
“Recruiters often write things like, ‘Must have a technical degree, three years of experience, and deep knowledge of Apache Hadoop.’ This is a mistake, even if you really want someone with these attributes,” Bartram says. “For a high-skill role like data science, the goal is to convince applicants who might be on the fence that your company and your role are interesting and worth their time.” This is especially important not just because the market is so hot, but because, Nicholson says, “A lot of the necessary skills are industry- and company-specific. Organizations use different languages, prefer certain vendors’ tech stacks and specific proprietary tools, so that is up to the hiring teams to know which ones.” Instead focus on the mission of your company, what the role will accomplish, and any technical details of the exciting problems candidates will get to solve, Bartram says. “For data science in particular, it can work great to write about the interesting data sets that the candidate will have access to — data science candidates love to geek out over cool data sets,” he says.
Wexflow: Open source workflow engine in C#
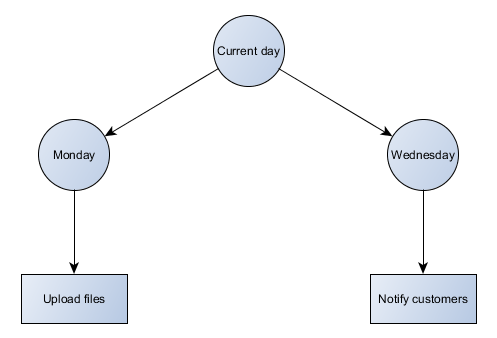
Wexflow is a high performance and extensible workflow engine with a cross-platform manager and designer. The goal of Wexflow is to automate recurring tasks without user intervention. With the help of Wexflow, building automation and workflow processes become easy. Wexflow also helps in making the long-running processes straightforward. Wexflow aims to make automations, workflow processes, long-running processes and interactions between systems, applications and folks easy, straightforward and clean. The communication between systems or applications becomes easy through this powerful workflow engine. Wexflow makes use of Quartz.NET open source job scheduling system that is used in large scale entreprise systems. Thus, Wexflow offers felixibility in planning workflow jobs such as cron workflows. ... Wexflow provides a GUI for managing workflows that can be installed on a Linux system. To run Wexflow on Linux, Wexflow server must be installed on a Windows machine. Wexflow provides a self hosted web service that allows to query Wexflow Engine.
Understanding mass data fragmentation

For most companies, data isn’t the fuel that powers digital transformation — it’s the biggest obstacle because of something I’m calling mass data fragmentation (MDF), which is a technical way of saying that data is currently scattered all over the place and unstructured, leading to an incomplete view of data. Data is fragmented across silos, within silos and across locations. Adding to the problem is that most companies have multiple copies of the same data. Some data managers have told me that about two-thirds of their secondary storage is comprised of copies, but no one knows which copies can be kept or deleted, forcing them to keep everything. If bad data leads to bad insights, then fragmented data will lead to fragmented insights, which can lead to bad business decisions. Digital natives such as Amazon and Google are data-centric and architected their infrastructure to avoid the MDF issue. This is why those businesses are agile, nimble and always seem to be at the forefront of market transitions. They have access to a larger set of quality data and are able to gain insights that other companies can’t.
Three keys to a cybersecurity culture that will stick
When it comes to cybersecurity, though, businesses are faced with a classic conundrum: How much money and resources should be spent on something that hasn’t – and may never have – happened? It’s easy to blame your employees for being susceptible to spear phishing attempts, but if they weren’t given proper training to spot them, then the fault lies elsewhere. And that’s just the tip of the iceberg. According to a recent ISACA/CMMI survey on cybersecurity culture, more than 70 percent of companies have specific policies in place for password management, automated device updates and device security, as well as employee training and proper communication workflows in place. However, only 40 percent of respondents say that their organizations’ efforts to create a culture of cybersecurity with substantial employee buy-in have been more than moderately successful. ... The most common support request at that time was for us to allow people to use their old passwords again – because people didn’t want to have to come up with a new one for each site they log into.
Cyber security – why you’re doing it all wrong

Let’s start with strategy – the overarching mission. How many organisations have such a thing? A few. How many are built through business engagement? Even fewer. Security strategy is generally written from a position of prejudice and as a means of gaining budget to mature the organisation’s posture. For a strategy to be sound, it should be preceded by a warts-and-all look at the effectiveness and maturity of the as-is position and a clear line of sight of where it needs to get to. This requires a deep understanding of the business within which security operates, alongside measuring the effects of the myriad security jigsaw pieces across the organisation. This almost never happens. If it did, security teams would recognise that investment needs to be made primarily and almost solely on fixing the crap that is already there. How can this be? Well, let’s go through some of the jigsaw pieces that just about every organisation will have in its security picture.
Software and beer: What open source and craft brewing have in common

Just as IBM and Microsoft want to cash in on the mainstreaming of open source, global giants of the beer industry want to tap into the hottest growth segment of their market. Not surprisingly, there has been significant consolidation over the past few years. But if you look at a bottle or can or go on the website of Ballast Point, you won't see any mention of the company being part of the Constellation Brands empire. Nor will you see that Goose Island is one of 100+ bands owned by ABInBev. The craft brewing industry has its fair share of angst about whether brewers that are no longer independent realty fit the category. There's a lot of concern that the power of global giants will push distributors away from independent brands. In the same way, were GitHub or Red Hat to be viewed as captive subsidiaries of Microsoft and IBM, much of their value proposition would evaporate. It could lead to forking, such as what happened with MySQLafter Oracle acquired its parent, Sun Microsystems. Admittedly, the IBM/Red Hat Deal has another value proposition for IBM that drove it to pay roughly a third of its market cap that went beyond the pure open source angle: the inclusion of OpenShift, that could make IBM, a distant challenger in the public cloud
While phishing campaigns traditionally are synonymous with email, social media is also a popular medium for using fraudulent information and lures to convince victims to click on a link to input credentials or download malware-embedded files. These attacks can be very targeted, such as Iranian-linked Cobalt Gypsy, which has created fake personas to connect with individuals in the Middle East and United States. Once the connections are made, over time, individuals are convinced to download malicious files onto corporate computers. These kinds of social media-enabled attacks have doubled in the last year, and are proving an effective way to steal financial information and credentials, or to deploy malware. Given the limited resources required and the potential for high returns, nation-state tactics are diffusing out to criminal groups as well. Today’s criminal phishing campaigns are much more sophisticated than the scams of yesteryear
Outsourcing, like most business technology processes, benefits from human input to provide insight and context, which will help SMEs to see real value in a managed service contract. This requires the right forums to be in place, such as a monthly service report reinforced by regular meetings. These might look at issues such as whether SLAs have been set correctly. On paper, the outsource provider may not be meeting some of them, but open, face-to-face discussions bring an understanding of why this is the case. A four-hour SLA to set up a new user may not be achievable for complicated roles that require complex access rights, for example. Appropriate communications resolve this, rather than leave a series of SLA red flags. SMEs are often faced with situations where everything is a priority, such as client relationships, IT, human resources (HR) and marketing. Therefore, it can make more sense to consider a more advisory or consultative IT security service to help senior management to understand what is important for their organisation, and to gain an external perspective on what good looks like.
Careful planning is key to mitigate the risks of moving to the cloud
There is no "one size fits all" set of methods to manage risks in the cloud. The risks are unique to each environment and use case. When your organization has a specific use case, your team can build controls around it. Develop your own cloud control framework based on those identified security risks. Consider current applicable regulations as you do—including SOX, PCI, PII and GDPR. For guidance, look at previous risk models and at best practices on cloud risks. Be alert to control overlap when developing your framework to avoid multiple controls addressing the same risk. Leverage your cloud service provider and internal risk/security experts to mitigate these risks as part of your overall migration plan. Finally, never underestimate the value of identifying your risks, or the time it will take to do it right. Cloud service providers, such as Amazon Web Services, take a "building blocks" approach by providing tools that can help you gain compliance in the cloud, but they do not manage compliance directly. Furthermore, the same cloud service providers make it exceedingly simple for individual teams to begin their migrations independent from the organization.
21% of all files in the cloud contain sensitive data

Cloud services bring a momentous opportunity to accelerate business through their ability to quickly scale, allowing businesses to be agile with their resources and provide new opportunities for collaboration. Cloud services like Box and productivity suites like Office 365 are used to increase the fluidity and effectiveness of collaboration. However, collaboration means sharing, and uncontrolled sharing can expose sensitive data. ... To secure sensitive data in cloud storage, file-sharing and collaboration applications, organizations must first understand which cloud services are in use, hold their sensitive data, and how that data is being shared and with whom. Once organizations have gained this visibility, they can then enforce appropriate security policies to prohibit highly sensitive data from being stored in unapproved cloud services and provide guardrails that prevent noncompliant sharing of sensitive data from approved cloud services, such as when data is shared with personal email addresses or through an open, public link.
Quote for the day:
"Your first and foremost job as a leader is to take charge of your own energy and then help to orchestrate the energy of those around you." -- Peter F. Drucker


No comments:
Post a Comment