Pepperdata CEO says AI ambitions outpace data management reality

When we had just classic databases, data warehouses, and stuff like data was
managed sort of centrally, people had a very well-defined view of what was going
on. It was very narrow in scope. That definition has been blown to smithereens.
It’s like everything is enterprise data. It’s just ballooned. ... People are
realizing that data for customer success is really important. That part is
becoming more obvious to more people. If somebody comes to my website, and I
take three days to respond to them, they’re going to be gone. But if I can
respond to them in 30 seconds and say something intelligent, all of a sudden
that interaction becomes much more valuable. My sales cycles become much
shorter. The rest of it, concerning how to use the data to more efficiently run
my business, however, is completely unclear at this point. ... Every time we do
a new technology and all of a sudden people invest a ton in it, then you find
your finance people are writing it off. This is no different. The data wave has
been hyped so much that people are putting more and more money into it. They got
to be like Google. They have to be like Facebook.
Banks are moving their core operations into the cloud at a rapid rate. But new tech brings new challenges

As with any concentrated market, there is a risk that cloud providers might
start dictating their own terms, at the expense of the stability of the
financial system. For example, they could refuse to be transparent by failing to
open up their technologies to third-party scrutiny, meaning that it would be
impossible to know if providers have baked in sufficient resiliency to carry out
banking operations. Modernizing is key, therefore, but it needs to be done
cautiously, and with a reliable strategy. For James, the best way forward is to
deploy multi-cloud configurations in the financial sector to balance the risk
across multiple providers. Only 17% of the financial institutions surveyed by
Google have already adopted multi-cloud as an architecture of choice, while 28%
rely on single cloud. According to the company, more work needs to be done from
a regulatory aspect to incentivize a robust and responsible adoption of cloud
among financial organizations. "Consumers' demand for very quick transformation
is becoming really overwhelming, and financial services organizations will take
shortcuts to deliver on customer expectations as soon as possible," said
James.
What is federated learning?

Federated learning starts with a base machine learning model in the cloud
server. This model is either trained on public data (e.g., Wikipedia articles or
the ImageNet dataset) or has not been trained at all. In the next stage, several
user devices volunteer to train the model. These devices hold user data that is
relevant to the model’s application, such as chat logs and keystrokes. These
devices download the base model at a suitable time, for instance when they are
on a wi-fi network and are connected to a power outlet (training is a
compute-intensive operation and will drain the device’s battery if done at an
improper time). Then they train the model on the device’s local data. After
training, they return the trained model to the server. Popular machine learning
algorithms such as deep neural networks and support vector machines is that they
are parametric. Once trained, they encode the statistical patterns of their data
in numerical parameters and they no longer need the training data for inference.
Therefore, when the device sends the trained model back to the server, it
doesn’t contain raw user data.
How One Rogue User Took Down Our API
A team of developers won’t be able to suss out all the various bugs in your
services, but thousands of users will. And it only takes one to exploit a
weakness. While our zealous user was the flapping butterfly wing that lead to
the tornado, it was aided and abetted by our own bad assumptions. Fortunately,
there are strategies and tools you can use to mitigate these situations. If
you’re lucky, you have a Quality Assurance team dedicated to catching bugs. Have
you heard the one about a QA tester walking into a bar? Even if you do have a QA
team — and especially if you don’t — automated load, end-to-end, and fuzz
testing will also help catch those tricky bugs. I would recommend reading Martin
Fowler’s article on The Practical Test Pyramid. In the end, APIs are like
chainsaws. They are powerful tools intended to that empower our users. But that
power needs to come with the necessary safety measures. Without them, your users
may end up causing a lot of undue damage to both themselves and you.
Reliance on third party workers making companies more vulnerable to cyberattacks
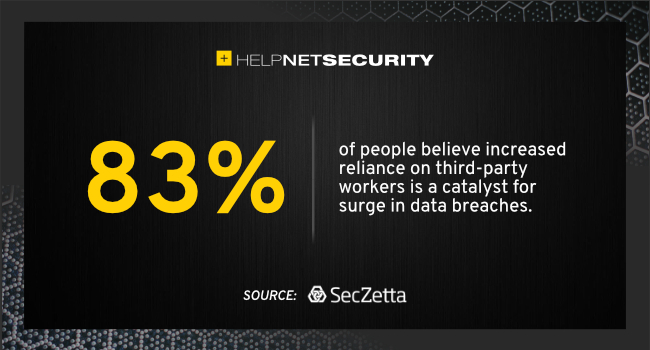
Too many organizations lack automated and effective methods to centrally track
and manage their relationships with the burgeoning number of third parties with
whom they do business. This, coupled with the lack of information organizations
have about these third parties, makes them a cybercriminal’s best friend. The
recent Presidential Executive Order (EO) mandates the federal government
“improve its efforts to identify, deter, protect against, detect, and respond to
these actions and actors.” For organizations looking to make changes to their
third party identity risk security measures, there are steps they can implement
today including: properly identifying who each third party is and the sensitive
data to which they have access; conducting regular user audits to ensure third
parties have access based on the least amount of privilege necessary to do their
jobs; extending zero trust programs to third party non-employees; and conducting
continuous risk ratings of the individuals working within a third party vendor
or partner, not just the organization as a whole.
The Intersection of Ecommerce and NFTs: How NFT Technology is Changing DeFi
DeFi (decentralized finance) technology allows for the inherent convenience of
centralized markets without allowing the wealth and governance authority to pool
into one person’s wallet. Essentially, DeFi is enabled by the blockchain, which
enables permission-less, peer-to-peer transactions. This removes middlemen like
banks and other large financial institutions. It lowers costs and technical
barriers for entrepreneurs and individuals. Fees, documentation, and legal
jurisdictions prevent many people across the world from accessing the financial
tools they need to succeed. DeFi platforms circumvent the need for all of these
things and allow them to transact in a secure environment. NFTs are the driving
force behind a significant portion of the DeFi infrastructure. NFTs aren’t
limited to collectibles. They represent programmable bits of data stored on the
blockchain. The blockchain provides a transparent, hack-proof storage solution.
This equates to ownership over pieces of data that can be programmed to do
different things when interacted with.
Top seven transformation trends dominating the digital ecosystem

Digital transformation essentially boils down to unlocking value for customers.
McKinsey estimates that digital transformation initiatives that focus on
customer-centricity increase customer satisfaction by 20-30% and economic gains
by 20-50%. Organisations investing in digital transformation are looking to
deliver innovative and seamless customer experiences in real-time. There is a
greater focus on customer lifetime value (CLV) and the role of innovative
customer experiences on long-term customer value. In a continuously evolving
digital ecosystem, with no dearth of choice and convenience, customer behaviours
are rapidly changing. In such a world, businesses need a holistic view of the
entire customer lifecycle to go beyond transactional interactions and establish
trust. Organisations are connecting each step in the customer journey to
interact and understand prominent needs and gain an exceptional number of
improvement opportunities. This is possible by implementing an automated data
collection process and creating a universally available data repository for
accurate, traceable, and updated information.
Are enterprises loving managed services?

The reason enterprises want to reduce their network-management burden is
difficulty in acquiring and maintaining skilled network-operations specialists.
This has been a problem for decades; network-operations specialists have no
career paths in most enterprises, so they top out in salary and promotion
opportunity. Over half of the 59 enterprises I talked with said that they had a
problem retaining a network specialist for more than three years, and 12 said
they had problems retaining them for two years. Every enterprise said that it
took longer to find qualified network specialists than programmers. ... A close
second in terms of managed-service drivers was difficulty in supporting remote
sites. The problem with remote network support, said 50 of my managed-service
enterprises, is that the best way for diagnosis of network problems at remote
sites requires that the network be used to project central technology skills to
those locations. Obviously, that's Catch-22 in action. This is one reason why
SD-WAN is so often associated with managed services; SD-WAN is all about adding
small, remote, sites to the company VPN.
Windows 365 response shows enterprises are hungry for cloud OS option

While a cloud OS may be attractive to some organizations and users, there will
be others that require additional app support that will still require access to
a machine with an onboard OS and apps (or at least browser-based access to a
different cloud). Many legacy enterprise apps may not run in such an environment
and are very unlikely to be migrated. Those users may not be good candidates for
a Windows 365 deployment. As a result, I don’t see a cloud OS like Windows 365
becoming the universal (or even dominant) OS anytime soon. The bottom line is,
enterprises that are struggling with managing multiple device types (e.g., PC
and Macs, Android and iOS, Chromebooks) that need a single access point (and a
single license) to apps might find Windows 365 an attractive option over buying
multiple licenses and/or managing multiple user device types at substantial
costs. Managing a cloud-based OS is far easier than managing installed OS and
app combinations. But for most companies, the current limitations of Windows
365, and a need to run many internal mature and legacy apps, will make Windows
365 a future rather than a current option.
How can we trust a digital identity? A security CEO explains…
It's hard to prove digital identity, and many of the current approaches – such
as email + password + SMS PIN codes – add complexity for the user without
actually addressing the core issue, which is: can these identities be trusted?
As I mentioned before, you can have email addresses that represent your identity
online. And you could have multiple [email] addresses – for example, it's easy
to get Gmail addresses; they're free, and so bad actors can exploit that
freedom. You can have multiple accounts created by using those multiple free
email addresses, and bad actors can hide behind them either to commit fraud or
just to spread fake news. The trick is very much to have some sort of balance
between the freedom and the friction; the freedom and that proven identity. ...
But if you can make it something that has an associated security factor – and
the phone does this, because it's got the SIM card – then you can have that
thing which you're willing to share, but at the same time has a proven
credential, and that allows you to build trust associated with that.
Quote for the day:
"Leaders make decisions that create the
future they desire." -- Mike Murdock
No comments:
Post a Comment