Event-driven architecture: Understanding the essential benefits
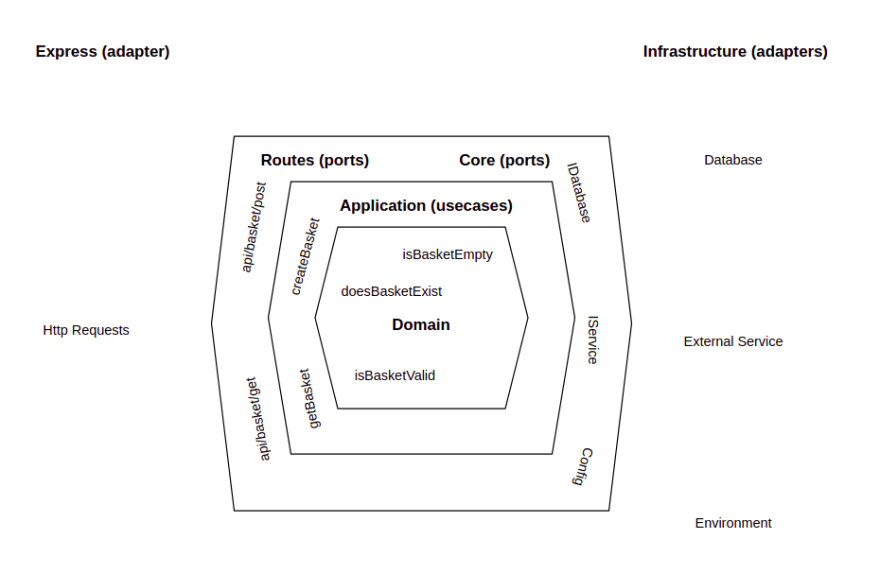
 Event-driven architectures address these problems head-on. At its core,
event-driven architecture relies upon facilitating inter-service communication
using asynchronous messaging. In the asynchronous messaging pattern, a service
sends information in the form of a discrete message to a message broker and then
moves on to other activities. On the broker side, that message is consumed by
one or many interested parties at their convenience. All communication happens
independently and discretely. It’s a “fire and forget” interaction. However,
while things do get easier by focusing on component behavior instead of managing
the burdens of endpoint discovery that go with inter-service communication,
there is still a good deal of complexity involved in taking a messaging
approach. In an event-driven architecture, a component needs to understand the
structure of an incoming message. Also, a component needs to know the format and
validation rules for the message that will be emitted back to the broker when
processing is complete. Addressing this scope of complexity is where a schema
registry comes into play.
Event-driven architectures address these problems head-on. At its core,
event-driven architecture relies upon facilitating inter-service communication
using asynchronous messaging. In the asynchronous messaging pattern, a service
sends information in the form of a discrete message to a message broker and then
moves on to other activities. On the broker side, that message is consumed by
one or many interested parties at their convenience. All communication happens
independently and discretely. It’s a “fire and forget” interaction. However,
while things do get easier by focusing on component behavior instead of managing
the burdens of endpoint discovery that go with inter-service communication,
there is still a good deal of complexity involved in taking a messaging
approach. In an event-driven architecture, a component needs to understand the
structure of an incoming message. Also, a component needs to know the format and
validation rules for the message that will be emitted back to the broker when
processing is complete. Addressing this scope of complexity is where a schema
registry comes into play.
Prevention Is the Only Cure: The Dangers of Legacy Systems
As companies organize their first post-pandemic steps back into an office or hybrid workflow, the threat from legacy systems is greater than ever. In part, this is due to the legacy of shadow IT, in which systems or devices are introduced without explicit IT department approval. It is more than likely that the rapid shift to work from home caused an uptick in shadow IT, attack surfaces, and exposure to related vulnerabilities. Large corporations like Shell have proven time and again that they are vulnerable to these attack vectors, but they may not need to be as concerned about shadow IT as their midsize counterparts. While large staff size may increase the potential for mismanagement, major corporations are also more likely to have systems and audits in place to manage their environment and control changes. Many midsize businesses and enterprises may be less aware of weaknesses in their system that leave them exposed to shadow IT's risks. How can a firm prevent the proliferation of legacy or shadow IT? The only solution is the proper management of all aspects of IT.Data is the Cure for What’s Ailing the Supply Chain
 The data generated through an end-to-end RFID solution provides an additional
key benefit: sustainability. Fact: As the decade progresses, there will be
increasing pressure on companies to help achieve global climate goals, while
meeting increased consumer demands. According to a recent report from McKinsey,
“consumer companies will have to greatly reduce the natural and social costs of
their products and services to capitalize on rising demand for them without
taxing the environment or human welfare.” Because data captured through an RFID
solution is utilized to increase the velocity of moving goods onto trucks, it
can also be used to configure and optimize space on the truck according to the
most efficient route to the destination of packages. Aggregating the data
enables movement of packages along the most efficient route. Accurately boxed
and shipped packages results in fewer trucks on the road and fewer airplanes in
the air. Simply stated, the carbon footprint is minimized through data: simply
by knowing what you have, and in what order you should be delivering it.
The data generated through an end-to-end RFID solution provides an additional
key benefit: sustainability. Fact: As the decade progresses, there will be
increasing pressure on companies to help achieve global climate goals, while
meeting increased consumer demands. According to a recent report from McKinsey,
“consumer companies will have to greatly reduce the natural and social costs of
their products and services to capitalize on rising demand for them without
taxing the environment or human welfare.” Because data captured through an RFID
solution is utilized to increase the velocity of moving goods onto trucks, it
can also be used to configure and optimize space on the truck according to the
most efficient route to the destination of packages. Aggregating the data
enables movement of packages along the most efficient route. Accurately boxed
and shipped packages results in fewer trucks on the road and fewer airplanes in
the air. Simply stated, the carbon footprint is minimized through data: simply
by knowing what you have, and in what order you should be delivering it.The evolution of the modern CISO
 With remote work poised to remain a mainstay in societal patterns, and growing
interest in a “work from anywhere” mentality continues, the onus to be adaptable
has never been higher for CISOs. For CISOs, there’s a fine balance between
continuing to make progress on strategic initiatives that will reduce risk and
improve security maturity, while also being adaptable enough to stop and pivot
as needed. Further, as businesses adapt to meet the growing needs of the
customer, the business needs to do so with CISOs in mind in order to stop and
ask the right questions to enable secure-from-the-start—such as, “Will this new
technology we’re onboarding potentially open up new security gaps?” or “Does
branching into new sectors open our business up to new areas of attack?” and
“Could we expose our customer base to threats by switching CRM platforms?” To be
able to answer these questions, CISOs need to be able to adapt across three
major areas that are constantly shifting and inherently intertwined: the needs
of the business and customer, the current threat landscape, and risk calculation
and prioritization.
With remote work poised to remain a mainstay in societal patterns, and growing
interest in a “work from anywhere” mentality continues, the onus to be adaptable
has never been higher for CISOs. For CISOs, there’s a fine balance between
continuing to make progress on strategic initiatives that will reduce risk and
improve security maturity, while also being adaptable enough to stop and pivot
as needed. Further, as businesses adapt to meet the growing needs of the
customer, the business needs to do so with CISOs in mind in order to stop and
ask the right questions to enable secure-from-the-start—such as, “Will this new
technology we’re onboarding potentially open up new security gaps?” or “Does
branching into new sectors open our business up to new areas of attack?” and
“Could we expose our customer base to threats by switching CRM platforms?” To be
able to answer these questions, CISOs need to be able to adapt across three
major areas that are constantly shifting and inherently intertwined: the needs
of the business and customer, the current threat landscape, and risk calculation
and prioritization.A better future of work is coming, but only if we make the right choices now
 It sounds like an almost idealistic vision of work, particularly for those who
have spent the majority of their careers tied to a desk with little say over how
they approach or structure their role. But evidence increasingly suggests that
those businesses who do offer greater flexibility, including the ability to work
remotely, are likely to attract and retain the most-skilled workers. Tech
workers in particular are getting more choosey about where they work. After a
year of rapid digital transformation across industries, demand for professionals
with cloud, cybersecurity and software development skills are peaking. Couple
that with the fact that tech workers increasingly want to work remotely , and
will potentially change roles if it enables them to do so, and it stands to
reason that flexible-working policies are crucial to enticing top digital
professionals. However businesses pursue their agendas, Wilmott and Walsh both
warn that organizations risk introducing further inequalities if they don't
manage the move to hybrid delicately For workers whose roles are primarily
on-site, Walsh says there is room for organizations to explore how they can
offer at least some of the benefits enjoyed for those who can work
remotely.
It sounds like an almost idealistic vision of work, particularly for those who
have spent the majority of their careers tied to a desk with little say over how
they approach or structure their role. But evidence increasingly suggests that
those businesses who do offer greater flexibility, including the ability to work
remotely, are likely to attract and retain the most-skilled workers. Tech
workers in particular are getting more choosey about where they work. After a
year of rapid digital transformation across industries, demand for professionals
with cloud, cybersecurity and software development skills are peaking. Couple
that with the fact that tech workers increasingly want to work remotely , and
will potentially change roles if it enables them to do so, and it stands to
reason that flexible-working policies are crucial to enticing top digital
professionals. However businesses pursue their agendas, Wilmott and Walsh both
warn that organizations risk introducing further inequalities if they don't
manage the move to hybrid delicately For workers whose roles are primarily
on-site, Walsh says there is room for organizations to explore how they can
offer at least some of the benefits enjoyed for those who can work
remotely. Embed Data Science Across the Enterprise
The organizational model should reflect the maturity of the AI capabilities.
For organizations just getting started with AI, a centralized model typically
builds critical mass. Then, it should be distributed. I like a hybrid model.
Being fully decentralized is like herding cats—the technology does not get
leveraged effectively. At J&J, IT owns the technology that underpins AI:
cloud computing, data repositories, APIs. But we’ve embedded the data science
in our functions, where it is closest to the business problems we’re looking
to solve. We’ve also created a data science council, with representation from
each part of the business, that oversees our portfolio, talent, and
technology. ... Think of data as an asset. Very few companies are embracing
data as the core of insight and decision-making. That requires spending time
to understand where you’re at with data and where you want to go. Also, never
underestimate the need for change management in increasing the use of AI. I
could develop all the models in the world, but if no one is using them,
there’s no value. You’ve got to work with the people who want to evolve.
 The entirety of the Covid-19 pandemic has served as a case study in the
cascading effects of social change. Things barely imaginable just over a year
ago are now a part of daily life. In the context of enterprise, these changes
manifest as both shifts in consumer behavior and new challenges for businesses
— none of which have been unaffected. Against this background, the role of
e-commerce has grown immensely. It’s not just niche items being ordered online
anymore; in 2020, over 50% of all consumers used direct-to-consumer sales
channels to buy everyday items like groceries, cleaning products and other
consumer-packaged goods. In fact, online grocery sales more than doubled,
growing 54% last year and nearly reaching the $100 million mark.
Brick-and-mortar was suffering even before the pandemic hit, but now appears
to be actually on the decline, with fewer new storefronts opening in 2020 than
in any of the three years prior. Even more surprisingly, a full 60% of
interactions between consumers and businesses now take place online.
The entirety of the Covid-19 pandemic has served as a case study in the
cascading effects of social change. Things barely imaginable just over a year
ago are now a part of daily life. In the context of enterprise, these changes
manifest as both shifts in consumer behavior and new challenges for businesses
— none of which have been unaffected. Against this background, the role of
e-commerce has grown immensely. It’s not just niche items being ordered online
anymore; in 2020, over 50% of all consumers used direct-to-consumer sales
channels to buy everyday items like groceries, cleaning products and other
consumer-packaged goods. In fact, online grocery sales more than doubled,
growing 54% last year and nearly reaching the $100 million mark.
Brick-and-mortar was suffering even before the pandemic hit, but now appears
to be actually on the decline, with fewer new storefronts opening in 2020 than
in any of the three years prior. Even more surprisingly, a full 60% of
interactions between consumers and businesses now take place online.
 More than four out of 10 companies admitted they don’t know where all of their
unstructured data is located. Nearly every company surveyed reported managing
access to unstructured data as difficult, specifying numerous challenges such
as too much data, a lack of single access solution for multiple repositories
and lack of visibility into access – including where data lives and who owns
it. It is unsurprising, given this data, that a Canalys report found companies
spending record sums on cyber security in order to protect the rapid digital
transformation we have experienced over the last year. 50% of European
businesses stated that investing in new security technology was their highest
prevention spending priority. Yet, despite these efforts and intentions, the
number of successful attacks continues to be higher than ever, with Canalys
reporting that “more records were compromised in just 12 months than in the
previous 15 years combined.” ... Looking even more closely at the research, we
can connect the dots between these findings and the rise in cloud adoption,
the unstructured data that resides in the apps and systems in the cloud, and
IT’s attempts at securing this monster network of information.
More than four out of 10 companies admitted they don’t know where all of their
unstructured data is located. Nearly every company surveyed reported managing
access to unstructured data as difficult, specifying numerous challenges such
as too much data, a lack of single access solution for multiple repositories
and lack of visibility into access – including where data lives and who owns
it. It is unsurprising, given this data, that a Canalys report found companies
spending record sums on cyber security in order to protect the rapid digital
transformation we have experienced over the last year. 50% of European
businesses stated that investing in new security technology was their highest
prevention spending priority. Yet, despite these efforts and intentions, the
number of successful attacks continues to be higher than ever, with Canalys
reporting that “more records were compromised in just 12 months than in the
previous 15 years combined.” ... Looking even more closely at the research, we
can connect the dots between these findings and the rise in cloud adoption,
the unstructured data that resides in the apps and systems in the cloud, and
IT’s attempts at securing this monster network of information.
 Stress testing is a type of testing that verifies the reliability and
stability of software applications. The goal of this kind of testing is to
measure the error handling capabilities of the software to ensure that it does
not crash under extremely heavy load conditions. Let us consider two scenarios
where website traffic may increase: During an online sale or holiday season, a
website can experience a tremendous spike in online traffic; When a blog
site is mentioned by an influencer or news outlet, then the website can
experience increased traffic; It is imperative to stress test a website
to ensure that it can accommodate spikes in traffic, as failure to do so will
result in a loss in revenue and an inconsistent brand image. To summarize, the
following can be listed as some of the end goals of running a software stress
test: A stress test helps to analyze which type of user data (if any) is
corrupted; The test helps to determine any triggers that signal
risk; It helps to identify any hardware features that can affect software
endurance; Stress test helps predict failures connected to high loads.
Stress testing is a type of testing that verifies the reliability and
stability of software applications. The goal of this kind of testing is to
measure the error handling capabilities of the software to ensure that it does
not crash under extremely heavy load conditions. Let us consider two scenarios
where website traffic may increase: During an online sale or holiday season, a
website can experience a tremendous spike in online traffic; When a blog
site is mentioned by an influencer or news outlet, then the website can
experience increased traffic; It is imperative to stress test a website
to ensure that it can accommodate spikes in traffic, as failure to do so will
result in a loss in revenue and an inconsistent brand image. To summarize, the
following can be listed as some of the end goals of running a software stress
test: A stress test helps to analyze which type of user data (if any) is
corrupted; The test helps to determine any triggers that signal
risk; It helps to identify any hardware features that can affect software
endurance; Stress test helps predict failures connected to high loads.
 Cooperation between The Data Mine and the private sector has included
discussions with the Central Indiana Corporate Partnership, which Ward says
focuses on economic development in the state and interconnection between
companies. Through his conversations with colleagues from the C-suite, Ward
says many executives do seem to understand the need for data science talent
and actively foster connections with universities. That could see more people
with data science enter the workforce as well as give internal staff chances
to grow in their careers. The Data Mine is a way for Purdue to keep up with
the changing technology, infrastructure, and tools of data science, Ward says.
“Think of data-driven projects as being much larger than just science or just
engineering, maybe with some traditional disciplines.” ... The focus of the
program is student centric, with Ward’s office in the students’ residence
hall. As companies retool and think ahead for how data driven insights can
lead to business impact, he says Data Mine works with students on nine-month
projects over the academic year. “We’ve completely gotten away from the idea
of having a 10-week internship,” Ward says. “It’s just way too short to have a
substantial experience.”
Cooperation between The Data Mine and the private sector has included
discussions with the Central Indiana Corporate Partnership, which Ward says
focuses on economic development in the state and interconnection between
companies. Through his conversations with colleagues from the C-suite, Ward
says many executives do seem to understand the need for data science talent
and actively foster connections with universities. That could see more people
with data science enter the workforce as well as give internal staff chances
to grow in their careers. The Data Mine is a way for Purdue to keep up with
the changing technology, infrastructure, and tools of data science, Ward says.
“Think of data-driven projects as being much larger than just science or just
engineering, maybe with some traditional disciplines.” ... The focus of the
program is student centric, with Ward’s office in the students’ residence
hall. As companies retool and think ahead for how data driven insights can
lead to business impact, he says Data Mine works with students on nine-month
projects over the academic year. “We’ve completely gotten away from the idea
of having a 10-week internship,” Ward says. “It’s just way too short to have a
substantial experience.”
Quote for the day:
"The test we must set for ourselves is not to march alone but to march in such a way that others will wish to join us." -- Hubert Humphrey
How E-Commerce Is Being Forced to Evolve In a Post-Covid World
 The entirety of the Covid-19 pandemic has served as a case study in the
cascading effects of social change. Things barely imaginable just over a year
ago are now a part of daily life. In the context of enterprise, these changes
manifest as both shifts in consumer behavior and new challenges for businesses
— none of which have been unaffected. Against this background, the role of
e-commerce has grown immensely. It’s not just niche items being ordered online
anymore; in 2020, over 50% of all consumers used direct-to-consumer sales
channels to buy everyday items like groceries, cleaning products and other
consumer-packaged goods. In fact, online grocery sales more than doubled,
growing 54% last year and nearly reaching the $100 million mark.
Brick-and-mortar was suffering even before the pandemic hit, but now appears
to be actually on the decline, with fewer new storefronts opening in 2020 than
in any of the three years prior. Even more surprisingly, a full 60% of
interactions between consumers and businesses now take place online.
The entirety of the Covid-19 pandemic has served as a case study in the
cascading effects of social change. Things barely imaginable just over a year
ago are now a part of daily life. In the context of enterprise, these changes
manifest as both shifts in consumer behavior and new challenges for businesses
— none of which have been unaffected. Against this background, the role of
e-commerce has grown immensely. It’s not just niche items being ordered online
anymore; in 2020, over 50% of all consumers used direct-to-consumer sales
channels to buy everyday items like groceries, cleaning products and other
consumer-packaged goods. In fact, online grocery sales more than doubled,
growing 54% last year and nearly reaching the $100 million mark.
Brick-and-mortar was suffering even before the pandemic hit, but now appears
to be actually on the decline, with fewer new storefronts opening in 2020 than
in any of the three years prior. Even more surprisingly, a full 60% of
interactions between consumers and businesses now take place online.
Keeping up with data: SaaS, unstructured data and securing it with identity
 More than four out of 10 companies admitted they don’t know where all of their
unstructured data is located. Nearly every company surveyed reported managing
access to unstructured data as difficult, specifying numerous challenges such
as too much data, a lack of single access solution for multiple repositories
and lack of visibility into access – including where data lives and who owns
it. It is unsurprising, given this data, that a Canalys report found companies
spending record sums on cyber security in order to protect the rapid digital
transformation we have experienced over the last year. 50% of European
businesses stated that investing in new security technology was their highest
prevention spending priority. Yet, despite these efforts and intentions, the
number of successful attacks continues to be higher than ever, with Canalys
reporting that “more records were compromised in just 12 months than in the
previous 15 years combined.” ... Looking even more closely at the research, we
can connect the dots between these findings and the rise in cloud adoption,
the unstructured data that resides in the apps and systems in the cloud, and
IT’s attempts at securing this monster network of information.
More than four out of 10 companies admitted they don’t know where all of their
unstructured data is located. Nearly every company surveyed reported managing
access to unstructured data as difficult, specifying numerous challenges such
as too much data, a lack of single access solution for multiple repositories
and lack of visibility into access – including where data lives and who owns
it. It is unsurprising, given this data, that a Canalys report found companies
spending record sums on cyber security in order to protect the rapid digital
transformation we have experienced over the last year. 50% of European
businesses stated that investing in new security technology was their highest
prevention spending priority. Yet, despite these efforts and intentions, the
number of successful attacks continues to be higher than ever, with Canalys
reporting that “more records were compromised in just 12 months than in the
previous 15 years combined.” ... Looking even more closely at the research, we
can connect the dots between these findings and the rise in cloud adoption,
the unstructured data that resides in the apps and systems in the cloud, and
IT’s attempts at securing this monster network of information.Everything You Need To Know About Stress Testing Your Software
 Stress testing is a type of testing that verifies the reliability and
stability of software applications. The goal of this kind of testing is to
measure the error handling capabilities of the software to ensure that it does
not crash under extremely heavy load conditions. Let us consider two scenarios
where website traffic may increase: During an online sale or holiday season, a
website can experience a tremendous spike in online traffic; When a blog
site is mentioned by an influencer or news outlet, then the website can
experience increased traffic; It is imperative to stress test a website
to ensure that it can accommodate spikes in traffic, as failure to do so will
result in a loss in revenue and an inconsistent brand image. To summarize, the
following can be listed as some of the end goals of running a software stress
test: A stress test helps to analyze which type of user data (if any) is
corrupted; The test helps to determine any triggers that signal
risk; It helps to identify any hardware features that can affect software
endurance; Stress test helps predict failures connected to high loads.
Stress testing is a type of testing that verifies the reliability and
stability of software applications. The goal of this kind of testing is to
measure the error handling capabilities of the software to ensure that it does
not crash under extremely heavy load conditions. Let us consider two scenarios
where website traffic may increase: During an online sale or holiday season, a
website can experience a tremendous spike in online traffic; When a blog
site is mentioned by an influencer or news outlet, then the website can
experience increased traffic; It is imperative to stress test a website
to ensure that it can accommodate spikes in traffic, as failure to do so will
result in a loss in revenue and an inconsistent brand image. To summarize, the
following can be listed as some of the end goals of running a software stress
test: A stress test helps to analyze which type of user data (if any) is
corrupted; The test helps to determine any triggers that signal
risk; It helps to identify any hardware features that can affect software
endurance; Stress test helps predict failures connected to high loads.Preparing Future Data Scientists for Jobs of Tomorrow
 Cooperation between The Data Mine and the private sector has included
discussions with the Central Indiana Corporate Partnership, which Ward says
focuses on economic development in the state and interconnection between
companies. Through his conversations with colleagues from the C-suite, Ward
says many executives do seem to understand the need for data science talent
and actively foster connections with universities. That could see more people
with data science enter the workforce as well as give internal staff chances
to grow in their careers. The Data Mine is a way for Purdue to keep up with
the changing technology, infrastructure, and tools of data science, Ward says.
“Think of data-driven projects as being much larger than just science or just
engineering, maybe with some traditional disciplines.” ... The focus of the
program is student centric, with Ward’s office in the students’ residence
hall. As companies retool and think ahead for how data driven insights can
lead to business impact, he says Data Mine works with students on nine-month
projects over the academic year. “We’ve completely gotten away from the idea
of having a 10-week internship,” Ward says. “It’s just way too short to have a
substantial experience.”
Cooperation between The Data Mine and the private sector has included
discussions with the Central Indiana Corporate Partnership, which Ward says
focuses on economic development in the state and interconnection between
companies. Through his conversations with colleagues from the C-suite, Ward
says many executives do seem to understand the need for data science talent
and actively foster connections with universities. That could see more people
with data science enter the workforce as well as give internal staff chances
to grow in their careers. The Data Mine is a way for Purdue to keep up with
the changing technology, infrastructure, and tools of data science, Ward says.
“Think of data-driven projects as being much larger than just science or just
engineering, maybe with some traditional disciplines.” ... The focus of the
program is student centric, with Ward’s office in the students’ residence
hall. As companies retool and think ahead for how data driven insights can
lead to business impact, he says Data Mine works with students on nine-month
projects over the academic year. “We’ve completely gotten away from the idea
of having a 10-week internship,” Ward says. “It’s just way too short to have a
substantial experience.”Quote for the day:
"The test we must set for ourselves is not to march alone but to march in such a way that others will wish to join us." -- Hubert Humphrey