Architecturally Aligned Testing
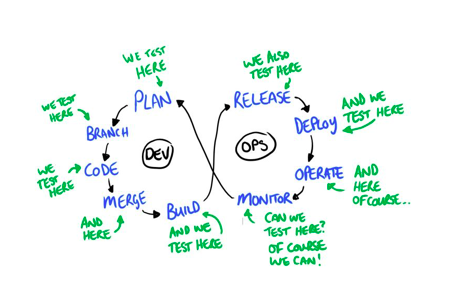
A loosely coupled system follows a service autonomy principle as its architecture is based on the decomposition in autonomous parts. Microservices are increasingly being adopted by organizations to improve the autonomy of their teams and increase the speed of change. Microservice applications are composed of those small, independently versioned, and scalable customer-focused services that communicate with each other over standard protocols with well-defined interfaces. ... Microservices are often accompanied by DevOps: In agile and DevOps, there is no separate design phase with an architect responsible to define the architecture prior to the development phase. Instead, the architecture is defined more federated, addressed across the project, and owned by the whole team. And how is the test approach changing for those systems? Also testing is typically not done anymore in a separate test phase by an independent test team. Instead, everybody is responsible for the quality.
The event took place as part of the digitalswitzerland challenge, a joint initiative from several of Switzerland’s leading businesses aimed at driving digitalization efforts across the country. The group said the idea emerged from the realization that an alternative to the current cumbersome, time-consuming and paper-intensive process of business registration needed to be introduced in Switzerland. By shifting the entire process encompassing the entrepreneur, lawyer, bank, notary and commercial register to a digital workflow and Hyperledger blockchain and by utilizing smart contracts, the key steps can be processed instantly, drastically reducing the amount of time spent toward verification. “The bank will state that the capital money has indeed been paid; the notary will confirm that the necessary documents have been provided, read over, and approved; and the commercial register does the final check that everything is lawful. If all of the conditions are met, then the filing, which up until that point will have been provisional, will be officially registered with the Commercial Register and Official Gazette of Commerce,” the group explained.
Microsoft's New Cortana Chief Plans To Put Her Smarts In More Places
If Soltero’s words are any indication, Cortana’s future will have her ranging far and wide beyond Windows. “The guiding light for us is the assistant concept, and the idea that you want to help people get more out of their time, and whether actively or proactively make the things that you do every day easier or better or more effective,” Soltero said. Cortana continues to be her most helpful when she can keep an eye on you and find ways to help. “Part of that means looking at a person throughout their day,” Soltero explained, “looking at opportunities and the different kinds of places where...an assistant technology or product experience or whatever you want to call it can provide.” That means Cortana will continue to pipe up when she senses a need. “What we’ve noticed, I guess, and what the world has shown us is that you can start by being convenient,” Soltero added. “There is actually a path towards earning the right to be an assistant.” This is how Microsoft sees Cortana’s next steps: less flash, more utility. But Soltero also said that doesn’t always play well with a user base that looks for the next big thing.
The future of enterprise IoT
As enterprise IoT grows, I was interested in what use cases would take hold first. Karen Panetta, an IEEE Fellow and dean of Graduate Engineering Education at Tufts University, looked to consumer applications like “deep learning on household security monitoring and energy consumption information.” Already, she said, “consumers can set their thermostats and virtually ‘answer their doorbell’ from anywhere. Next will come understanding exactly where that energy is being used within the household, such as how much energy goes into lighting, heating, doing laundry, TV, and computers.” At the same time, of course, that will give companies a much deeper understanding of how customers spend their time. On a more explicitly enterprise level, “IoT technologies that have a rapid return on investment (ROI) are the most likely to take off first, and that means “reducing costs through automation,” said Kayne McGladrey, an IEEE member and director of Integral Partners, an identity and access management (IAM) consultant firm.
Social Engineering: It's time to patch the human

In short, if we don't patch the human – no matter how good the tech is – we're still going to have problems. "Everybody wants to build a Blinky Box, and build technology that intercepts and protects the human, instead of getting humans to be developed and educated enough to protect the technology. They're not a liability, they're an asset. [Humans] are the biggest intrusion detection system that you're going to get." There's an assumption within some circles that continuous awareness training is a too difficult of a battle to fight within a given organization. Depending on scope, it can be a resource drain on time and money. Yet, equally as difficult is the recovery from socially-based attacks when they could've been prevented. The harsh truth though, is that information security really isn't part of the average worker's job, and even if there are some security elements, they're an afterthought, not the core. "We're not making information security part of the user's job, and if it's not part of their job, then it's not their concern and they don't care about it," Street said.
New Microsoft Teams features on deck, but more work needed
Over the past six months, Microsoft has moved many Skype for Business features into Teams. The vendor announced in September 2017 that cloud-based Skype for Business in Office 365 would transition to Teams. Despite its progress, however, Microsoft still has work to do, especially for full enterprise voice features. Many key Microsoft Teams features -- particularly for meetings and calling -- are expected to launch by the end of the second quarter this year. Other calling capabilities -- such as call park, group call pickup, location-based routing and shared line experience -- are expected by the end of this year. The migration roadmap for Skype for Business to Microsoft Teams includes 70 enterprise voice features, according to Lori Wright, general manager of Microsoft Teams and Skype. Microsoft delivered half of those features by January 2018, Wright said. The vast majority of overall voice features should be completed by June 2018, she added.
How blockchain could solve the internet privacy problem

There are many blockchain specifications, and many of them are based on open-source software. The Sovrin Network is based on the Linux Foundation's Hyperledger Indy specification, which was built from the ground up for verifying a user's identity. Blockchain networks, or distributed electronic ledgers, can protect the identity of users behind a randomly generated hash table, a type of cryptographically signed credential, to prove the digital identity information in the identity owner's possession. Once a business or organization has verified information about a person, a simple icon can be used approve a transaction. Besides being used for bitcoin and other cryptocurrency transactions, blockchain has most recently been adopted for business transactions, such as automating supply-chain management and cross-border money exchanges. In short, many businesses and governments believe blockchain could underpin a new trust economy, one constructed of person-to-person (P2P) transactions and not dependent on more traditional methods such as credit ratings or guaranteed cashier's checks.
Data scientists that produce data-driven products rule the market
In a data-driven product organization, the data science team will also work closely with the product manager, head of product or chief product officer, as invariably the data scientists will likely be the biggest contributors to the organization's product designs and ultimate success. What is a data-driven product? In straightforward terms, a data-driven product is a software, service or platform that is able to solve deeply complex problems by utilizing a number of different machine learning algorithms. These algorithms will vary from the straightforward all the way to much more complex programs that utilize deep learning and artificial intelligence. There isn't an industry where data-driven products aren't becoming mainstream. Demand for this role: In these data-driven project firms, the product is defined by the quality of data that goes into it and the ability of the said product to create actionable insight through machine learning. Due to this, the data science team is absolutely indispensable.
What Hackers Do: Their Motivations & Their Malware

The malware writer or distributor may also be paid to infect people’s devices with completely different types of malware. It’s a renter’s market out there, and if the malware controller can make more money renting the compromised devices than they can make alone, they will do it. Plus, it’s much less risk for the controller in the end. Many hackers (and hacking groups) use malware to gain access across a company or much broader array of target victims, and then individually select some of the already compromised targets to spend more effort on. Other times, like with most ransomware, the malware program is the whole ball of wax, able to compromise and extort money without any interaction from its malicious leader. Once released, all the hacker has to do is collect the ill-gotten gains. Malware is often created and then sold or rented to the people who distribute and use them. ... Today, most hackers belong to professional groups, which are motivated by taking something of value, and often causing significant harm. The malware they use is designed to be covert as possible and to take as much of something of value as is possible before discovery.
Google's Fuchsia could replace Android and unite all devices

There is a lot of uncertainty around Fuchsia, but we know a few things about it. It’s rumoured there could be a launch in 2019 at the very earliest. Its user interface comes in two animal-named versions; Capybara for the desktop, and Armadillo for mobile, the OS is built using a brand new kernel called ‘Zircon’, instead of using Linux like Android does, and it’s all designed to be continuously upgraded. At the moment, Android has a fragmentation problem where most users run older versions. It also contains a feature called ‘Ledger’ which will synchronise all your devices together, letting you start writing something on one machine and finish it on another. Apps for Fuchsia can be made using Flutter, a Google-made software development kit that is already in use for its existing operating systems. Developers and intrepid users have been able to look at a basic preview of Fuchsia by downloading the files to Google’s Pixelbook, the only device currently supported.
Quote for the day:
"The successful man doesn't use others. Other people use the successful man. For above all the success is of service" -- Mark Kainee

No comments:
Post a Comment