Generation Z majority left cold by data literacy

Helena Schwenk, analyst relations and market intelligence lead at Exasol, said:
“Regardless of job descriptions, the ability to work with data is becoming
increasingly crucial in the workplace. In theory, D/Natives should have
developed the data literacy skills necessary for effective data analysis,
storytelling and visualisations. Their untapped potential could spur a
revolution in the way we use data to transform business and improve our daily
lives. “But our survey highlights two issues: a genuine skills shortage when it
comes to the more complex data skills gained through the education system, and a
clear miscommunication between the language D/Natives use and the business
jargon used by employers. There is work for educators, business leaders and the
young people themselves to do to bridge the data literacy gap – to create not
just a productive workforce, but also a richer society.” Schwenk, a former
analyst at IDC and Ovum, has recently been joined at Exasol by Peter Jackson as
its chief data and analytics officer. Jackson also has a high profile in the UK
data community, as the co-author, with Caroline Carruthers, of The chief data
officer’s playbook and a former data leader at the Pensions Regulator, Southern
Water and Legal & General.
Strategies to Modernize, Maintain, and Future-Proof Systems
We tend to think about technology advancing in a straight line, with each
iteration better and more sophisticated than what came before. The reality is a
little more complicated than that because there are no one-size-fits-all
solutions. As we make incremental improvements to technology, we are only really
optimizing for a specific set of use cases. Those same improvements might make
other uses more difficult. Over time what tends to happen is as one technology
gets more and more optimized, the group of people for whom things are moving in
the opposite direction of what they actually need gets larger and larger, until
finally there are enough people to establish a market for a “new” technology to
shift things back in the opposite direction. My favorite example of this is cell
phone size: for a while cellphones were about staying connected to the office on
the go, so each more advanced version was smaller and thinner. Then the emphasis
shifted from work functions to entertainment functions, and suddenly cell phones
started to get bigger and bigger. Technology is filled with these kind of cycles
where it feels like we’re reinventing or repackaging old solutions.
5 Web Application Security Threats and 7 Measures to Protect Against Them

Broken authentication is another common vulnerability that is caused by poorly
implemented authentication and session management controls. If an attacker is
successful in identifying and exploiting authentication-related vulnerabilities,
they can gain direct access to sensitive data and functionality. The goal of the
attackers to exploit authentication vulnerabilities is to impersonate a
legitimate user of the application. Attackers employ a wide variety of
techniques such as credential stuffing, session hijacking, password brute force,
Session ID URL rewriting, etc., to leverage these weaknesses. These attacks can
be prevented by implementing strong session management controls, multi-factor
authentication, restricting and monitoring failed login attempts. For more
details on prevention, refer to this article. Sensitive data exposure occurs
when the web application does not sufficiently safeguard sensitive information
such as session ids, passwords, financial information, client data, etc. The
most common flaw of organizations resulting in data exposure is not encrypting
sensitive data.
Hidden areas of security and the future of hybrid working
Businesses should think carefully about how they utilize these platforms –
starting with security. Many of the platforms, such as Microsoft Teams, do not
come with built-in cybersecurity features, and don’t provide a way for data to
be easily archived. In fact, Microsoft does not provide any guarantee of
restorability – if a file is accidently deleted, it’s gone forever. This leaves
a big gap for operations that need to ensure that they have a strong archiving
strategy in place. Additionally, IT and security teams must be aware of the
vulnerability of these tools to phishing or social engineering attacks. Unlike
email, files shared via collaboration platforms cannot be scanned for malicious
links or other content. A good example of this is a Microsoft Teams phishing
campaign recently discovered by Mimecast which consisted of 772 emails and
targeted recipients mainly based in the US. Those targeted were sent fake email
notifications asking them to verify their password or telling them they had been
added to a project via their Teams account. Similarly, another Teams attack
discovered late last year was estimated to have targeted 15,000-50,000 people by
the time it was detected, showing how widespread the problem can get.
Hybrid workers are stressed out, but "empathy-based management" could help

As the remote-work landscape has blurred the lines between work and personal
life, workers struggle to put up boundaries, and many stay connected long
after the work day is done. According to the research, workers in the hybrid
world are "1.27 times more likely to struggle to disconnect from work than
employees in the on-site world." And "40% of hybrid or remote employees [are]
reporting an increase in the length of their workday in the past 12 months."
This kind of fatigue caused by the longer workday is a main concern for 92% of
HR leaders. Leaders should stop expecting employees to be always "on." The
very tools that are used to ensure the smooth transition to a hybrid work
model are also its Achilles' Heel. "Organizations have inadvertently been
making the fatigue worse," Cambon said. There have actually been more
check-ins (78%) between managers and workers, and 84% more virtual meetings
with teams, for instance. According to Garter, "HR leaders must lead and
support the creation of a hybrid model that mitigates the adverse impacts of
digital distraction, virtual overload and the always-on mindset. Ironically,
many of the actions that organizations are taking to improve the hybrid
employee experience are actually exacerbating the fatigue these hybrid
realities are creating."
From Digital To Physical: The Ultimate Challenge For AI
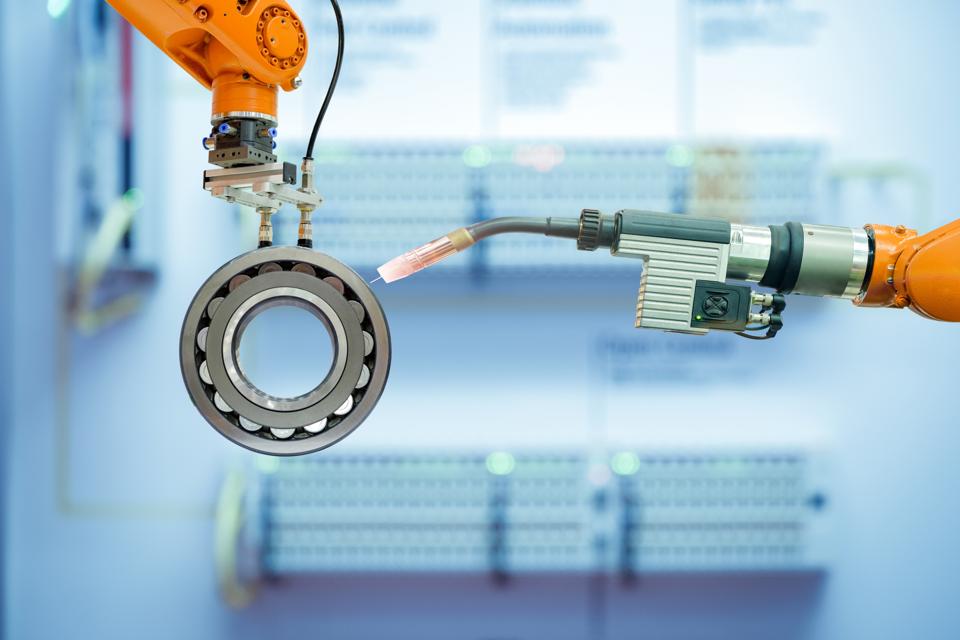
By crossing the digital/physical barrier and implementing AI-powered visual
quality inspections, the industry can mitigate the crisis and labor shortage.
The use of AI removes the barriers that typically slow technology adoption in
that it is cost effective, easy to integrate and doesn't need specially
trained staff to operate. AI-based visual inspections are used today to
inspect for defects in metal engine parts, check integrity of rugs/carpet,
assess whether raw material (such as meat) has foreign contaminants (e.g.,
plastic particles), check plastic food trays for the right item, inspect
quality of baked goods (e.g., bread), determine integrity of vaccine vials and
more. These are all real-world, often mission-critical applications of AI
technology in challenging physical settings. The value of digital-to-physical
applications of AI is clear, as well as how they can be applied in the
manufacturing industry—so what's next? For anyone looking to implement AI
across their organization, the next steps are simple. First, you need to take
a look at your specific workflows and determine what processes could benefit
from AI: Is it a quality inspection, is it predictive maintenance or is it
something else?
Working with Secure Enclaves in Azure SQL Database

Encryption has always been challenging to implement, but if it is implemented
infrequently, data breaches become much more damaging: If a bunch of encrypted
data gets breached, it is not useful to anyone. If we think back to database
encryption in SQL Server, until Always Encrypted was introduced, anyone who
was a system administrator had access to the encryption keys, allowing them to
view decrypted data. Always Encrypted changed that paradigm. Instead of
storing encryption keys in the database, the keys that can decrypt data were
stored in the client application. This meant administrators could only view
the ciphertext (the result of the encrypted value) and not the plain text
value. Always Encrypted supports two types of encryption: deterministic (in
which the value of the ciphertext will always be the same for the same seed
value) and randomized (which provides a unique encrypted value for each
record). ... The key difference here is that with secure enclaves in place,
the database engine can send encrypted results into the secure enclave, where
data operations can take place. Then the data is returned to the database
engine, and in turn to the client operation in encrypted format. While the
enclave is shown in its container, it is part of the SQL Server process on the
server.
The unique opportunity for Fintech in the payments space

As a society we’re becoming disengaged with the cumbersome process of card
payments and more conscious than ever about typing pin codes into public
machines, with antibacterial gel on stand-by. With today’s available
technology there is just no need to queue, swipe, PIN and collect paper
receipts. We’re moving into an age of completely contactless spending, one
where people can exit a taxi without “paying”, leave a shop without visiting
the till, and get instant credit at a digital checkout. Where e-wallets
account for 8%-10% year on year growth of ecommerce transactions, with no sign
of slowing down. We’re moving into a digital-first generation that is used to
buying things with the tap of a phone screen or a scan of their face. So much
so, physical wallets are becoming obsolete as phones stay glued to hands.
Although as a society we’re engaging less and less in person or making
payments over a counter, fintechs are leading the way with technology to trust
customers are who they say they are, digitally, so that they can access
frictionless payment experiences without merchants incurring the risk of
fraud.
What IT Leaders Can Do To Diminish Fear Within Their Teams

First, I take personal responsibility for team progress on the project. I do
this visibly and deflect criticism of the team. I make it clear within the
team that only the complete team can succeed. As a group, we will work to
balance the assignments so no one person feels like the single point of
failure. To our sponsors of the project, I am clear about our status and needs
from senior leadership. Knowing that we are all on the same journey keeps the
team together. Eventually, all businesses run into budget problems. IT
spending is a necessary evil because businesses leverage mission-critical
applications. But the fear within the employees is that people may not seem as
necessary. The threat of possible downsizing casts an enormous shadow and can
be debilitating in concentrating on complex mental work. How do I keep our
focus amidst layoff rumors? My communication stresses our value. I ask the
team to show our company that we are going to continue to strive for
excellence. I pose this to my team: “Let’s continue to do great things. Will
the company value us more if we slip on quality, complain about our situation,
or spread layoff rumors?
The Evolution of Distributed Systems on Kubernetes
If you look at how microservice looks on Kubernetes, you will need to use some
platform functionality. Moreover, you will need to use Kubernetes features for
lifecycle management primarily. And then, most likely, transparently, your
service will use some service mesh, something like an Envoy, to get enhanced
networking capabilities, whether that's traffic routing, resilience, enhanced
security, or even if it is for a monitoring purpose. On top of that, depending
on your use case, you may need Dapr or Knative, depending on your workloads.
All of these represent your out-of-process, additional capabilities. What's
left to you is to write your business logic, not on top, but as a separate
runtime. Most likely, future microservices will be this multi-runtime composed
of multiple containers. Some of those are transparent, and some of those are
very explicit that you use. ... All the interactions of your business logic
with the external world happen through the sidecar, integrating with the
platform and does the lifecycle management. It does the networking
abstractions for the external system and gives you advanced binding
capabilities and state abstraction.
Quote for the day:
"Leadership is, among other things,
the ability to inflict pain and get away with it - short-term pain for
long-term gain." -- George Will
No comments:
Post a Comment