Five ways the pandemic has changed compliance—perhaps permanently

There is a strong acknowledgment that compliance will be forced to rely
heavily on technology to ensure an adequate level of visibility to emerging
issues. We need to strategically leverage technology and efficient systems to
monitor risk. This is causing some speculation that a greater skills overlap
will be required of CCO and CISO roles. This, however, also raises privacy
concerns. Taylor believes the remote environment will lead to “exponential
growth” in employee surveillance and that compliance officers will need to
tread carefully given that this can undermine ethical culture: “Just because
the tools exist, doesn’t mean you have to use them,” she says. Compliance
veteran and advisor Keith Darcy predicts dynamic and continuous risk
assessment—one that considers “the rapidly deteriorating and changing business
conditions. ‘One-and-done’ assessments are completely inadequate.” Some
predict that investigation interviews conducted on video conference and remote
auditing will become the norm. Others are concerned that policies cannot be
monitored or enforced without being in the office together; that compliance
will be “out of sight, out of mind” to some degree. Communication must be a
top priority for compliance, as the reduction of informal contacts with
stakeholders and employees makes effectiveness more challenging.
In the Search of Code Quality
In general functional and statically typed languages were less error-prone
than dynamically typed, scripting, or procedural languages. Interestingly
defect types correlated stronger with language than the number of defects. In
general, the results were not surprising, confirming what the majority of the
community believed to be true. The study got popularity and was extensively
cited. There is one caveat, the results were statistical and interpreting
statistical results one must be careful. Statistical significance does not
always entail practical significance and, as the authors rightfully warn,
correlation is not causation. The results of the study do not imply (although
many readers have interpreted it in such a way) that if you change C to
Haskell you will have fewer bugs in the code. Anyway, the paper at least
provided data-backed arguments. But that’s not the end of the story. As
one of the cornerstones of the scientific method is replication, a team of
researchers tried to replicate the study from 2016. The result, after
correcting some methodological shortcomings found in the original paper, was
published in 2019 in the paper On the Impact of Programming Languages on Code
Quality A Reproduction Study.
3 unexpected predictions for cloud computing next year

With more than 90 percent of enterprises using multicloud, there is a need for
intercloud orchestration. The capability to bind resources together in a
larger process that spans public cloud providers is vital. Invoking
application and database APIs that span clouds in sequence can solve a
specific business problem; for example, inventory reorder points based on a
common process between two systems that exist in different
clouds. Emerging technology has attempted to fill this gap, such as cloud
management platforms and cloud service brokers. However, they have fallen
short. They only provide resource management between cloud brands, typically
not addressing the larger intercloud resource and process binding. This a gap
that innovative startups are moving to fill. Moreover, if the public cloud
providers want to truly protect their market share, they may want to address
this problem as well. Second: cloudops automation with prebuilt corrective
behaviors. Self-healing is a feature where a tool can take automated
corrective action to restore systems to operation. However, you have to build
these behaviors yourself, including automations, or wait as the tool learns
over time. We’ve all seen the growth of AIops, and the future is that
these behaviors will come prebuilt with pre-existing knowledge that can
operate distributed or centralized.
How Organizations Can Build Analytics Agility

Data and analytics leaders must frame investments in the current context and
prioritize data investments wisely by taking a complete view of what is
happening to the business across a number of functions. For example, customers
bank very differently in a time of crisis, and this requires banks to change
how they operate in order to accommodate them. The COVID-19 pandemic forced
banks to take another look at the multiple channels their customers traverse —
branches, mobile, online banking, ATMs — and how their comfort levels with
each shifted. How customers bank, and what journeys they engage in at what
times and in what sequence, are all highly relevant to helping them achieve
their financial goals. The rapid collection and analysis of data from across
channels, paired with key economic factors, provided context that allowed
banks to better serve customers in the moment. New and different sources of
information — be it transaction-level data, payment behaviors, or real-time
credit bureau information — can help ensure that customer credit is protected
and that fraudulent activity is kept at bay. Making the business case for data
investments suddenly makes sense as business leaders live through data gap
implications in real time.
Cisco targets WAN edge with new router family
The platform makes it possible to create a fully software-defined branch,
including connectivity, edge compute, and storage. Compute and switching
capabilities can be added via UCS-E Series blades and UADP-powered switch
modules. Application hosting is supported using containers running on the
Catalyst 8300’s multi-core, high-performance x86 processor, according JL
Valente, vice president of product management for Cisco’s Intent-Based
Networking Group in a blog about the new gear. Cisco said the Catalyst 8000V
Edge Software is a virtual routing platform that can run on any x86 platform,
or on Cisco’s Enterprise Network Compute System or appliance in a private or
public cloud. Depending on what features customers need. the new family
supports Cisco SD-WAN software, including Umbrella security software and Cisco
Cloud On-Ramp that lets customers tie distributed cloud applications from AWS,
Microsoft and Google back to a branch office or private data center. The
platforms produce telemetry that can be used in Cisco vAnalytics to provide
insights into device and fabric performance as well as spot anomalies in the
network and perform capacity planning.
2021 Will Be the Year of Catch-Up

With renewed focus on technology to bring about the changes needed, it’s
crucial that organizations recognize that infrastructure must be secure. Our
new office environment is anywhere we can find a connection to Wi-Fi, and that
opens many more doors to cyber-attacks. The rapid shift in business operations
significantly impacted the cyberthreat landscape – as companies fast-tracked
the migration of digital assets to the cloud, they also inadvertently
increased the attack surfaces from which hackers can try to gain access to
their data and applications. C-suite executives are moving quickly with
network plans to support exploding customer and supplier demand for
contactless interactions and the unplanned need to connect a remote workforce,
yet they are also aware that they are not fully prepared to adequately protect
their organizations from unknown threats. The situation is further compounded
by the cloud shared responsibility model, which says that cloud service
providers are responsible for the security of the cloud while customers are
responsible for securing the data they put into the cloud. Many organizations
rely on their third-party providers to certify security management services,
but the decentralized nature of this model can add complexity to how
applications and computing resources are secured.
BA breach penalty sets new GDPR precedents

The reduction in the fine also adds fuel to the ongoing class action lawsuit
against BA, said Long at Lewis Silkin. “Completely separate from the £20m fine
by the ICO, British Airways customers, and indeed any staff impacted, are
likely to be entitled to compensation for any loss they have suffered, any
distress and inconvenience they have suffered, and indeed possibly any loss of
control over their data they have suffered,” she said. “This might only be
£500 a pop but if only 20,000 people claim that is another potential £10m hit,
and if 100,000 then £50m. So whilst a win today, this is very much only round
one for BA.” Darren Wray, co-founder and CTO of privacy specialist Guardum,
said it was easy to imagine many of the breach’s actual victims would be put
out by the ICO’s decision. “Many will feel their data and their fight to
recover any financial losses resulting from the airline’s inability to keep
their data safe has been somewhat marginalised,” he said. “This can only
strengthen the case of the group pursuing a class action case against BA. The
GDPR and the UK DPA 2018 do after all allow for such action and if the
regulator isn’t seen as enforcing the rules strongly enough, it leaves those
whose data was lost few alternative options,” said Wray.
Is Artificial Intelligence Closer to Common Sense?
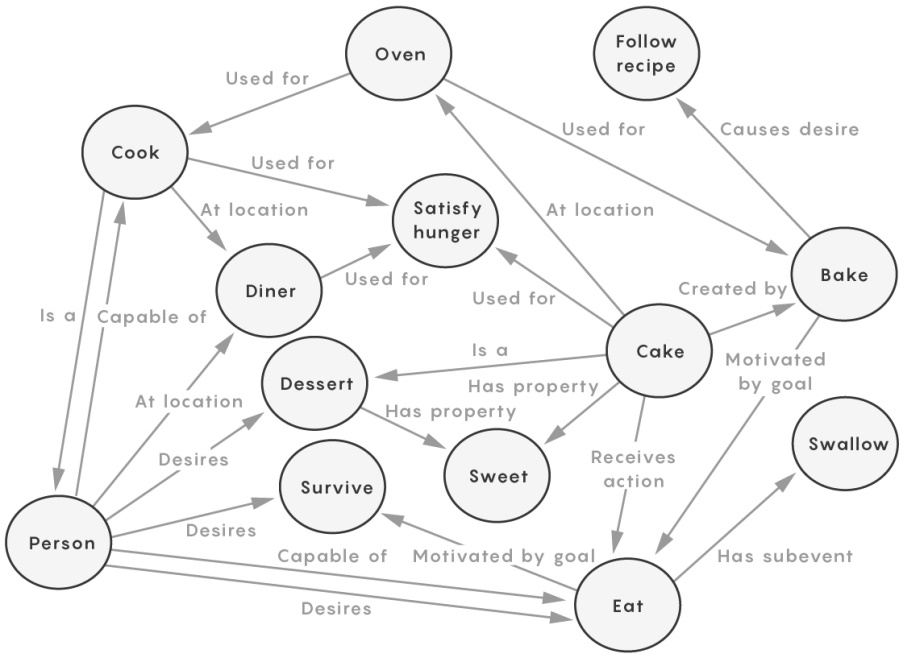
COMET relies on surface patterns in its training data rather than
understanding concepts. The key idea would be to supply surface patterns with
more information outside of language such as visual perceptions or embodied
sensations. First person representations, not language, would be the basis for
common sense. Ellie Pavlick is attempting to teach intelligent agents
common sense by having them interact with virtual reality. Pavlick notes that
common sense would still exist even without the ability to talk to other
people. Presumably, humans were using common sense to understand the world
before they were communicating. The idea is to teach intelligent agents to
interact with the world the way a child does. Instead of associating the idea
of eating with a textual description, an intelligent agent would be told, “We
are now going to eat,” and then it would see the associated actions such as,
gathering food from the refrigerator, preparing the meal, and then see its
consumption. Concept and action would be associated with each other. It could
then generate similar words when seeing similar actions. Nazneen Rajani
is investigating whether language models can reason using basic physics. For
example, if a ball is inside a jar, and the jar is tipped over, the ball will
fall out.
Russia planned cyber-attack on Tokyo Olympics, says UK

The UK is the first government to confirm details of the breadth of a
previously reported Russian attempt to disrupt the 2018 winter Olympics and
Paralympics in Pyeongchang, South Korea. It declared with what it described as
95% confidence that the disruption of both the winter and summer Olympics was
carried out remotely by the GRU unit 74455. In Pyeongchang, according to the
UK, the GRU’s cyber-unit attempted to disguise itself as North Korean and
Chinese hackers when it targeted the opening ceremony of the 2018 winter
Games, crashing the website so spectators could not print out tickets and
crashing the wifi in the stadium. The key targets also included broadcasters,
a ski resort, Olympic officials, service providers and sponsors of the games
in 2018, meaning the objects of the attacks were not just in Korea. The GRU
also deployed data-deletion malware against the winter Games IT systems and
targeted devices across South Korea using VPNFilter malware. The UK assumes
that the reconnaissance work for the summer Olympics – including spearphishing
to gather key account details, setting up fake websites and researching
individual account security – was designed to mount the same form of
disruption, making the Games a logistical nightmare for business, spectators
and athletes.
What intelligent workload balancing means for RPA

“To be truly effective, a bot must be able to work across a wide set of
parameters. Let’s say, for example, a rule involves a bot to complete work for
goods returned that are less than $100 in value, but during peak times when
returns are high, the rules may dynamically change the threshold to a higher
number. The bot should still be able to perform all the necessary steps for that
amount of approval without having to be reconfigured every time.” Gopal
Ramasubramanian, senior director, intelligent automation & technology at
Cognizant, added: “If there are 100,000 transactions that need to be performed
and instead of manually assigning transactions to different robots, the
intelligent workload balancing feature of the RPA platform will automatically
distribute the 100,000 transactions across different robots and ensure
transactions are completed as soon as possible. “If a service level agreement
(SLA) is tied to the completion of these transactions and the robots will not be
able to meet the SLA, intelligent workload balancing can also commission
additional robots on demand to distribute the workload and ensure any given task
is completed on time.”
Quote for the day:
"You can build a throne with bayonets, but you can_t sit on it for long." -- Boris Yeltsin
No comments:
Post a Comment