AI in IoT elevates data analysis to the next level

In a typical enterprise network, IoT exists beyond the boundaries of the cloud, passing data back through a firewall, where it then takes residence in storage and is made available to some process or application. But with so many different devices reporting -- a number that will steadily increase -- traffic problems are inevitable. Managing the flow of so much data from so many endpoints is beyond the resources of most companies. But wait; it gets worse. Many IoT applications are two-way streets, where data gathered by sensors has consequences in the locations they're reporting on; for example, adjusting the power consumption of a building based on changes in occupancy and weather. In many such cases, there's no time for data to make a round trip to a cloud. ... The fix for these problems is edge computing -- extending the processing power of an enterprise network by adding gateways and IoT devices that offer local processing power.
.NET Core: Past, Present, and Future

The highlight of the .NET Core 3.0 announcement was the support for Windows desktop applications, focused on Windows Forms, Windows Presentation Framework (WPF), and UWP XAML. At the moment of the announcement, the .NET Standard was shown as a common basis for Windows Desktop Apps and .NET Core. Also, .NET Core was pictured as part of a composition containing ASP.NET Core, Entity Framework Core, and ML.NET. Support for developing and porting Windows desktop applications to .NET Core would be provided by "Windows Desktop Packs", additional components for compatible Windows platforms. ... Microsoft shows .NET 5 as a unifying platform for desktop, Web, cloud, mobile, gaming, IoT, and AI applications. It also shows explicit integration with all Visual Studio editions and with the command line interface (CLI). The goal of the new .NET version is to produce a single .NET runtime and framework, cross-platform, integrating the best features of .NET Core, .NET Framework, Xamarin, and Mono.
Google’s Hangouts Chat gets chatbot boost with Dialogflow
By bringing Dialogflow to Hangouts Chat, Google wants to simplify the process of creating natural language bots users can interact with. “With Dialogflow, you can create a natural-sounding conversational UI with just a few clicks,” said Jon Harmer, product manager, Google Cloud, in a blog post. “Because Dialogflow includes built-in Natural Language Understanding (NLU), your bot can quickly understand and respond to user messages.” Developers can make their Dialogflow bots available for use in Google’s team collaboration app via the Hangouts Chat Integrations page, where they can install a bot on their own account to test in the application. In addition, a new Hubot adapter has been introduced, allowing developers to bring Hubot bots into Hangouts Chat. A chatbot catalog is also on its way to improve discoverability as the number of bots grows. That catalog will be available in the “coming months,” Google said. "Google continues to aggressively move to enable intelligent chatbots and natural voice capabilities to add value and remove mundane steps in communications and collaboration,” said Wayne Kurtzman
U.S. adds Chinese technology companies to export blacklist
Among those added to the blacklist were AMD’s Chinese joint-venture partner Higon, Commerce said in the statement. Also included were Sugon, which Commerce identified as Higon’s majority owner, along with Chengdu Haiguang Integrated Circuit and Chengdu Haiguang Microelectronics Technology, both of which the department said Higon had an ownership interest in. The ban affects AMD’s Chinese joint venture THATIC, which was established in 2016. AMD uses THATIC to license its microprocessor technology to Chinese companies including Higon. THATIC, or Tianjin Haiguang Advanced Technology Investment Co., is a Chinese holding company comprising an AMD joint venture with two entities, according to an AMD regulatory filing. THATIC provides chips to Sugon, a Chinese server and computer maker. Lisa Su, AMD’s chief executive officer, said at a recent conference in Taiwan that AMD would not license its newer technologies to Chinese companies.
There are multiple approaches to zero trust, but the main ones are focused on identity, gateway and the device. However, as the tide of mobile and cloud continues to intensify, the limitations of gateway and identity-centric approaches become more apparent. For instance: Identity-centric approaches - provide limited visibility on device, app and threats, while also still relying on passwords; one of the main causes of a data breach; and Gateway-centric approach - limited visibility on device, apps and threats, while also assuming that all enterprise traffic goes through the enterprise network when in reality 25 per cent of enterprise traffic doesn’t go through their network. Only a mobile-centric zero trust approach addresses the security challenges of the perimeter-less modern enterprise while allowing the agility and anytime access that business needs. Mobile-centric zero trust seeks to verify more attributes than both these approaches before granting access. It validates the device, establishes user context, checks app authorisation, verifies the network, and detects and remediates threats before granting secure access to any device or user.
7 steps to enhance IoT security

Controlling access within an IoT environment is one of the bigger security challenges companies face when connecting assets, products and devices. That includes controlling network access for the connected objects themselves. Organizations should first identify the behaviors and activities that are deemed acceptable by connected things within the IoT environment, and then put in place controls that account for this but at the same time don’t hinder processes, says John Pironti, president of consulting firm IP Architects and an expert on IoT security. “Instead of using a separate VLAN [virtual LAN] or network segment which can be restrictive and debilitating for IoT devices, implement context-aware access controls throughout your network to allow appropriate actions and behaviors, not just at the connection level but also at the command and data transfer levels,” Pironti says. This will ensure that devices can operate as planned while also limiting their ability to conduct malicious or unauthorized activities, Pironti says. “This process can also establish a baseline of expected behavior that can then be logged and monitored to identify anomalies or activities that fall outside of expected behaviors at acceptable thresholds,” he says.
Introduction to ELENA Programming Language
ELENA is a general-purpose, object-oriented, polymorphic language with late binding. It features message dispatching/manipulation, dynamic object mutation, a script engine / interpreter and group object support. ... There is an important distinction between "methods" and "messages". A method is a body of code while a message is something that is sent. A method is similar to a function. in this analogy, sending a message is similar to calling a function. An expression which invokes a method is called a "message sending expression". ELENA terminology makes a clear distinction between "message" and "method". A message-sending expression will send a message to the object. How the object responds to the message depends on the class of the object. Objects of differents classes will respond to the same message differently, since they will invoke different methods. Generic methods may accept any message with the specified signature (parameter types).
Cyber attackers using wider range of threats

“The key findings illustrate the importance of layered security protections,” said Corey Nachreiner, chief technology officer at WatchGuard Technologies. “Whether it be DNS-level filtering to block connections to malicious websites and phishing attempts, intrusion prevention services to ward off web application attacks, or multifactor authentication to prevent attacks using compromised credentials – it’s clear that modern cyber criminals are using a bevy of diverse attack methods. “The best way for organisations to protect themselves is with a unified security platform that offers a comprehensive range of security services,” he said. Another key finding of the report is that Mac OS malware on the rise. Mac malware first appeared on WatchGuard’s top 10 malware list in the third quarter of 2018, and now two variants have become prevalent enough to make the list in the first quarter of 2019, the report said. It added that this increase in Mac-based malware further debunks the myth that Macs are immune to viruses and malware and reinforces the importance of threat protection for all devices and systems.
Google Cloud Scheduler is Now Generally Available
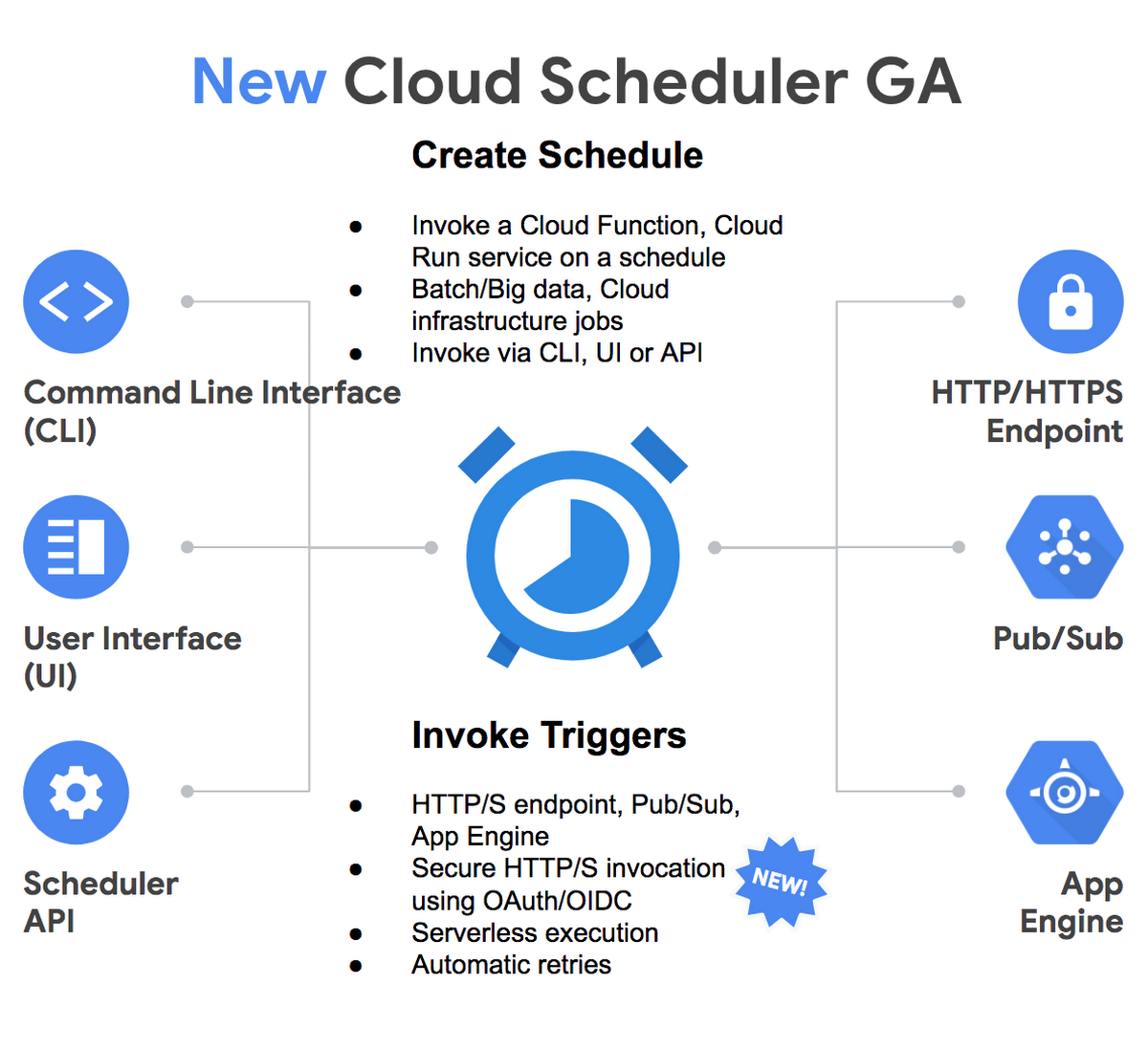
Users can schedule a job in Cloud Scheduler by using its UI, or the CLI or API to invoke an HTTP/S endpoint, Cloud Pub/Sub topic or App Engine application. When a job starts, it will send Cloud Pub/Sub message or an HTTP request to a specified target destination on a recurring schedule. Subsequently, the target handler will execute the job and return a response of the outcome – either: A success code (2xx for HTTP/App Engine and 0 for Pub/Sub) when it succeeds; Or an error, resulting in the Cloud Scheduler retrying the job until it reaches the maximum number of attempts. Furthermore, once user schedules a job, they can monitor this in the Cloud Scheduler UI and check the status. Google Cloud Scheduler is not the only managed cron service available in the public cloud. Competitors Microsoft and Amazon already offered a scheduler service that has been available for quite some time. Microsoft offers the Azure Scheduler service, which became generally available in late 2015 and will be replaced by Azure Logic Apps Service, where developers can use the scheduler connector. Also, Logic Apps offers additional capabilities for application and process integration, data integration and B2B communication. Furthermore, AWS released the Batch service with similar capabilities to Scheduler in late 2016.
4 steps to developing responsible AI

As AI capabilities race ahead, government leaders, business leaders, academics and many others are more interested than ever in the ethics of AI as a practical matter, underlining the importance of having a strong ethical framework surrounding its use. But few really have the answer to developing ethical and responsible AI. Responsible AI is the practice of designing, building and deploying AI in a manner that empowers people and businesses, and fairly impacts customers and society – allowing companies to engender trust and scale AI with confidence. It is imperative for business leaders to understand AI and make a top-down commitment to the responsible use of AI. Central to this is taking a human-centric approach to AI thinking and development. It is not enough to have the correct data, or an algorithm that performs accurately. It is critical to incorporate systems of governance, design and training that provide a framework for successfully implementing AI in an organization. A strong Responsible AI framework entails mitigating the risks of AI with imperatives that address four key areas
Quote for the day:
"Leaders keep their eyes on the horizon, not just on the bottom line." -- Warren G. Bennis

No comments:
Post a Comment