Strategies for Improving Smart City Logistics
 Efficient, timely and accurate delivery is a necessity to retailers and logistics providers survival in an Amazon Prime world. Smart Cities goals of livability and sustainability means they want less trucks, congestion and pollution. For all stakeholders to achieve their goals, the only answer is to work together. If cities, retailers, and logistics providers work together, collaboration and digital solutions can help resolve traditional challenges of last-mile logistics and improve the livability and sustainability of cities. ... In Europe, where they have higher urbanization, more aggressive goals for CO2 reduction, and the width of the streets in its older cities are less equipped to handle a rise in urban freight transport, there have been many initiatives and cities working on this issue. The European Union has been co-funding and working together more collaboratively with cities and partners such as logistics companies like TNT and DHL, as well as, local retailers in the creation of consolidation centers and more sophisticated delivery practices.
Efficient, timely and accurate delivery is a necessity to retailers and logistics providers survival in an Amazon Prime world. Smart Cities goals of livability and sustainability means they want less trucks, congestion and pollution. For all stakeholders to achieve their goals, the only answer is to work together. If cities, retailers, and logistics providers work together, collaboration and digital solutions can help resolve traditional challenges of last-mile logistics and improve the livability and sustainability of cities. ... In Europe, where they have higher urbanization, more aggressive goals for CO2 reduction, and the width of the streets in its older cities are less equipped to handle a rise in urban freight transport, there have been many initiatives and cities working on this issue. The European Union has been co-funding and working together more collaboratively with cities and partners such as logistics companies like TNT and DHL, as well as, local retailers in the creation of consolidation centers and more sophisticated delivery practices.Bank Products Are Dead: Long Live Experiences

By 2020 we’re going to see 50 billion new devices connected to the Internet — everything will be smart. Smart Fridges that order your groceries or can tell you what you can cook with the remaining items inside, sensors you wear on your wrist or in your clothes that monitor your health and activity, cars that will talk to each other and drive themselves, smart mirrors that will show you how you look in that new shirt, robot drones and pods that will deliver you groceries or Amazon order — the world will be filled with smart stuff. We live in a world where new technology emerges and is adopted in months today, versus the years it took previously. It’s all moving so quickly. As more and more technology is injected into our lives, we become acclimatized and just accept the increased role technology has to play. This is known as technology, adoption diffusion. As we move to this technology-optimized world, we’ll start to redesign where and how humans fit in society. Banking will be embedded in our life.
This mind-reading AI can see what you're thinking - and draw a picture of it

While headlines around the world have screamed out that AI can now read minds, the reality seems to be more prosaic. Computers are not yet able to anticipate what we think, feel or desire. As science writer Anjana Ahuja remarked in the Financial Times, rather than telepathy, “a more accurate, though less catchy, description would be a ‘reconstruction of visual field’ algorithm”. Most of the research so far has been aimed at deciphering images of what subjects are looking at or, in limited circumstances, what they are thinking about. Studies have previously focused on programs producing images based on shapes or letters they had been taught to recognize when viewed through subjects’ minds. However, in one recent piece of research, from Japan’s ATR Computational Neuroscience Laboratories and Kyoto University, scientists said that not only was a program able to decipher images it had been trained to recognize when people looked at them but: “our method successfully generalized the reconstruction to artificial shapes, indicating that our model indeed ‘reconstructs’ or ‘generates’ images from brain activity, not simply matches to exemplars.”
Microsoft officially christens 'Redstone 5' as the Windows 10 October 2018 Update

The October 2018 Update rollout will likely be staggered, as in past feature releases, with machines known to be able to best handle the new bits getting them pushed to them first. Microsoft also will likely begin rolling out the server complements to the October 2018 Update -- Windows Server 1809 and Windows Server 2019 -- on the same day in October as the client build goes live. The part of today's announcement that is a bit more surprising is that Microsoft is still saying that the October 2018 Update will be going to the "nearly 700 million devices" running Windows 10. Microsoft has been using this same 700 million figure since March 2018 and hasn't provided an updated momentum figure. ... The Windows 10 October 2018 Update will include the Cloud Clipboard, dark-mode File Explorer option, a number of new Notepad features and other tweaks and updates. It also will deliver a number of new security and enterprise features, as well as a new Windows 10 Enterprise Remote Sessions edition. Microsoft will likely detail these enterprise features at its Ignite show.
Want To Survive & Thrive With AI?…Then Mind The Skills Gap
“The battle for diversity is vital, just from the perspective of finding the best talent in the widest possible pool. Demystifying the idea that AI is something very difficult is crucial, you do not need to code like Sergey Brin, the co-founder of Google. Being unafraid of a strange discipline is key. There is a huge gap between STEM and the arts and we need each other,” says Dr Lauterbach. ... “The phrase Artificial Intelligence is misleading because everything happens by human design. Human beings pick big data sets, algorithms, methodology and processing hardware.” According to Dr Lauterbach, if algorithms are not created to be inclusive, they could contribute to inequalities and thus would not be effective in helping the world. “AI has a capability to scale everything we are about as humans,” she says. “So if you have a team of only white male developers or only Chinese male developers, then you will get a data set or some algorithms that are wired according to the preferences, habits and thinking processes of those groups.”The Modern Marketing Model for the Financial Industry
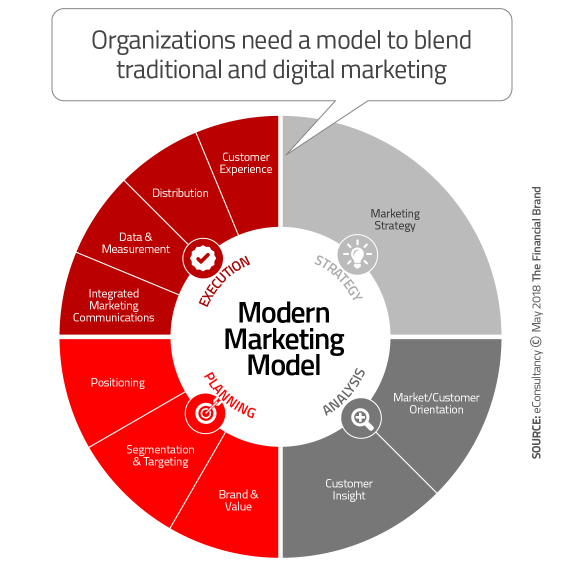
When we consider the new complexities of modern financial services marketing, it is best to integrate both traditional and digital marketing in a manner that achieves synergistic benefits. By fusing together both classical and digital marketing, organizations are in a better position to identify capability gaps placing a focus on where and how to move forward. The chart below from eConsultancy helps to visualize the required components. This model is a natural progression from previous models used by marketers. For instance, in the 1960s, the prevalent marketing model was the ‘4Ps’ (Product, Price, Place and Promotion). In the 1980s, there were three additional Ps added (People, Process and Physical) reflecting increased customer interaction and the beginning of targeting. In the 1990s, ROI entered the equation, as did the ongoing increase in importance of targeting (the ‘4Cs’ included Consumer, Cost, Communication and Convenience). The new marketing model highlights the importance of customer insight, analytics, brand and customer experience.
7 factors that will push implementation of AI in healthcare

Because artificial neural networks of deep learning mirror the brain’s ability to learn difficult patterns, Hinton noted that the networks also model complicated between inputs and outputs used for predicting future medical events from past events or large data sets. “As data sets get bigger and computers become more powerful, the results achieved by deep learning will get better, even with no improvement in the basic learning techniques, although these techniques are being improved,” Hinton wrote. A remaining challenge artificial intelligence has yet to overcome, Hinton wrote, is detecting patterns in unlabeled data in the process called “unsupervised learning." “As new unsupervised learning algorithms are discovered, the data efficiency of deep learning will be greatly augmented in the years ahead, and its potential applications in healthcare and other fields will increase rapidly,” according to Hinton. Overall, clinicians and physicians should be aware of the challenges that come with implementing AI and deep learning into everyday workflow and know how to efficiently approach it
 Another sticking point the panel discussed was the issue of maturity. That is, organizations have to ask themselves whether they truly have the ability to define, develop and manage their AI investments in a way that will create value. After all, AI isn’t some piece of plug-and-play software you can just flip on and start using. There are significant process changes that need to occur, in technology systems and human employees alike. Security should also be of chief concern. AI’s impact on security can be profound, which means you must determine what controls and protections will be necessary from the very beginning to ensure your sensitive data (sources and outcomes) remain secure. When there’s confusion and disagreement over how to proceed, it can lead to a case of analysis paralysis. So before charging full steam ahead with AI, companies should realistically assess their own readiness to do so. Thankfully, the IP Soft AI Pioneers Forum is now working to develop a universal AI maturity model that may be helpful to companies in these cases.
Another sticking point the panel discussed was the issue of maturity. That is, organizations have to ask themselves whether they truly have the ability to define, develop and manage their AI investments in a way that will create value. After all, AI isn’t some piece of plug-and-play software you can just flip on and start using. There are significant process changes that need to occur, in technology systems and human employees alike. Security should also be of chief concern. AI’s impact on security can be profound, which means you must determine what controls and protections will be necessary from the very beginning to ensure your sensitive data (sources and outcomes) remain secure. When there’s confusion and disagreement over how to proceed, it can lead to a case of analysis paralysis. So before charging full steam ahead with AI, companies should realistically assess their own readiness to do so. Thankfully, the IP Soft AI Pioneers Forum is now working to develop a universal AI maturity model that may be helpful to companies in these cases.Focusing on machine learning 2020: augmentation instead of automation
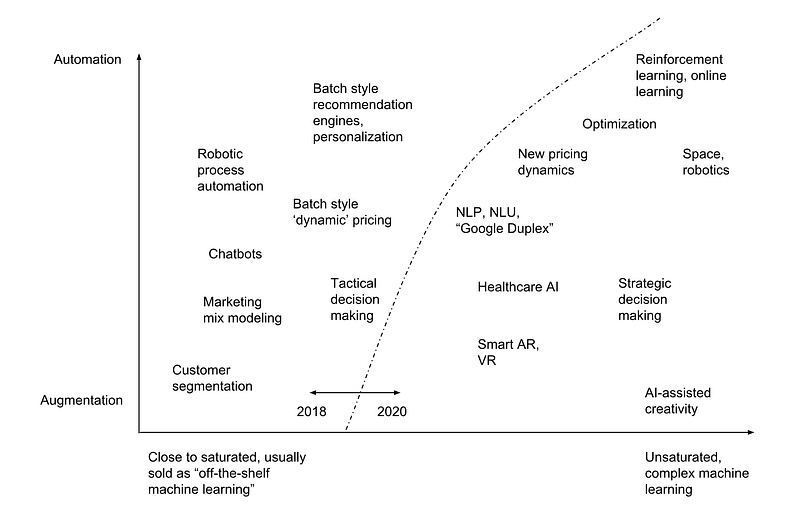
The holy grail of augmentation can be easily seen as the pursuit of creativity but there are many other areas of interest as well. Strategic decision making, such as choosing where to build new skyscrapers, where to build new infrastructure (bridges, roads, facilities), what type of aircraft should we buy to maximize profitability and growth and what routes should we fly —counting in sustainability. These questions are still largely thought out with excel sheets, BI-tools and GIS-systems, and maybe some legacy statistics software (SAS, SPSS) with some custom analysis. While that may be sufficient for some industries, many of these problems have so many attributes that it’s impossible for us as humans to make optimal decisions — hence welcoming optimization and machine learning to help as augmenting features of decision making. And despite the fact that it’s still quite early to tell, deep learning may well be of use here
Quote for the day:
"Becoming a leader is synonymous with becoming yourself. It is precisely that simple, and it is also that difficult." -- Warren G. Bennis