Top network skills to succeed in a post-coronavirus world

"Cloud security is a huge topic moving forward," says James Stanger, chief
technology evangelist at CompTIA, a trade association for the global IT
industry. "To cut costs and increase resiliency and be more flexible, folks
are moving to the cloud. We're also seeing companies that aren't used to the
cloud be increasingly surprised at the lack of control" and loss of asset
visibility the cloud can bring. Companies are looking for individuals who know
how to create cost-effective but capable alternative business platforms,
Stanger says, in case a company's primary systems become unavailable or
impacted by a stay-at-home order or other event. The rise of the remote worker
has also led to greater demand for people with the skills to resolve network
access issues and optimize network connections. "If you have remote workers,
you need to make sure they have good bandwidth," Stanger says. "If you are
moving to the cloud, you need good QoS [quality of service] and bandwidth
control." For that matter, any skills that support the work-from-home model
will be in demand, says Jim Johnson, senior vice president for staffing firm
Robert Half Technology.
Ultimate guide to artificial intelligence in the enterprise
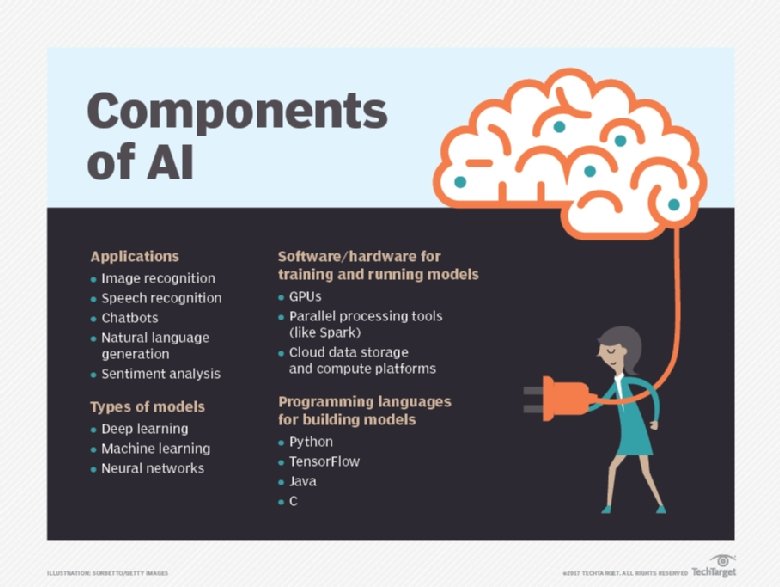
One of the biggest risks to the effective use of AI in the enterprise is
worker mistrust. Many employees fear and distrust AI or remain unconvinced of
its value in the workplace. Anxieties about job elimination are not unfounded,
according to many studies. A report from the Brookings Institute, "Automation
and Artificial Intelligence: How Machines Are Affecting People and Places,"
estimated that some 36 million jobs "face high exposure to automation" in the
next decade. The jobs most vulnerable to elimination are in office
administration, production, transportation and food preparation, but the study
found that by 2030, virtually every occupation will be affected to some degree
by AI-enabled automation. Of more immediate concern is the prevailing
skepticism about AI's value in the workplace: 42% of IT and business
executives surveyed do not "fully understand the AI benefits and use in the
workplace," according to Gartner's 2019 CIO Agenda survey. Fear of the unknown
accounts for some of this skepticism, the report stated, adding that business
and IT leaders must take on the challenge of quantifying the benefits of AI to
employees.
Canadian major telcos effectively lock Huawei out of 5G build

Canadian carriers Bell and Telus announced on Tuesday that each of them would
not be continuing the use of Huawei equipment in their respective 5G networks,
having signed deals with the Chinese giant's rivals instead. For Bell, it
announced Ericsson would be supplying its radio access network. It added that
it was looking to launch 5G services as the Canadian economy exited lockdown.
Bell, which in Febraury announced it had signed an agreement with Nokia, said
it was maintaining the use of multiple vendors in its upcoming network, as it
had for 4G. "Ericsson plays an important role in enabling Bell's award-winning
LTE network and we're pleased to grow our partnership into 5G mobile and fixed
wireless technology," said Bell chief technology officer Stephen Howe.
Meanwhile, the British Columbia-based Telus also chose to go with a
combination of Ericsson and Nokia. The company said it had spent CA$200
billion on its network since the turn of the century, and would part with a
further CA$40 billion over the next three years to deploy its 5G network. Both
Bell and Telus had previously used Huawei equipment in their networks.
Cloud Based Development - From Dream to Reality
Thanks to the internet, software as a service solutions quickly brought a significant shift to a software team's daily routine. What used to be done manually and offline can now be performed more efficiently online, with real-time collaboration and quick, in-the-moment feedback loops. Nowadays, it is common for the requirements, design, test and maintenance stages of the SDLC to be performed in the cloud. Whether a business migrates to the cloud or is born in the cloud, a so-called cloud-native business, the trend is crystal clear: The cloud is here to stay and the SDLC too adopts this innovation. Except for the Implementation stage... Have you ever looked at a pull request, said to yourself "This looks good" and left a LGTM comment, without actually testing the code? Right, you have - we all have. Gitpod comes with a built-in code review feature that lets you review changes and leave comments inline. For even better productivity, you can configure Gitpod to add a PR comment with a link to a workspace that contains this exact pull request's code changes. Your workflow as a reviewer now is: Open PR; click link; review & test code.Capital One ordered to disclose third-party analysis of 2019 breach

Capital One's security flaw was rooted in a misconfigured web application
firewall, similar to the flaw compromised in Equifax's 2017 breach. The WAF
misconfiguration led to criticism around the company's reliance on Amazon Web
Services' security. The bank hired Mandiant in 2015 to perform "engagement
activities, results and recommendations for remediation" in the event of a
cyber incident, according to the court document. The bank updated their
agreement in January 2019 to 285 hours of service. Capital One extended its
services "out of the retainer already provided to Mandiant under the Jan. 7,
2019, [statement of work]," according to the court document. But when the
retainer was "exhausted," Capital One paid Mandiant using its cyber
organization's funds. By December, the bank's legal department took on
Mandiant's payments, redesignating the service's costs as legal
fees. While Capital One said Mandiant's report was confidential, the bank
said it disclosed it to about 50 Capital One employees, four regulators and
the accounting firm Ernst & Young. The bank does not state why, for
business or legal purposes.
Internet pioneer Leonard Kleinrock on the great experiment we’re living through
Some mix of work at home will undoubtedly remain. And some jobs that used to be necessary are now being seen to be not necessary. Businesses are saying, "Gee, I didn't need that functionality anyway. We can get it either by AI or by some other automated way". And entertainment, you know, do I really want to go to the movie theater? Well… versus Netflix or whatever? We're never going to get back to where we were. In engineering, there's a term called hysteresis. We're in such a situation now, where we've stretched the system in one direction. If we relax now, it's not going to come back to where it was. It's going to have memory of what went on. It certainly applies to medicine, to social interactions, etc. So, I find that very exciting. It is exploring things we couldn't have, and we're finding advantages of those things. Economically, it's a very serious issue here, what's happened and how we come back. Supply chains are being broken. How they get restructured is not clear. There are opportunities out there now for new products and services based on the fact that we are less in physical contact, more remote.How to balance trust and technology in banking

The implementation of AI and machine learning to analyse and use data has
helped financial services companies both internally – the ability to monitor
account activity, complete multiple tasks at greater speed, and more
effectively, combat fraudulent activities, and so on – and externally; and
data is proving to be the framework for the provision of greater user
experience and the managing of trust and relationships. A common perspective
in this forward-looking narrative is that banks – incumbents or ‘traditional’
in particular – face a significant challenge when it comes to developing and
implementing such technologies compared to those more innovative fintech
market entrants or the tech giants. However, in a report published last year
exploring what the next decade holds for incumbents in the age of digital
banking, HSBC suggested that this is a “common myth”, highlighting the growing
landscape for collaboration between banks and fintechs and suggesting that “we
are already in an era of innovative cross business collaboration which many
would have not imagined a few years ago”.
How are FinTech innovation and AI disrupting traditional banking models in the ME?
The surge in demand for online banking services during the pandemic has spiked the need for fintech firms to incorporate fresh, innovative technology to meet the changing needs of customers. To meet this demand, the key sources of fintech innovation in the coming months and years is likely to be blockchain, open banking, cloud-based systems and, most importantly, AI. With increased government support in the form of stimulus packages due to COVID-19 and start-up funding, alongside customer demand, these technological innovations are set to disrupt traditional banking models - completely transforming the way we manage our finances both during and after the pandemic. At the heart of fintech innovation lie consumers. The increasingly tech-savvy, digitally minded population in the gulf region has pushed fintech firms to provide consumers with a personalised and seamless online banking experience. To achieve this, fintech firms have focused on implementing technological innovations that promise faster, cheaper, customer-centric banking services.14 tips for CIOs managing shadow IT activities

Considering how complex IT has become, particularly in the age of the
internet, the ability to know about and effectively manage IT resources --
both internal and external -- has become increasingly important. Here, we
examine situations to be aware of regarding shadow IT and offer guidance to
ensure that CIOs can identify and mitigate rogue activities. The primary goal
for most CIOs is a smooth-running IT organization that is compliant, secure
and risk-free. On the issue of security, they pay attention to any situation
that threatens the confidentiality, integrity and availability of information.
Non-approved installation of systems, whether on site or via cloud technology,
presents possible unauthorized access to internal systems. From a risk
management perspective, shadow IT presents unique challenges to CIOs and their
cybersecurity and operations teams and should be a key element in those
activities. The growth of cloud-based systems using software as a service
(SaaS), infrastructure as a service (IaaS) and platform as a service (PaaS)
represents significant opportunities for shadow IT activities.
AI adoption – Don’t leave data governance behind
Data is the driver for AI and digital transformation. Yet time and time again,
we see instances where it is not leveraged in a way that reflects its value.
Of course, it is never as easy as we want – data governance and conditioning
take time and resources. However, it must be viewed in terms of the benefits
it will bring: observability, reproducibility, efficiency and transparency.
With AI now very much a part of business function and only set to increase in
reach and take-up, the enterprise must react accordingly. In understanding the
main challenges and obstacles to AI adoption, companies can proactively look
to tackle them. Moreover, for companies yet to begin their AI journey, prior
knowledge of challenges will allow them to prepare and plan. Addressing
company culture and practices early on makes a big difference down the line.
Many have had to learn the hard way, so businesses should take heed when they
can. It is essential that data governance procedures are given the
careful consideration they require and that – as much as possible – companies
avoid viewing them as an addendum tacked on to digital transformation plans.
Quote for the day:
No comments:
Post a Comment