How to build a winning analytics team

Analytics teams thrive in dynamic environments that reward curiosity, encourage
innovation, and set high expectations. Building and reinforcing this type of
culture can help put organizations on a path to earning impressive returns from
analytics investments. An active analytics culture thrives when CXOs reward
curiosity over perfection. Encourage analysts to challenge convention and ask
questions as a method to improve quality and reduce risks. This thinking goes
hand in hand with a test-and-learn mentality, where pushing boundaries through
proactive experimentation helps identify what works, and optimize accordingly.
It’s also important to create a culture where failure and success are celebrated
equally. Giving airtime to what went wrong allows the team to more effectively
learn from their mistakes and see that perfection is an unhealthy pipe dream.
This encourages an environment that holds analysts accountable for delivering
quality processes and results, further helping to mitigate risk and improve
marketing programs.
How SSE Renewables uses Azure Digital Twins for more than machines

This approach will allow SSE to experiment with reducing risks to migrating
birds. For example, they can determine an optimum blade speed that will allow
flocks to pass safely while still generating power. By understanding the
environment around the turbines, it will be possible to control them more
effectively and with significantly less environmental impact. Simon Turner,
chief technology officer for data and AI at Avanade, described this approach as
“an autonomic business.” Here, data and AI work together to deliver a system
that is effectively self-operating, one he described as using AI to “look after
certain things that you understood that could guide the system to make decisions
on your behalf.” Key to this approach is extending the idea of a digital twin
with machine learning and large-scale data. ... As Turner notes, this approach
can be extended to more than wind farms, using it to model any complex system
where adding new elements could have a significant effect, such as understanding
how water catchment areas work or how hydroelectric systems can be tuned to let
salmon pass unharmed on their way to traditional breeding grounds, while still
generating power.
McKinsey report: Two AI trends top 2022 outlook

Roger Roberts, partner at McKinsey and one of the report’s coauthors, said of
applied AI, which is defined “quite broadly” in the report, “We see things
moving from advanced analytics towards… putting machine learning to work on
large-scale datasets in service of solving a persistent problem in a novel
way,” he said. That move is reflected in an explosion of publication around
AI, not just because AI scientists are publishing more, but because people in
a range of domains are using AI in their research and pushing the application
of AI forward, he explained. ... According to the McKinsey report,
industrializing machine learning (ML) “involves creating an interoperable
stack of technical tools for automating ML and scaling up its use so that
organizations can realize its full potential.” The report noted that McKinsey
expects industrializing ML to spread as more companies seek to use AI for a
growing number of applications. “It does encompass MLops, but it extends more
fully to include the way to think of the technology stack that supports
scaling, which can get down to innovations at the microprocessor level,” said
Roberts.
CISA: Prepare now for quantum computers, not when hackers use them
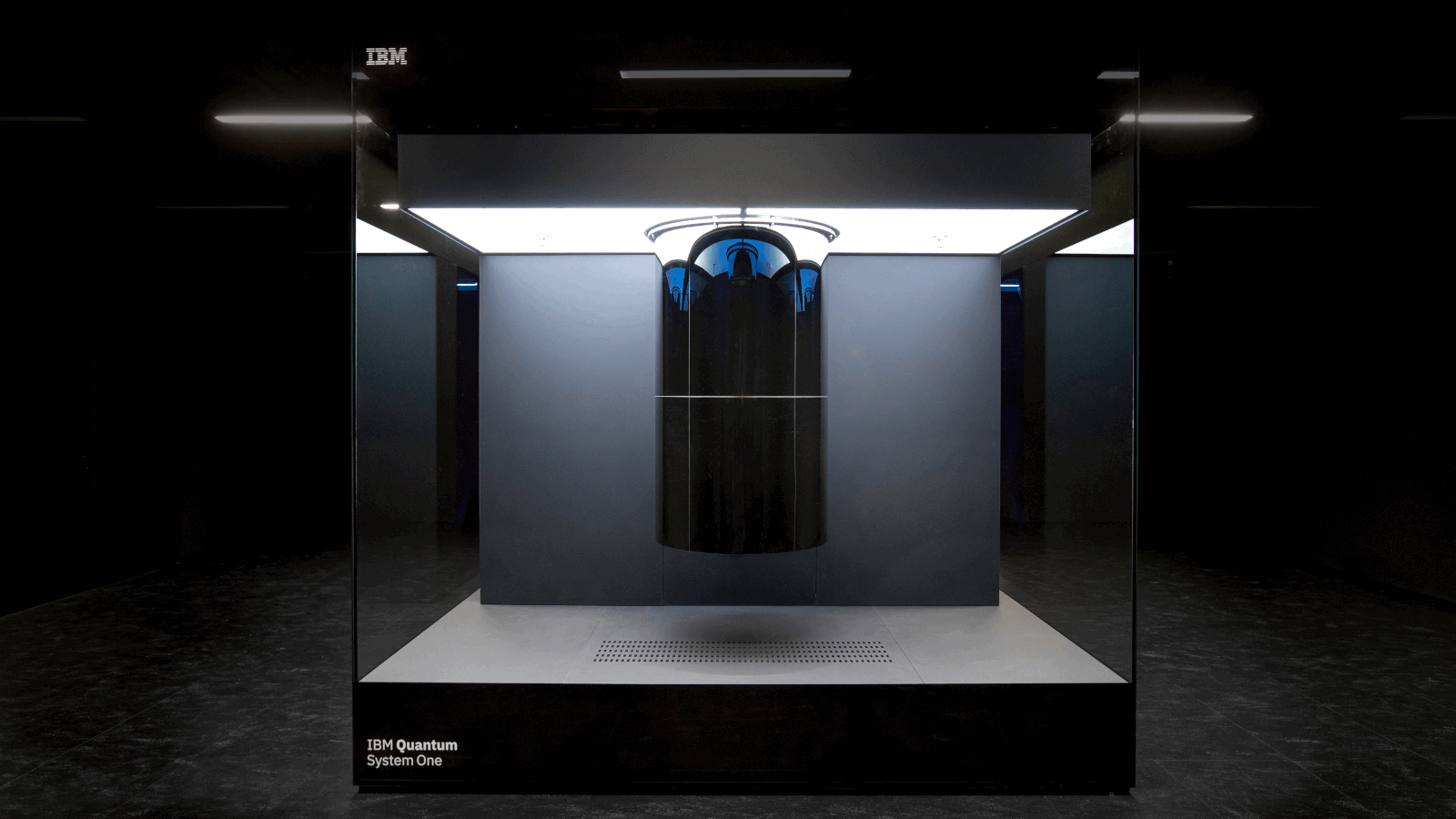
The main negative implication of this quantum computing concerns the
cryptography of secrets, a fundamental element of information security.
Cryptographic schemes that are today considered secure will be cracked in mere
seconds by quantum computers, leaving persons, companies, and entire countries
powerless against the computing supremacy of their adversaries. “When quantum
computers reach higher levels of computing power and speed, they will be
capable of breaking public key cryptography, threatening the security of
business transactions, secure communications, digital signatures, and customer
information,” explains CISA. This could threaten data in transit relating to
top-secret communications, banking operations, military operations, government
meetings, critical industrial processes, and more. Yesterday, China's Baidu
introduced “Qian Shi,” an industry-level quantum supercomputer capable of
achieving stable performance at 10 quantum bits of power.
How Are Business Intelligence And Data Management Related?

Business intelligence (BI) describes the procedures and tools that assist in
getting helpful information and intelligence that can be used from data. A
company’s data is accessed by business intelligence tools, which then display
analytics and insights as reports, dashboards, graphs, summaries, and charts.
Business intelligence has advanced significantly from its theoretical
inception in the 1950s, and you must realize that it is not just a tool for
big businesses. Most BI providers are tailoring their software to users’ needs
because they recognize that our current era is considerably more oriented
toward small structures like start-ups. SaaS, or software-as-a-service,
vendors are incredibly guilty of this. Another issue is that it’s a more
straightforward tool than it once was. It is still a professional tool;
managing data is not simple, even with the most powerful technology.
Nevertheless, BI has developed into something more accessible than local
software, which used to require installation on every computer in the
organization and may represent a sizable expenditure with the emergence of the
Cloud and SaaS in the early 21st century.
Oxford scientist says greedy physicists have overhyped quantum computing

It’s unclear why Dr. Gourianov would leave big tech out of the argument
entirely. There are dozens upon dozens of papers from Google and IBM alone
demonstrating breakthrough after breakthrough in the field. Gourianov’s
primary argument against quantum computing appears, inexplicably, to be that
they won’t be very useful for cracking quantum-resistant encryption. With
respect, that’s like saying we shouldn’t develop surgical scalpels because
they’re practically useless against chain mail armor. Per Gourianov’s article:
Shor’s algorithm has been a godsend to the quantum industry, leading to untold
amounts of funding from government security agencies all over the world.
However, the commonly forgotten caveat here is that there are many alternative
cryptographic schemes that are not vulnerable to quantum computers. It would
be far from impossible to simply replace these vulnerable schemes with
so-called “quantum-secure” ones. This appears to suggest that Gourianov
believes at least some physicists have pulled a bait-and-switch on governments
and investors by convincing everyone that we need quantum computers for
security.
Computer vision is primed for business value

In healthcare, computer vision is used extensively in diagnostics, such as in
AI-powered image and video interpretation. It is also used to monitor patients
for safety, and to improve healthcare operations, says Gartner analyst Tuong
Nguyen. “The potential for computer vision is enormous,” he says. “It’s
basically helping machines make sense of the world. The applications are
infinite — really, anything you need to see. The entire world.” According to
the fourth annual Optum survey on AI in healthcare, released at the end of
2021, 98% of healthcare organizations either already have an AI strategy or
are planning to implement one, and 99% of healthcare leaders believe AI can be
trusted for use in health care. Medical image interpretation was one of the
top three areas cited by survey respondents where AI can be used to improve
patient outcomes. The other two areas, virtual patient care and medical
diagnosis, are also ripe for computer vision. Take, for example, idiopathic
pulmonary fibrosis, a deadly lung disease that affects hundreds of thousands
of people worldwide.
AI Therapy: Digital Solution to Address Mental Health Issues
AI for health has been a long-discussed topic specifically on therapy by
bringing digital solutions to mental health issues. Some applications have
already been, such as Genie in a Headset which manages human emotional
behavior in work environments. But bringing AI into therapy means building an
AI that feels and is keen to improve mental health issues. The fundamental
objective of AI therapy is to assist patients in fighting mental illnesses.
Ideally, this technology would be able to distinguish each patients needs and
personalize their mental health programs through an efficient data collection
process. ... Psychological therapy is a tough job that requires extracting
confidential information from patients they hesitate to share. Like any other
medical issue, it is essential to diagnose the problem before curing it. It
requires exquisite skills to make someone comfortable. An AI therapist can
access your cellphone, laptop, personal data, emails, all-day movement, and
routine, making it more efficient in understanding you and your problems.
Knowing problems in depth gives an AI-therapist advantage over the usual
therapist.
What is the Microsoft Intelligent Data Platform?

The pieces that make up the Microsoft Intelligent Data Platform are services
you may already be using because it includes all of Microsoft’s key data
services, such as SQL Server 2022, Azure SQL, Cosmos DB, Azure Synapse,
Microsoft Purview and more. But you’re probably not using them together as
well as you could; the Intelligent Data Platform is here to make that easier.
“These are the best-in-class services across what we consider the three core
pillars of a data platform,” Mansour explained. According to Mansour, the
Microsoft Intelligent Data Platform offers services for databases and
operational data store, analytics, and data governance, providing authorized
users with insight that will allow them to properly understand, manage and
govern their business’s data. “Historically, customers have been thinking
about each of those areas independent from one another, and what the
Intelligent Data Platform does is bring all these pieces together,” said
Mansour. Integrating databases, analytics and governance isn’t new either, but
the point of presenting this as a platform is the emphasis on simplifying the
experience of working with it.
Threatening clouds: How can enterprises protect their public cloud data?

Public clouds don’t inherently impose security threats, said Gartner VP
analyst Patrick Hevesi — in fact, hyperscale cloud providers usually have more
security layers, people and processes in place than most organizations can
afford in their own data centers. However, the biggest red flag for
organizations when selecting a public cloud provider is the lack of visibility
into their security measures, he said. Some of the biggest issues in recent
memory: Misconfigurations of cloud storage buckets, said Hevesi. This has
opened files up for data exfiltration. Some cloud providers have also had
outages due to misconfigurations of identity platforms. This has affected
their cloud services from starting up properly, which in turn affected
tenants. Smaller cloud providers, meanwhile, have been taken offline due to
distributed denial-of-service (DDoS) attacks. This is when perpetrators make a
machine or network resource unavailable to intended users by disrupting
services — either short-term or long-term — of a host connected to a network.
Quote for the day:
“Real integrity is doing the right thing, knowing that nobody’s going to
know whether you did it or not.” -- Oprah Winfrey