What is the role of the data manager?

The data manager role is not just about being “good with data”. It involves a
combination of technical and interpersonal skills, says Andy Bell, vice
president global data product management at data integrity specialist Precisely.
As well as technical skills, he says data managers need to have “a thorough
understanding about the application of technology”. In addition, they need to
understand “how data is moved, managed and processed across organisations, what
capabilities it does and doesn’t provide, and how data science teams can use
information in the best way possible”. At the same time, data managers must be
good critical thinkers, according to Bell. “They need to keep up to date with
wider technology industry trends, as well as how legislation and data privacy
regulations impact tools – which may need to be adapted to ensure they are
compliant.” Good communication skills are essential for data managers because
the role requires explaining complex concepts in a simple way. “Increasingly,
data managers are involved in influencing the company in how they should be
using and managing data, which involves great communication skills as well as
commercial awareness,” Bell adds.
3 ways to gauge your company’s preparedness to recover from data loss
Where you store your data backup is nearly as important as creating copies in
the first place. Storing your data in the cloud does not mean it is secure.
Cloud services follow the cloud shared responsibility model, where the service
holds and maintains your data, but your IT staff is primarily responsible for
protecting it. ... Just because your data is backed up does not mean it can be
recovered — without a restoration strategy, you may still lose data. Companies
need a step-by-step plan to salvage their data if it is compromised. If you
decide to pay an attacker, you cannot count on a clean exchange. ...
Write down your recovery plan step by step, including who is responsible for
each task. Run through regular simulation tests with teams and stakeholders
involved in the process to ensure it works. And much like a football coach
reworks plays based on changing conditions, you must make adjustments as
business and technological circumstances evolve. Set a schedule to
periodically review and update the strategy.
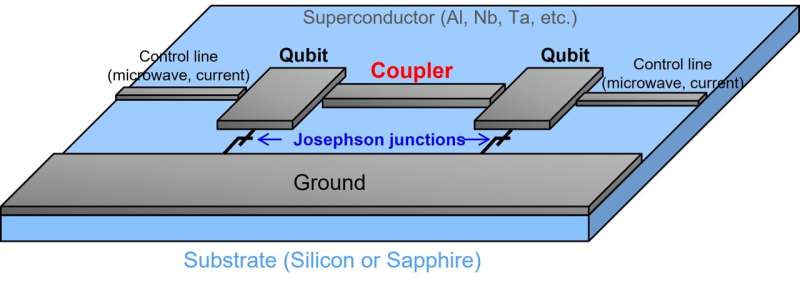
Data Management in Complex Systems
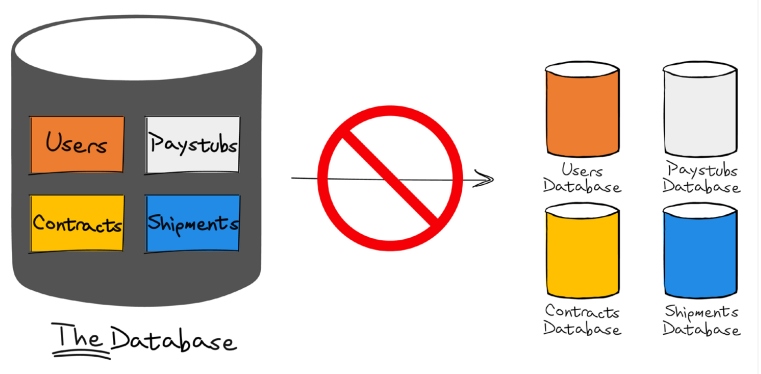
Concerns such as data privacy and provenance are far more important, like being able to audit and analyze who accesses a particular data item and why it can be a hard requirement in many fields. The notion of one bucket in which all the information in the organization resides is no longer viable. Another important sea change was common architectural patterns. Instead of a single monolithic system to manage everything in the organization, we now break apart our systems into much smaller components. Those components have different needs and requirements, are released on different schedules, and use different technologies. The sheer overhead of trying to coordinate between all of those teams when you need to make a change is a big barrier when you want to make changes in your system. The cost of coordination across so many teams and components is simply too high. Instead of using a single shared database, the concept of independent application databases is commonly used. This is an important piece of a larger architectural concept.
Google wants to help Singapore firms tap data, AI responsibly
With organisations worldwide digitally transforming their business, including
those in Singapore and Malaysia, the US cloud vendor is keen to figure out how
its technology and infrastructure can facilitate their efforts. Data,
specifically, will prove critical in enabling companies to tap new
opportunities in a digital economy, said Google Cloud's Singapore and Malaysia
country director, Sherie Ng, in an interview with ZDNET. She said businesses
would need to figure out how to leverage data to better understand and serve
customers as well as to reduce inefficiencies and improve work processes. The
ability to generate insights from the right data also would be essential for
companies to not only birth new businesses and products and services, but also
identify ways to measure and reduce their energy consumption and costs, Ng
said. This meant building digital infrastructures that were global in scale
and able to support real-time access to data, she noted. She added that
organisations in some markets such as Singapore now were looking to gain more
value from their cloud adoption as they moved up the model.
Google Engineer Outlines What’s Next for Angular

“Now we enter into phase three, which is the fruits of our hard work,” Twersky
said. “This phase has yet to happen, frankly. Version 15 is scheduled for
November, so this is very speculative and early preview. But the idea here is
[…] everything that we unlocked.” Version 15 will see support for full
standalones and support for that, she said. “We have something that will
benefit everyone, which is zone JS-enabled async stack taking by default, but
we’re just calling it better stack traces,” she said. This is through another
collaboration with Chrome and will make it easier to pare down to what’s
relevant even when using open source code a developer didn’t write and where
errors occur. Version 15 also promises to make the router tree shakable, which
basically removes unused code from the code base. In writing a standalone
version of the router, the team was able to integrate a lot of things about
the router module that are no longer needed, making it more tree shakable, she
said. The new config API allows developers to tree shake major pieces of the
router API, she said.
Which cloud is for you?

Google Cloud, Lakshmanan goes on, “is about ease of use—a few robust products
that integrate robustly for the most popular needs across all scales.” This is
great so long as you stick with Google’s opinionated approach. If not, be
warned. “If you are building something offbeat, it will be frustrating,” says
engineer Clint Byrum: “GCP is neat and orderly, pretty much one way to solve
any problem, which means it is great for 90% of problems and pretty
frustrating for the 10%.” For all these reasons and despite those issues,
Lakshmanan concludes, “Software developers [and] data scientists love it.” ...
Ant Stanley, who has used all three cloud providers in his consulting
practice, finds much to like about each but hints that Azure is perhaps the
one that adheres most doggedly to its Windows past. This can be a criticism,
but it’s also a source of strength. Microsoft has spent decades making IT
folks very happy. If Azure is a way of continuing that trend, it’s hard to
suggest this is bad strategy or bad technology. Matt Gillard, who also
consults using the different clouds, notes that Azure is very focused on
enterprises and government, both of which run lots of Windows.
Data Management Models for the Cloud
When the organization knows what or who is driving cloud cost, it can
collaborate with those consumers on usage, optimization, and governance policies
that ensure business value is being derived from cloud workloads. Karl Martin,
chief technology officer at integrate.ai, adds a key step is to understand and
plan for the intended ways in which value is to be extracted from the data
assets before implementing a new data management scheme. “Historically,
investments into general-purpose data management tooling, such as data lakes,
were made without a full understanding of how value was to be extracted,” he
says. The strategy often assumed that it would be “figured out later”, which has
produced disappointing results for organizations where there is a struggle to
map a potential wealth of data assets to business problems. “In some cases, the
data management systems do not contemplate the demands of modern machine
learning systems that would be a center of creative experimentation for data
scientists and owners of lines of business,” Martin explains.
Retaining IT talent: 5 tips for better training opportunities
While it’s good to foster growth opportunities, the real benefit comes when you
enable employees to have ownership over these practices. Consider a community of
practice (CoP); this is an excellent avenue for people to interact, learn,
collaborate, and even devise organizational improvements. Traditionally,
employees need executive sponsorship to form a CoP, but try to stay out of the
process until the finish line. Empower staff to create CoP proposals
independently and then sponsor when you can. Employees will likely create
communities around various role-relevant topics like test automation, continuous
delivery, and DevOps. However, even something as simple as a book club can be a
great source of skill development. Allowing staff members to spearhead clubs,
initiatives, or training opportunities relevant to them means that they’ll feel
more ownership over the learning process – and that those lessons are more
likely to stick. It’s counterproductive to give staff the option of creating a
CoP without giving them the resources they need for the group to succeed.
Data privacy audit checklist – how to compile one

When conducting a privacy audit, it’s important to identify the data you have,
where it is stored and what you use it for. “Once you know what data you have,
you need to establish where you got it from,” says Nigel Jones, co-founder,
Privacy Compliance Hub. “Then you can work out what rights you have in relation
to it; what you do with it; where you keep it; how long you keep it; and what
happens when you no longer need it.” This basic inventory will form the basis of
the rest of your audit as well as your Record of Processing Activities (ROPA),
he says. But there is no point keeping data safe within your own organisation if
you then share it with others who do not respect it, Jones points out. “Make
sure you have a list of all organisations you share information with; have
agreements in place with all of them; and be ready to demonstrate why you think
they are safe to process data.” GDPR compliance requires that data is only used
for the purpose it was collected for, so you’ll need to prove your business has
committed to this principle, says Jamie Akhtar, CEO and co-founder of
CyberSmart.
DevOps at Schneider: a Meaningful Journey of Engaging People into Change
Bottom line - telling your story, no matter how bad it may look or sound, but
really pulling back the covers and putting the raw data out there can be
uncomfortable, but is absolutely necessary to ignite your case for change. Spend
time making your case for change less formal and more meaningful and something
people can easily relate to. The best way to do this is by scrapping all those
stiff templates, and crafting your case for change like you are writing a story
and marketing it like you are making the sale of your life! Some fun ways to do
this include using short motion graphic animations vs. boring emails or one-page
PowerPoints, scheduling informal town hall meetings to collect feedback and get
input on what you are trying to do (or sell), and anonymous surveys for
those who are uncomfortable providing feedback in a more formal way. The options
are endless, but think outside the box and make it fun. ... DevOps and Scope
Creep are synonymous - Always come back to the "why" of your DevOps
transformation and use your goals and objectives as your true north to validate
your progress as you get started.
Quote for the day:
"No great manager or leader ever fell
from heaven, its learned not inherited." -- Tom Northup


/2022/09/21/image/jpeg/gDXGTTprNtIwME2brvsIbvXCQuTYgiMbSRTzQVHh.jpg)