It May Be Too Early to Prepare Your Data Center for Quantum Computing

The fact that there are multiple radically different approaches to quantum
computing under development, with no assurance that any will meet market success
(let alone market dominance), speaks to quantum computing's infancy. Merzbacher
compares the situation to the early days of microprocessors, when there was a
debate on whether computer chips should be made of silicon or germanium. "There
were arguments for germanium. It's a better system for semiconductor computing
in some sense, but it's expensive, not as easy to manufacture, and it's not as
common, so in the end, it was silicon," she said. Quantum computing hasn't
reached a point where "everybody settled on a technology here, and so there
still is uncertainty. It may be that the IBM approach is better for certain
types of computing, and then the trapped-ion approaches [are] better for
others." This past March, IonQ became the first publicly traded pure-play
quantum computing company via a SPAC merger. According to Merzbacher, the
startup appears to have its eye on marketing rack-mounted quantum hardware to
the data center market, although it hasn't voiced such intentions publicly.
Lucas Cavalcanti on Using Clojure, Microservices, Hexagonal Architecture ...
One thing to mention about the Cockburn Hexagonal Architecture, is that it was
born into a Java object or entered word. And just to get a context. So what we
use, it's not exactly that implementation. But it uses that idea as an
inspiration. So I think on the Coburn's idea is you have a web server. And at
every operation that web server is a port and you'll have the adapter, which a
port that's an interface. And then the above adapter is the actual
implementation of that interface. And the rest is how to implement the classes
implement in that. The implementation, we use that idea of separating a port,
that it's the communication with the external world from the adapter, which is
the code that translate that communication to actual code that you can execute.
And then the controller is the piece that gets that communication from the
external world, and runs the actual business logic. I think the Cockburn
definition stops at the controller. And after the controller, it's already
business logic. Since we are working on Clojure and functional programming.
Excel 4, Yes Excel 4, Can Haunt Your Cloud Security

Scary? Sure, but still, how hard can it be to spot a macro attack? It’s harder
than you might think. Vigna explained XLM makes it easy to create dangerous but
obfuscated code. It started with trivial obfuscation methods. For example, the
code was written hither and yon on and written using a white font on a white
background. Kid’s stuff. But, later versions started using more sophisticated
methods such as hiding by using the VeryHidden flag instead of Hidden. Users
can’t unhide a VeryHidden flag from Excel. You must uncover VeryHidden data with
a VBA script or even resort to a hex editor. How many Excel users will even know
what a hex editor is, never mind use it? Adding insult to injury, Excel 4
doesn’t differentiate between code and data. So, yes what looks like data may be
executed as code. It gets worse. Vigna added “Attackers may build the true
payload one character at a time. They may add a time dependence, making the
current day a decryption key for the code. On a wrong day, you’ll just see
gibberish.” As VMware security researcher Stefano Ortolani added, Excel 4.0
macros are “easy to use but also easy to complicate.”
Agile Data Labeling: What it is and why you need it
The concept of Autolabeling, which consists of using an ML model to generate
“synthetic” labels, has become increasingly popular in the most recent years,
offering hope to those tired of the status quo, but is only one attempt at
streamlining data labeling. The truth, though is, no single approach will solve
all issues: at the center of autolabeling, for instance, is a chicken-and-egg
problem. That is why the concept of Human-in-the-Loop labeling is gaining
traction. That said, those attempts feel uncoordinated and bring little to no
relief to companies who often struggle to see how those new paradigms apply to
their own challenges. That’s why the industry is in need of more visibility and
transparency regarding existing tools (a wonderful initial attempt at this is
the TWIML Solutions Guide, though it’s not specifically targeted towards
labeling solutions), easy integration between those tools, as well as an
end-to-end labeling workflow that naturally integrates with the rest of the ML
lifecycle. Outsourcing the process might not be an option for specialty use
cases for which no third party is capable of delivering satisfactory
results.
Brain-computer interfaces are making big progress this year

The ability to translate brain activity into actions was achieved decades ago.
The main challenge for private companies today is building commercial products
for the masses that can find common signals across different brains that
translate to similar actions, such as a brain wave pattern that means “move my
right arm.” This doesn’t mean the engine should be able to do so without any
fine tuning. In Neuralink’s MindPong demo above, the rhesus monkey went through
a few minutes of calibration before the model was fine-tuned to his brain’s
neural activity patterns. We can expect this routine to happen with other tasks
as well, though at some point the engine might be powerful enough to predict the
right command without any fine-tuning, which is then called zero-shot learning.
Fortunately, AI research in pattern detection has made huge strides,
specifically in the domains of vision, audio, and text, generating more robust
techniques and architectures to enable AI applications to generalize. The
groundbreaking paper Attention is all you need inspired many other exciting
papers with its suggested ‘Transformer’ architecture.
Here’s how hackers are cracking two-factor authentication security

Our experiments revealed a malicious actor can remotely access a user’s
SMS-based 2FA with little effort, through the use of a popular app (name and
type withheld for security reasons) designed to synchronize user’s notifications
across different devices. Specifically, attackers can leverage a compromised
email/password combination connected to a Google account (such as
username@gmail.com) to nefariously install a readily available message mirroring
app on a victim’s smartphone via Google Play. This is a realistic scenario since
it’s common for users to use the same credentials across a variety of services.
Using a password manager is an effective way to make your first line of
authentication — your username/password login — more secure. Once the app is
installed, the attacker can apply simple social engineering techniques to
convince the user to enable the permissions required for the app to function
properly. For example, they may pretend to be calling from a legitimate service
provider to persuade the user to enable the permissions. After this, they can
remotely receive all communications sent to the victim’s phone, including
one-time codes used for 2FA.
Agile drives business growth, but culture is stifling progress

Senior leaders who invest in upskilling will ensure a culture of innovation in
the enterprise. Skills needed today and in the future are identified and
learning curves accelerated by providing immersive experiences to supplement
learning. At Infosys, we categorize employees into different skill horizons
based on workers’ core, digital, and emerging skills. For staying close to the
customer through better insights, data is not just a lazy asset locked in
systems of record — it is accessible through an end-to-end system that
translates customer insights into action. Going further, artificial intelligence
taps into unspoken team behaviors and interactions, which research from CB
Insights found increases revenue by as much as 63%. Teams will also need to
collaborate effectively and make decisions on their own. This will only happen
if leaders understand when to guide and when to trust. In our research, we found
that the most effective Agile firms (we call these “Sprinters”) are much more
likely to foster servant leadership, along with the seven levers described.
Attackers Change Their Code Obfuscation Methods More Frequently
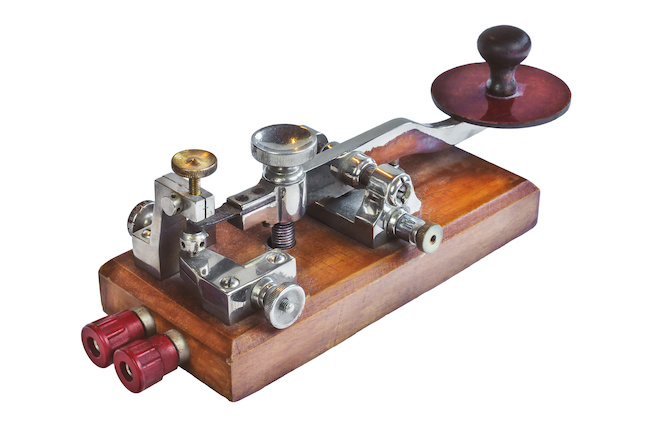
In an analysis posted last week, researchers at the Microsoft 365 Defender
Threat Intelligence Team tracked one cybercriminal group's phishing campaign as
the techniques changed at least 10 times over the span of a year. The campaign,
dubbed XLS.HTML by the researchers, used plaintext, escape encoding, base64
encoding, and even Morse code, the researchers said. Changing up the encoding of
attachments and data is not new, but highlights that attackers understand the
need to add variation to avoid detection, the Microsoft researchers said.
Microsoft's research is not the first to identify the extensive use of
obfuscation. Such techniques are as old as malware itself, but more recently,
attackers are switching up their obfuscation techniques more frequently. In
addition, increasingly user-friendly tools used by cybercriminals intent on
phishing make using sophisticated obfuscation much easier. Messaging security
provider Proofpoint documented seven obfuscation techniques in a paper published
five years ago, and even then, many of the obfuscation techniques were not new,
the company said.
Navigating an asymmetrical recovery

The key for many businesses will be to build scenarios that account for a wider
diffusion of results than was needed in the past. Take the cinema business as an
example. Instead of sales projections being drawn up in a band between down-10%
and up-10%, we’ve seen that some businesses can find themselves in a band
between down-70% and up-80%. An unexpected upside sounds like a nice problem to
have, but it also can create real operating challenges. Few of the companies
whose growth was supercharged during the pandemic had a plan for that level of
growth, which led to shortages, stock-outs, and delays that undermined
performance. Planning for extremes is almost certain to be critical for some
time to come. Although there is considerable liquidity overall in the debt
markets, whether from traditional loans, bonds, or newer debt funds, companies’
ability to access these markets will vary widely. Regional and country
differences in government support, along with variations in capital availability
between companies of different sectors and size, are all creating additional
asymmetries and unpredictable balance sheet pressures.
Driving DevOps With Value Stream Management
A value stream, such as a DevOps pipeline, is simply the end-to-end set of
activities that delivers value to our customers, whether internal or external to
the organization. In an ideal state, work and information flow efficiently with
minimal delays or queuing or work items. So far, this all sounds great. But good
things seldom come easily. Let's start with the fact that there are hundreds of
tools available to support a Dev(Sec)Ops toolchain. Moreover, it takes specific
skills, effort, costs, and time to integrate and configure the tools selected by
your organization. While software developers perform the integration effort, the
required skills may differ from those available in your software development
teams. Also, such work takes your developers away from their primary job of
delivering value via software products for your internal and external customers.
In short, asking your development teas to build their Dev(Sec)Ops toolchain
configurations is a bit like asking manufacturing operators to build their
manufacturing facilities.
Quote for the day:
"Great leaders are almost always great
simplifiers who can cut through argument, debate and doubt to offer a solution
everybody can understand." -- General Colin Powell
No comments:
Post a Comment