Quote for the day:
"Always remember, your focus determines your reality." -- George Lucas
Escaping the transformation trap: Why we must build for continuous change, not reboots
 Each new wave of innovation demands faster decisions, deeper integration and
tighter alignment across silos. Yet, most organizations are still structured
for linear, project-based change. As complexity compounds, the gap between
what’s possible and what’s operationally sustainable continues to widen. The
result is a growing adaptation gap — the widening distance between the speed
of innovation and the enterprise’s capacity to absorb it. CIOs now sit at the
fault line of this imbalance, confronting not only relentless technological
disruption but also the limits of their organizations’ ability to evolve at
the same pace. ... Technical debt has been rapidly amassing in three areas:
accumulated, acquired, and emergent. The result destabilizes transformation
efforts. ... Most modernization programs change the surface, not the
supporting systems. New digital interfaces and analytics layers often sit atop
legacy data logic and brittle integration models. Without rearchitecting the
semantic and process foundations, the shared meaning behind data and
decisions, enterprises modernize their appearance without improving their
fitness. ... The new question is not, ‘How do we transform again?’ but ‘How do
we build so we never need to?’ That requires architectures capable of
sustaining and sharing meaning across every system and process, which
technologists refer to as semantic interoperability.
Each new wave of innovation demands faster decisions, deeper integration and
tighter alignment across silos. Yet, most organizations are still structured
for linear, project-based change. As complexity compounds, the gap between
what’s possible and what’s operationally sustainable continues to widen. The
result is a growing adaptation gap — the widening distance between the speed
of innovation and the enterprise’s capacity to absorb it. CIOs now sit at the
fault line of this imbalance, confronting not only relentless technological
disruption but also the limits of their organizations’ ability to evolve at
the same pace. ... Technical debt has been rapidly amassing in three areas:
accumulated, acquired, and emergent. The result destabilizes transformation
efforts. ... Most modernization programs change the surface, not the
supporting systems. New digital interfaces and analytics layers often sit atop
legacy data logic and brittle integration models. Without rearchitecting the
semantic and process foundations, the shared meaning behind data and
decisions, enterprises modernize their appearance without improving their
fitness. ... The new question is not, ‘How do we transform again?’ but ‘How do
we build so we never need to?’ That requires architectures capable of
sustaining and sharing meaning across every system and process, which
technologists refer to as semantic interoperability.
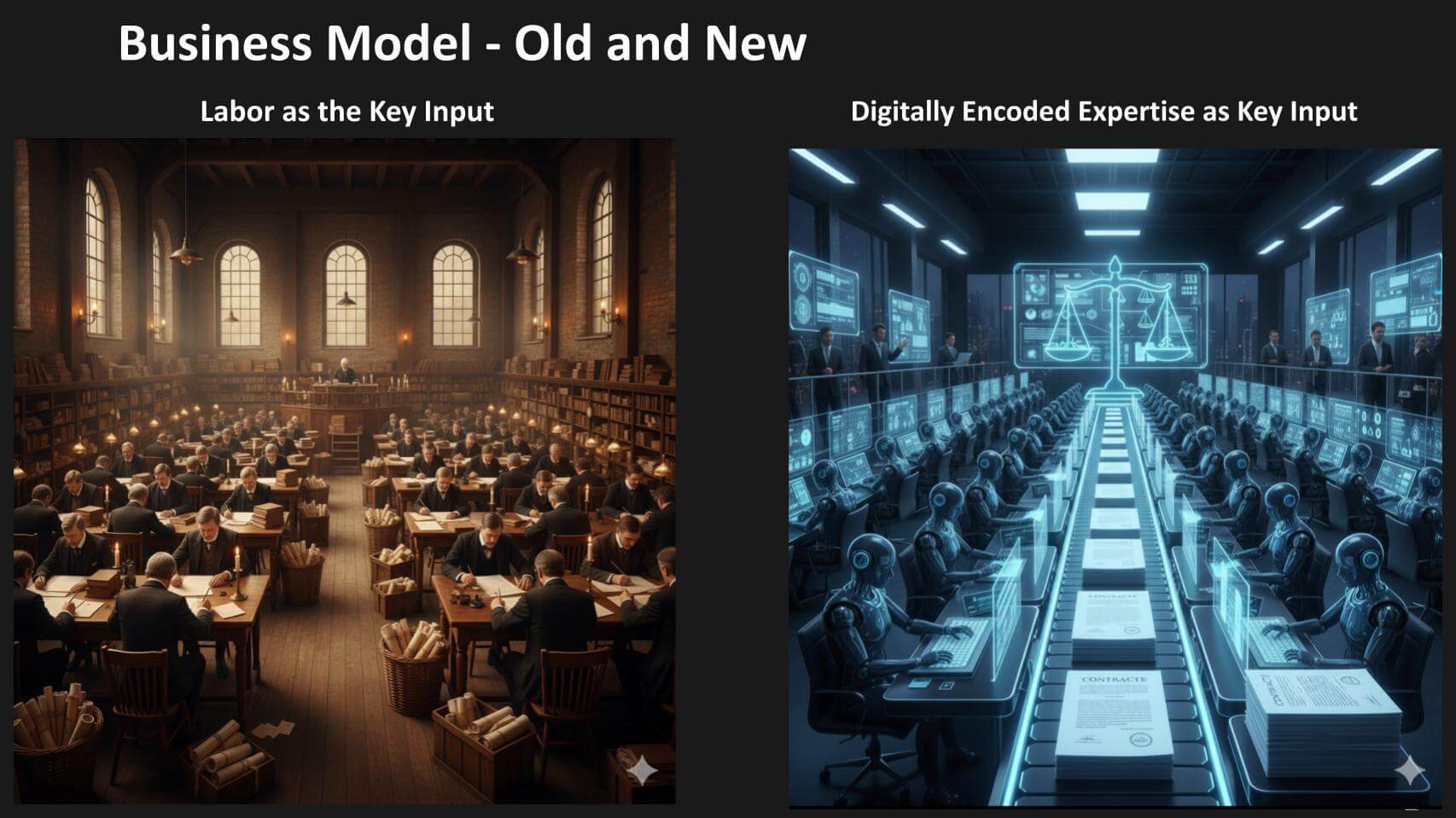
The state of AI in 2026 – part 1
 “The real race will be about purpose, measurable outcomes and return on
investment. AI is no longer simply a technical challenge, it has become a
business strategy,” said Zaccone. “However, this evolution comes with new risks.
As agentic systems gain autonomy, securing the underlying AI infrastructure
becomes critical. Standards are still emerging, but adopting strong security and
governance practices early dramatically increases the likelihood of success. At
the same time, AI is reshaping the risk landscape faster than regulation can
adapt, which means it’s raising pressing questions around data sovereignty,
compliance and access to AI-generated data across jurisdictions.” ... “Many
teams now face practical limits around data quality, compute efficiency and
responsible integration with existing systems. There is a clear gap between
those who just wrap APIs around foundation models and those who actually
optimise architectures and training pipelines. The next phase of AI is about
reliability, interpretability and building systems that engineers can trust and
improve over time,” Khan said. ... “To close the gap between the vision and
reality of agentic AI over the next 12 months, enterprise agentic automation
(EAA) will be essential. By blending dynamic AI with determinist guardrails and
human-in-the-loop checkpoints, EAA empowers enterprises to automate complex,
exception-heavy or cognitive work without losing control,” explained Freund.
“The real race will be about purpose, measurable outcomes and return on
investment. AI is no longer simply a technical challenge, it has become a
business strategy,” said Zaccone. “However, this evolution comes with new risks.
As agentic systems gain autonomy, securing the underlying AI infrastructure
becomes critical. Standards are still emerging, but adopting strong security and
governance practices early dramatically increases the likelihood of success. At
the same time, AI is reshaping the risk landscape faster than regulation can
adapt, which means it’s raising pressing questions around data sovereignty,
compliance and access to AI-generated data across jurisdictions.” ... “Many
teams now face practical limits around data quality, compute efficiency and
responsible integration with existing systems. There is a clear gap between
those who just wrap APIs around foundation models and those who actually
optimise architectures and training pipelines. The next phase of AI is about
reliability, interpretability and building systems that engineers can trust and
improve over time,” Khan said. ... “To close the gap between the vision and
reality of agentic AI over the next 12 months, enterprise agentic automation
(EAA) will be essential. By blending dynamic AI with determinist guardrails and
human-in-the-loop checkpoints, EAA empowers enterprises to automate complex,
exception-heavy or cognitive work without losing control,” explained Freund.
Cybersecurity isn’t underfunded — It’s undermanaged
 Of course, cybersecurity projects are often complex because they need to reach
across corporate silos and geographies to deliver effective protection to the
business. This is not natural in large firms, which are, almost by essence,
territorial and political. But beyond that, the profile of CISOs is also a key
dimension: Most are technologists by trade and background, and have spent the
last decade firefighting incidents, incapable of building or delivering any kind
of long-term narrative. They have not developed the type of management
experience, political finesse or personal gravitas that they would require to be
truly successful, now that the spotlight is firmly on them from the top of the
firm. Many genuinely think that chronic under-investment in cybersecurity is the
root cause of insufficient maturity levels, while it is in fact chronic
execution failure linked to endemic business short-termism that is at the heart
of the matter: All point to governance and cultural aspects that are the real
root causes of the long-term stagnation of cybersecurity maturity levels in
large firms. For the CISOs who have not integrated those cultural aspects and
are almost always left out of those decisions, it breeds frustration;
frustration breeds short tenures; short tenures aggravate the management and
leadership mismatch: You cannot deliver much of genuine transformative impact in
large firms on those timeframes.
Of course, cybersecurity projects are often complex because they need to reach
across corporate silos and geographies to deliver effective protection to the
business. This is not natural in large firms, which are, almost by essence,
territorial and political. But beyond that, the profile of CISOs is also a key
dimension: Most are technologists by trade and background, and have spent the
last decade firefighting incidents, incapable of building or delivering any kind
of long-term narrative. They have not developed the type of management
experience, political finesse or personal gravitas that they would require to be
truly successful, now that the spotlight is firmly on them from the top of the
firm. Many genuinely think that chronic under-investment in cybersecurity is the
root cause of insufficient maturity levels, while it is in fact chronic
execution failure linked to endemic business short-termism that is at the heart
of the matter: All point to governance and cultural aspects that are the real
root causes of the long-term stagnation of cybersecurity maturity levels in
large firms. For the CISOs who have not integrated those cultural aspects and
are almost always left out of those decisions, it breeds frustration;
frustration breeds short tenures; short tenures aggravate the management and
leadership mismatch: You cannot deliver much of genuine transformative impact in
large firms on those timeframes.Document databases – understanding your options
 There are two decisions to take around databases today—what you choose to run,
and how you choose to run it. The latter choice covers a range of different
deployment options, from implementing your own instance of a technology on your
own hardware and storage, through to picking a database as a service where all
the infrastructure is abstracted away and you only see an API. In between, you
can look at hosting your own instances in the cloud, where you manage the
software while the cloud service provider runs the infrastructure, or adopt a
managed service where you still decide on the design but everything else is done
for you. ... The first option is to look at alternative approaches to running
MongoDB itself. Alongside MongoDB-compatible APIs, you can choose to run
different versions of MongoDB or alternatives to meet your document database
needs. ... The second migration option is to use a service that is compatible
with MongoDB’s API. For some workloads, being compatible with the API will be
enough to move to another service with minimal to no impact. ... The third
option is to use an alternative document database. In the world of open source,
Apache CouchDB is another document database that works with JSON and can be used
for projects. It is particularly useful where applications might run on mobile
devices as well as cloud instances; mobile support is a feature that MongoDB has
deprecated.
There are two decisions to take around databases today—what you choose to run,
and how you choose to run it. The latter choice covers a range of different
deployment options, from implementing your own instance of a technology on your
own hardware and storage, through to picking a database as a service where all
the infrastructure is abstracted away and you only see an API. In between, you
can look at hosting your own instances in the cloud, where you manage the
software while the cloud service provider runs the infrastructure, or adopt a
managed service where you still decide on the design but everything else is done
for you. ... The first option is to look at alternative approaches to running
MongoDB itself. Alongside MongoDB-compatible APIs, you can choose to run
different versions of MongoDB or alternatives to meet your document database
needs. ... The second migration option is to use a service that is compatible
with MongoDB’s API. For some workloads, being compatible with the API will be
enough to move to another service with minimal to no impact. ... The third
option is to use an alternative document database. In the world of open source,
Apache CouchDB is another document database that works with JSON and can be used
for projects. It is particularly useful where applications might run on mobile
devices as well as cloud instances; mobile support is a feature that MongoDB has
deprecated.
Why AI Fatigue Is Sending Customers Back to Humans
 The pattern is familiar across industries: digital experiences that start
strong, then steadily degrade as companies prioritize cost-cutting over
satisfaction. In banking, this manifests in frustratingly specific ways:
chatbots that loop through unhelpful responses, automated fraud alerts that lock
accounts without a path to resolution, and phone trees that make reaching a
human nearly impossible. ... The path forward for community banks and credit
unions isn’t choosing between digital efficiency and human service or retreating
to nostalgia for branch-based banking. It’s investing strategically in both. ...
Geographic proximity enables genuine empathy that algorithms can’t replicate.
Rajesh Patil, CEO at Digital Agents Service Organization (CUSO), offers an
example: “When there’s a disaster in a community, an AI chatbot doesn’t know
what happened. But a local branch employee knows and can say, ‘I understand. Let
me help you.'” The most sophisticated community bank strategy uses technology to
identify opportunities while humans deliver the insight. ... After decades of
pursuing digital transformation, community banks and credit unions are
discovering their competitive advantage was human all along. But the path
forward isn’t nostalgia for branch-based banking, it’s strategic investment in
both digital infrastructure and human capacity.
The pattern is familiar across industries: digital experiences that start
strong, then steadily degrade as companies prioritize cost-cutting over
satisfaction. In banking, this manifests in frustratingly specific ways:
chatbots that loop through unhelpful responses, automated fraud alerts that lock
accounts without a path to resolution, and phone trees that make reaching a
human nearly impossible. ... The path forward for community banks and credit
unions isn’t choosing between digital efficiency and human service or retreating
to nostalgia for branch-based banking. It’s investing strategically in both. ...
Geographic proximity enables genuine empathy that algorithms can’t replicate.
Rajesh Patil, CEO at Digital Agents Service Organization (CUSO), offers an
example: “When there’s a disaster in a community, an AI chatbot doesn’t know
what happened. But a local branch employee knows and can say, ‘I understand. Let
me help you.'” The most sophisticated community bank strategy uses technology to
identify opportunities while humans deliver the insight. ... After decades of
pursuing digital transformation, community banks and credit unions are
discovering their competitive advantage was human all along. But the path
forward isn’t nostalgia for branch-based banking, it’s strategic investment in
both digital infrastructure and human capacity.
The Cloud Investment Paradox: Why More Spending Isn’t Delivering AI Results
There are three common gaps that stall AI progress, even after significant cloud spend. First is data architecture. Many organisations lift and shift legacy systems into the cloud without rethinking how data will flow across teams and tools. They end up with the same fragmentation problems, just in a new environment. Second is the skills gap. Research has found that 27% of organisations lack the internal expertise to harness AI’s potential. And it is not just data scientists. You need cloud architects who understand how to design environments specifically for AI workloads, not just generic compute. Third is data quality and accessibility. AI models cannot perform well without clean, consistent input. But too often, data governance is an afterthought. Only 1 in 5 organisations feel confident that their data is truly AI-ready. That is a foundational issue, not a fine-tuning one. ... Before investing in another AI pilot or data science hire, organisations should take a step back. Is the data ready? Are the pipelines in place? Do internal teams have what they need to turn compute into insight? This means prioritising data integration and governance before algorithms. It means investing in internal training and hiring with long-term capability in mind. And it means treating cloud and AI as part of the same strategy, not separate silos.Beyond the login: Why “identity-first” security is leaking data and why “context-first” is the fix
 The uncomfortable truth emerging from recent high-profile breaches is that
identity-first security—when operating in isolation—is leaking data. Threat
actors have evolved; they are no longer just trying to break down the door; they
are cloning the keys. The reliance on static authentication events has created a
dangerous blind spot. ... Standard facial recognition often looks for geometric
matches—distance between eyes, shape of the nose. Deepfakes can replicate this
perfectly, turning video verification into a vulnerability rather than a
safeguard. To counter this, modern security must implement advanced “Liveness
Detection”. It is no longer enough to match a face to a database; the system
must analyse micro-expressions and texture to ensure the face belongs to a live
human presence, not a digital puppet. Yet, even with these safeguards, betting
the entire security posture solely on verifying who the user is, remains a risky
strategy. ... To stop these leaks, security must move beyond the “Who”
(Identity) and interrogate the “Where,” “What,” and “How” (Context). This
requires a shift from static gates to Continuous Adaptive Trust. Context is not
a single data point; it is a composite score derived from real-time telemetry.
... For technology leaders, this convergence is not just a technical upgrade; it
is a strategic necessity for compliance. Frameworks like the Digital Personal
Data Protection (DPDP) Act require organisations to implement “reasonable
security safeguards”.
The uncomfortable truth emerging from recent high-profile breaches is that
identity-first security—when operating in isolation—is leaking data. Threat
actors have evolved; they are no longer just trying to break down the door; they
are cloning the keys. The reliance on static authentication events has created a
dangerous blind spot. ... Standard facial recognition often looks for geometric
matches—distance between eyes, shape of the nose. Deepfakes can replicate this
perfectly, turning video verification into a vulnerability rather than a
safeguard. To counter this, modern security must implement advanced “Liveness
Detection”. It is no longer enough to match a face to a database; the system
must analyse micro-expressions and texture to ensure the face belongs to a live
human presence, not a digital puppet. Yet, even with these safeguards, betting
the entire security posture solely on verifying who the user is, remains a risky
strategy. ... To stop these leaks, security must move beyond the “Who”
(Identity) and interrogate the “Where,” “What,” and “How” (Context). This
requires a shift from static gates to Continuous Adaptive Trust. Context is not
a single data point; it is a composite score derived from real-time telemetry.
... For technology leaders, this convergence is not just a technical upgrade; it
is a strategic necessity for compliance. Frameworks like the Digital Personal
Data Protection (DPDP) Act require organisations to implement “reasonable
security safeguards”.
Why Critical Infrastructure Needs Security-Forward Managed File Transfer Now
Today’s cyber attackers often use ordinary documents and files to breach organizations. Without strong security checks, it’s surprisingly easy for bad actors to cause major problems. Attacks exploit both common file formats and weaknesses in legacy operational technology (OT) environments. ... Modern managed file transfer (MFT) requires a layered security approach to effectively combat file-based threats and comply with best practices. This approach dictates that organizations must encrypt files at rest and in transit, employ strong hash checks, and use digital signing to validate the origin and integrity of files throughout their lifecycle. ... Many MFT tools incorporate multi-layered malware scanning. This works by scanning every file with multiple malware engines rather than relying on a single one, given that different engines detect different malware families and variants. Parallel multiscanning not only improves detection rates but also shortens the window for exploitation of zero‑day vulnerabilities and polymorphic malware. This helps to reduce the chance of false negatives before files enter sensitive networks. The scanning should be directly integrated into upload, download, and workflow steps so no file can move between zones without passing through a multi‑engine inspection pipeline. ... MFT workflows can automatically route files to a sandbox based on risk scores, file types, sender reputation, or country of origin. Then, files are only released upon passing behavioral checks.Fight AI Disinformation: A CISO Playbook for Working with Your C-Suite
 Unlike misinformation or malinformation, which may be inaccurate or misleading
but not necessarily harmful, disinformation is both false and designed
specifically to damage organizations. It can be episodic, targeting individuals
for immediate gain, such as tricking an employee into transferring funds via a
deepfaked call. It can also be industrial, operating at scale to undermine brand
reputation, manipulate stock prices, or probe organizational defenses over time.
The attack surfaces are broad: internally, adversaries exploit corporate meeting
solutions, email, and messaging platforms to bypass authentication and
impersonate trusted individuals. ... Without clear ownership and
cross-functional collaboration, efforts to counter disinformation are often
disjointed and ineffectual. In some cases, organizations leave disinformation as
an unmanaged risk, exposing themselves to episodic attacks on individuals and
industrial campaigns targeting reputation and financial stability. Another
common pitfall is failing to differentiate between types of information threats.
CISOs should focus their resources on disinformation where intent to harm and
lack of accuracy intersect, rather than attempting to police all forms of
misinformation or malinformation. ... CISOs must lead the way in communicating
the risks and fostering a culture of shared responsibility, engaging all
employees in detection, reporting, and response. This includes developing
internal tooling for monitoring and reporting, promoting transparency, and
ensuring ongoing education about evolving threats.
Unlike misinformation or malinformation, which may be inaccurate or misleading
but not necessarily harmful, disinformation is both false and designed
specifically to damage organizations. It can be episodic, targeting individuals
for immediate gain, such as tricking an employee into transferring funds via a
deepfaked call. It can also be industrial, operating at scale to undermine brand
reputation, manipulate stock prices, or probe organizational defenses over time.
The attack surfaces are broad: internally, adversaries exploit corporate meeting
solutions, email, and messaging platforms to bypass authentication and
impersonate trusted individuals. ... Without clear ownership and
cross-functional collaboration, efforts to counter disinformation are often
disjointed and ineffectual. In some cases, organizations leave disinformation as
an unmanaged risk, exposing themselves to episodic attacks on individuals and
industrial campaigns targeting reputation and financial stability. Another
common pitfall is failing to differentiate between types of information threats.
CISOs should focus their resources on disinformation where intent to harm and
lack of accuracy intersect, rather than attempting to police all forms of
misinformation or malinformation. ... CISOs must lead the way in communicating
the risks and fostering a culture of shared responsibility, engaging all
employees in detection, reporting, and response. This includes developing
internal tooling for monitoring and reporting, promoting transparency, and
ensuring ongoing education about evolving threats.

_(10).jpg&h=420&w=748&c=0&s=0)