Do Disaster Recovery Sites Actually Work?

Having the right resources available during a crisis is crucial. While internal
IT teams perform disaster drills and claim they are able to run operation from
the remote site, the fact is that new discoveries come to the fore when a
disaster strikes and top management team is usually oblivious to these issues.
These so-called drills are often just a farce put on for external and internal
auditors, who seldom get to the core issues that may have occurred during the
drill. Most auditor reports are checklists and they are happy to tick them off
and present a rosy picture to the management. It is important to remember that
NSE’s press release also said that it did not invoke the disaster recovery site
based on management consultations. So what actually is a disaster recovery site?
In layman terms it is an alternate site (which can be within the same city or
another city) which is capable of running all the operations designed in a
primary site. The genesis of a disaster recovery site is the business continuity
policy (BCP). This document lists all IT systems that hold the data of an
organisation, its dependencies with other systems, and all the elements which
are necessary to run the system
We’ll never have true AI without first understanding the brain
The vast majority of AI researchers don’t really embrace the idea that the
brain is important. I mean, yes, people figured out neural networks a while
ago, and they’re kind of inspired by the brain. But most people aren’t trying
to replicate the brain. It’s just whatever works, works. And today’s neural
networks are working well enough. And most people in AI have very little
understanding of neuroscience. It’s not surprising, because it’s really hard.
It’s not something you just sit down and spend a couple of days reading about.
Neuroscience itself has been struggling to understand what the hell’s going on
in the brain. But one of the big goals of writing this book was to start a
conversation about intelligence that we’re not having. I mean, my ideal dream
is that every AI lab in the world reads this book and starts discussing these
ideas. Do we accept them? Do we disagree? That hasn’t really been possible
before. ... An AI that can detect cancer cells is great. But is that
intelligence? No. In the book I use the example of robots on Mars building a
habitat for humans. Try to imagine what kind of AI is required to do that. Is
that possible? It’s totally possible.
Why paying off ransomware gangs is not a good idea

So what is the alternative? Insurers, especially in the US, urge their clients
to quickly and quietly pay the ransom to minimise the damage of disruption.
Then insurers allow the company to claim back the ransom payment on their
insurance and raise their premiums for the following year. This payment is
usually handled discreetly by a broker. In essence, the ransomware ecosystem
functions like a protection racket, effectively supported by insurers who are
set to pocket higher premiums as attacks continue. Aside from the moral
objections we might have to routinely paying money to criminals, this practice
causes two important practical problems. First, it encourages complacency in
cybersecurity. This complacency was best exemplified when a hacked company
paid a ransom, but never bothered to investigate how the hackers had breached
their system. The company was promptly ransomed again, by the same group using
the very same breach, just two weeks later. Second, some ransomware gangs
invest their ill-gotten gains into the research and development of better
cyber-tools. Many cybersecurity researchers are concerned about the increasing
sophistication of the malware used by leading cybercrime groups such as REvil
or Ryuk, which are both thought to be based in Russia.
Credential exposure trends: You need a better password
The data recovered by SpyCloud researchers includes more than 4.6 billion
pieces of personally identifiable information (PII), including names,
addresses, birthdates, job titles, social media URLs and nearly 1.3 billion
phone numbers. Criminals use PII to create fake accounts or steal someone
else’s identity and then apply for lines of credit, intercept tax refunds,
drain bank accounts and more. With as little as one or two pieces of PII, they
can compromise a person’s identity. Despite years of advice about the
importance of strong passwords, people inevitably end up reusing or recycling
the same credentials for multiple sites. Outdated password complexity
requirements have complicated the issue by providing people with a false sense
of security when they recycle a favorite password with a few simple changes,
like capitalizing the first letter and adding a 1 or ! at the end. Industry
standards call for organizations to convert plaintext passwords into hashes so
if they are breached, criminals can’t easily access the passwords themselves.
But some hashing algorithms are computationally harder to crack than others.
Unfortunately, even the strongest hashing algorithm means little when users
make weak or common password choices.
The office of the future is about people not places

Experts suggests the future of employment will be a hybrid mix of office- and
home-working. As many as 90% of HR leaders believe employees will carry of
working remotely in the post-COVID age, says tech analyst Gartner. That shift
to hybrid working is something that resonates with Paul Coby, CIO at global
science and chemicals company Johnson Matthey, whose guess is that people in
the future will split their time between working from home and going into the
office. What that means for many of us is that the traditional nine-to-five
working day at the corporate HQ isn't coming back. "It seems to me that
sitting in an office doing emails doesn't seem like a great use of offices or
an individual's time," says Coby. Other experts agree. Researcher CCS Insights
predicts more than half of all office-based employees will still work mainly
remotely through 2022. IoD research, meanwhile, suggests more than half of
business leaders plan on reducing their long-term use of workplaces, with more
than one in five reporting use will be significantly lower. The office that
many of us knew – with its command-and-control leadership styles – is probably
gone forever. Get it right, and managers could change how we all work for the
better. But quite how business leaders will organise and manage the hybrid
workplace of the future is still very much up for debate right now.
Why global power grids are still vulnerable to cyber attacks

“Power grids are getting increasingly vulnerable because of digitalization and
the use of more smart applications,” said Daine Loh, a Singapore-based power
and renewables analyst at Fitch Solutions. It’s a threat highlighted in an
initial probe in India that found an October blackout in Mumbai may have been
caused by cyber sabotage. That outage impacted stock markets, trains and
thousands of households in the nation’s financial hub. The disruptive
potential of grid failures — as seen in Texas last month due to a sudden deep
freeze — makes the sector a key target, particularly for state-based hostile
actors. Over the past four decades, power plants and substations have been
moving from manual to automatic controls, and are increasingly being connected
to public and private networks for remote access, leaving them exposed to
attacks. Producers and distributors have also often been reluctant to spend on
protecting themselves against low-probability attacks. “India’s power system
is in urgent need of proper cybersecurity systems,” said Reji Kumar Pillai,
president of India Smart Grid Forum, a think-tank backed by the federal power
ministry and which advises governments, regulators and utilities.
Version 2 of Google’s Flutter toolkit adds support for desktop and web apps
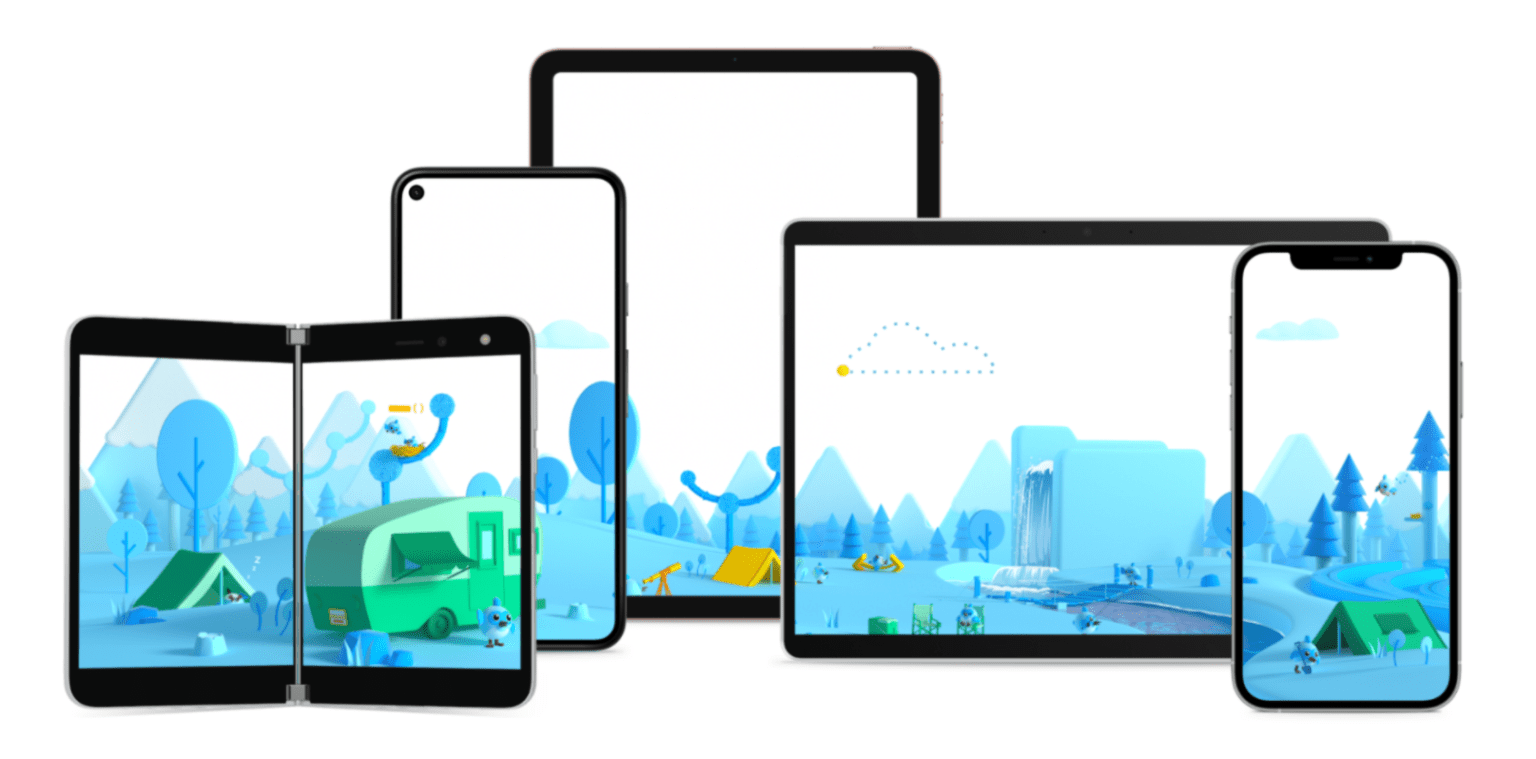
Over the course of the last year or so, the team started working on what it
calls Canvas Kit. This WebAssembly-based project takes the same Skia graphics
engine that powers Android and Chrome itself and makes it available to web apps.
“What that’s meant is that we can now essentially bypass the core HTML — sort of
the document-centric parts of the web platform — and really use the app-centric
parts of the web platform without leaving [behind] things like auto-complete of
text or passwords and all the things that keep the web feeling very unique,”
Sneath said. On the desktop, Google is announcing that Canonical is going all-in
on Flutter and making it the default choice of all its future desktop and mobile
apps. Microsoft, too, is expanding its support for Flutter and working with
Google on Windows support for Flutter. Given Microsoft’s interest in Android,
that’s maybe no huge surprise, and indeed, Microsoft today is releasing
contributions to the Flutter engine to help support foldable Android devices. In
total, Google notes, there are now over 15,000 packages for Flutter and Dart
from companies like Amazon, Microsoft, Adobe, Huawei, Alibaba, eBay and Square.
Data Science Environments
Environment managers are critical to the concept of virtual machines. A
virtual machine (VM) can be thought of as a computer inside of your computer
(Inception style). As with everything mentioned here, a virtual machine is
simply a method of file management. The VM is a program that isolates itself
from all the other files on the computer; it may even run a different
operating system. (For example, a MacOS computer might have a virtual machine
running a Windows operating system.) Virtual machines are very effective
when you want to recreate a programming environment on another computer,
because you don’t need to know anything about that computer’s current
dependencies. You can set up a virtual machine that has exactly the files
visible to it that you have on your own computer’s virtual machine. For this
reason, data science heavily utilizes virtual machines; they ensure
reproducibility of results. Cloud-based applications are another common
example of VMs. The developer counts on the fact that their VM will be
isolated from any other code living on the server hosting their application.
8 mobile security threats you should take seriously

A mobile device is only as secure as the network through which it transmits
data. In an era where we're all constantly connecting to networks that might not
be optimally secured — be they improperly configured home networks, for remote
workers, or public WiFi networks — our information frequently isn't as protected
as we might assume. Just how significant of a concern is this? According to
research by Wandera, in a more typical year, corporate mobile devices use WiFi
almost three times as much as they use cellular data. Nearly a quarter of
devices connect to open and potentially insecure WiFi networks, and 4% of
devices encounter a man-in-the-middle attack — in which someone maliciously
intercepts communication between two parties — within an average month. Those
numbers have dipped this past year due to reduced travel and fewer physical
businesses being open during COVID, but that doesn't mean the threat is gone —
or that there's no need to remain ahead of the game, even with employees working
mostly from home. "Rather than relying on man-in-the-middle attack detection to
be reactive, we recommend organizations take a more proactive approach to
securing remote connections," says Michael Covington
Risky business: 3 timeless approaches to reduce security risk in 2021
Some organizations see migrating to the cloud as a way of creating greenfield
environments that can be secured more easily than the tech-debt-laden
on-premises network. Yes, cloud adoption does have many security benefits.
And, yes, the cloud does represent an opportunity to do things over better.
With a greenfield architecture, with best practices baked neatly into it.
Only, many organizations’ lack of cloud security processes and controls can
quickly eat away at the cloud’s forecasted risk reduction benefits, reducing
the overall value of this opportunity. You should keep in mind that AWS S3
buckets are left unsecured and publicly available all the time. Developers
have been known to leave (or hardcode) private keys and tokens in the most
embarrassing places. Personnel leave files unsecured and open to the public
far too often. Publicly available endpoints are improperly segmented from
private networks, sometimes creating an autobahn towards the on-premises
network. Many organizations don’t do a good enough job of monitoring activity
in the cloud or the information flow between the cloud and the on-premises
network.
Quote for the day:
"It is easy to lead from the front
when there are no obstacles before you, the true colors of a leader are
exposed when placed under fire." -- Mark W. Boyer
No comments:
Post a Comment