It may seem reasonable to worry about researchers developing very advanced artificial intelligence systems that can operate entirely outside human control. A common thought experiment deals with a self-driving car forced to make a decision about whether to run over a child who just stepped into the road or veer off into a guardrail, injuring the car’s occupants and perhaps even those in another vehicle. Musk and Hawking, among others, worry that a hyper-capable AI system, no longer limited to a single set of tasks like controlling a self-driving car, might decide it doesn’t need humans anymore. It might even look at human stewardship of the planet, the interpersonal conflicts, theft, fraud, and frequent wars, and decide that the world would be better without people. Science fiction author Isaac Asimov tried to address this potential by proposing three laws limiting robot decision-making
The fundamental benefits of the 'as a service' model are well known, and include: a shift from capital to operational expenditure (capex to opex), often leading to lower TCO (total cost of ownership); access for businesses of all sizes to up-to-date technology, maintained by service providers that can leverage economies of scale; scalability according to business requirements; fast implementation times for new applications and business processes; freeing up staff and resources for other projects and priorities. Of course there are potential downsides to 'as-a-service' adoption, which include: service outages; security, governance and compliance issues; inadequate performance; hidden costs; service provider lock-in; and customer support issues. Most of these potential problems can be minimised with good planning and a tightly-defined SLA ...
Microsoft Open Sources Java Debugger for Visual Studio Code Editor
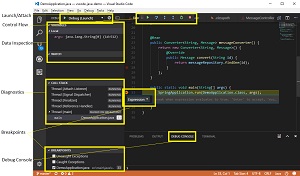
This week, while noting the move to open source, Microsoft also announced the open sourcing of the Java Debug Server that provides support on the back-end. "Since we first released our Java Debugger extension for Visual Studio Code on Sept. 28, it quickly became the most trending extension of the month," said Xiaokai He, program manager, Java Tools and Services, in a blog post. "And of course, lots of feedback and suggestions were submitted from our active developer community. ..." The two main improvements to the debugger mentioned by He are automatic resolution of a project's main class, so developers don't have to explicitly specify it anymore, and fully supported external source files. Speaking of the latter, He said, "With this feature, you can now also debug with third-party classes, when the source code is inside a JAR or a source attachment. And you can also set breakpoint in those classes ahead of debugging."
VHPC is on the rise, but comes with its own challenges
Despite these improvements, there are still challenges on the software side. HPC is often highly tuned and, moreover, might run on a nonmainstream Unix or Linux distribution that has many proprietary tweaks. Examples include Catamount OS, which the U.S. Department of Energy's National Nuclear Security Administration Advanced Simulation and Computing Program uses on the Red Storm supercomputer, the Compute Node Linux used in some Cray models and IBM's Compute Node Kernel. These are all lightweight kernels that minimize OS overhead. It can be difficult to get these through any hypervisor certification process, especially if they involve device drivers. One might think the answer is to go directly to a certified and supported Linux distribution, but one major issue with parallelized operations is that a compute cycle -- say an iteration of a simulation -- isn't complete until the last server finishes.
Cohesity makes it easier to manage secondary storage

Cohesity customers should see a marked reduction in total cost of ownership (TCO). The deduplication and data management capabilities will likely reduce the overall amount of data stored by more than 40 percent. The reduction in secondary storage is certainly nice, but the big savings to be had is operational. By my estimate, 60 percent of the TCO from secondary storage is in people costs. Like HCI has taken a chunk out of the operational costs associated with running different workloads, it will have the same impact on secondary data management. In fact, because this area lacks any kind of best practices or strategy, it’s likely to cut operational costs by 50 percent or more, freeing up valuable time for more strategic things. If you love HCI, you’re certainly not alone, as it’s been one of the fastest-growing IT technologies.
Why digital assistants are so hot right now

AI-enabled agents make an attempt to solve the “paradox of choice” that often leads to lower customer satisfaction and abandoned carts. Many retailers, including eBay, Walmart, and Whole Foods, bet on AI-powered virtual shopping assistants to fine-tune their offerings. ...Obviously, there’s a bigger picture for each individual benefit of digital assistants. On the one hand, the growth of voice assistants runs parallel with the progress in artificial intelligence, IoT, self-driving technology, and emerging interfaces based on text, audio, image, and haptic signals. The intelligent agent serves as a practical tool for today’s high-tech environment. It becomes indispensable to the normal functioning of the new generation of devices and emerging driverless cars, connected homes, and smart cities. On the other hand, AI-enabled assistants serve as a mediator between humans and innovation.
What is Asana? Task management tracking made easy

“[Asana] allows teams in organizations to determine how they need to work together,” said Margo Visitation, vice president and principal researcher at Forrester. “Whether they want to work in a way that is driven by conversations or by tasks, they have the opportunity to work in the way that is comfortable for the team.” Raúl Castañón-Martínez, senior analyst at 451 Research, said that Asana will benefit teams that previously relied on a diverse set of tools like spreadsheets, file sharing and even email and chat apps. “As projects grow more complex it becomes a burden trying to manage teamwork this way.” The software is relatively easy to use when compared to more complex project management tools sich as Trello and Smartsheet and is aimed at a wide range of business professionals. Asana’s product design is one of its key strengths, said Castañón-Martínez.
Google's grand plan for health, from fitness apps right up to defeating death

Its best-known healthcare product is Streams, an app designed to decrease the incidence of acute kidney injury before it occurs by alerting clinicians to the warning signs that indicate a patient is a candidate for such an injury. The app itself doesn't contain any AI at present -- think of it as more simple analytics software for healthcare -- it's likely that such elements will make their way into the products in future. The system is being trialled with the Royal Free hospital, and may be extended to other conditions where picking up the right signs early on can prevent a full-blown life-threatening condition, such as sepsis, taking hold. Other partnerships with UK healthcare organisations show the direction of travel for DeepMind's products. For example, in pilots with the Moorfields Eye Hospital and University College London Hospital,
Heart-stopping cybersecurity threats — literally
As the number of internet-connected medical devices and their respective vulnerabilities continues to grow, we must proactively take substantive steps to bolster their security and protect the Americans who rely on them by establishing health-care industry guidelines for how to best to defend against these types of radical cyber assaults. I was joined by my colleague, Rep. Susan Brooks (R-Ind.), in introducing the Internet of Medical Things Resilience Partnership Act, legislation that will bring public and private sector counterparts together to address the vulnerabilities of medical technologies by establishing a robust, yet malleable, comprehensible cybersecurity framework. We cannot stand idly by while these imminent attacks threaten the American people.
Beware the promise of a digital silver bullet
It could be the Architecture Tribe where everything is about infrastructure. Or the Automation Tribe who declare that robots are the only way forward. Or the Radical Redesign Tribe who will tell you it’s pointless doing anything unless you completely rethink the company from the ground up. Meanwhile, all you may want to do is row the boat a bit faster. And we chose the word ‘tribes’ with good reason. This isn’t a cohort of people rationally discussing the rights and wrongs of all their diverse approaches; these are frequently groups with fervent and invested beliefs in their own technical specialisms, who may be fiercely competitive, yet still need to be knitted together with a common purpose to create an environment of change. So how can a leader do all that? We’ve been developing a series of tools to help, one of which is the Digital Change Curve.
Quote for the day:
"The two most powerful warriors are patience and time." -- Leo Tolstoy























![wireless network - internet of things edge [IoT] - edge computing](https://images.idgesg.net/images/article/2017/09/wireless_network_management_world_map_iot_internet_of_things_edge_computing_thinkstock_684807514_3x2_1200x800-100736491-large.jpg)
