The best robots and AI innovations at CES 2023
Advancements in autonomous driving haven't developed as quickly as some imagined
they would. However, cars are incrementally becoming smarter and smarter, with
autonomy seemingly just over the horizon. Case in point: Peugeot, Stellantis's
French automobile brand, unveiled the Inception Concept car, an electric vehicle
demonstrating what a car can be, once you do away with the steering wheel, get
comfortable and let the vehicle get to know you a little. ... While autonomous
cars are still in development, other market-ready autonomous mobility tools were
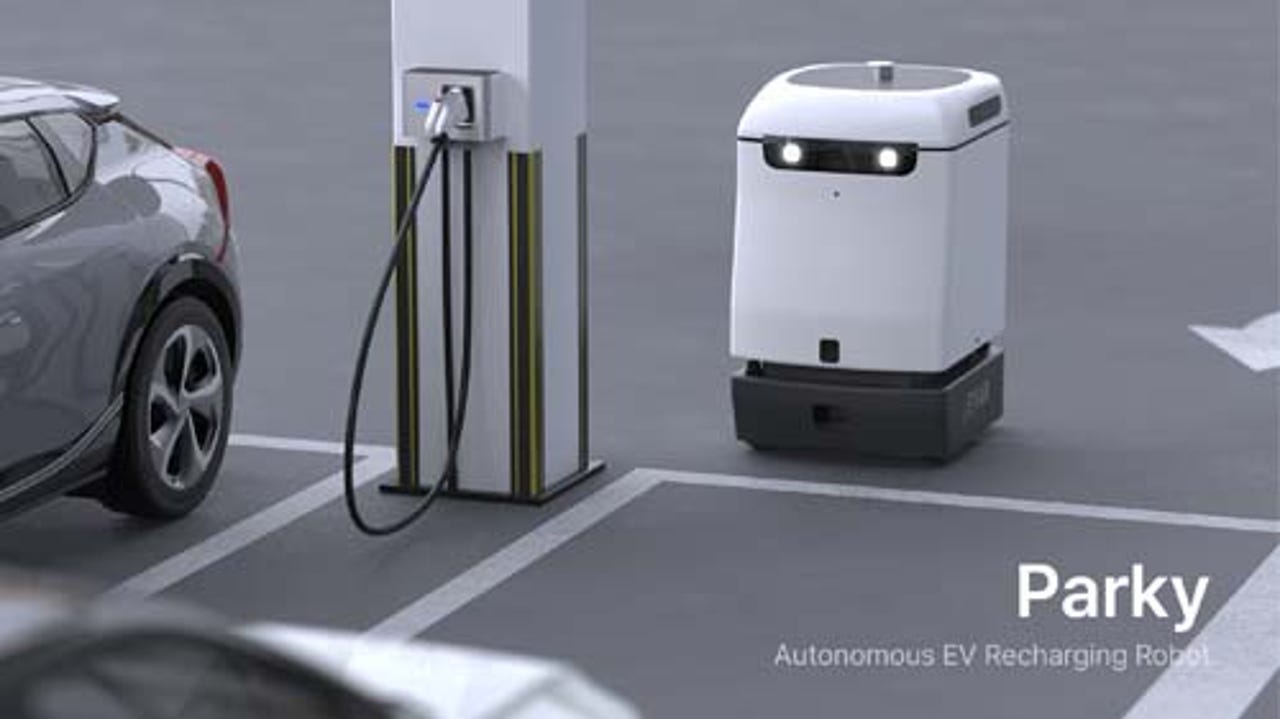
on display on CES. The company Evar was at the conference with Parky, an
autonomous EV recharging robot that brings a charging station to any parking
spot. It's designed for building owners that want to make their parking spots
more EV-friendly without adding electric capacity. ... The Withings U-Scan
toilet bowl sensor attaches to the inside of your toilet's bowl. It includes a
nutrition and metabolic urine tracker, checks pH, ketone, vitamin C levels, and
more. A second tracker monitors women's luteinizing hormone for ovulation
cycles. Each promise early detection of potential health issues.
Math Behind Software and Queueing Theory
Unsurprisingly, queueing theory is a branch of mathematics, focused on studying
and describing queues (or, in more professional terms, lines). The whole theory
is all about how lines are created, how they behave, and, most important, how
and why they malfunction. It is one of these branches of mathematics which are
useful in real life; e.g., it can be used in many branches of industry. ...
Basically, we can treat most of the systems like a queue so users send requests,
the request process, and the response return to the user, or when the system is
too busy to process the request right away, the request waits until some
arbitrary timeout is reached or it will be processed. The real problem is to
correctly identify the class of the system we are working on. In most cases, it
will be the variation of M/M/c or Mx/m/c. Unfortunately, it can result in our
calculations not being very in line with real life. As long as we are taking
care of long-term average system performance then M/M/c is an appropriate
description and most of the inconsistencies should be kept in line with averaged
results.
SpiderLightning: Making WebAssembly cloud applications portable

A key element of this extensibility is the WebAssembly Component Model.
Defined by the WebAssembly working group as the Wasm equivalent of an OS
process model, it’s the foundation for how WASI implements its interfaces. A
key element of any low-level approach like this is an interface definition
language, which provides a way to specify how interfaces interact with code.
For Wasm, and especially for the Component Model, the standard IDL is wit,
which gives us a concise and human-readable way of defining interfaces that
are expanded into WebAssembly code. To use WASI to build distributed
applications, we need a set of extensions that lets us abstract
provider-specific services as interfaces. Instead of having to use separate
APIs for S3 on AWS and Blob storage on Azure and the code to manage them, we
could have a single storage component that would provide a common set of
interfaces on all platforms, with the underlying WASI instance managing
service-specific implementations.
Attackers create 130K fake accounts to abuse limited-time cloud computing resources

Researchers refer to the abuse of free offers as freejacking, and the
creation of accounts that incur charges and then are never paid as "play
and run." The latter is more difficult to pull off because most service
providers require the user to register a valid credit card or payment
method before giving them access to paid-for computing resources. However,
even if usage is tracked and charged on a per-minute basis, the bill is
usually issued after a longer period. This gives attackers a time window
to abuse such services. ... "The infrastructure architecture employed by
the actors uses CI/CD techniques, in which each individual software
component of an operation is placed within a container," the researchers
said. "This container operates within a modular architecture within the
larger mining operation. CI/CD architectures provide highly modular
operational environments, allowing some components of an operation to
fail, be updated, or even be terminated and replaced, without affecting
the larger environment." Not all the containers are used for
cryptomining.
How to Get the Best Cyber-Insurance Deal

The first step in obtaining affordable cyber insurance is finding a broker
who is well-versed in coverage terms and has access to several different
insurance markets, says Mark Dobrow, a vice president in the insurance
brokerage division of Segal, a human resources and employee benefits
consulting firm. “Market knowledge and experience is limited due to the
relative newness of the product as compared to the long history of
standard property coverages,” he explains. “The right broker can tailor
the coverage to your needs and should know which markets are best for a
particular situation.” ... The biggest mistake cyber-insurance applicants
make, Aiello says, is paying poor attention to detail. “Businesses must
ensure technology is being deployed in line with the insurance firm's
conditions, otherwise insurers can attempt to get out of paying a claim if
the technology was not ‘properly implemented’,” he warns. Unfortunately,
the language used in cyber-insurance policies isn't always consistent
between providers.
Southwest Airlines: ‘Shameful’ Technical Debt Bites Back
It’s been an open secret within Southwest for some time … that the company
desperately needed to modernize its scheduling systems. … This problem —
relying on older or deficient software that needs updating — is known as
incurring technical debt [and it] appears to be a key factor in why
Southwest Airlines couldn’t return to business as usual the way other
airlines did after last [month’s] major winter storm. When hiccups or
weather events happen, the employees have to go through a burdensome,
arduous process … because Southwest hadn’t sufficiently modernized its
crew-scheduling systems. For example, if … their flight was
canceled … employees have had to manually call in to let the company know
where they are [sometimes] being left on hold on the phone for … hours
just to let the company know their whereabouts. … Online forums are full
of employee accounts of such misery. … This can easily cascade to a
systemwide halt. … Such breakdowns resulting from technical debt are often
triggered by external events, like weather. … So why didn’t Southwest
simply update its software and systems?
Top 3 trends experts predict to hit software development in 2023
While hackers are typically associated with cyberattacks, many of them
also have a “broad, practical skillset” that can make them useful for
parts of software development. That’s according to Alex Rice, the
co-founder and CTO of HackerOne, which connects businesses with
penetration testers and cybersecurity researchers. Rice believes that both
hackers and external code reviewers will become a more integrated part of
the software development processes in 2023, as more organisations adopt
security reviews into their development process. “As the value of
DevSecOps (development, security and operations) increases, we’ll see the
line between hackers and developers blurring as hackers with development
expertise become a core element of the software development processes,”
Rice said. “There’s a lot of value hackers can bring when it comes to
catching security risks earlier rather than later.” Earlier this year,
Irish start-up Noloco raised $1.4m in seed funding for its platform, which
lets companies build internal tools, portals and apps without writing a
line of code.
Blind Eagle APT Hunts Banking Victims in Colombia, Ecuador

Based on Trend Micro's report, the APT is traditionally known to leverage
publicly available remote access tools and Trojans such as njRAT, imminent
monitor, ProyectoRAT, Warzone RAT, Async RAT, Lime RAT, Remcos RAT and
BitRAT. Over time, the APT switches from one RAT to another. Continuing
that trend, Blind Eagle is now using a modified version of the QuasarRAT,
Check Point researchers say. The attack begins with phishing emails
containing a booby-trapped link that deploys a Trojan named Quasar RAT.
The APT used a geo-filter server in one campaign that redirects requests
made from outside of Ecuador and Colombia to the website of the Ecuadorian
Internal Revenue Service, suggesting the APT's targeting focus. The
campaign not only drops a RAT but also employs a more complex infection
chain. It abuses the legitimate mshta.exe binary to execute VBScript
embedded in an HTML file to ultimately download two Python scripts, which
adds a new stage in the infection chain. The first of the two, ByAV2.py,
is an in-memory loader that runs a Meterpreter payload in DLL format.
What is Cython? Python at the speed of C

Enter Cython. The Cython language is a superset of Python that compiles to
C. This yields performance boosts that can range from a few percent to
several orders of magnitude, depending on the task at hand. For work bound
by Python’s native object types, the speedups won’t be large. But for
numerical operations, or any operations not involving Python’s own
internals, the gains can be massive. ... Note that Cython’s approach is
incremental. That means a developer can begin with an existing Python
application, and speed it up by making spot changes to the code, rather
than rewriting the whole application. This approach dovetails with the
nature of software performance issues generally. In most programs, the
vast majority of CPU-intensive code is concentrated in a few hot spots—a
version of the Pareto principle, also known as the “80/20” rule. Thus,
most of the code in a Python application doesn’t need to be
performance-optimized, just a few critical pieces. You can incrementally
translate those hot spots into Cython to get the performance gains you
need where it matters most.
5 ways to improve security automation

One essential part of security automation that you'll likely want to
tackle before anything else is monitoring. If you don't know where your
issues are, you won't catch critical exposures in your environment and
won't know what to prioritize for automation. The bottom line is to
automate monitoring your environment, if you do nothing else. Even if you
don't have the time or budget to automate remediation, you can at least
target areas for manual fixes. There are many fantastic articles and
products around this space (including How we designed observability for a
hybrid cloud platform), from basic infrastructure monitoring to code
scanning to network vulnerability scanning and more. Another thing to keep
in mind is transition planning. You won't get all of this done at once,
nor should you. As you figure out what areas to target first and focus
your automation efforts accordingly, you will undoubtedly face challenges
rolling out your new standards and processes to your environment. If you
didn't set standards before, you'll be met with resistance from teams with
their own priorities and commitments to the business that don't understand
why you're trying to change things on them.
Quote for the day:
"Leaders are more powerful role
models when they learn than when they teach." --
Rosabeth Moss Kantor
No comments:
Post a Comment