Big Data Driven Smart Transportation: the Underlying Story of IoT Transformed Mobility
For public transportation, big data analytics have transformed both the plan and operations phases on planning and demand modeling, predictive maintenance, and event response. New big data tech-savvy has brought more personalized services to public transportation users, such as offering ancillary services to providing recommendations about additional destinations to visit as part of an upgrade to the passenger’s journey, etc. The big data driven smart public transportation influences both automated and human decision-making, which has clearly played a big part in re-energizing public transport network, and has offered plenty of opportunities to improve the public transportation experience with improved reliability and safety. For drivers, real-time traffic sensor data collection, analysis, visualization and optimization of dynamic transportation systems has reduced transportation time and emissions greatly.
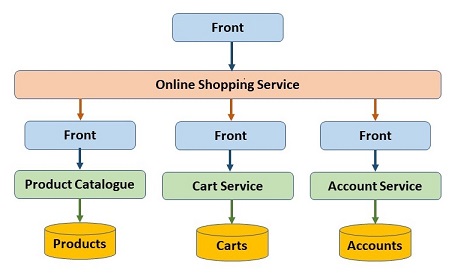
The customer-facing software development world is outgrowing stateful, object-oriented (OO) development. The bar for great, intuitive customer experience has been raised by ambient, conversation-driven user interfaces, like through Amazon Alexa. Functional programming allows enterprises to take better advantage of compute power to deliver those experiences at scale; better flexibility for delivering the right output; and a more efficient way of delivering customer value. FP also reduces regression defects in code, simplifies code creation and maintenance and allows for greater code reuse. Just as object-oriented programming (OOP) emerged as the solution to the limitations of procedural programming at the dawn of the internet boom in the mid-'90s, FP is emerging as the solution to the limitations of OOP today. The shift is already underway -- 53 percent of global developers reported that at least some teams in their companies are practicing functional programming and are planning to expand their usage.
Breaking Bitcoin With a Quantum Computer
Alex Beath, a Toronto-based physicist and pension fund analyst, is skeptical about Bitcoin but sees one useful purpose for the crypto-currency: It may detect when someone creates a working quantum computer. “The second someone creates a viable quantum computer, the NP-complete math problems at the heart of Bitcoin mining tech become instantly solvable,” Beath notes. “In other words, one answer to the question ‘what’s the first thing you’d do with a quantum computer?’ is ‘mine all of the remaining Bitcoin instantly.’ Until that happens, nobody has a quantum computer.” Beath’s off-the-cuff observation, which he made in response to a Fortune query about the security of bitcoin, is amusing. But it also underscores a serious problem: Namely, a new era of computing is fast-approaching and when it arrives, the system that gave rise to many crypto-currency fortunes will collapse.
AI Weekly: If we create artificial intelligence, will we know it?

When people talk about creating an artificial intelligence, the conversation is often focused on human or superhuman AI — systems that would equal or surpass us in intelligence. But what if we create an artificial intelligence that’s deserving of respect, but don’t recognize it as such? That’s a question I’ve had bouncing around in my head for the past several months. Over the course of human history, we’ve proven very poor as a species at successfully evaluating the intelligence of other beings, whether they’re human or non-human. Consider crows, who learn from their dead, recognize individuals, use tools, and even bring gifts to those they like — are they … intelligent? Furthermore, if we were to create an AI that produced those characteristics, does it require the same sort of considerations that a crow does, with regards to its treatment at the hands of humanity? We likely won’t have to reckon with a human-level AI for many years, but these questions could prove more pressing.
5 machine learning mistakes – and how to avoid them
Machine learning gives organizations the potential to make more accurate data-driven decisions and to solve problems that have stumped traditional analytical approaches. However, machine learning is not magic. It presents many of the same challenges as other analytics methods. In this article, we introduce some of the common machine learning mistakes that organizations must avoid to successfully incorporate this technique into their analytics strategy. The shortage of deep analytics talent continues to be a glaring challenge, and the need for employees who can manage and consume analytical content is even greater. Recruiting and keeping these in-demand technical experts has become a significant focus for many organizations. Data scientists, the most skilled analytics professionals, need a unique blend of computer science, mathematics and domain expertise. Experienced data scientists command high price tags and demand engaging projects.
Security fears have held companies back from adopting cloud services
Companies have been slow to move from running applications and storing data on their own private servers to doing them on public clouds such as Google Cloud and Amazon Web Services, a new study by McKinsey found. Only 40% of the companies studied had more than 10% of their workloads on public clouds. Concerns about cybersecurity were holding many companies back, although attitudes are changing, McKinsey, a consulting company, found in the study, which surveyed 90 companies across multiple industries. "Despite the benefits of public-cloud platforms, persistent concerns about cybersecurity for the public cloud have deterred companies from accelerating the migration of their workloads to the cloud," McKinsey said in its report. "Executives cited security as one of the top barriers to cloud migration, along with the complexity of managing change and the difficulty of making a compelling business case for cloud adoption."
How I fell for the blockchain gold rush
I found myself obsessed, constantly monitoring Twitter, waking in the night to check coin tracking apps. Pundits were hailing verge as a game-changer, the next bitcoin. Unbelievers pointed to previous missed deadlines and called it “vaporware”, a nonexistent con, the biggest scam in crypto history. In this unprecedented hype, there was clearly unprecedented money to be made. And more than one way to make it. Three things hold sway over these unregulated crypto markets: coin innovations, bitcoin whales manipulating prices with huge pump and dumps, and social media. The merest hint of FUD (fear, uncertainty and doubt) on a coin’s Twitter or Reddit threads can tank its price quickly, and as the final days of 2017 slipped by with Wraith Protocol still unreleased, the FUDers went to town on verge. A crypto tipster named Marquis Trill tweeted his 4.6 million followers on Christmas Day to “sell XVG!”, claiming he had proof from a Reddit whistleblower that the Wraith Protocol project was falling apart.
Top 10 Retail Banking Trends and Predictions for 2018
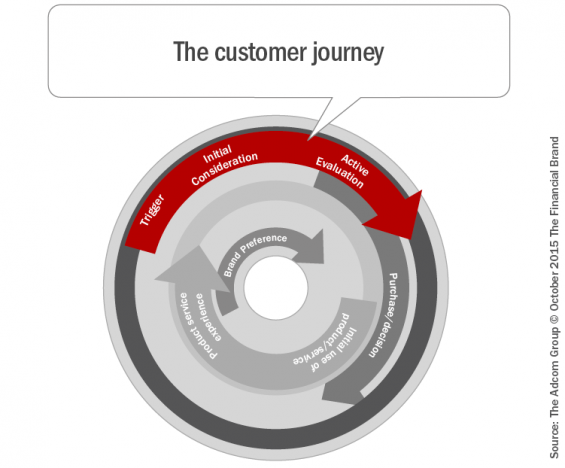
The fact that the list of trends identified by the financial services industry has remained relatively consistent could be a symptom of a greater problem. The banking industry is moving much too slow, and legacy firms are failing to differentiate themselves. According to Forrester, “In a market where one-third of all customers say ‘all banks are basically the same,’ it would make sense for executives and their teams to obsess over how to differentiate. Unfortunately, 2018 will look more like a digital arms race between warring incumbents than a year in which firms find new ways to specialize and create value for customers.” Regarding changes in emphasis for this year’s trends, removing friction from the customer journey increased in importance from last year, with 61% of organizations placing this trend in the top three, compared to 54% last year. The trend around the use and application of data also increased in importance from last year, with 57% of those surveyed placing this in the top 3 for 2018, compared to 53% in predictions for 2017.
Google Cloud Preemptible GPUs: Dirt cheap machine learning with a serious catch
The words “artificial intelligence” often conjure up a sense of fear and apprehension. Fear for the unknown possibilities of AI, fear for the AI-fueled dystopian images brought about by movies like The Terminator, and most practically, fear for the possibility that AI will someday take our jobs. This fear is neither new nor totally unfounded. As with any disruptive technological invention, faster, more efficient machines are bound to replace human workers. However, those who fear AI will take their jobs can rest a little easier knowing they will at least have the potential to find a new job. A new report by Gartner states that although AI will eliminate 1.8 million jobs, it will create 2.3 million jobs. Peter Sondergaard, head researcher at Gartner, predicted AI will augment workers’ abilities and could be a “net job creator” starting in 2020. I believe, like all other disruptive technologies of the past, AI will bring about many opportunities for new jobs.
Brazilian Government Plans to Process Petitions and Write Laws on Ethereum
The key to employing a Blockchain system in processing petitions and electoral votes is to encrypt votes onto the immutable Blockchain network as transactions, to ensure that the specific piece of data remains unalterable and invulnerable to manipulation. Essentially, processing petition signatures on the Ethereum network would require smart contracts, and the system would operate similarly as other decentralized applications that exist on the network. The electoral system of Brazil would act as a decentralized application of its own with an independent digital token, that is used to process every vote on the Blockchain. Henrique Costa, a Universidade de Brasilia law professor, told QZ that the lack of an immutable platform to collect signatures of votes had been a real issue for the government in the past. Within the Brazilian electoral system, any popular petition with the signatures of one percent of the country’s populations is required to be heard in Congress.
Quote for the day:
"Next generation leaders are those who would rather challenge what needs to change and pay the price than remain silent and die on the inside." -- Andy Stanley