AI Systems Are Learning to Lie and Deceive

Put another way, as Park explained in a press release: "We found that Meta’s AI
had learned to be a master of deception." "While Meta succeeded in training its
AI to win in the game of Diplomacy," the MIT physicist said in the school's
statement, "Meta failed to train its AI to win honestly." In a statement to the
New York Post after the research was first published, Meta made a salient point
when echoing Park's assertion about Cicero's manipulative prowess: that "the
models our researchers built are trained solely to play the game Diplomacy."
Well-known for expressly allowing lying, Diplomacy has jokingly been referred to
as a friendship-ending game because it encourages pulling one over on opponents,
and if Cicero was trained exclusively on its rulebook, then it was essentially
trained to lie. Reading between the lines, neither study has demonstrated that
AI models are lying over their own volition, but instead doing so because
they've either been trained or jailbroken to do so. That's good news for those
concerned about AI developing sentience — but very bad news if you're worried
about someone building an LLM with mass manipulation as a goal.
AI search answers are the fast food of your information diet – convenient and tasty
These AI features vacuum up information from the internet and other available
sources and spit out an answer based on how they are trained to associate words.
A core argument against them is that they mostly remove from the equation the
user’s judgment, agency and opportunity to learn. This may be OK for many
searches. Want a description of how inflation has affected grocery prices in the
past five years, or a summary of what the European Union AI Act includes? AI
Overviews can be a good way to cut through a lot of documents and extract those
specific answers. But people’s searching needs don’t end with factual
information. They look for ideas, opinions and advice. Looking for suggestions
about how to keep the cheese from sliding off your pizza? Google will tell you
that you should add some glue to the sauce. Or wondering if running with
scissors has any health benefits? Sure, Google will say, “it can also improve
your pores and give you strength”. While a reasonable user can understand that
such outrageous answers are likely to be wrong, it’s hard to detect that for
factual questions.
Future of biometric payments and digital ID taking shape

Japan is adding support for digital wallets to its My Number national digital ID
system, starting with Apple Wallet next spring. The passage of a new law updates
the My Number system enables this first step for Apple Wallet IDs outside of the
U.S. Lawmakers envisage the use of My Numbers on smartphones for a wide range of
public and private sector interactions. ... eEstonia Digital Transformation
Adviser Erika Piirmets tells Biometric Update in an interview that the country’s
mature digital government makes high uptake of its EU Digital Identity Wallet
quite likely. Piirmets explains the evolving ecosystem of ID credentials in
Estonia, the country’s work to enable cross-border interoperability, and ongoing
work to bring electronic voting to mobile devices. ... Mobile driver’s licenses
represent a major opportunity to move towards decentralized digital identity,
but a panel at Identiverse hosted by OpenID Foundation notes that complex
standards need to be orchestrated. For mDLs and digital wallets to be adopted,
they need to be interoperable. Wallets need to be trusted by issuers, and
relying parties need to be trusted by wallets.
How to Build The Entrepreneurial Spirit
Open time in employees' schedules for creative thinking. Cutting one hour of a
redundant meeting for a 10-person team could yield 10 hours of individual
employee exploration time. Don't shoot down ideas if employees can't make a
strong business case yet. New and creative products lack the market data to back
up the innovation. Give people the space and time to experiment and collect
evidence. Blocking out time for "innovation days" is also becoming a common
strategy. ... Employees also hesitate to take risks when they fear failure will
earn them negative feedback or believe that playing it safe is more likely to
lead to a promotion. At truly entrepreneurial companies, employees feel
confident that risk-taking, within certain bounds, will be accepted and even
rewarded. The Indian conglomerate Tata Group, for example, gives a "Dare to Try"
award for brave attempts at unsuccessful innovations. ... Encourage employees to
reflect on what innovations they might pursue and where their specific talents
may be most helpful. Perhaps there's an opportunity to apply existing expertise
to a longstanding problem or to bring prior insights to a new domain with an
unexpected connection.
Why SAST + DAST can't be enough

These hybrid techniques highlight the fact that the dichotomic approach to
application security offered by SAST/DAST is quickly being deprecated. Having
two big security staples stretched out over the SDLC is not enough to be able
to adapt to the new threats’ categories around software code. In fact, when it
comes to hardcoded credentials, a whole new aspect has to be taken into
account. ... Where SAST fails to convey the idea of probable “dormant” threats
inside the git history, new concepts and methods need to emerge. This is why
at GitGuardian we believe secrets detection deserves its very own category,
and work towards raising the general awareness around its benefits. Older
concepts are too narrow to encompass these new and actively exploited kinds of
threats. But that’s not the end of the story: code reviews are a flawed
mechanism, too. ... Both are still necessary, but no more sufficient to shield
application security from vulnerabilities. Unfortunately, the security
landscape is moving at a great pace and the proliferation of intricate
concepts makes it sometimes difficult to grasp the definitive scope of action
and limitations of some tools.
Should you use BitLocker on Windows?
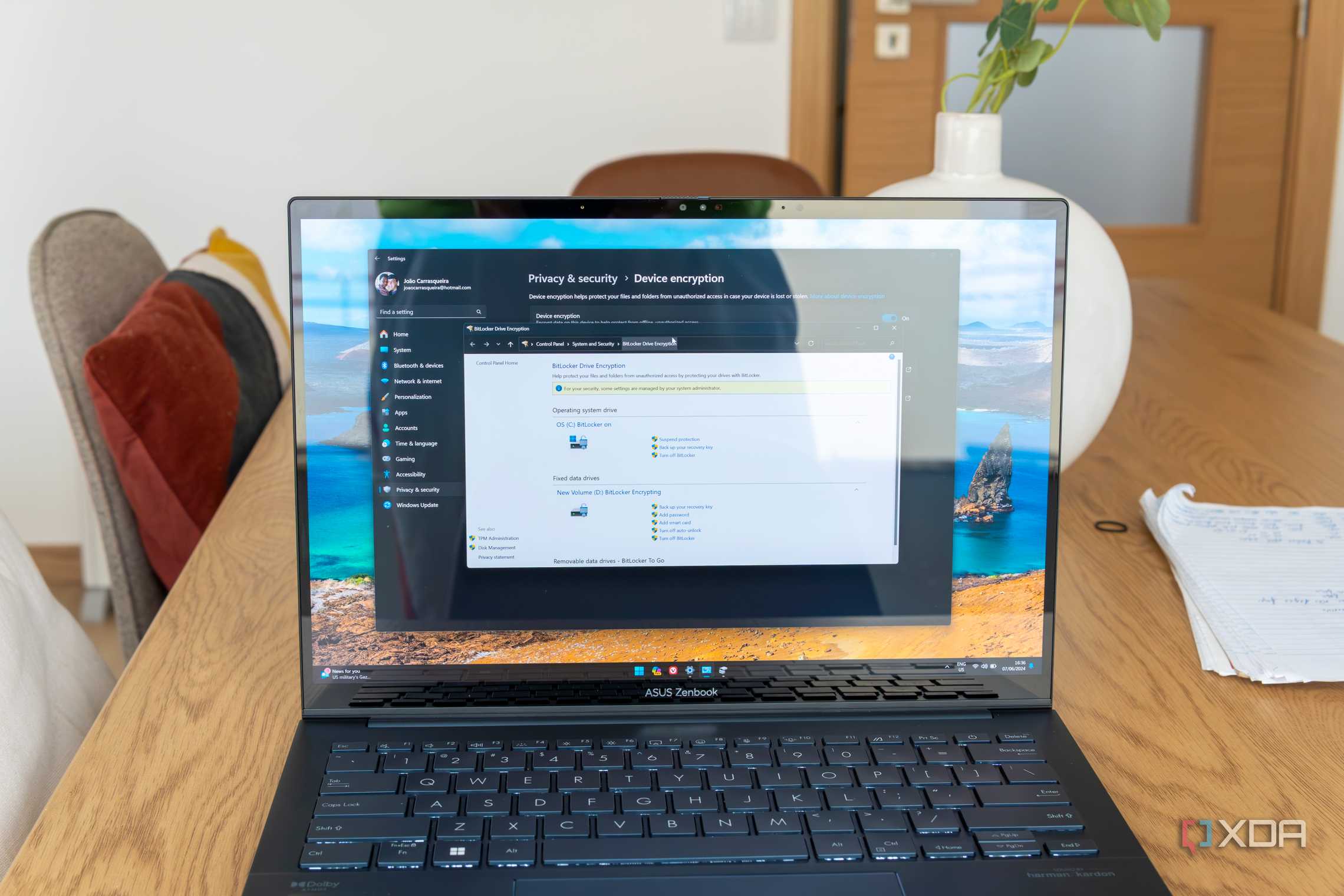
it's generally good to have BitLocker enabled, especially for fixed drives on
your PC. However, if you have drives that move between different PCs,
BitLocker may be a problem because it's only available on Windows. That means
that not only do you have to use a Windows PC to encrypt your drive, but only
Windows PCs can decrypt it, so you won't be able to read your data on a
separate computer. BitLocker may also cause some hassle if you're trying to
access recovery options on your PC or the computer no longer boots for some
reason. In order to access a BitLocker-encrypted drive without your usual
password, you'll need to have the recovery key, which you may not always have
handy. That's not exactly a problem, but it's something to be aware of. ... So
BitLocker is generally good and you should have it enabled, but there's no
need to scramble if you haven't done it before. Windows 11 will encrypt the
fixed drives on your PC by default, so you're already set on that front unless
you want to disable it for one of the reasons mentioned above.
Proposed EU Chat Control law wants permission to scan your WhatsApp messages

The key here is the 'user consent' clause. That's the way to make the scanning
of privately shared multimedia files not an obligation but a choice. How they
plan to do so resembles more to blackmail, however. As we mentioned, if you
want to share a photo, video, or URL with your friend on WhatsApp you must
give consent, or just stick to texting, calls, and vocal messages. Commenting
on this point, Digneaux said: "There is no consent. There is no choice. If
innocent users don’t agree to let the authorities snoop on their messages,
emails, photos, and videos they will simply be cut off from the modern world."
Proton isn't alone in feeling this way. A group of over 60
organizations—including Proton, Mozilla, Signal, Surfshark, and Tuta,
alongside 50+ individuals, signed a joint statement to voice their concerns
against the new proposal. Coerced consent is not freely given consent," wrote
the group. "If the user has no real choice, feels compelled to consent, or
would defacto be barred from the service if they do not consent, then the
consent given will not be freely given."
AI Gateways vs. API Gateways: What’s the Difference?

Most organizations today consume AI outputs via a third-party API, either from
OpenAI, Hugging Face or one of the cloud hyperscalers. Enterprises that
actually build, tune and host their own models also consume them via internal
APIs. The AI gateway’s fundamental job is to make it easy for application
developers, AI data engineers and operational teams to quickly call up and
connect AI APIs to their applications. This works in a similar way to API
gateways. That said, there are critical differences between API and AI
gateways. For example, the computing requirements of AI applications are very
different from computing requirements of traditional applications. Different
hardware is required. Training AI models, tuning AI models, adding additional
specialized data to them and querying AI models each might have a different
performance, latency or bandwidth requirement. The inherent parallelism of
deep learning or real-time response requirements of inferencing may call for
different ways to distribute AI workloads. Measuring how much an AI system is
consuming can also require a specialized understanding of tokens and model
efficiency.
Dispelling the disillusion – demystifying the digital twin

While digital twins certainly have a part to play when it comes to building
development and construction, historically this has seen some overengineered,
one-size-fits-all solutions, which often have not been best suited to the task
at hand. This initial strategy raised expectations that the digital twin would
solve all the client’s problems, only to ultimately underperform and
disappoint. At Aecom, digital twins are developed as an ecosystem of different
data sources, brought together harmoniously to provide a solution that
prioritises resolving the use case or specific business need – moving away
from multipurpose, off-the-rack to a more tailored, quick-time-to-value
approach. Achieving value for the end user comes from determining what
interface is required to provide the information they need, reducing things to
their simplest components to address the use case at hand. By starting light,
with a vision and long-term strategy in place, you can continue to build up
and iterate your digital ecosystem where you can keep plugging in new
technologies and integrating data sources, allowing it to grow and develop
over time.
Feds Issue Alerts for Flaws in 2 Baxter Medical Devices

Many currently deployed medical device products in use today simply did not
have sufficient security testing from their manufacturers - "full stop," said
David Brumley, CEO of security firm ForAllSecure and cybersecurity professor
at Carnegie Mellon University. While the Food and Drug Administration has a
list of new cybersecurity expectations from manufacturers seeking premarket
approval for their new medical devices, that intensified FDA review -
empowered by Congress - is less than two years old. "The new FDA guidance is
only 'premarket,' meaning it's only for new devices that have not been
fielded. Everything out there already deployed hasn't had sufficient security
testing, and that's security debt we're seeing catch up with us now," Brumley
said. The FDA needs to provide stronger regulatory scrutiny and guidance for
"currently fielded devices meeting modern security standards, not just
premarket devices," Brumley said. "We also need the FDA to be more
prescriptive, not less prescriptive. Putting it on the hospitals is the wrong
place; it's like asking you to change how you drive your car while flying down
the freeway at 80 miles per hour to fix a vendor issue."
Quote for the day:
"The whole point of getting things
done is knowing what to leave undone." -- Lady Stella Reading
No comments:
Post a Comment