Use the AI S-curve to drive meaningful technological change

The S-curve is a graphical representation of how technology matures over time.
It starts slowly, with early adopters, specialized use cases, and technocrats.
As the technology proves its value, it enters a phase of rapid growth where
adoption accelerates and becomes more widely integrated into various industries
and applications. However, as technology advances, becoming cheaper, faster, and
more efficient, it inevitably reaches some logical limit and settles into a
natural “top” of the S-curve. When a technology reaches its limit, progress is
relatively slow, typically requiring significant increases in complexity. ... As
new technologies like AI emerge and mature, organizations must balance the need
to stay competitive with the potential risks and uncertainties associated with
early adoption. This challenge is not new. In his book, The Innovator’s Dilemma,
Clayton Christensen describes the difficult choice companies face between
maintaining their existing, profitable business models and investing in new,
potentially disruptive technologies. So, how can organizations navigate this
decision? One approach is to ensure that there is a dedicated unit that operates
on a long takt time, outside the quarterly or annual reporting
pressure.
How to Present the Case for a Larger IT Budget

Outright rejection of a budget expansion request is unlikely, but not
impossible. "The important thing is not to take rejection personally -- it's the
case that's rejected, not the person who presented it," Biswas says. It's also
important to understand that the rejection is not necessarily wrong. "Sometimes,
we get too close to our ideas to evaluate them impartially," he explains.
Understand, too, that a rejection isn't necessarily forever, since issues that
prevented approval can be addressed and resolved to present a more convincing
case. It's important to fully understand stakeholders' individual interests as
well as their tactical and strategic goals, Hachmann advises. "This approach
requires a strong understanding of the respective priorities of each person
involved in the budget approval processes." he says. "With this [tactic], you'll
be better equipped to align IT initiatives and their costs with the
stakeholders' business strategy." IT leaders often make the mistake of
generalizing on how a bigger budget will improve IT instead of communicating the
ways it will help the business. "IT leaders should be careful they're not
perceived as 'empire builders' instead of business leaders who want what's best
for the larger organization," Biswas says.
Beyond Orchestration: A Comprehensive Approach to IaC Strategy

In large organizations, enforcing a single IaC tool across all departments is
often impractical. Today, there are a diversity of tools that cater to different
stacks, strengths and collaboration with developers — from those that are native
to a specific platform (CloudFormation or ARM for Azure), and those for
multicloud or cloud native, from Terraform and OpenTofu, to Helm and Crossplane,
and those that cater to developers like Pulumi or AWS Cloud Development Kit
(CDK). Different teams may prefer different tools based on their expertise, use
cases or specific project requirements. A robust IaC strategy must account
for:The coexistence of multiple IaC tools within the organization. Visibility
across various IaC implementations. Governance and compliance across diverse IaC
ecosystems. Ignoring this multi-IaC reality can lead to silos, reduced
visibility and governance challenges. ... As DevOps and platform engineers,
we’ve developed a platform that we ourselves have needed over many years of
managing cloud fleets at scale. A platform that addresses not just tooling and
orchestration, but all aspects of a comprehensive IaC strategy can be the
difference between 2 a.m. downtime and a good night’s sleep.
DevSecOps Needs Are Shifting in the Cloud-Native Era
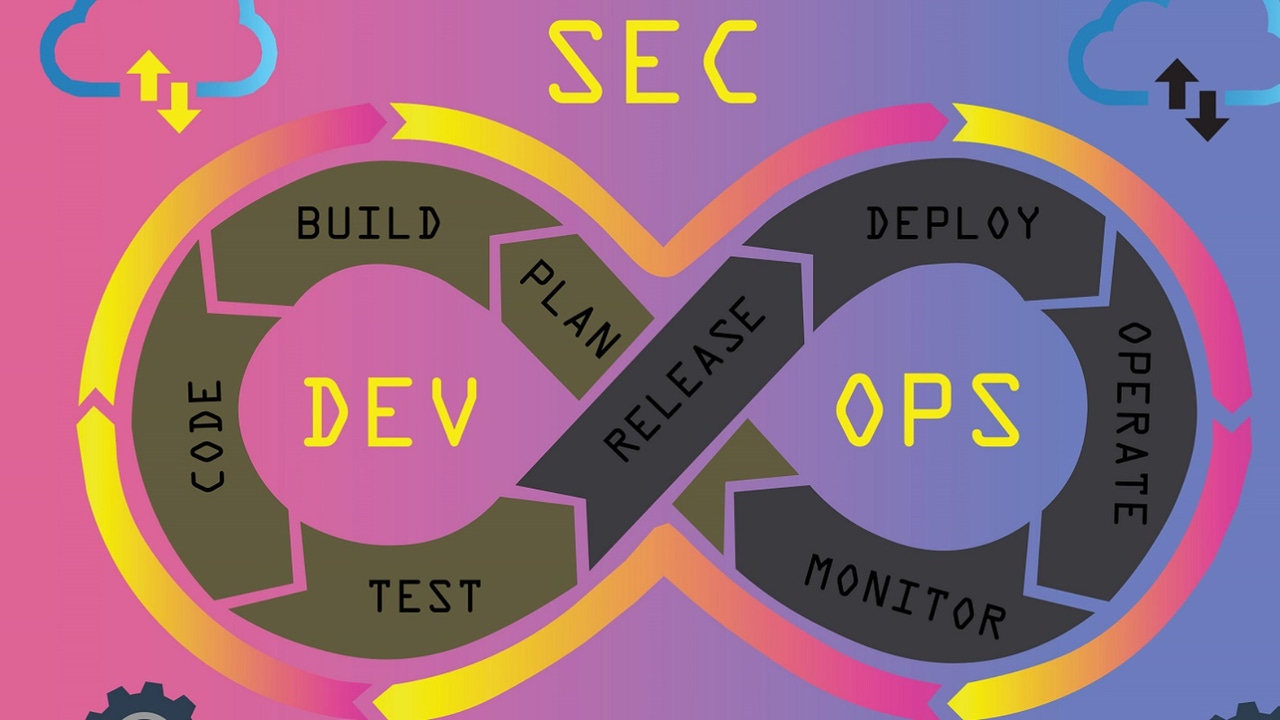
A cornerstone activity for any DevSecOps team is to secure secrets — that is,
the passwords and access credentials that allow access to services and
applications. Marks noted that despite many respondents having tools in place
for secret scanning or detection, the highest number of incidents (32%) were
from secrets stolen from a repository. The study also included data on frequency
of usage of tools. She said that it showed that scanning takes place
periodically, including daily, multiple times per week, or weekly, but this was
not aligned with code pushes or development processes. "So, this is an area for
much improvement as scanning takes resources and time and should align better
with developer workflows," Marks said. ... Having so many tools can
introduce such challenges as gaining consistency across development teams,
dealing with alert fatigue, or determining which remediations are needed and/or how remediation can mitigate risk. ... "Instead, a third-party platform that can support multiple tools can serve as a governance layer to help orchestrate the usage of needed tools, collect data, and help security teams more efficiently gain the visibility they need, apply the right controls and processes, and determine needed actions."
Exclusive: How Piramidal is using AI to decode the human brain

The company is first fine-tuning its model for the neuro ICU; that product will
be able to ingest EEG data and interpret in near-real time, providing outputs to
medical staff on occurrence and diagnosis of disorders such as seizures,
traumatic brain bleeding, inflammations and other brain dysfunctions. “It is
truly an assistant to the doctor,” said Pahuja, noting that the model can
ideally help provide quicker and more accurate diagnoses that can save doctors’
time and get patients the care they need much more quickly. “Brainwaves are
central to neurology diagnosis,” Piramidal co-founder and CEO Dimitris
Sakellariou, who holds a PhD in neuroscience, told VentureBeat. By automating
analysis and enhancing understanding through large models, personalized
treatment can be revolutionized and diseases can be predicted earlier in their
progression, he noted. And, as wireless EEG sensors become more mainstream,
models like Piramidal’s can enable the creation of personalized agents that
“continuously measure and monitor brain health.” “These agents will offer
real-time insights into how patients respond to new treatments and how their
conditions may evolve,” said Sakellariou.
What is ‘model collapse’? An expert explains the rumours about an impending AI doom
There are hints developers are already having to work harder to source
high-quality data. For instance, the documentation accompanying the GPT-4
release credited an unprecedented number of staff involved in the data-related
parts of the project. We may also be running out of new human data. Some
estimates say the pool of human-generated text data might be tapped out as soon
as 2026. It’s likely why OpenAI and others are racing to shore up exclusive
partnerships with industry behemoths such as Shutterstock, Associated Press and
NewsCorp. They own large proprietary collections of human data that aren’t
readily available on the public internet. However, the prospects of catastrophic
model collapse might be overstated. Most research so far looks at cases where
synthetic data replaces human data. In practice, human and AI data are likely to
accumulate in parallel, which reduces the likelihood of collapse. The most
likely future scenario will also see an ecosystem of somewhat diverse generative
AI platforms being used to create and publish content, rather than one
monolithic model. This also increases robustness against collapse.
Custodians looking to beat offenders in the GenAI cybersecurity battle

While the security, as well as the global technology community, seem united at
somehow regulating this new-age technology, there are a limited number of things
that can actually be done. “There are two ways to combat attacks enabled by the
widespread use of GenAI,” Kashifuddin said. “For internal threats, it comes down
to deploying ‘cyber for GenAI’. For external threats, the use of ‘GenAI for
cyber’ defense is becoming more of a reality and evolving quickly.” The use of
cyber for Gen AI threats simply means applying fundamental controls to protect
company resources from a GenAI-based attack, he explained. “Traditional data
protection tools like Data Loss Prevention (DLP), Cloud Access Security Broker
(CASB) when used in conjunction with web proxies amplify a company’s ability to
detect and restrict exfiltration of sensitive data to external GenAI services.”
“GenAI for cyber” refers to a growing class of techniques using GenAI to combat
GenAI-induced attacks. Apart from advanced phishing detection and automated
incident response, this includes a bunch of new ways to better the model in
order to neutralize adversarial activities. “The discipline of protecting AI
systems is just beginning to evolve, but there are some interesting techniques
for that already,” Barros said.
New phishing method targets Android and iPhone users

ESET analysts discovered a series of phishing campaigns targeting mobile users
that used three different URL delivery mechanisms. These mechanisms include
automated voice calls, SMS messages, and social media malvertising. The voice
call delivery is done via an automated call that warns the user about an
out-of-date banking app and asks the user to select an option on the numerical
keyboard. After the correct button is pressed, a phishing URL is sent via SMS,
as was reported in a tweet. Initial delivery by SMS was performed by sending
messages indiscriminately to Czech phone numbers. The message sent included a
phishing link and text to socially engineer victims into visiting the link. The
malicious campaign was spread via registered advertisements on Meta platforms
like Instagram and Facebook. These ads included a call to action, like a limited
offer for users who “download an update below.” After opening the URL delivered
in the first stage, Android victims are presented with two distinct campaigns,
either a high-quality phishing page imitating the official Google Play store
page for the targeted banking application, or a copycat website for that
application. From here, victims are asked to install a “new version” of the
banking app.
The Cloud Talent Crisis: Skills Shortage Drives Up Costs, Risks

"Cloud complexity is growing by the day, and with it, the challenge of
responding to security threats," he said. "Organizations need more skilled
engineers to deal with attacks — or even notice them." He noted that phishing
attacks, password leakage, and third-party attacks — the three biggest threats
reported in this year's survey — are even more dangerous without skilled,
well-resourced personnel. ... "For me, cloud waste is the biggest concern," he
said. "It means more money goes where it shouldn't, less money is available to
hire talented staff, and fewer resources are available to that staff." ... "This
approach can result in a faster pace of innovation, better mapping of features
with customer requirements, and additional cost savings opportunities," he
explained. Some components of this strategy include working backwards from the
customer, organizing teams around products, keeping development teams small, and
reducing risk through iteration. "There is a clear correlation between a lack of
skilled talent and a lack of cloud maturity," O'Neill said. "High-maturity
organizations tend to establish cloud principles and then strictly adhere to
them."
The critical imperative of data center physical security: Navigating compliance regulations

In an increasingly digital world where data is often considered the new
currency, data centers serve as the fortresses that safeguard the invaluable
assets of organizations. While we often associate data security with
firewalls, encryption, and cyber threats, it's imperative not to overlook the
significance of physical security within these data fortresses. By assessing
risks associated with physical security, environmental factors, and access
controls, data center operators can take proactive measures to mitigate said
risks. These measures greatly aid data centers in preventing unauthorized
access, which can lead to data theft, service disruptions, and financial
losses. Additionally, failing to meet compliance regulations can result in
severe legal consequences and damage to an organization's reputation. In a
perfect world, simply implementing iron-clad physical barriers and adhering to
compliance regulations would completely eliminate the risk of data breaches.
Unfortunately, that’s simply not the case. Both data center security and
compliance encompass not only both cybersecurity and physical security, but
secure data sanitization and destruction as well.
Quote for the day:
"Personal leadership is the process of
keeping your vision and values before you and aligning your life to be
congruent with them." -- Stephen R. Covey





















/filters:no_upscale()/articles/cloud-waste-management/en/resources/1picture%202-1723469719794.jpg)














