
Every technological advance can and will be exploited at some point, but if we think before we quickly push devices out into consumer’s and corporation’s hands – if we build security and privacy in to start with – we’ll have a better handle on what can go wrong. Take medical devices, for instance. Per a recent study by Trend Micro, more than 100,000 medical devices were discovered to be insecure. Think of an infusion pump precisely monitoring the flow of a lifesaving fluid into your loved one. Don’t think it can be hacked and the dosage changed? Think it doesn’t happen? The HIPAA journal recently featured a study done by Vanderbilt University that suggested healthcare data breaches cause 2,100 deaths a year. Was this IoT related? I don’t know, but the evidence of what can happen with unmanaged, unsecure IoT is powerful and must be addressed. So, where to now? Want to learn more about IoT? It really applies to everything: medicine, health, transportation, smart cities and smart homes.
How to add IoT functions to legacy equipment
The hardest part of bringing the IoT to older systems seems to be dealing with the unique, one-off characteristics of each legacy situation — often without accurate documentation. “Older equipment sometimes requires a necessary, unique design step in each individual case,” Flynn says. The key, he adds, is to avoid disrupting the existing control scheme and operations of the legacy system. “We have to be careful not to create new issues. If the legacy system uses an older communication protocol, then we have to ensure not to overload any bandwidth or processor,” he says. If that’s not possible, using new IoT sensors requires selecting the right new IoT sensors and instrumentation to solve a particular problem. That, in turn, requires a higher level of operational technology expertise. But that’s only part one, Flynn says. You still have to network into an existing IT infrastructure, often using a combination of edge devices and sensors. New Wi-Fi connections may be needed.
Elastic tackles containers and APM in the new 6.5 release

As Elastic adds capabilities for supporting the new forms of deployments, largely cloud-native, involving containers and serverless infrastructure, another theme of the new release is going higher up the stack and ramping up competition with, as opposed to complementing, APM vendors. The new release of Elastic APM allows users to correlate data on application performance with infrastructure logs, server metrics, and security events to identify bottlenecks. In itself, this capability overlaps those of APM vendors. APM vendors have built their IP over the years understanding how to abstract low level log readings from the standpoint of application processes making their way through IT infrastructure. A major difference form Elastic is that the APM crowd built their expertise in the walled gardens of data center deployments. By contrast, Elastic was not necessarily engineered for the cloud, but its scale-out, big data architecture made it a natural for the cloud.
Terraform orchestration matures as multi-cloud lingua franca
Terraform 0.12 makes remote state storage available free to users of the open source edition as well. Without this feature, multiple IT administrators might overwrite one another's infrastructure code or lack a single "source of truth" for infrastructure configurations. With 0.12, HashiCorp established a SaaS remote state management product for open source users that can indefinitely store an unlimited amount of state information. Terraform 0.12 also revamps the HashiCorp Configuration Language (HCL), its domain-specific language for infrastructure code, to make it more consistent and easy to use. Enterprise IT shops already favor Terraform orchestration for multi-cloud microservices management but said there was a time when ease of use was an issue. "Terraform has been instrumental for us to tame the chaos of multiple clouds and data centers," said Zack Angelo, director of platform engineering at BigCommerce, an e-commerce company based in Austin, Texas. "But in the past, if you weren't on Terraform Enterprise, migrating a state file was a pain point ..."
Global Family Business Survey 2018
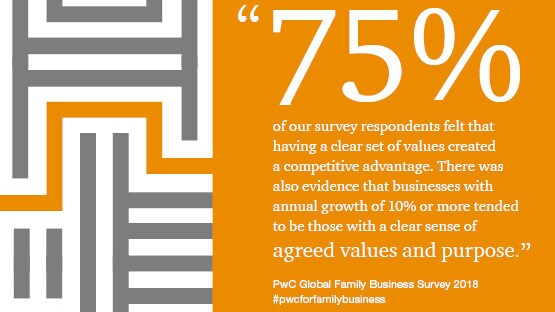
The release of our ninth PwC Global Family Business Survey comes at a time of extraordinary transformation. Digital technology is disrupting whole industries; sustainability is becoming central to the conduct of business; in the corporate and financial worlds, winning trust is more important than it’s ever been; and millennials represent an enduring demographic change. After surveying nearly 3,000 family businesses across 53 territories, we were able to prove that family businesses - built around strong values and with an aspirational purpose - have a competitive advantage in disruptive times, that pay off in real terms. Therefore we believe there is an enormous opportunity for family businesses to start generating real gains from their values and purpose by adopting an active approach that turns these into their most valuable asset.
How Kubernetes is becoming a platform for AI
Xinglang Wang, a principal engineer at eBay, said AI had a high barrier to entry, but packaging tools in a Kubernetes cluster made it easier for businesses to get started on an AI project. At eBay, he said Kubernetes was used to create a unified AI platform, which enables data sharing and sharing of AI models. The AI platform also provides automation to enable eBay to train and deploy AI models. One of the big users at the KubeCon Shanghai event was Chinese e-commerce retailer JD.com. Explaining the use of AI at JD.com, principal architect Yuan Chen described how the the company was running one of the largest Kubernetes clusters in the world. While it was traditionally used to support a microservices architecture, he said: “Everything is now driven by AI, so we have to use Kubernetes for AI. It is the right infrastructure for deep learning to train the AI models. AI scientists are expensive, so they should focus on their algorithms and not have to worry about deploying containers.”
The Linux desktop: With great success comes great failure

First, while the major Linux companies — Canonical, Red Hat and SUSE — all support Linux desktops, they all decided early on that the big money was to be made with servers (and nowadays with containers and the cloud). The biggest Linux players determined that the Linux desktop was a small market — and then they did very little to change that. But there’s more to it than that. The Linux desktop has also been plagued by fragmentation. There is no one Linux desktop; there are dozens, and they are not at all alike. There’s the Debian Linux family, which includes Ubuntu and Mint; the Red Hat team, with Fedora and CentOS; Arch Linux;Manjaro Linux; and numerous others. And then there are the desktop interfaces. Personally, as a dedicated Linux desktop user for decades, I love that I have a choice between GNOME, KDE Plasma, Cinnamon, Xfce, MATE, etc. for my desktop interface. But most people just find it confusing. All of that just scratches the surface.
GPS killer? Quantum 'compass' promises satellite-free navigation

The transportable quantum accelerator could address GPS's dependence on satellite signals, which can be jammed or spoofed by an attacker, rendering the system useless for navigational information. Instead of using GPS, scientists from Imperial College London and UK laser instrument maker M Squared have demonstrated a way to measure how super-cooled atoms respond when inside an accelerating vehicle. Accelerometers are used for navigation, but as the researchers explain, they quickly lose accuracy over time unless aided by satellite signals. The satellite-free navigational device they created relies on M Squared's laser, which cools atoms in a chamber to the point where they behave in a quantum way, as both matter and waves. When a vehicle carrying the device moves, the wave properties of the cooled atoms are affected by its acceleration. A laser beam that acts as an 'optical ruler' measures how atoms move over time.
Zero-trust security not an off-the-shelf product

Zero trust is a “business enabler” because, done correctly, it enables businesses to be faster more quickly and more securely because it is a combination of processes and technologies, he said. “Security is improved because it effectively blocks lateral movement within organisations.” It is widely recognised that complexity is the enemy of security because it encourages end-users and business leaders to bypass security, said Simmonds. “The zero-trust model once again improves security by reducing complexity, and if you get it right, it works for everyone, including business partners, by providing a unified experience with greater flexibility and productivity,” he said. On the other hand, zero trust is not about trusting no one, said Simmonds, it is not a “next-generation perimeter” and it is not “VPN modernisation”. “It is not an off-the-shelf product,” he said.
Understanding the CEO’s role early in digital transformation programs

First, the CEO should be marketing the mission. It must be repeated to leaders and employees several times and the CEO should help answer several key questions. Why must the organization pursue the defined digital business strategy? What are the issues with the existing business model? Who are the new competitors that are disrupting existing businesses, products, and services? What markets is the organization targeting? What are the new and emerging customer needs and expectations? Why technology is critical for future success? These communications should always end with some of the short-term goals of the program and how people can participate. The CIO and others on the leadership team also be communicating and answering these questions, but the staff wants to know and see that the CEO is truly behind it and driving it. With a strategy and mission defined, their needs to be clarity on how the program is being led and how responsibilities are aligned.
Quote for the day:
"A leader must have the courage to act against an expert's advice." -- James Callaghan
No comments:
Post a Comment