The basic definition of a digital twin: it’s a digital representation of a physical object or system. The technology behind digital twins has expanded to include larger items such as buildings, factories and even cities, and some have said people and processes can have digital twins, expanding the concept even further. Digital twins could be used in manufacturing, energy, transportation and construction. Large, complex items such as aircraft engines, trains, offshore platforms and turbines could be designed and tested digitally before being physically produced. These digital twins could also be used to help with maintenance operations. For example, technicians could use a digital twin to test that a proposed fix for a piece of equipment works before applying the fix the physical twin. With the explosion of IoT sensors, digital-twin scenarios can include smaller and less complex objects, giving additional benefits to companies. ... This is similar to the “run the simulation” scenario often seen in science-fiction films, where a possible scenario is proven within the digital environment. With additional software and data analytics, digital twins can often optimize an IoT deployment for maximum efficiency, as well as help designers figure out where things should go or how they operate before they are physically deployed.
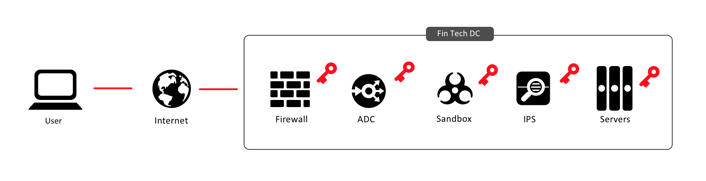
Cloud security: The reason hackers have it so easy will infuriate you
Cloud managers are playing catchup to close the door on the critical data left out in the open. Sophisticated new cybersecurity tools designed to securely store these kinds of credentials in a way that legitimate, automated processes can access, and intruders can’t—and to scan files uploaded to cloud storage to make sure passwords and keys aren’t exposed—are turning the tide, experts say. “Everyone knew this was a bad thing to do,” says Armon Dadgar, founder and co-CTO of San Francisco-based software company HashiCorp. “It wasn’t like anyone had an illusion that keeping these credentials in plain text was smart or sane, but no one had a better answer.” HashiCorp offers an open-source tool called Vault that stores sensitive credentials, encrypted themselves, and strictly limits what people, servers and programs can access them. Vault keeps logs of who accesses the secrets when. In some cases, it can also generate temporary credentials that give people permissions to use cloud resources for a limited time. Last month, cloud industry leader Amazon launched AWS Secrets Manager, its own credential management tool.
5 reasons why edge services are critical to your resiliency strategy

Edge services have become critical to helping organizations provide performance and security features to internal-facing apps like CRM and ERP systems, as well as customer-facing apps. Companies must direct users to the appropriate networks and infrastructure so they can connect to the proper services. Using edge services to move the point of control closer to the user enhances security and helps ensure compliance with regulatory and privacy specifications, where required. In addition, computing at the edge requires less latency and, with IoT devices, does not require constant connectivity, which would not hamper resiliency. More applications today rely on multi-cloud architectures for flexibility, resilience and improved performance at the edge. The analyst study cited business intelligence and reporting applications, IoT apps and marketing automation apps as among those most likely to use multi-cloud architectures. Moreover, multi-cloud in conjunction with edge services such as managed domain name system (DNS) solutions can improve resilience. DNS not only helps with application performance and network resiliency, but also optimizes web app performance and managing traffic across multi- cloud environments.
London's tech startups are booming, but their biggest challenge is just around the corner

UK companies could also find it harder both to attract the talent they need and actually get them into the country, depending on the harshness of the post-Brexit immigration policy. If the UK becomes less welcoming to foreign workers, companies will struggle to find the staff they need to be competitive, which could make them consider relocating. Longer term, the effect of the UK's exit from the European Digital Single market remains to be seen. This aims to remove barriers to consumers and businesses using and selling digital services across Europe, thereby growing the digital economy across the trading bloc. Another Brexit-related worry is the prospect of European cities such as Frankfurt mounting a challenge London as a financial centre, which may weaken its fin-tech status. A recent report from the Institute for Public Policy Research think-tank said that startups had three concerns about Brexit: "first, the uncertainty it has generated around the retention and recruitment of people; second, the possibility of regulatory divergence; and third, future access to finance."
Coinrail cyber heist highlights need for exchange security

The Coinrail heist has further raised concerns about the lack of regulation in the industry and is the latest in a series of heists at cryptocurrency exchanges, which cyber security analysts say is a logical target for cyber criminals whose primary aim is to amass wealth in the easiest ways possible. The Coinrail attack comes just months after Japan’s Coincheck cryptocurrency exchange lost $400m worth of digital currency and South Korea’s Youbit exchange was forced to file for bankruptcy and close after two cyber attacks, while in 2014 MTGox filed for bankruptcy after losing bitcoins worth around $500m. The Bank of England and global policy-makers are calling for greater regulation of cryptocurrencies to protect the financial system and reduce illicit activities. In March 2018, Bank of England governor Mark Carney said the time had come for regulation to hold the crypto-asset ecosystem to the same standards as the rest of the financial system. “A better path would be to regulate elements of the crypto-asset ecosystem to combat illicit activities, promote market integrity, and protect the safety and soundness of the financial system,” he said.
GDPR: UK Privacy Regulator Open to Self-Certification
Organizations in Europe may eventually be able to self-certify that they are compliant with the EU's General Data Protection Regulation, an official at the U.K.'s independent privacy watchdog said. But for now, "if anyone tries to tell you they're GDPR-certified - they're lying," Nigel Houlden, head of technology policy for the U.K. Information Commissioner's Office, said on Wednesday at the Infosecurity Europe conference in London during a panel discussion on GDPR. "There is no such thing as GDPR certification; there is only compliance that you can work toward," Houlden said. But he noted that the ICO is exploring how organizations might eventually be able to self-certify compliance with a list of GDPR requirements to help prove that they have been trying to comply with GDPR, especially if they should later suffer a breach or be reported to the ICO for some reason. The panel discussion, moderated by Brian Honan, head of Dublin-based BH Consulting, focused on how organizations can maintain compliance with GDPR, which became EU law in 2016. But many organizations appear to have been left scrambling to attempt to do something about GDPR since May 25, which is when each EU member state's privacy watchdog began enforcing GDPR compliance
Strong VPN Review: A Good VPN Service For Rookies

First and foremost, StrongVPN was able to access U.S. Netflix in my tests. The company doesn’t advertise the ability to get around Netflix’s regional restrictions, but at the time of this writing StrongVPN obliged. That could change, however, at any time. There is not a lot to StrongVPN in terms of extras, making this a solid choice for beginners or users looking for simplicity. Click the settings cog in the upper right-hand corner of the app, and the options screen opens. Under the Options tab there are some generic options such as “Start when Windows starts,” “Auto reconnect,” and “Connect on launch.” There’s also a kill switch option that kills all internet activity if the VPN connection drops, but at this writing the feature was not active. The only other place in the app to do any tweaking is under the Protocoltab. StrongVPN defaults to the IKEv2 protocol on Windows, but there are also options for OpenVPN, SSTP, and L2TP. The other tabs are just for looking at your account, diagnostics, and app updates.
How to get developer relations right for your company

The first order of business is to determine who your developer community includes. According to SlashData estimates, there are roughly 13 million developers, but that doesn't mean there are 13 million developers interested in your company/product. While some companies absolutely need random developers sitting in their garages to write applications to run on their platforms, that likely doesn't describe your need. In my case, our primary developer audience is employed by system integrators or other software vendors. They don't need campfires. They need APIs, documentation, use cases, and sample code to give them a running start on delivering on customer needs. You only learn this, however, if you listen to them. For example, when I took on my role running our developer ecosystem, I assumed what was needed was more developer assets. This was a gap, but the first-order priority was actually fixing the provisioning and authentication process such that a third-party developer could more seamlessly start working with the APIs we provide. As for internal needs, it was nice that I could tell the product teams to put all their documentation in a central repository, but it was better to learn that the reason they weren't doing so was that the system we had in place was too cumbersome.
The Cost of Fear in Organisational Change
Organisations today aim to adapt to a more collaborative, customer-centric, flexible format. Leaders have a genuine intention of creating an Agile organisation where people thrive and are allowed to make mistakes, as long as they learn from their errors. Experimentation will be the new approach. This is the dream, the quest, the purpose. And we have the “status-quo” of hierarchical organisations, annual targets and budgeting. We have all sorts of planning activities. This is our “status-quo”. The art of storytelling, calls the contradiction between the purpose and the status-quo, “creative tension”. As in all of humanity’s history, this “tension longing for change”,, operates also in the business environment. How can we truly step out of the status-quo and create a new (hi)story for the future of the business place? Without trying to answer this completely, let’s take a first step: let’s start by looking at the status quo’s impact on the aspiration to change. Peter Senge says that true tension is born when the theory exposed (what I aspire to) is different from the theory in action (what I actually do). If the tension is acknowledged, learning can occur. Effective alignment between the exposed theory and the theory in action can be achieved.
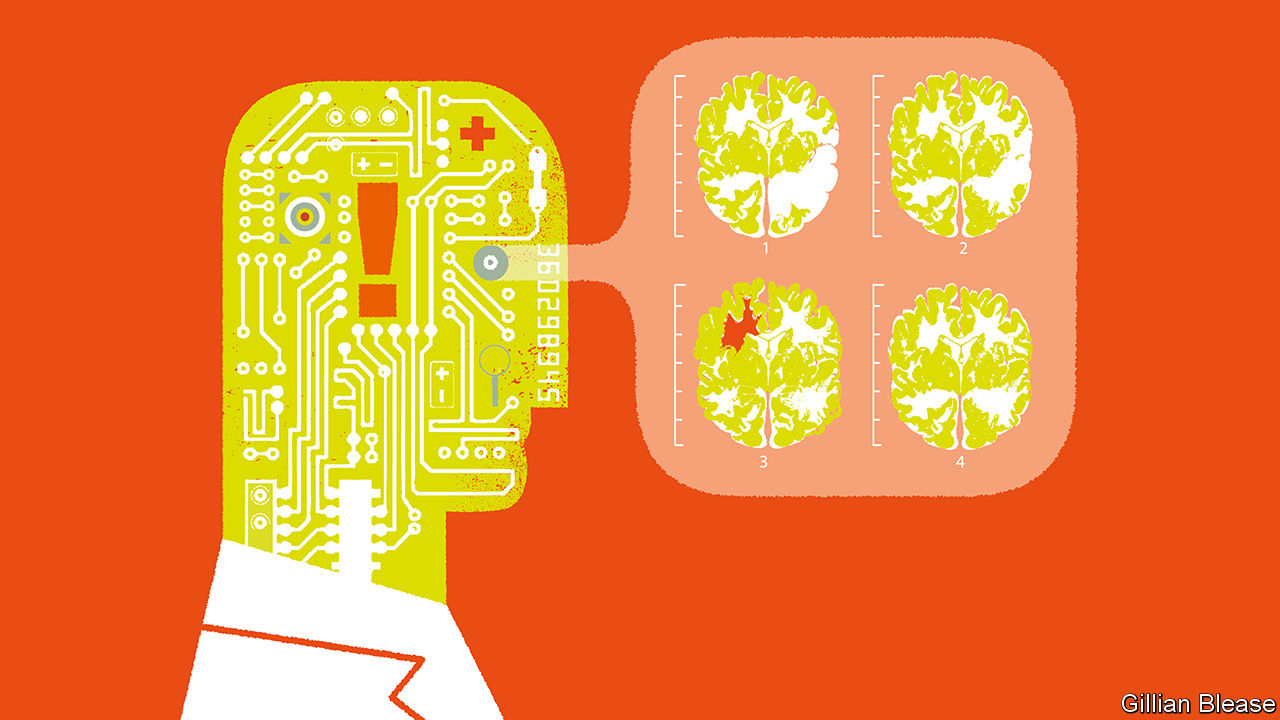
Why AI is So Brilliant and So Stupid

"It's all in the data, that's the number one thing to understand, and the feedback loops on truth," said Warren. "You need to know in a real way what's working and not working to do this well." Daniel Morris, director of product management at real estate company Keller Williams agrees. He and his team have created Kelle, a virtual assistant designed for Keller Williams' real estate agents that's available as iPhone and Android apps. Like Alexa, Kelle has been built as a platform so skills can be added to it. For example, Kelle can check calendars and help facilitate referrals between agents. "We're using technology embedded in the devices, but we have to do modifications and manipulations to get things right," said Morris. "Context and meaning are super important." One challenge Morris and his team run into as they add new skills and capabilities is handling longtail queries, such as for lead management, lead nurturing, real estate listings, and Keller Williams' training events. Agents can also ask Kelle for the definitions of terms that are used in the real estate industry or terms that have specific meaning at Keller Williams.
Quote for the day:
"Great listeners don't just hear what was said, they hear what was meant." -- @LeadToday