Does Cloud Computing Help or Harm the Environment?
:max_bytes(150000):strip_icc():format(webp)/GettyImages-1247665468-7fdf4af32a4f4df3a0d885e71b77a601.jpg)
Fortunately, getting data centers to rely on clean, renewable energy sources
and use that energy more efficiently are far easier tasks than reducing the
carbon footprint of the billions of digital storage devices that they've
replaced. Here is where economic and environmental interests may overlap. Data
center companies have every incentive to maximize the efficiency of their
resources and reduce their cost. For that reason alone, the world's biggest data
center companies—Amazon, Microsoft, and Google—have all begun implementing plans
for their data centers to run on 100% carbon-free electricity. Amazon claims to
be the world's largest renewable energy purchaser, consistent with its goals of
powering its company with 100% renewables by 2025 and to become carbon net-zero
by 2040. Microsoft has pledged to be carbon negative by 2030 and to remove from
the atmosphere all the carbon the company has ever emitted since it was founded
in 1975. To achieve this, it plans on having all of its data centers running on
100 renewable energy by 2025. And Google had already reached its 100% renewable
energy target in 2018, though it did so in part by purchasing offsets to match
those parts of its operations that still relied on fossil fuel electricity.
5 Keys to Creating a Zero-Trust Security Foundation

Recent high-profile attacks have disrupted global commerce across the world,
bringing home the critical importance of maintaining a robust IT security
program. The recent ransomware attacks on the Colonial Pipeline, the largest
petroleum pipeline in the US, and meat supplier JBS, highlight the cascading,
society-disrupting havoc these types of attacks can create. Those concerns
increasingly extend to IoT devices, as evidenced by the recent hack of
cloud-based security services firm Verkada, where bad actors gained access to
150,000 of the company’s cameras, including inside factories, hospitals,
prisons, schools, and even police stations. Vulnerabilities come in many forms
and we have known for a long time that the onslaught of IoT devices onto
corporate networks is largely unprotected. It’s little wonder then that when the
Ponemon Institute surveyed 4,000 security professionals and asked why breaches
still happen, the top answer was the increasing attack surface. ... As a
networking vendor, connecting people and things is part of Aruba’s core
mission.
4 ways AI can help us enter a new age of cybersecurity

Combine conventional threat intelligence (a list of all known cyberthreats to
date) and use machine learning to understand risks. This should result in a
better, more efficient system of threat detection and prevention. This can also
help to identify any loophole or threat present in the data. In fact, machine
learning can also be used to spot any abnormality or potential vulnerability in
the midst of “normal” activity and warn users of a threat before it could
compromise essential data. With the right systems in place, your hackers won't
even realize that you know of their presence, so you can take immediate measures
to ensure the safety of your digital infrastructure. ... In recent years,
cryptocurrencies like Bitcoin and Ethereum have been rising in popularity. These
cryptocurrencies are built upon blockchain, an innovative technical solution to
store a secure, decentralized record of transactions. Blockchain can be used to
enable medical records and help in security management by identifying criminal
identity loopholes in the system. With blockchain technology, verification
keys wouldn't be required anymore. If someone tries to hack the data, the system
analyzes the whole mass of data chains.
Moving From Digital Banking To Embedded Experiences

First and most importantly, banks and credit unions must focus on placing the
consumer at the center of the organization, with product silos eliminated in
favor of teams aligned around the customer journey. According to the research,
64% of the banking sector’s digital masters have “created personae and journey
maps to identify and serve customers better.” Beyond that, it will be imperative
to create an agility and flexibility in delivery similar to what exists in
fintech and bigtech firms. This will most likely require changes in the
composition of boards, top leadership and departmental management who can see
banking from a new perspective. New operating models will also be required that
will include the collaboration with third-party providers. There also needs to
be support of open banking APIs that will enable the offering of new products
both within and outside financial services. Bottom line, the infrastructure of
banking as well as the perspective of banking’s role in the consumer’s life must
change. According to Capgemini, 64% of banks are actively working with a wide
ecosystem of partners – such as startups, incubators, technology firms, and even
competitors – to co-develop solutions.
Cybersecurity: Five key reminders for compliance teams

Cybersecurity breaches are not always the work of nefarious actors orchestrating
a sophisticated hack. Damaging data breaches may be as likely to result from
unintentional human error. Even seemingly benign behaviors –– using public
Wi-Fi, neglecting to put passwords on computers and mobile devices, and clicking
on bad links –– can be all it takes to give cybercriminals the access they need.
It does little good to build a digital fortress if there aren’t adequate
controls over who gains access, and under what circumstances. ... First,
establishing clear SoD helps avoid conflicts that could lead to fraud or other
abuse. For large organizations with multiple lines of business, this is
particularly important. Investment professionals on a firm’s buy-side, for
example, should not have access to the exact same data as those on the
sell-side. SoD may also help prevent control failures that can occur when too
many people have access to data for which they aren’t necessarily accountable
for. By segregating duties (and data access), compliance teams are better
positioned to spot weaknesses, while also ensuring that teams and individuals
understand exactly what data should be in their purview and what may be
off-limits.
The four Fs of employee experience
Ask yourself what it would take for employee experience to be a delight — for
example, through gamified training modules or KPIs. We work with a leading
technology firm that asked itself this very question and developed its tools for
surveying employees accordingly, designing them to be simple and intuitive,
satisfying, and not frustrating. The firm used layman’s terms and an appealing
tone of voice in written content such as instructions, explanations, and
requests. It avoided jargon. And it invested in interesting, stimulating visual
interactions rather than ones that were bland and text-heavy — the new
experience was less like a spreadsheet assignment to be endured and more of an
opportunity to engage. ... Don’t neglect the foundations. Ultimately, employees
have a right to expect that “it just works,” whether “it” is their human
resources self-service portal, their expense management system, or their system
interoperability. It’s also critical that user experience be accessible to all,
including employees with any type of disability.
Amex bets on AI and NLP for customer service

We started this journey [of leveraging AI] long before we applied machine
learning to some other more mature use cases, including our fraud models and
some credit risk models. And in the past couple years, especially in the past
five years or so, we started to see with certainty that deep neural network
models started to outperform almost every other machine learning model when it
comes to high dimensional data and highly unstructured data. We not only deal
with some of the traditional fields, like customer transactions, but also there
are tax consequences and volume history data. Neural network models can
effectively deal with all of that. ... First, I think it’s really about
recognizing patterns. And if you look at certain use cases where you have
customer behavior that’s being repeated and you can expedite that behavior, then
that tends to be a real sweet spot for machine learning capabilities. The other
thing I would add is we take the decision to apply machine learning techniques
quite seriously. We have an entire AI governance board that cross-checks all the
models that we build for bias and privacy concerns. So even taking the approach
of AI, we have to justify to a number of internal teams why it makes sense.
‘Debt’ as a Guide on the Agile Journey: Technical Debt
If network infrastructure is not your specialty, you might question how much
requirements for connectivity could really change over 10 years? Does the
Network Team really need to develop a completely new solution and live the
DevOps dream? The answer to that is a resounding yes! Today’s (not to mention
tomorrow’s) requirements for security features and performance are significantly
different from 10 years ago; the network infrastructure is key in the cyber
security area of protecting vital business processes and applications by
controlling data traffic, and the network must support the vastly increasing
amount of data traffic that is the result of new streaming and IoT services, for
instance. The Network Team was not able to deliver to these expectations with
the legacy technology that we were fighting to operate and maintain, and thus,
the business was impacted. Internally, the Network Team themselves were also
impacted. They felt the heat from several CXOs who were frustrated that they
couldn't satisfactorily support top priorities such as the cyber security
agenda.
Deep reinforcement learning will transform manufacturing as we know it

For many large systems, the only possible way to find the best action path is
with simulation. In those situations, you must create a digital model of the
physical system you want to understand in order to generate the data
reinforcement learning needs. These models are called, alternately, digital
twins, simulations and reinforcement-learning environments. They all essentially
mean the same thing in manufacturing and supply chain applications. Recreating
any physical system requires domain experts who understand how the system works.
This can be a problem for systems as small as a single fulfillment center for
the simple reason that the people who built those systems may have left or died,
and their successors have learned how to operate but not reconstruct them. Many
simulation software tools offer low-code interfaces that enable domain experts
to create digital models of those physical systems. This is important, because
domain expertise and software engineering skills often cannot be found in the
same person.
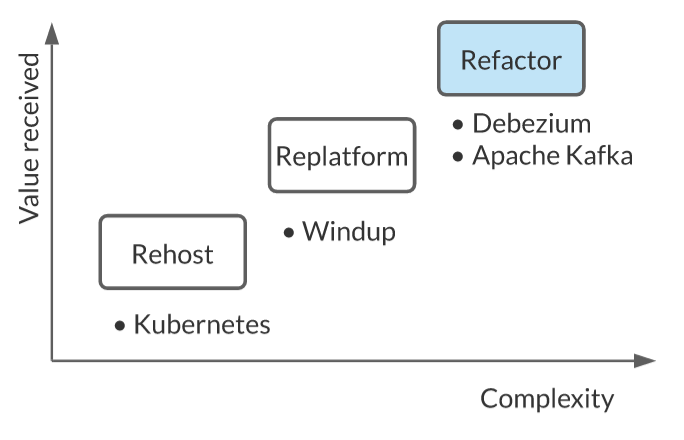
Multicluster Management with Kubernetes and Istio
Do you have multiple Kubernetes clusters and a service mesh? Do your virtual
machines and services in a Kubernetes cluster need to interact? This article
will take you through the process and considerations of building a hybrid
cloud using Kubernetes and an Istio Service Mesh. Together, Kubernetes and
Istio can be used to bring hybrid workloads into a mesh and achieve
interoperability for multicluster. But another layer of infrastructure — a
management plane — is helpful for managing multicluster or multimesh
deployments. ... Using Kubernetes enables rapid deployment of a distributed
environment that enables cloud interoperability and unifies the control plane
on the cloud. It also provides resource objects, such as Service, Ingress and
Gateway, to handle application traffic. The Kubernetes API Server communicates
with the kube-proxy component on each node in the cluster, creates iptables
rules for the node, and forwards requests to other pods. Assuming that a
client now wants to access a service in Kubernetes, the request is first sent
to the Ingress/Gateway, then forwarded to the backend service
Quote for the day:
"A good leader can't get too far ahead
of his followers." -- Franklin D. Roosevelt























:format(webp)/cdn.vox-cdn.com/uploads/chorus_image/image/69438999/VRG_4614_7_NIST.0.jpg)