From AML to cybersecurity: The evolving challenges of bank compliance

For banks, it is a strategic necessity to protect their financial health and
reputational standing. The ability to effectively identify, assess, and
mitigate these threats is critical in safeguarding against operational
disruptions and legal repercussions. In this high-stakes environment, the
adoption of advanced solutions, particularly automation technology, is
becoming increasingly important. These tools are not merely operational aids
but strategic assets that streamline compliance processes and facilitate
adherence to the constantly evolving regulatory landscape. ... KYC compliance
focuses on verifying client identities and assessing their financial behavior,
while AML efforts are aimed at preventing money laundering through transaction
monitoring and analysis. These measures serve multiple roles in banking risk
and compliance, including reducing operational risk by preventing illegal
activities, mitigating legal and regulatory risks to avoid fines and
reputational damage, and safeguarding the financial system and society from
financial crimes.
How Fintech Is Disrupting Traditional Banks in 2024
Broadly speaking, incumbent banks have adapted well to the past decade’s wave
of fintech innovation, while startups have also managed to carve out
meaningful market share. Both were able to drive and adapt to changing
technology in the consumer banking space. Neobanks like Chime, SoFi and Varo
found success providing “new front doors” for consumers — between them, the
three companies’ apps were downloaded over 8 million times in 2023 alone.
Meanwhile, incumbents were able to quickly adopt neobanks’ more attractive
features like zero overdraft fees and continue to see substantial user base
growth. Mobile app download data suggests incumbents and disruptors are both
winning the race to be consumers’ primary financial relationship. On the
business banking side, startup neobanks like Mercury and Brex benefited from
early 2023 bank instability — receiving an estimated 29% of Silicon Valley
Bank (SVB) deposit outflows. ... By facilitating “hands-off” investment and
trading, the rise of roboadvisors opened the door to millions of consumers who
were otherwise unreachable to wealth and asset management companies.
Suptech on the Rise As Consumer Protection & Prudential Banking Prioritised

A cultural shift is taking place alongside the digital transformation, with
financial authorities creating new roles to drive suptech adoption, training
staff, and collaborating across the supervisory ecosystem. Surveyed financial
authorities report the biggest impact of their suptech implementation is the
speed with which they are able to respond to emerging risks and take
supervisory action (76 per cent). They also cite more efficient information
flows between consumers and supervisors (65 per cent). This enables better and
more transparent data analysis and timely response to potential issues.
Suptech initiatives also positively impact consumer outcomes (52 per cent).
Consequently, there has been improved protection and increased confidence in
financial markets. ... “The diverse perspectives from the global supervisory
community reflected in State of SupTech Report serve as the guiding force in
shaping our research, training programs, and digital tools. This year’s report
dives particularly deeply into the strategies and structures that dictate data
flows within financial authorities, which necessarily inform how suptech
solutions can be tailored and harmonised with existing supervisory processes.
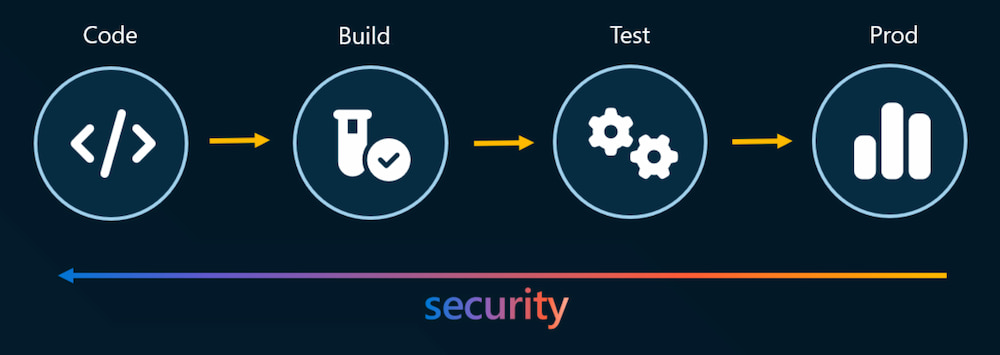
Cybersecurity in the Cloud: Integrating Continuous Security Testing Within DevSecOps
To successfully integrate Continuous Security Testing (CST), you must prepare
your cloud environment first. Use a manual tool like OWASP or an automated
security testing process to perform a thorough security audit and ensure your
cloud environments are well-protected to lay a robust groundwork for CST.
Before diving into integrating Continuous Security Testing (CST) within your
cloud infrastructure, it's crucial to lay a solid foundation by meticulously
preparing your cloud environment. This preparatory step involves conducting a
comprehensive security audit to identify vulnerabilities and ensure your cloud
architecture is fortified against threats. Leveraging tools such as the Open
Web Application Security Project (OWASP) for manual evaluations or employing
sophisticated automated security testing processes can significantly aid this
endeavor. Conduct a detailed inventory of all assets and resources within your
cloud architecture to assess your cloud environment's security posture. This
includes everything from data storage solutions and archives to virtual
machines and network configurations.
How Leaders Can Instill Hope In Their Teams

“When something is meaningful, it helps us to answer the question ‘Why am I
here?’ Amid the cost-of-living crisis and general world instability, it is
important that employees are able to foster meaning in their work, as it is
meaning that also brings hope to the day to day.” ... “The rising tide of
conflict, complaints and concerns that we are seeing in our workplaces is
contributing to high levels of anxiety and depression,” says David Liddle,
CEO and chief consultant at mediation provider The TCM Group and author of
Managing Conflict. “When people are spending their working days in toxic
cultures, where incivility, bullying, harassment and discrimination are
rife, it has a huge impact on both their physical and mental health.” ...
Servantie argues that to tackle employee disengagement, leaders should “lead
and inspire by example, showing that belief in change is possible, even in
difficult times”. She says: “They should also remain steadfast in purpose
and prioritize the growth of individuals over the growth of companies.
Finally, communication and transparency in leadership are fundamental.
How to create an efficient governance control program

Your journey toward robust governance control begins with establishing a
solid foundation. A house built on a shaky foundation will collapse over
time. The framework of foundational practices and addressing cultural shift
to security as a business concept, not a technology problem, is therefore
key. It is an incremental development of proven practices to then start
gauging your overall maturity and path to continuous improvement. You will
need to measure and plan for today and look ahead to where you want to be.
To get this view, you need to stand on solid ground, and that starts off
with your governance program. While navigating this step, it’s important for
you to understand your regulatory environment and build capabilities to
support the compliance of your internal program to that of your sector.
Bringing in stakeholder and business context will align practices to support
risk management and also compliance. The controls in place will have the
benefit of being informed of the requirements for control as well as a
capability that will enforce a by-product of compliance.
4 tabletop exercises every security team should run

Third-party risk management (TPRM) exercise participants should include
representatives from key downstream business partners — partners who supply
goods and services to the enterprise — as well as your cyber insurance
provider, law enforcement, and all key stakeholders, often including the
board of directors and senior management. While supply-chain attacks are
ubiquitous, often they are misidentified because the actual attack might be
initially identified as ransomware, an advanced persistent threat, or some
other cyber threat. Often it requires the forensics team post-breach
investigation to identify that the attack came through a trusted third
party. ... Insider threats come in two primary types: malicious insiders who
deliberately compromise corporate assets for personal, financial, political
or some other gain, and those who create a security vulnerability either
accidentally or simply due to lack of knowledge but without malice. In the
former case, a deliberate crime against the company is committed. The latter
case might involve either a user error or perhaps a user taking an action
that seems reasonable to them to perform their jobs but could create a
vulnerability.
Digital Twins Are the Next Wave of Innovation, and Australia Needs to Move Quickly
In fact, in many ways, the journey of the digital twin seems to be parallel
to the story of both digital transformation and AI before it — a lack of
understanding of what digital twins are leads to excitement and investment,
but without the right understanding, the risk of failure is higher. Gavin
Cotterill, founder and managing director of Australian digital twin
consultancy GC3 Digital, said in an interview with IoT Hub: “A lot of people
think digital twin is just focused on a flashy 3D model, but effectively it
is a master data management strategy.” “You need good quality data to
support that decision making and the quality of our data, generally, is
pretty poor. We have a lot of data, but we don’t know what to do with it,”
Cotterill said. “Data governance, data strategy is the unsexy part of
digital twin — it’s the engine room, it’s the fuel.” This means IT leaders
face competing challenges with regard to digital twins. On the one hand, the
appetite is there, particularly among those executives and boards to be
aware of the bleeding edge of technology. On the other hand, Australian
organisations, as a whole, are not ready to tackle the digital twin
opportunity.
Longer coherence: How the quantum computing industry is maturing

On-premise quantum computers are currently rarities largely reserved for
national computing labs and academic institutions. Most quantum processing
unit (QPU) providers offer access to their systems via their own web portals
and through public cloud providers. But today’s systems are rarely expected
(or contracted) to run with the five-9s resiliency and redundancy we might
expect from tried and tested silicon hardware. “Right now, quantum systems
are more like supercomputers and they're managed with a queue; they're
probably not online 24 hours, users enter jobs into a queue and get answers
back as the queue executes,” says Atom’s Hays. “We are approaching how we
get closer to 24/7 and how we build in redundancy and failover so that if
one system has come offline for maintenance, there's another one available
at all times. How do we build a system architecturally and engineering-wise,
where we can do hot swaps or upgrades or changes with minimal downtime as
possible?” Other providers are going through similar teething phases of how
to make their systems – which are currently sensitive, temperamental, and
complicated – enterprise-ready for the data centers of the world.
Why Blockchain Payments Are Misunderstood
:format(webp)/cloudfront-us-east-1.images.arcpublishing.com/coindesk/7KX4QWBYHJDW7LLOH53VFK4EGI.jpg)
Comparing a highly regulated system to one that sits in a gray area can be
misleading. Many crypto-based remittance applications do little or no
know-your-customer and anti-money laundering checks, which are costly and
difficult to run. This is a cost advantage that is unlikely to last. Low
levels of competition are another big driver in high payment costs. This is
true both for business-to-business and consumer-to-consumer payments. ... On
the business side, blockchains can drive costs down and build sustainable
advantage through differentiated technology. While it is true that main-net
transaction costs in Ethereum are higher, the addition of smart contract
functionality changes the equation entirely. Enterprises issue payments to
each other usually as part of a complex agreement. This usually means not
only verifying receipt of goods or services, but also compliance with the
agreed upon terms. ... Right now, the kind of fully digital end-to-end
systems that smart contracts enable are the province of the world’s biggest
companies. With scale and deep pockets, big companies have built integrated
systems without blockchains.
Quote for the day:
"If you don't understand that you work for your mislabeled 'subordinates,'
then you know nothing of leadership. You know only tyranny." --
Dee Hock