The Role Of Big Data And Mobile Apps In Healthcare

The use of sensors to monitor everything – from whether a patient took the right dose of medication at the right time, to whether their insulin levels are in check – is one of the big growth areas in the Internet of Things (IoT). Combining this with the global adoption of mobile devices, especially smartphones and wearables, means our health can be monitored on a continuous and proactive basis by AI. If a problem is detected, a healthcare professional can be alerted to take appropriate action. While the benefits of such constant surveillance of one’s health, especially in cases of patients with chronic or life-threatening illnesses, are obvious, they also bring added risk. Where there is a sensor, there is vulnerability and the risk of cyberattacks. Recently, Johnson and Johnson warned diabetes patients of the possibility of hackers affecting their insulin dosages. Although the probability is low (and possibly would have been lower without the publicity), this does raise fears of attacks on prominent people who need to manage their insulin.
Digital Is About Speed — But It Takes a Long Time

The ability of digital technologies to accelerate business is giving rise to new value propositions — value propositions that use information to eliminate hassles, enhance awareness, and create solutions. Companies succeed in the digital economy by converting meaningful digital value propositions into revenue-generating digital offerings. We define digital offerings as information-enriched customer solutions wrapped in engaging customer experiences. The great irony is that, while new digital offerings are accelerating the pace of business, they only gradually come to fruition. That is because established companies are usually designed for efficient delivery of their existing products. They are not designed as software companies that rapidly build — and just as rapidly change — their customer offerings. Digital demands entirely new approaches to imagining, designing, delivering, and servicing those value propositions. Consequently, organizational transformation cannot be speedy. ... it takes time — and longer than you might think — to identify and then deliver a new digitally inspired value proposition. The experiences of Royal Philips highlight why.
Global Digital Operations 2018 Survey
Distinct from Industry 3.0, which involved the automation of single machines and processes, Industry 4.0 encompasses end-to-end digitization and data integration of the value chain: offering digital products and services, operating connected physical and virtual assets, transforming and integrating all operations and internal activities, building partnerships, and optimizing customer-facing activities. PwC’s Strategy& interviewed 1,155 manufacturing executives in 26 countries to develop an index that ranks companies by digital operations maturity, from Digital Novices, Digital Followers, Digital Innovators to Digital Champions. Based on the study data, we were able to create a sweeping portrait of Digital Champions — companies that have taken digitization to the highest degree — and assess what it takes to be a Digital Champion through the lens of the four essential ecosystems they must master and orchestrate.
Private by design: Why Apple’s iOS meets the needs of healthcare IT

Apple already has industry-leading security and privacy built in, and a proven commitment to software patches means c.80 percent of all actively used Apple devices are running the most recent version of the OS. Apple’s recently introduced Health Records app for iPhone is clear evidence of Apple’s advantage. It makes patient data portable in such a way as to put the patient in complete control of that data. “I think the good thing about the Apple solution is that the data only resides on the end-user’s device,” Mike Restuccia, CIO at Penn Medicine told Computerworld. “So, we don’t have access to that. Apple doesn’t have access to the data. The beauty of the solution is it is patient managed, patient controlled and patient centered.” That’s fine, but with cloud-based data analytics expected to become a big driver for future mobile healthcare innovation, the need for privacy will become even harder to meet. Such solutions will require data leave the device in such a way as to provide sufficient information for real-time insights and positive health interventions, while at the same time retaining total patient privacy.
Change is Good When It’s Free, Easy, and Has a Happy Endpoint
When a company announces a new version of something I rely upon in my personal life, like Apple announcing a new iPhone, I cringe. Of course, the thought of the latest and best is exciting, but the thought of upgrading – the cost, the hassle – usually makes me wait (longer than my teenage son would like). The same can be said for our customers who are happy using McAfee virus protection to secure their environment. As a McAfee senior product marketing manager focused on endpoint security and endpoint detection and response solutions for enterprises, I can tell you that today that’s not enough. Cyberthreats continue to evolve, no matter how much we resist change. We must move to a modern endpoint defense solution that can detect zero-day threats, and stop them in their tracks. Now, wait a minute before you go running for aspirin because you are thinking, “This is going to cost a lot of money! This is going to be complex and hard to manage!” We thought about that. Upgrading may be easier than you think.
Using data to cross the finish line

Two such areas are geospatial and translytical – both emerging disciplines that hold large amounts of data that were previously untapped. Geospatial data analysis brings together GIS, the system of record for maps, and ERP tools to overlay data onto maps for increased visibility and insights on a geographic basis – a particularly useful tool for applications like smart cities looking to improve traffic patterns, public transportation routes, energy grids and emergency response. Translytical data is another emerging data source that has seen tremendous growth of late, though industry leaders are still defining the term. Gartner defines translytical database architectures as hybrid transactional/analytical processing (HTAP), meaning they work to make operational data more analytical. According to a recent Forrester report, the growth of translytical is due to the fact that “more enterprise architecture pros see translytical as critical for their enterprise strategy.”
Examine CORD architecture's benefits and challenges

CORD offers a new business model to achieve the benefits of NFV. It provides an architecture for open hardware and open software that will reduce overall equipment costs, thus lowering Capex. Networking operators can upgrade their network technology without hardware dependency. A vibrant ecosystem of open source software will accelerate innovation and potentially allow service providers to deliver new services to customers more rapidly. A number of suppliers offer CORD-specific products and development efforts, including Radisys, Calix and Adtran. CORD is early in its adoption cycle, with limited production deployment at this time. CORD architecture has a number of variants -- e.g., R-CORD and M-CORD -- and may not coalesce into a standard with enough critical mass to affect the market. Like NFV, CORD needs to attract a broader ecosystem in terms of NFV hardware, software and services suppliers.
How mobile devices in the travel industry can improve customer service with AR

With competition increasing from Airbnb and other vacation rentals, hotels have been focused on winning over customers by creating immersive, exciting experiences. In that way, augmented reality could be a revolutionary technology. Developers have already identified multiple use cases for AR in hotels. Individual rooms can be outfitted with virtual markers that pull up information about housekeeping, room service and other hotel amenities. Lobbies can overlay maps and directions to navigate the hotel and find luggage checks, pools and other attractions. Hotels can also use AR as a supplement to concierge services, such as providing virtual directions for taking public transportation across the city or finding interesting attractions nearby. Because hotels offer a physical space that travelers spend so much time in, each property represents a gold mine of AR markers that can increase engagement and customer satisfaction. Most travelers know what it’s like to look at a historic building and not entirely know what they’re looking at or why it’s important.
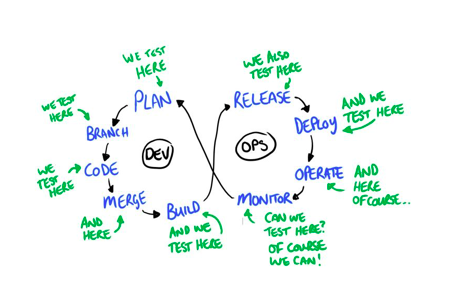
Agile Development & Remote Teams - 6 Powerful Productivity Hacks You Should Know

Agile environment is backed by the idea to make clustered or in-house teams more productive. AGILE CULTURE RUNS ON THE PRINCIPLE OF TEAM COLLABORATION, CONTINUOUS LEARNING & PLANNING, AND SEAMLESS INTERACTION. As businesses go global, expand to different geographies, teams become more scattered with talent from less competitive markets working on projects around the clock. Effective collaboration between remote teams using Agile, as one of the new-age development models, has proven to be very effective. However, Agile development and remote teams sometimes have friction and fall into different sorts of challenges such as: Building rapport with team members; Coordinating across time zones; Scheduling meetings when both teams are online together only for a short duration; and Collaboration among different development cultures. To ease this conflicting situation, organizations require a hybrid Agile development approach specifically targeted towards streamlining and powering up remote software development.
11 signs you’re writing great code

Even if you have a modern debugger that you can attach to your runtime and step through your code, the world just does not work that way. Meaning, you code may run somewhere else, it may be serverless, it may be multithreaded or distributed, or it may run on a cloud somewhere. In those environments, it may not behave the same as on your computer. So, you’re going to need a log. And that means you need a logging framework. You need to write the code and set up the logging in a way that makes the log readable or at least digestible with some sort of log reader. You need to make this part of your software going in. If you fail to do so, you end up doing production deployments to deploy logging code to debug a production problem. In other words, your hair is on fire and you are walking into an oil refinery. At long last, write unit tests. This is a red line. Leave any company that traps you in the old “business case for writing unit tests” discussion—chaos and hell is going to follow this discussion.
Quote for the day:
"Success is liking yourself, liking what you do, and liking how you do it. -- Maya Angelou