Let’s make testing Agile, they said. Uh, what did they mean by that?
Automated software testing is a fundamental part of Agile software development, even though it is not included in the manifesto. Automated testing helps in many ways, say Okken. But in general, a robust test suite helps ensure working software, increases a team’s ability to refactor and extend a software system, and respects individuals by automating the generally boring task of manual regression testing. “Automated tests also speed up development, further respecting the time of software developers, and allowing faster and more frequent deliveries to end users,” Okken says. “The development of automated tests during production code development helps developers understand the problem domain, the API, the problem at hand better, and help them in turn develop better software. Why would anyone want that learning to go to a separate team and not to the development team?” In adopting DevOps, you are discarding the traditional method of development, commonly called “waterfall,” for the more iterative process of building a small amount and testing rigorously we know as Agile.
Project Orleans and the distributed database future with Dr. Philip Bernstein
The set of mechanisms that we use to solve database problems, they don’t change very fast. Back in the early days, we were learning about certain base technologies for the first time, but now, there’s this repertoire of ingredients that you put into solving a database problem. I’m very sympathetic to graduate students who are trying to learn this stuff because, you know, I learned it slowly over a period of many years as it was unfolding, but people getting into the field, they learn it in a very compressed amount of time and they don’t necessarily have a deep understanding of why things are the way they are and so when they encounter a problem, they’re trying to solve it just based on an understanding of the problem and then trip over some approach that they think, oh, I’ll bet that would be helpful, but then they don’t realize this is actually a variation on something that has been applied in several other contexts before.
New botnet attack "puts other IoT botnets to shame"

A destructive new botnet that compromises vulnerable Internet of Things (IoT) devices and hijacks their resources to carry out devastating Distributed Denial of Service (DDoS) attacks is being reported by security research firm Bitdefender. The IoT botnet, which the company named "dark_nexus," has recently been found in the wild and is taking innovative and dangerous new approaches to successfully attacking IT infrastructure. "Our analysis has determined that, although dark_nexus reuses some Qbot and Mirai code, its core modules are mostly original," Bitdefender said in a 22-page white paper released April 8 about the attacks, "New dark_nexus IoT Botnet Puts Others to Shame." While some of its features may be shared with previously known IoT botnets, the way some of its modules have been developed makes dark_nexus significantly more potent and robust, the report said. ... "The victims won't even be aware that their devices are used as weapons against innocuous targets on the internet, even if the results might be catastrophic for victims or for the proper functioning of the internet," Botezatu said.
How Will The Cloud Impact Data Warehousing Technologies?

As data volumes continued to grow at rapid speeds, traditional relational databases and data warehouses were unable to handle the onslaught of this data. In order to circumvent this issue and ensure more efficient big data analytics systems, engineers from companies like Yahoo created Hadoop in 2006, as an Apache open source project, with a distributed processing framework which made the running of big data applications possible even on clustered platforms. Given the volume of data generated in the modern times and the advanced infrastructure required to handle it, decision support databases are facing considerable pressure to evolve, both technologically as well as architecturally. Alongside several new data warehousing architecture approaches, numerous technologies have also emerged as key contributors to modern business intelligence solutions, ranging from cloud services to data virtualization to automation and machine learning, among others. Cloud based solutions are the future of the data warehousing market. With numerous enterprises turning to the cloud to power and store their data warehousing solutions, internet companies like Amazon and Google and working tirelessly to develop and host innovative cloud-based data warehouses.
‘Unbreakable’ Smart Lock Draws FTC Ire for Deceptive Security Claims
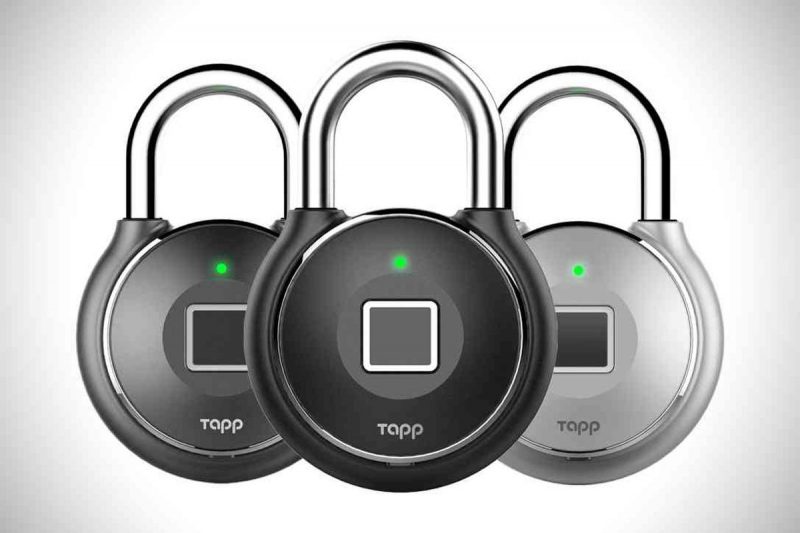
“This vulnerability allowed the researchers to sniff data packets for the information necessary to authenticate their access to the lock,” the FTC explained. “With that information, researchers were able to continue accessing the lock even after their access had been revoked.” Adding insult to injury, the complaint also noted that it’s possible unlock the smart locks by simply unscrewing the back panel. In June 2018, Youtuber JerryRigEverything posted a video demonstrating how the lock could come apart using a screwdriver to loosen and pop off the back of the lock, and then open the shackle. The upshot of all of this, according to the FTC, is that Tapplock “did not take reasonable measures to secure its locks, or take reasonable precautions or follow industry best practices for protecting consumers’ personal information,” despite advertising that it did. “[Tapplock] advertised its smart locks to consumers as ‘Bold. Sturdy. Secure.,'” according to the complaint. “[Its] advertisements touted that its ‘secure’ smart locks were also…designed to be ‘unbreakable.'” The complaint added, “in fact, [Tapplock] did not have a security program prior to the discovery of the vulnerabilities.”
Keeping Vigilant for BEC Amid COVID-19 Chaos
In fact, FBI IC3 recently noted in its 2019 Internet Crime Report that BEC scams accounted for 40% of the losses for cybercrime last year. That number is likely to spike even further as criminals see BEC in the pandemic as low-lying fruit. The rapid distribution of employees to makeshift work-from-home situations, the use of unfamiliar devices, the distractions and anxiety created by illness and business disruption, have all combined to create an ideal BEC hunting ground for the bad guys. "Employees working from home are likely to be even more distracted than usual, with children, household chores, and coronavirus anxieties all competing for their attention," explains Seth Blank, vice president of standards and new technologies at Valimail. "That will make them even less attentive to the subtle clues that an email is a phishing attack. And, when working from home, they're also more likely to be using a small screen or even their cellphones to manage email, which can make some of these phish attempts — which used bogus sender identities — nearly impossible to detect."
The APT groups examined in this report are likely comprised of civilian contractors working in the interest of the Chinese government who readily share tools, techniques, infrastructure, and targeting information with one another and their government counterparts. The APT groups have traditionally pursued different objectives and focused on a wide array of targets; however, it was observed that there is a significant degree of coordination between these groups, particularly where targeting of Linux platforms is concerned. The research identifies two new examples of Android malware, continuing a trend seen in a previous report which examined how APT groups have been leveraging mobile malware in combination with traditional desktop malware in ongoing cross-platform surveillance and espionage campaigns. One of the Android malware samples very closely resembles the code in a commercially available penetration testing tool, yet the malware is shown to have been created nearly two years before the commercial tool was first made available for purchase.
Wanted urgently: People who know a half century-old computer language so states can process unemployment claims

On top of ventilators, face masks and health care workers, you can now add COBOL programmers to the list of what several states urgently need as they battle the coronavirus pandemic. In New Jersey, Gov. Phil Murphy has put out a call for volunteers who know how to code the decades-old computer programming language called COBOL because many of the state's systems still run on older mainframes. In Kansas, Gov. Laura Kelly said the state's Departments of Labor was in the process of modernizing from COBOL but then the virus interfered. "So they're operating on really old stuff," she said. Connecticut has also admitted that it's struggling to process the large volume of unemployment claims with its "40-year-old system comprised of a COBOL mainframe and four other separate systems." The state is working to develop a new benefits system with Maine, Rhode Island, Mississippi and Oklahoma. But the system won't be finished before next year. "Literally, we have systems that are 40-plus-years-old," New Jersey Gov. Murphy said over the weekend.
“VMware’s goal is to make NSX invaluable to the VMware installed base as those customers modernize their on-premises data-center network infrastructure and similarly seek to provide consistent network and security polices for modern applications running in public clouds," Casemore said. "As the data center becomes distributed in a multicloud world, the data-center network must become a multicloud data-center network. On the VeloCloud [VMware’s SD-WAN offering] side, the focus is on modernizing the WAN to accommodate delivery of these applications to the branch.” One new feature of NSX is the ability to control and synchronize multiple virtual networks as a single entity. Called NSX Federation, the feature lets customers set network configuration, management and policy setting across large environments. NSX Federation would let customers generate “fault tolerant zones” where they could contain network problems in a single zone, minimizing problems and preventing them from spreading, VMware stated.
The hard of hearing community has been contributing to the success of business globally in all kinds of industries. They’ve navigated the challenges of building connections even when dealing with the issues of fast paced conversations and multiple speakers in meeting settings. They’ve adapted by learning to read lips, pick up on speech patterns and build support networks with peers to help them keep pace with their fully hearing capable counterparts. Some of us may feel like this really has nothing to do with our own work experience. But based on the following items of note from the Disabled World Organization and the World Health Organization, you are bound to know, work with or even become someone who is hard of hearing. Approximately 432 million adults worldwide have a disabling hearing loss. It is estimated that by 2050, more than 900 million people will have a disabling hearing loss. There is a progressive loss of ability to hear high frequencies with increasing age known as presbycusis.
Quote for the day:
"Great leaders go forward without stopping, remain firm without tiring and remain enthusiastic while growing" -- Reed Markham




No comments:
Post a Comment