CISO Imperatives in the Age of Digital Transformation

With proliferation of open source, enterprises need to secure not just commercial software, but also invest in securing open source software. Every member in a connected ecosystem from vendors, services providers, practitioners to end consumers, needs to be secure. Any weak link can put the entire ecosystem at risk. Open source usage is increasingly seen in categories like cloud management, security, analytics and storage, which have historically been dominated by proprietary products. Some of the key emerging open source technologies are open source firewall, instantaneous server-less workloads, trustworthy AI, blockchain, quantum computing, etc. Fueled by open methodologies and peer production, employees from enterprises are contributing to open source communities and collaborating better, thus forcing management to rethink their strategies. 5G next generation wireless technology will enable enhanced speed and performance, lower latency and better efficiency. It is expected to be broadly used for IoT communications and videos while controls/automation, fixed wireless access, high-performance edge analytics, and location tracking are the second tier uses for 5G-capable networks.
Verizon: Companies will sacrifice mobile security for profitability, convenience

"For a number of reasons, mobile today is a smaller issue than many others," Zumerle said via email. "Among other factors, the operating system is more hardened, and mobile devices have less access to critical enterprise infrastructure and data." The Verizon report found that 39% of organizations admitted to suffering a security compromise involving a mobile device — up from 33% in the 2019 report and 27% in 2018. Of those that suffered a compromise, 66% said the impact was major and 36% said it had lasting repercussions. Twenty-percent of organizations that suffered a mobile compromise said a rogue or insecure Wi-Fi hotspot was involved. "Although the risks of public Wi-Fi are becoming well known, convenience trumps policy – even common sense — for many users. Some organizations are trying to prevent this by implementing Wi-Fi-specific policies, but inevitably, rules will be broken," Verizon said. According to MobileIron, 7% of protected devices detected a man-in-the-middle (MitM) attack in the past year.
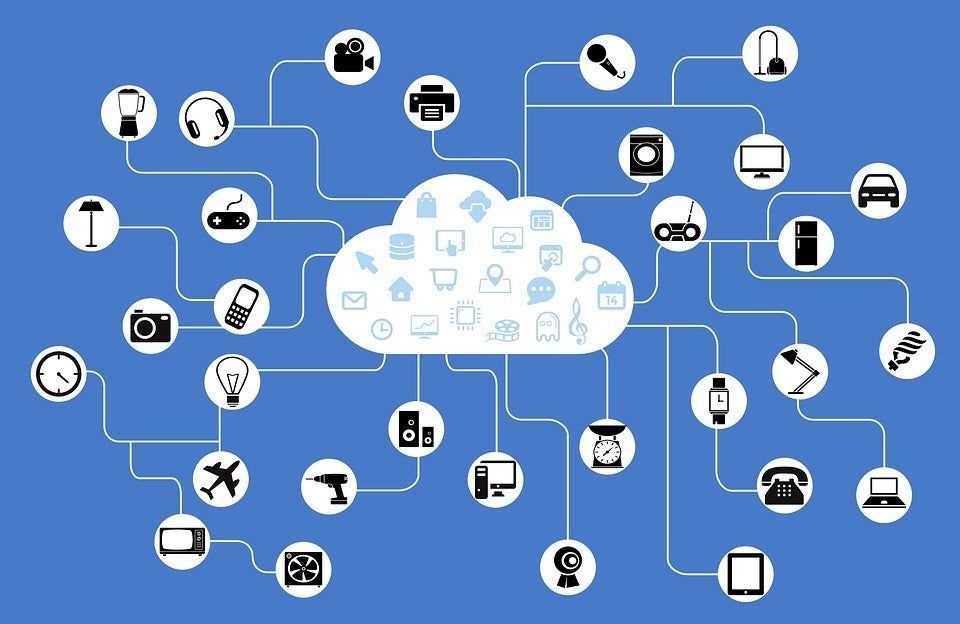
Report: Most IoT transactions are not secure
Zscaler is a bit generous in what it defines as enterprise IoT devices, from devices such as data-collection terminals, digital signage media players, industrial control devices, medical devices, to decidedly non-business devices like digital home assistants, TV set-top boxes, IP cameras, smart home devices, smart TVs, smart watches and even automotive multimedia systems. “What this tells us is that employees inside the office might be checking their nanny cam over the corporate network. Or using their Apple Watch to look at email. Or working from home, connected to the enterprise network, and periodically checking the home security system or accessing media devices,” the company said in its report. Which is typical, to be honest, and let (s)he who is without sin cast the first stone in that regard. What’s troubling is that roughly 83% of IoT-based transactions are happening over plaintext channels, while only 17% are using SSL. The use of plaintext is risky, opening traffic to packet sniffing, eavesdropping, man-in-the-middle attacks and other exploits. And there are a lot of exploits.
Envision The Future To Unlock Business Value
While we were busy applying service packs and working out how to prevent “dumb users” from getting themselves into trouble at work, those same people were beginning to enjoy the spoils of the 21st century. Armed increasingly with high speed domestic and even mobile broadband, as well as a wide range of tactile consumer tech devices, they were gradually starting to enjoy a dizzying array of consumer services that were transforming their daily lives. From building stronger relationships with friends and family through social networking, through to the transformation in their retail and lifestyle habits, for the first time ever, normal, every day people (not just nerds like me and my colleagues) were beginning to enjoy the opportunity of a world where technology is something that lifts our capability, helping us to achieve more in all aspects of our lives. Slowly, the centre of gravity of people’s use of technology shifted from the world of work to their personal lives to the point where, certainly by the end of the last decade, most people had access to better technology in their domestic lives than they did at work.
5 big microservices pitfalls to avoid during migration

Rushing into microservices adoption is one of the most common mistakes software teams make. Even though microservices provide a chance to deploy new applications and updates quickly, the distributed architecture's inherent complexity means it's not ideal for certain types of organizations or applications. Teams should review the state of their existing development culture to see if management skills are in place. They should also examine existing applications to determine whether they are suitable and ready for a migration to microservices. Agile and DevOps principles should be in place, as microservices tend not to play well with a Waterfall development approach. Teams also need diligent training and access to documentation before they begin a migration of monolith-based workloads. Performance issues soon arise when a microservices migration starts without a proper plan and appropriate infrastructure investments in place. Teams can mitigate these issues if they ensure services are strictly independent from each other but can still communicate normally, as is the target for a loosely coupled architecture.
AI, Azure and the future of healthcare with Dr. Peter Lee
What’s interesting about AI for Health is that it’s the first pillar in the AI for Good program that actually overlaps with a business at Microsoft and that’s Microsoft Healthcare. One way that I think about it is, it’s an outlet for researchers to think about, what could AI do to advance medicine? When you talk to a lot of researchers in computer science departments, or across Microsoft research labs, increasingly you’ll see more and more of them getting interested in healthcare and medicine and the first things that they tend to think about, if they’re new to the field, are diagnostic and therapeutic applications. Can we come up with something that will detect ovarian cancer earlier? Can we come up with new imaging techniques that will help radiologists do a better job? Those sorts of diagnostic and therapeutic applications, I think, are incredibly important for the world, but they are not Microsoft businesses. So the AI for Health program can provide an outlet for those types of research passions. And then there are also, as a secondary element, four billion people on this planet today that have no reasonable access to healthcare.
Why Unsupervised Machine Learning is the Future of Cybersecurity

There are two types of Unsupervised Learning: discriminative models and generative models. Discriminative models are only capable of telling you, if you give it X then the consequence is Y. Whereas the generative model can tell you the total probability that you’re going to see X and Y at the same time. So the difference is as follows: the discriminative model assigns labels to inputs, and has no predictive capability. If you gave it a different X that it has never seen before it can’t tell what the Y is going to be because it simply hasn’t learned that. With generative models, once you set it up and find the baseline you can give it any input and ask it for an answer. Thus, it has predictive ability – for example it can generate a possible network behavior that has never been seen before. So let’s say some person sends a 30 megabyte file at noon, what is the probability that he would do that? If you asked a discriminative model whether this is normal, it would check to see if the person had ever sent such a file at noon before… but only specifically at noon. Whereas a generative model would look at the context of the situation and check if they had ever sent a file like that at 11:59 a.m. and 12:30 p.m. too, and base its conclusions off of surrounding circumstances in order to be more accurate with its predictions.
Advanced Tech Needs More Ethical Consideration & Security
The recent confrontation between the US and Iran is a case in point. Threats of cyber warfare along with conventional military action put security executives at every major organization on high alert and questioning what to do in the event of a breach. There are worries of vulnerabilities to the infrastructure and that attackers could be impossible to identify. Very few organizations are fully prepared to respond to an incident at an enterprise or organizational level. An effective response to a major cyber incident requires current, effective IT-focused cyber plans, but also participation from all lines of business and operational support areas to ensure a successful integrated, orchestrated recovery. The benefits of advanced technologies to industry and commerce are manifold. In healthcare, robotic surgeries improve recovery rates and reduce days spent in the hospital. AI and machine learning boost productivity in the data-dependent financial services industry, increasing analytical efficiency while reducing manual work and human errors. The same goes for most industries.

IoT-specific regulations aren’t the only ones that can have an impact on the marketplace. Depending on the type of information a given device handles, it could be subject to the growing list of data-privacy laws being implemented around the world, most notably Europe’s General Data Protection Regulation, as well as industry-specific regulations in the U.S. and elsewhere. The U.S. Food and Drug Administration, noted Maxim, has been particularly active in trying to address device-security flaws. For example, last year it issued security warnings about 11 vulnerabilities that could compromise medical IoT devices that had been discovered by IoT security vendor Armis. In other cases it issued fines against healthcare providers. But there’s a broader issue with devising definitive regulation for IoT devices in general, as opposed to prescriptive ones that simply urge manufacturers to adopt best practices, he said. Particular companies might have integrated security frameworks covering their vertically integrated products – such as an industrial IoT company providing security across factory floor sensors – but that kind of security is incomplete in the multi-vendor world of IoT.
Intel CSME bug is worse than previously thought

At the time, the CVE-2019-0090 vulnerability was only described as a firmware bug that allowed an attacker with physical access to the CPU to escalate privileges and execute code from within the CSME. Other Intel technologies, like Intel TXE (Trusted Execution Engine) and SPS (Server Platform Services), were also listed as impacted. But in new research published today, Ermolov says the bug can be exploited to recover the Chipset Key, which is the root cryptographic key that can grant an attacker access to everything on a device. Furthermore, Ermolov says that this bug can also be exploited via "local access" -- by malware on a device, and not necessarily by having physical access to a system. The malware will need to have OS-level (root privileges) or BIOS-level code execution access, but this type of malware has been seen before and is likely not a hurdle for determined and skilled attackers that are smart enough to know to target the CSME.
Quote for the day:
"The problem with being a leader is that you're never sure if you're being followed or chased." -- Claire A. Murray
No comments:
Post a Comment