Women in Fintech: How Open Banking Can Help Address Data Bias

A disturbing recent example is the story of Jamie Heinemeier Hansson, who was
granted permission to borrow 20 times less on her Apple Card than her husband
David was. This was despite her having a better credit score, as well as the
couple filing a joint tax return and having an equal share in their property.
The Apple Card incident highlighted that computers are not impartial.
Artificial intelligence may well be able to digest vast amounts of information
and identify patterns far beyond the capability of humans, but the historical
data from which such systems “learn” in order to draw conclusions can be
biased, even if it is unintentional. So a system can make a discriminatory
decision about a woman’s credit rating due to inherent bias in its training –
for example, as women were less likely to have been granted credit, the
algorithm continues that pattern – despite having not specifically asked her
gender. However, many believe that while technology can perpetuate these
biases, it could also be used to address them, particularly in the open
banking era. “I genuinely believe technology can level the playing field
fundamentally,” says Sam Seaton, CEO of Moneyhub.
Simplify agile, devops, and ITSM with Jira automations
Jira automations work like other IFTTT algorithms, except they have access to
all the underlying data and workflows within Jira Software. A Jira automation
trigger can be one of several types, including Jira issue types, sprints, and
versions. You can design automations for when team members add or modify Jira
issues, when scrum masters start or complete sprints, or when team leads
create, update, or release versions. These triggers are highly useful for
scrum masters, product owners, and technical leads who want to simplify the
work needed to keep Jira updated with high-quality data. Jira automation also
supports triggers tied to devops events such as pull requests, builds,
branches, commitments, and deployments. These events connect with Bitbucket,
GitLab, and Github and update Jira issue or version status based on developer
activities performed in version control. More advanced triggers can run on a
defined schedule or respond to webhooks. Teams using these two triggers can
get very creative with integrating Jira workflows with other tools or
automating administrative tasks on a schedule. Once you configure the trigger,
you have the option to add more filtering conditions or to branch the flow and
support different sets of actions.
How trusted data is driving resilience and transformation beyond Covid-19

Over the next three to five years, most business workflows will be disrupted
by the application of data and artificial intelligence (AI). Efficiency will
be prioritised because it underpins business survival. If we take power and
utilities as an example, we can expect disruption of the billing workflow,
call centres, customer onboarding, customer service, and distribution.
Document intelligence will also be used to glean insights from large volumes
of information. Ultimately, data and AI will reinvent the entire end-to-end
value chains of industries. Companies that recognise the strategic value of
data will be the leaders in digital transformation, giving them a competitive
position in the market. ... The pandemic has highlighted the value of data
since having and sharing information on individuals will be key to defeating
the virus. So, in the evolving normal, we can expect more data-sharing
platforms – platforms that allow the public sector to share information with
the private sector and platforms that allow different companies within the
private sector to share information with each other. Boundaries between
sectors will blur over time and regulation will adapt to accommodate data
sharing.
Bluetooth Bug Opens Devices to Man-in-the-Middle Attacks

The Bluetooth SIG is recommending that potentially vulnerable Bluetooth
implementations introduce the restrictions on CTKD that have been mandated in
Bluetooth Core Specification versions 5.1 and later. These restrictions
prevent the overwrite of an authenticated key or a key of a given length with
an unauthenticated key or a key of reduced length. “The Bluetooth SIG is also
broadly communicating details on this vulnerability and its remedies to our
member companies and is encouraging them to rapidly integrate any necessary
patches,” according to Bluetooth. “As always, Bluetooth users should ensure
they have installed the latest recommended updates from device and operating
system manufacturers.” Several Bluetooth-based attacks have cropped up over
the past year. In May, academic researchers uncovered security vulnerabilities
in Bluetooth Classic that could have allowed attackers to spoof paired devices
and capture sensitive data. In February, meanwhile, a critical vulnerability
in the Bluetooth implementation on Android devices was discovered that could
allow attackers to launch remote code-execution (RCE) attacks – without any
user interaction.
Australia’s very small step to make the Internet of Things safer

Security flaws in IoT devices are common. Hackers can exploit those
vulnerabilities to take control of devices, steal or change data, and spy on
us. In recognition of these risks, the Australian government has introduced a
new code of practice to encourage manufacturers to make IoT devices more
secure. The code provides guidance on secure passwords, the need for security
patches, the protection and deletion of consumers’ personal data and the
reporting of vulnerabilities, among other things. The problem is the code is
voluntary. Experiences elsewhere, such as the United Kingdom, suggest a
voluntary code will be insufficient to deliver the protections consumers need.
... A better option would have been a “co-regulatory” approach. Co-regulation
mixes aspects of industry self-regulation with both government regulation and
strong community input. It includes laws that create incentives for compliance
(and disincentives against non-compliance) and regulatory oversight by an
independent (and well-resourced) watchdog. The Australia government has, at
least, described its new code of practice as “a first step” to improving the
security of IoT devices.
Four ways network traffic analysis benefits security teams

The SecOps team will often need the network data and behavior insights for
security analytics or compliance audits. This will usually require network
metadata and packet data from physical, virtual and cloud-native elements of
the network deployed across the data center, branch offices and multi-cloud
environments. The easier it is to access, index and make sense out of this
data (preferably in a “single pane of glass” solution), the more value it will
provide. Obtaining this insight is entirely feasible but will require a mix of
physical and virtual network probes and packet brokers to gather and
consolidate data from the various corners of the network to process and
deliver it to the security tool stack. NDR solutions can also offer the SecOps
team the ability to capture and retain network data associated with indicators
of compromise (IOCs) for fast forensics search and analysis in case of an
incident. This ability to capture, save, sort and correlate metadata and
packets allows SecOps to investigate breaches and incidents after the fact and
determine what went wrong, and how the attack can be better recognized and
prevented in the future.
A Beginner’s Introduction To DevOps Principles

To put it simply, DevOps is all about integrating these two teams together
(hence the portmanteau of a name). It isn’t going to make your developers into
sysadmins, or vice versa, but it should help them work together. Each aspect
and phase is complemented with tools that make this whole process easier.
DevOps is more than just tools and automation, and implementing a set of
“DevOps tools” won’t automatically make your team work twice as fast, but
these tools are a major part of the process, and it’d be hard to be as
efficient without some of them. ... Rather than testing and building only once
when everything is finished, in a DevOps environment, each developer will
ideally submit changes to source control multiple times a day, whenever issues
are complete or a minor milestone is reached. This allows the build and
testing phases to start early, and make sure no developer gets too far away
from the HEAD of the master source control. This stage is mostly about proper
source control management, so having an effective git service like GitHub,
Gitlab, or BitBucket are crucial to keeping continuous integration running
smoothly. You don’t have to deploy every commit to production right away, but
quick automated deployments are a major part of being able to push rapid
releases.
It's the biggest job in tech. So why can't they find anyone to do it?
The failure to appoint a senior leader to coordinate the mammoth task of
digitizing public services is at odds with the government's rhetoric. Three
years ago, the UK re-iterated the need to create a "government as a platform"
in a brand-new digital strategy, with the objective of harnessing the
potential of digital to improve the efficiency of public services. The goal?
To enable "digital by default" across government, and use technology and data
to better serve citizens with digitally enabled public services that would be
easier, simpler and cheaper. Since then, many reports have emerged stressing
the difficulty of achieving this digital transformation journey without proper
management from the very top. Last year, for instance, a report from the House
of Commons' Science and Technology Committee found that the government's
digital momentum was slowing, and that the shift was partly due to a lack of
senior leadership. These failures have been especially palpable in the past
few months. As the global COVID-19 pandemic threw the world upside down, the
need for a government that effectively delivers digital services in a time of
crisis became ever-more important.
Visa Warns of Fresh Skimmer Targeting E-Commerce Sites

The Visa alert does not indicate how Baka is initially delivered to a network.
But the report notes that the malicious code is hosted on several suspicious
domains, including: jquery-cycle[.]com, b-metric[.]com, apienclave[.]com,
quicdn[.]com, apisquere[.]com, ordercheck[.]online and pridecdn[.]com. Once
the initial infection takes hold, the skimmer is uploaded through the
command-and-control server, but the code loads in memory. This means the
malware is never present on the targeted e-commerce firm's server or saved to
another device, helping it to avoid detection, according to the alert. "The
skimming payload decrypts to JavaScript written to resemble code that would be
used to render pages dynamically," according to Visa. Once embedded in an
e-commerce site's checkout page, the skimmer begins to collect payment and
other customer data from various fields and sends the information to the
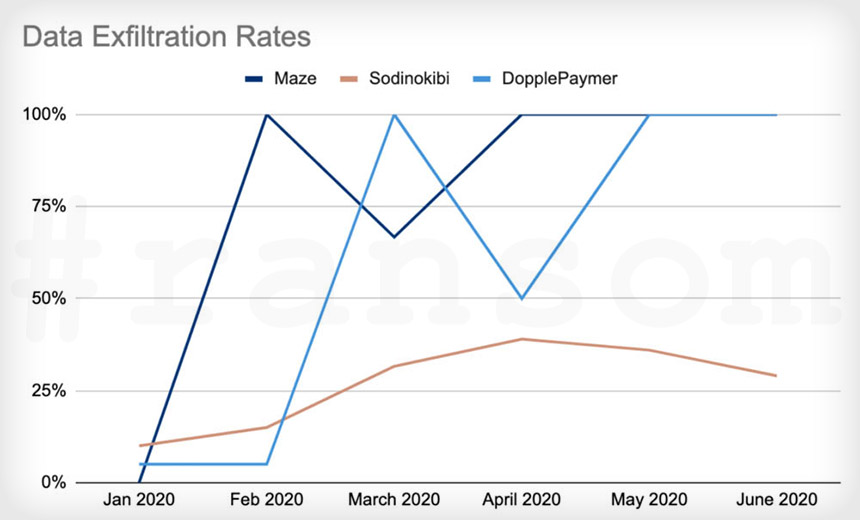
fraudsters' command-and-control server, Visa notes. Once data exfiltration is
complete, Baka performs a "clean-up" function that removes the skimming code
from the checkout page, according to the alert. This also helps ensure that
JavaScript is not spotted by anti-malware tools.
Elon Musk is one step closer to connecting a computer to your brain
While the development of this futuristic-sounding tech is still in its early
stages, the presentation was expected to demonstrate the second version of a
small, robotic device that inserts tiny electrode threads through the skull and
into the brain. Musk said ahead of the event he would “show neurons firing in
real-time. The matrix in the matrix.” And he did just that. At the event, Musk
showed off several pigs that had prototypes of the neural links implanted in
their head, and machinery that was tracking those pigs’ brain activity in real
time. The billionaire also announced the Food and Drug Administration had
awarded the company a breakthrough device authorization, which can help expedite
research on a medical device. Like building underground car tunnels and sending
private rockets to Mars, this Musk-backed endeavor is incredibly ambitious, but
Neuralink builds on years of research into brain-machine interfaces. A
brain-machine interface is technology that allows for a device, like a computer,
to interact and communicate with a brain.
Quote for the day:
"The actions of a responsible executive are contagious." -- Joe D. Batton