Cambridge Analytica’s secret coding sauce allegedly leaked

Security firm UpGuard claims that it found a large code repository from AggregateIQ (AIQ), a Canadian political data firm also active in the 2016 US presidential race, left publicly downloadable online. You might remember that data analytics firm’s name for its part in Brexit: the official Vote Leave campaign gave £3.5m to AIQ, which, like CA, specializes in highly targeted Facebook advertising. Over the weekend, The Guardian reported that CA has undisclosed links to AIQ. The Guardian reports that former CA employee/founder turned whistleblower Christopher Wylie has revealed that besides setting up CA, he was also a central figure in setting up AIQ. AIQ and CA’s parent company, SCL Group, are tied by an intellectual property license, but the threads that bind go way beyond that: Wylie says that some CA staff referred to AIQ as a “department” within the company and that the two businesses shared the same underlying technology. According to UpGuard, it found that technology within an open repository that holds a smorgasbord of tools used to influence individuals
Cisco emboldens its disaggregation strategy
“We are already seeing customers use these early capabilities to run applications for network analytics, security, network operations workflows and IoT on the network infrastructure,” Cisco said. For its data center customers, Cisco said it will now offer a number of portability options for its Nexus switches and the Nexus Operating System (NX-OS) — including the Cisco Cloud Scale Switch Abstraction Interface (SAI). “SAI lets customers the freedom run the network operating system of their choice on our SAI-ready Nexus platforms. Microsoft and other web-scale customers are now running their Sonic operating system on these Nexus 9200/9300 platforms,” Cisco stated. In addition Cisco said it’s now possible to run its Nexus Operating System (NX OS) on third-party hardware platforms — independent of Nexus switches. Cisco also now offers a virtual NX OS that “will let customers simulate new features during upgrades through the software upgrade impact on existing tooling environment for their actual large-scale topologies.”
Fixing Hacks Has Deadly Impact on Hospitals
Choi says that hospitals should be careful to focus changes in their security processes, procedures, and technology to improve both data security and patient outcomes. Ponemon sees healthcare organizations starting to improve in security. "We do see healthcare organizations starting to take care of security and rising to the next level of security. I think the public demands it," he says. Two factors contribute to the improvement across the industry, he says. The first is the simple acknowledgement that doctors and hospitals are targets - an acknowledgement that was a long time coming. The next is the march of technology. "There are technologies that healthcare can now afford because they're available in the cloud and it provides the opportunities for healthcare security to improve," Ponemon says. The improved security may come just in time to have an impact on a looming area of security concern: The medical IoT. "There's a universe of devices, many of which are implanted and many can be communicated with through WiFI or Bluetooth," Ponemon says. "Right now, the providers are looking at records but the devices are really an area of huge concern."
A Different Take on Voice Interfaces, IBM Launches Watson Assistant

IBM's deployment model is a little different from the other assistants, however. You won't be able to download an IBM Watson app directly from IBM, Greenstein said, or buy an IBM smart speaker. Instead, IBM is offering Watson Assistant to business/technology partners who will incorporate it into their own offerings. Those offerings will then be offered to consumers. For instance, an automobile company could embed the assistant in the car dashboard. One early partner is automotive embedded electronics company Harman. Hotels may offer the assistant in a mobile app that consumers can use to control the experience in their hotel rooms in terms of lighting, music, and other features. The service is delivered through the IBM Cloud, and IBM says it also incorporates contextual elements, such as delivering particular experiences to consumers based on their location and time of day, anticipating their needs and proactively making recommendations, the company said. For instance, a traveler may be listening to certain music in her rental car. Watson Assistant could then ensure that same music is playing in her hotel room once she checks in.
Is 2018 the Tipping Point in Digital Transformation?
Digital is destroying this equation by creating more value for customers than for firms. For example, digital competitors with niche products and agile delivery offerings are forcing organizations to unbundle profitable product and service offerings. This results in more freedom of choice for customers to buy only what they need (and not being forced to buy what they don’t need). This is shifting the profit pools and decision making away from the firms and towards the customers. Digital also renders physical distribution intermediaries obsolete. Consider, how healthy is your nearest big-box store? With digital distribution providing limitless choice and price transparency, digital offerings can be reproduced freely, instantly, and perfectly, shifting value to hyper-scale players while driving marginal costs – and product margins – towards zero. ... Profits are no longer distributed across a large number of participants. Think about how Amazon’s market capitalization towers above that of other retailers or how the iPhone regularly captures over 90+ percent of ALL the smartphone industry profits.
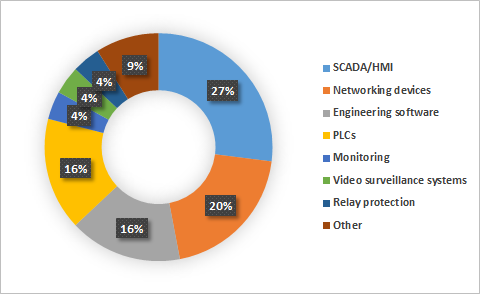
Why IoT security should keep you up at night

Despite the steady year-over-year growth in worldwide spending, Gartner predicts that through 2020 the biggest inhibitor to growth for IoT security will come from a lack of prioritization and implementation. This means that companies using IoT won’t follow security best practices and use the right tools in IoT planning. This will hamper the potential spend on IoT security by 80 percent, which means that the hackers will go after these connected devices, like they would a bank vault with a screen door. The fact of the matter is that keep things secure—your cloud-based systems, traditional on-premises systems, and now IoT devices—everything must be secure that is interconnected. Security is like the links of a chain: It’s only as strong as the weakest link. This weakest link is now typically a robot on the factory floor, the thermostat on the wall, or even the fitness tracking watches you’re probable wearing right now. Cloud computing security is holistic, meaning it needs to be systemic to all cloud-based platforms and workloads—including any systems connected to those workloads, and any devices connected to the cloud.
How to Use AI and Blockchain in a Disruptive World
Actively seek out opinions that contradict your own. Don't allow yourself to live within an echo chamber, including only those opinions you already agree with. The truest measure of intelligence is the ability to hold two opposing views at the same time, so practice this. The world is becoming more decentralized, resulting in competing and vastly divergent realities. Nobody's willing to change their mind, and everyone has plenty of evidence that they're right and everyone else is wrong. This is a form of anarchy. Do it differently. Success amidst anarchy requires defiant leadership! The most strategic thing you can do is fine-tune your unique value proposition. Open a document on your computer, or pull out a notebook and write down your thoughts to this: Who are you? What do you stand for? Since the world is characterized by competing realities, you have to pick your reality and ignore the rest. You can't change people's minds. Build your tribe and ignore the haters.
What is the Open Compute Project?

When Facebook designed the hardware for its first dedicated data center in Prineville, Ore., it wanted to make savings on three fronts: energy, materials and money. It boosted energy efficiency by cutting wastage in the power supply and by making the servers taller, which left room for bigger, more effective heatsinks and meant that it could use fans of a larger diameter, able to move more air with less energy. By doing away with vanity faceplates, paint, logos, unneeded expansion slots and components such as video cards and even mounting screws, it saved more than 6 pounds of material per server. That inevitably led to cost reductions, as you don’t pay for electricity you don’t consume or parts you don’t use. On top of that, it made savings on labor: Without the mounting screws, racking and unracking servers was quicker; standardization saved time dealing with spares, and overall systems coulc be deployed more quickly. In its 2018 spending study, IHS Markit identified the three main barriers to the adoption of OCP hardware as being concerns about security, sourcing, and integration.
Time for Transformational Cybersecurity!
The exponential growth of cyber-attacks, as evidenced by newspaper headlines describing massive loss of our personal information, including credit information and passwords, is now a Presidential level challenge and has elevated cyber to a U.S. National Security warfare area. Not often discussed or considered is the fact that every cyber malware attack must borrow a Computer Processing Unit (CPU) instruction from the attack target system in order for attacking software to operate the malware instructions! In the physical world equivalent, such as bank robberies, criminals must borrow access to city streets, bank buildings, and bank vaults to conduct successful robberies. Fortunately, in cyber space, new synergistic technologies are now available to prevent malware from borrowing CPU instructions, thereby significantly enhancing cyber defense-in-depth. Unfortunately, most organizations are reluctant to purchase this enhanced cybersecurity because they are confused by all of the cybertool hype and fall back on the mythology that persistent cyber intruders will always win so what they have is good enough.
IT Leadership: Winning at What Cost?
Companies establish and center their culture on a code of conduct that highlights their company’s values. Values start skewing when winning comes into play. All for-profit companies strive to make money, grow business, and put competitors out of business. That is the nature of the game. Thus, winning is also where “shades of grey” can come into play, as sinful deeds can lead to gainful deals. These situations provide leaders with an opportunity to show their true character and deliver their core leadership values. Their team members are watching and observing the rules of engagement. What is allowed? What is a foul? And what falls in between? The simple question they want answered is: How is one rewarded within an organization by its leadership team? This question and its answer drive the behavior of the people within an organization and set the culture for the organization as a whole. For better or worse, leaders need to understand the dynamics with respect to delivering wins because too much rewarding for sins leads to a lethargy from team members who are playing it straight up.
Quote for the day:
"If no good can come from a decision, then no decision should be made." -- Simon Sinek