potential for leadership can be
detected at a very young age. Furthermore, the dispositional enablers that
increase people’s talent for leadership have a clear biological and genetic
basis. ... The best leaders are confident: Not true. Although confidence does
predict whether someone is picked for a leadership role, once you account for
competence, expertise, intelligence, and relevant personality traits, such as
curiosity, empathy, and drive, confidence is mostly irrelevant. And yet, our
failure to focus on competence rather than confidence, and our lazy tendency
to select leaders on style rather than substance (such as during presidential
debates, job interviews, and short-term in person interactions), contributes
to most of the leadership problems described in point 1. Note that when
leaders have too much confidence they will underestimate their flaws and
limitations, putting themselves and others at risk.
How Organizations Can Create Successful Process Automation Strategies
Organizations can promote more collaboration by adopting a modified “Center of
Excellence” (CoE) approach. In some companies, that might mean assembling a
community devoted to process automation tasks and strategies, in which
practitioners can share best practices and ask questions of one another. The CoE
should help members from business and IT teams work together better by
coordinating tasks, avoiding reinventing projects from scratch, and generally
empowering them to drive continuous improvement together. Some organizations may
want to create a central focus on process automation without using the actual
CoE term. The terminology itself carries some legacy baggage from centralized
Business Process Management (BPM) software. Some relied on a centralized
approach for their CoE, counting on one team to implement process automation for
the entire organization. That approach often led to bottlenecks for both
developers and a line of business leaders, giving the CoE a bad reputation with
few demonstrable results.
8 habits of highly secure remote workers

By working in a public place you are exposing yourself to serious
cybersecurity risks. The first, and most direct one is over-the-shoulder
attacks, also known as shoulder surfing. All this takes is for an observant,
determined hacker to be sitting in the same space as you paying close
attention to your every move. ... "As you use public Wi-Fi, you are exposing
your laptop or your device to the same network somebody else can log on to so
that means they can actually peruse through your network, depending on the
security of the local network on your laptop," says Gartner VP Analyst,
Patrick Hevesi. Doing work in a public space while also not using public Wi-FI
may seem like a paradox, but there are simple and secure solutions. The first
is using a VPN when accessing corporate information in public. ... "Your
security is as good as your password, because that's the first first line of
defense," says Shah. "You want to make sure that you have a good strong
password, and also don't use the same password for all the other sites you may
be accessing."
Multicloud deployments don't have to be so complicated

The solution to these problems is not scrapping a complex cloud deployment.
Indeed, considering the advantages that multicloud can bring (cost savings and
the ability to leverage best-of-breed solutions), it’s often the right choice.
What gets enterprises in trouble is the lack of an actual plan that states
where and how they will store, secure, access, manage, and use all business
data no matter where it resides. It’s not enough to push inventory data to a
single cloud platform and expect efficiencies. We’re only considering data
complexity here; other issues also exist, including access to application
functions or services and securing all systems across all platforms. Data is
typically where enterprises see the problems first, but the other matters will
have to be addressed as well. A solid plan tells a complete data access story
and includes data virtualization services that can make complex data
deployments more usable by business users and applications. It also enables
data security and compliance using a software layer that can reduce complexity
with abstraction and automation. Simple data storage is only a tiny part of
the solution you need to consider.
E-Commerce Firms Are Top Targets for API, Web Apps Attacks

Attack vectors, such as server-side template injection, server-side request
forgery and server-side code injection, have also become popular and may lead
to data exfiltration and remote code execution. "This, in turn, may be playing
a role in preventing online sales and damaging a company's reputation," the
researchers said, citing an Arcserve survey in which 60% of consumers said
they wouldn't buy from a website that had been breached in the previous 12
months. SSTI is a hacker favorite for zero-day attacks. Its use is
well-documented in "some of the most significant vulnerabilities in recent
years, including Log4j," the researchers said. Hackers mainly targeted
commerce companies with Log4j, and 58% of all exploitation attempts happened
in the space. The Hafnium criminal group popularized SSRFs, which they used to
attack Microsoft's Exchange Servers and reportedly launched a supply chain
cyberattack that affected 60,000 organizations, including commerce. Hafnium
used the SSRF vulnerability to run commands to the web servers, according to
the report.
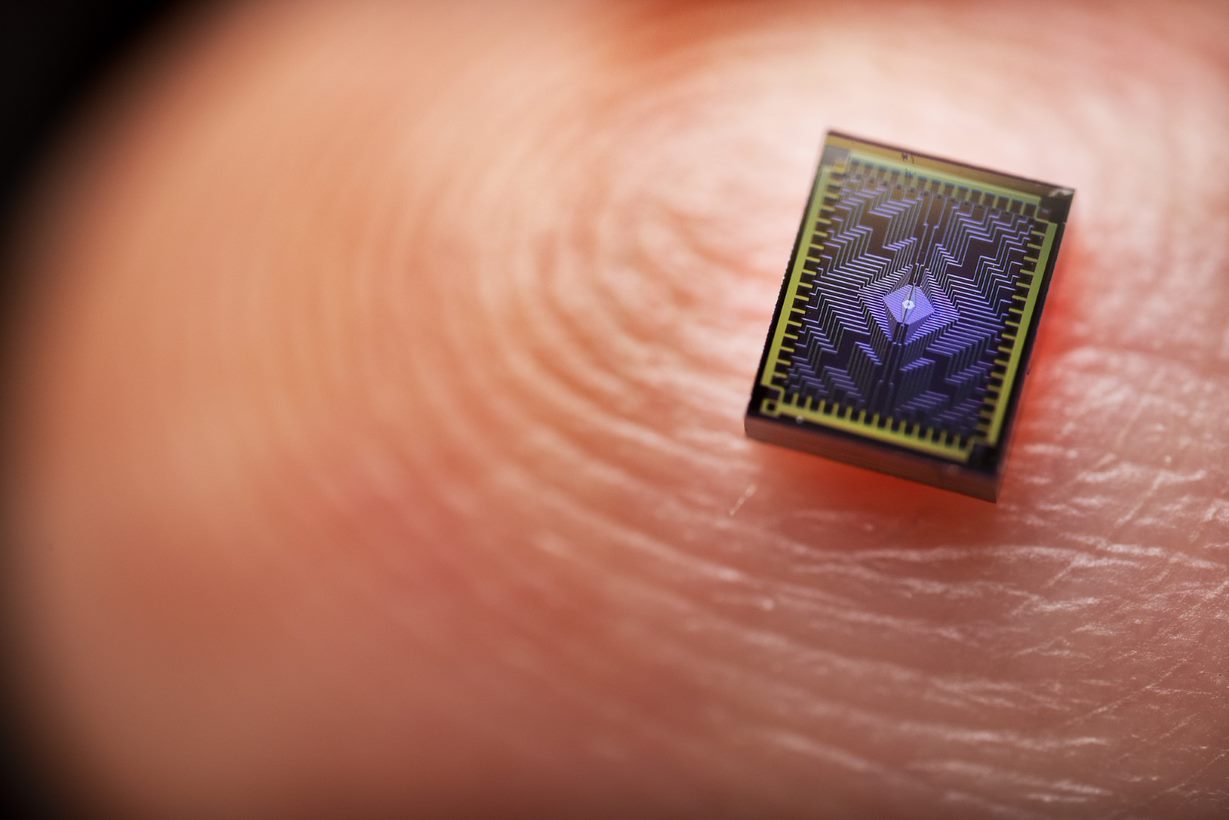
It’s going to take AI to power AI
AI in the datacentre has the ability to act as a pair of eyes, keeping a keen watch on every aspect of the facility to detect and prevent threats. Analysing data from sources such as online access logs and network traffic would allow AI systems to watch for and alert organisations to cyber breaches in seconds. Further, we’re heading in the direction where AI-powered sensors could apply human temperature checks and facial recognition to monitor for physical intrusions. Ultimately, AI will have the opportunity to tune datacentres to operate like well-oiled machines, making sure all components work in harmony to deliver the highest level of performance in our AI-hungry world – a world pressurised by a cost-of-energy crisis and expanding cyber security threats. While the reality is more nuanced, put plainly, it is going to take AI to power AI. In fact, Gartner estimates that half of all cloud datacentres will use AI by 2025. It’s going to be a productive couple of years for industry developing one of the fastest-growing technologies, rolling it out, and doing so in a way that ensures trust.
Beyond ChatGPT: What is the Business Value of Generative Artificial Intelligence?
Beyond the attraction to the technology itself, generative AI has huge
potential business value. Regardless of the processes, professions, or sectors
of activity involved, the common thread among artificial intelligence projects
is their shared objective of enabling, expediting, or enhancing human actions,
either by facilitating or accelerating them. The use of AI usually starts with
a question, or a problem. This is immediately followed by the analysis of a
significant amount of exogenous information or endogenous information, with
the aim of obtaining an answer to the question or problem through the creation
of information useful to humans: aiding decision-making, detecting an anomaly,
analyzing a hand-drawn schema, prioritizing problems to be solved, etc. More
broadly, the automated generation of information makes it easier and safer to
streamline some processes, such as moving from an idea to a first version by
allowing for quicker validation or failure recognition, A/B testing, and
simplified re-experimentation.
Even in cloud repatriation there is no escaping hyperscalers
Hansson’s blog sparked pushback from cloud advocates like TelcoDR CEO Danielle
Royston. She contended in an interview with Silverlinings that those using the
cloud aren’t just paying for servers, but also for the proprietary tools the
different cloud giants provide, the salaries they pay their top-tier developer
talent, the hardware upgrades they make available to cloud users and the
built-in security they offer. For those who use the cloud to its full
potential, she said, the cloud is “the gift that keeps on giving.” Not only
that, but those looking to repatriate workloads will need to invest
significant time and money to transition back and hire more staff to develop
new applications and manage the on-prem servers, she added. ... So, who’s
right? Well, it seems the answer will vary by company and even by application.
Pichai explained the cloud is the ideal environment for a small handful of
workloads, namely “vanilla applications” which incorporate only standard
rather than specialized features and “spikey applications” which need to scale
on demand to accommodate irregular patterns of usage.
Quote for the day:
"To be an enduring, great company, you
have to build a mechanism for preventing or solving problems that will long
outlast any one individual leader" -- Howard Schultz