Despite rise in security awareness, employees’ poor security habits are getting worse
Efforts to get around IT may not necessarily be done with malicious intent, but the reality is they directly increase IT risk for the organization. For example, 13% of employees admitted they would not immediately notify their IT department if they thought they had been hacked. Further compounding this issue is a workforce that tends not to understand the role of all employees in keeping an organization secure, as 49% of respondents would actually blame the IT department for a cyberattack if one occurred as a result of an employee being hacked. However, it’s not just today’s employees exposing organizations to risk. As the digital transformation blurs the traditional security perimeter with cloud apps, it is also redefining the definition of a “user.” Enterprises are increasingly adopting software bots powered by robotic process automation (RPA), and granting them access to mission-critical applications and data, like their human counterparts.
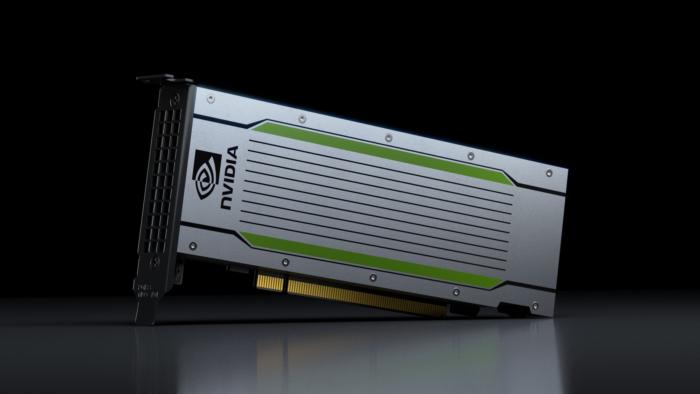
A side-channel attack is one where the attacker uses how a technology operates, in this case a GPU, rather than a bug or flaw in the code. It takes advantage of how the processor is designed and exploits it in ways the designers hadn’t thought of. In this case, it exploits the user counters in the GPU, which are used for performance tracking and are available in user mode, so anyone has access to them. 3 types of GPU attacks All three attacks require the victim to download a malicious program to spy on the victim’s computer. The first attack tracks user activity on the web, since GPUs are used to render graphics in browsers. A malicious app uses OpenGL to create a spy program to infer the behavior of the browser as it uses the GPU. The spy program can reliably obtain all allocation events of each website visited to see what the user has been doing on the web and possibly extract login credentials. In the second attack, the authors extracted user passwords because the GPU is used to render the login/password box. Monitoring the memory allocation events leaked allowed for keystroke logging.
Defences based on Lockheed Martin’s cyber kill chain were mainly aimed at preventing reconnaissance, weaponising, delivery and exploitation, said Tolbert, with detection and response only required at the malware installation, callback and execution phases of the kill chain. While this is still a valid approach, he said the Mitre framework was more up to date and more realistic, with prevention mentioned only in connection with the initial access and execution phases, while detection and response is specified with regard to the eight other phases, including privilege escalation, credential theft, lateral movement and exfiltration. “These frameworks are useful in helping organisations to plan where they need to do work, and while prevention always will be important, there has been a shift in emphasis to detection and response. We believe artificial intelligence and machine learning [ML] can help in making this shift,” said Tolbert.
Managing Change in the Face of Skepticism
To be sure, skepticism can play a positive role in organizations. It helps companies make better decisions. It can build tight trading algorithms and sturdy satellites. Doubting hockey-stick growth and suspicious data helps companies make better capital allocation choices. When skepticism is constructive, it can be leveraged to evaluate a change effort’s benefits, and build employee enthusiasm for it. Cynicism is a different matter. It often stems from a history of failed programs or lack of management credibility. Cynicism breeds distrust and pessimism, so if it is present, transformation efforts must restore credibility before moving to the next step of the plan. Regardless of an organization’s culture, business leaders should avoid strong-arming change — recent failed transformation efforts have shown the pitfalls of that approach. When leading a transformation in a skeptical culture, look within and leverage the skepticism to move forward.
Why the Artificial Intelligence Era Requires New Approaches to Create AI Talent

With the horizons dictating artificial technology expected to broaden in the future, one can tell that AI talent will have an imperative role to play in company performance. The talent that a company possesses in the field of AI dictates how well they’re able to manage the analytics for the future. The best AI talent in the market will realize the performance of different models and harness their potential to help them perform at their full potential. This knowledge is what AI companies will crave in the future. As the age of AI kicks in, the management philosophy will also change. While previously managements were involved in routine decision making and innovations, the AI age will define how organizations now rely more on their top talent to define and lead innovation. The innovation that the workforce inside an organization brings would be the differentiating factor for all forms of AI companies. Their workers would help propel them forward and foster innovation for them.
Mastering data governance initiatives in the age of IIoT
Most IIoT gadgets both send and receive information about processes that occur within the scope of the businesses that use them. However, concerning distributed data, companies must ensure it doesn't reveal information to recipients that could highlight trade secrets. For example, many IIoT sensors track various actions that happen in assembly lines. If recipients can extract details from information that tells them how companies go about making their products and what helps them stand out, businesses will discover their operations are not sufficiently locked down from outside parties. While some of those entities might not seek gain from the information, others may try to mimic certain practices. When that happens, the increased competitiveness mentioned above becomes less prominent and may no longer be relevant at all. However, keeping sensitive information secret is not straightforward. That's because it takes substantial forethought to figure out how to spend money on IIoT equipment that works seamlessly together.
How to Prevent Data Leaks in a Collaborative World

MyWorkDrive is a secure data access and collaboration solution. It does not require the organization to copy all its data to a cloud provider, and it does not require users to access data via VPN. Data is shared and collaborated on in place. The customer installs the MyWorkDrive server software on a server within their environment. IT then points the MyWorkDrive server to the existing fileserver mount points to which it wants to allow access. The solution moves no data in the process. Users can directly access data through the MyWorkDrive WebClient, native desktop client, iOS or Android app. The software initially presents shared files in a browser window. MyWorkDrive administrators designate the actions users can take on those shared files. The administrator can remove the ability to download the file, to copy data to the clipboard and to take screenshots. The administrator can also watermark the files which should discourage a user from taking a picture of the screen with a smartphone.
Why cryptojacking malware is a bigger threat to your PC than you realise
That's because cryptocurrency miners give attackers a foothold into PCs which can be exploited to deliver more damaging malware in future, security firm Fortinet has warned in its latest threat landscape report - noting that underestimating cryptojacking places organisations under heightened risk. "What we're finding out is that this particular malware also has other nefarious activities that it does while it's mining for cryptocurrency," Anthony Giandomenico, senior security researcher at Fortinet's FortiGuard Labs told ZDNet. "It will disable your antivirus, open up different ports to reach out to command and control infrastructure, it can download other malware. Basically, it's reducing or limiting your security shields, opening you up to lots more different types of attacks". A number of examples of cryptocurrency miners packing an additional punch have already been spotted in the wild: PowerGhost alters how systems perform scans and updates, while also disabling Windows Defender.
Did IBM overhype Watson Health's AI promise?

While IBM faces declining revenue overall, and its recently released third-quarter earnings showed revenue from cognitive offerings was down 6% from last year, Watson Health saw growth, according to Barbini. He noted that IBM does not release numbers specific to Watson Health for "competitive reasons." Barbini admitted that developing Watson Health and, specifically, Watson for Oncology is not an easy task, but it remains an important one. "That's why IBM dove into it three years ago. Did you really think oncology would be mastered in three years?" Barbini said. "However, let's look at the facts. More than 230 hospitals are using one of our oncology tools. We've had 11 [software] updates over last year and half and we've doubled the number of patients we've reached to over 100,000 as of the end of the third quarter of this year." Earlier this month, the head of Watson Health for the past three years, Deborah DiSanzo, stepped down and Kelly took over. DiSanzo is continuing to work with IBM Cognitive Solutions' strategy team, according to a company spokesperson.
Cisco fuses SD-WAN, security and cloud services

What Cisco is doing is adding support for its Umbrella security system to its SD-WAN software which runs on top of the IOS XE operating system that powers its core branch, campus and enterprise routers and switches. Cisco describes Umbrella as a cloud-delivered secure internet gateway, that stops current and emergent threats over all ports and protocols. It blocks access to malicious domains, URLs, IPs, and files before a connection is ever established or a file downloaded. It basically protects customers and communications at the Domain Name Server (DNS) layer. Umbrella’s key features come from OpenDNS which Cisco bought for $635 million in 2015. OpenDNS offers a cloud service that prevents customers from connecting to dangerous internet IP addresses such as those known to be associated with criminal activity, botnets, and malicious downloads. “Umbrella blocks access to malicious destinations before a connection is ever established, and it is backed by the threat intelligence of Cisco Talos,” Prabagaran said.
Quote for the day:
"If you find a path with no obstacles, it probably doesn't lead anywhere." -- Frank A Clark


No comments:
Post a Comment